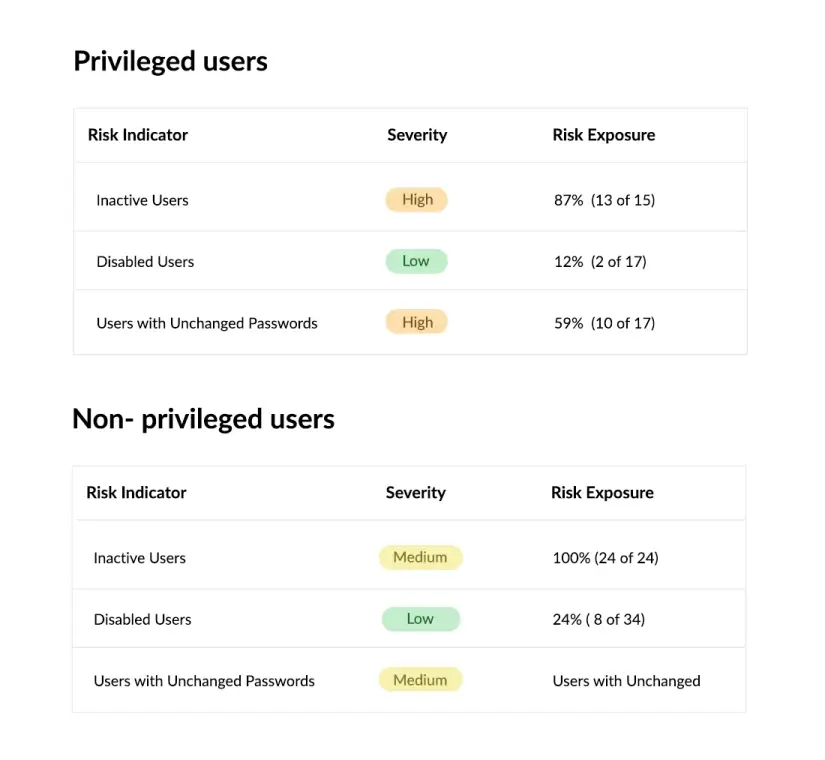
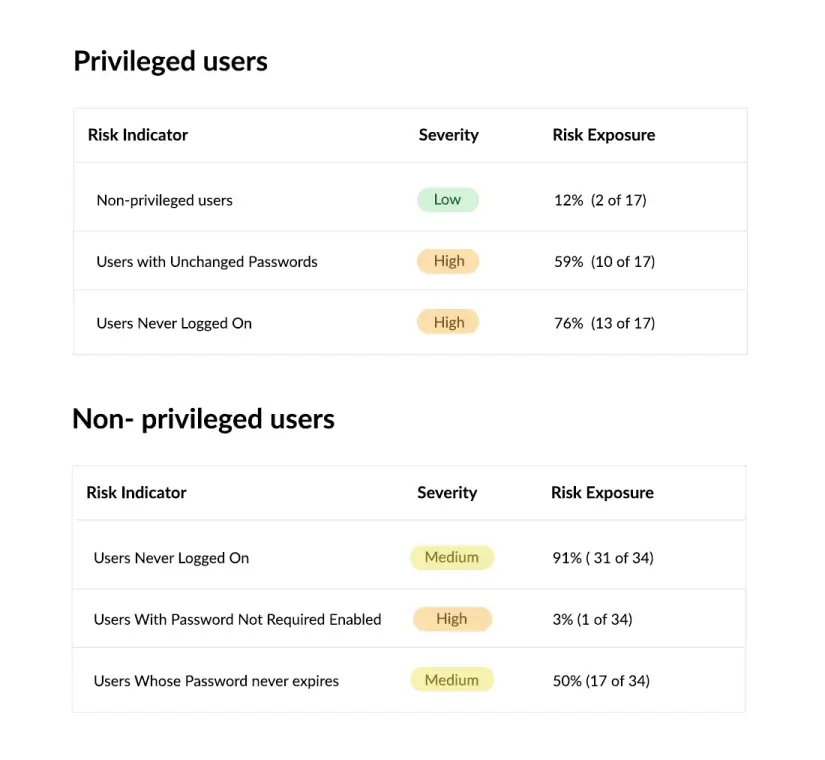
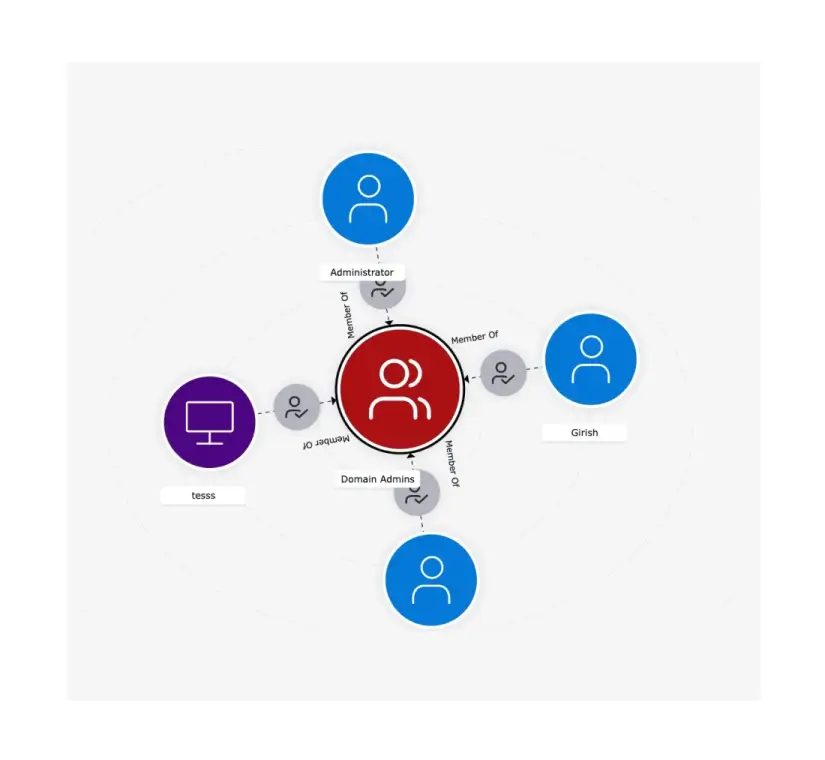
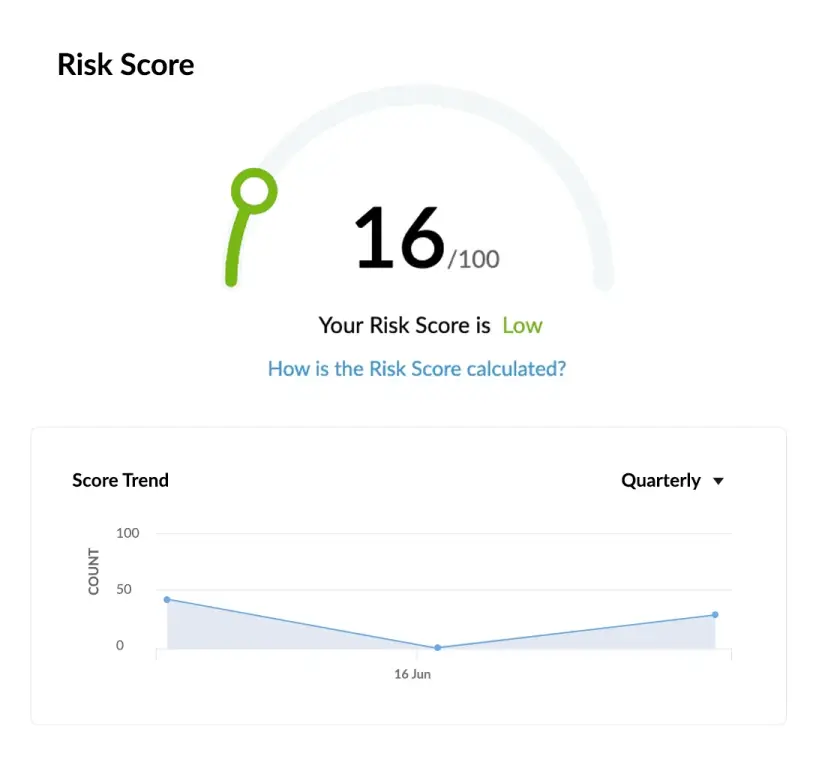
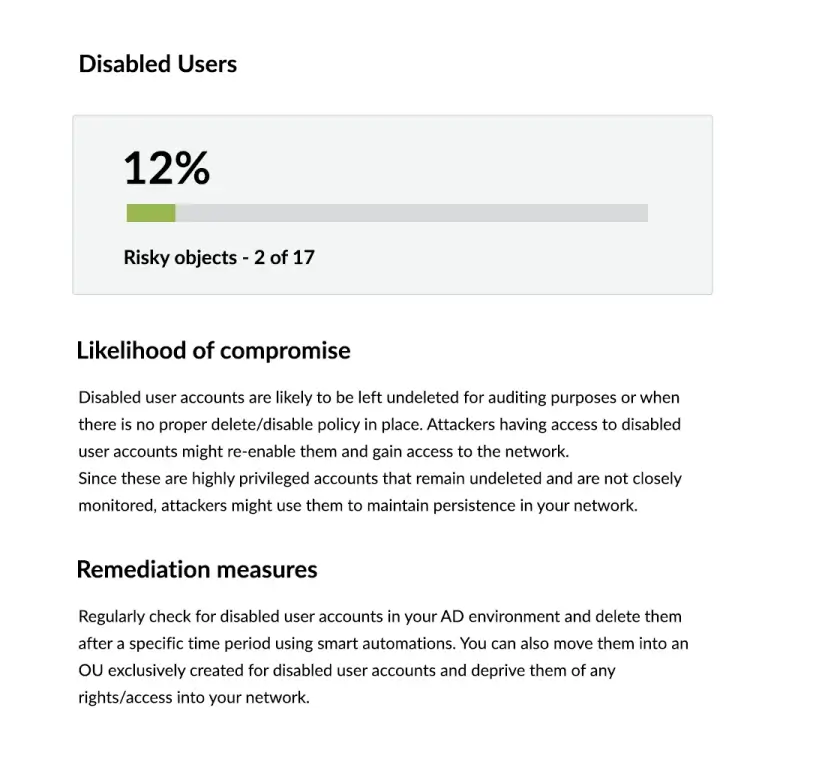
