Control which applications run. Control who gets access. Enforce Zero Trust.
Remove standing admin rights, enable just-in-time access, and stop application abuse without slowing users down.
Only approved and verified applications run. Block unknown, unsigned, or risky executables as part of a Zero Trust execution model.
Prevent trusted applications from spawning malicious or unauthorized child processes. Stops LOLBins and script abuse.
Eliminate standing admin privileges and maintain control without affecting routine tasks.