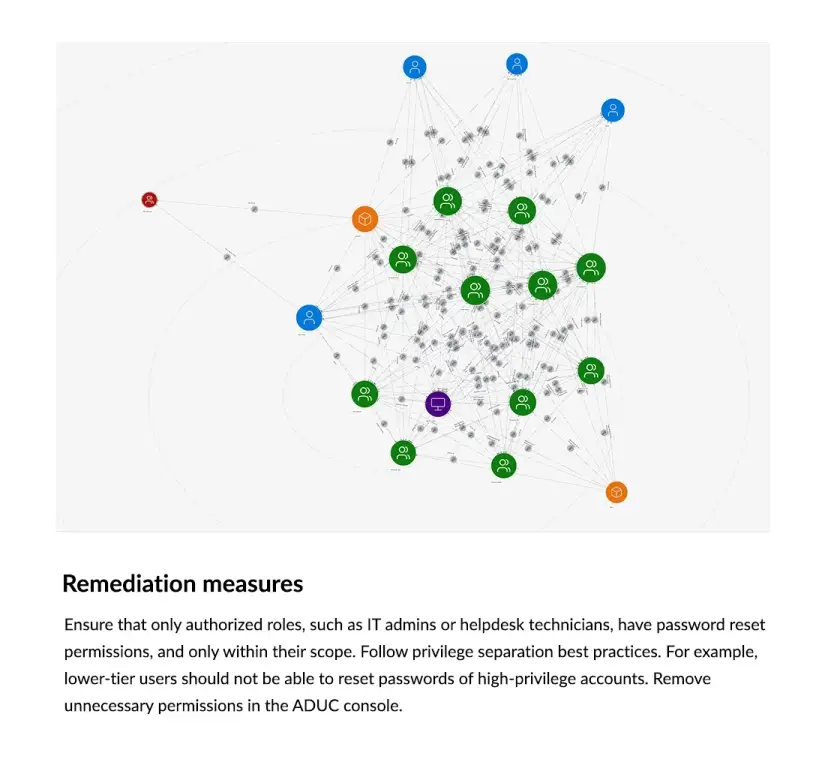
Identity security posture management (ISPM) is the continuous process of monitoring, assessing, and improving the security of identities and access permissions across an organization’s environment. It helps detect misconfigurations, excessive privileges, and unusual behaviors that could lead to identity-based breaches.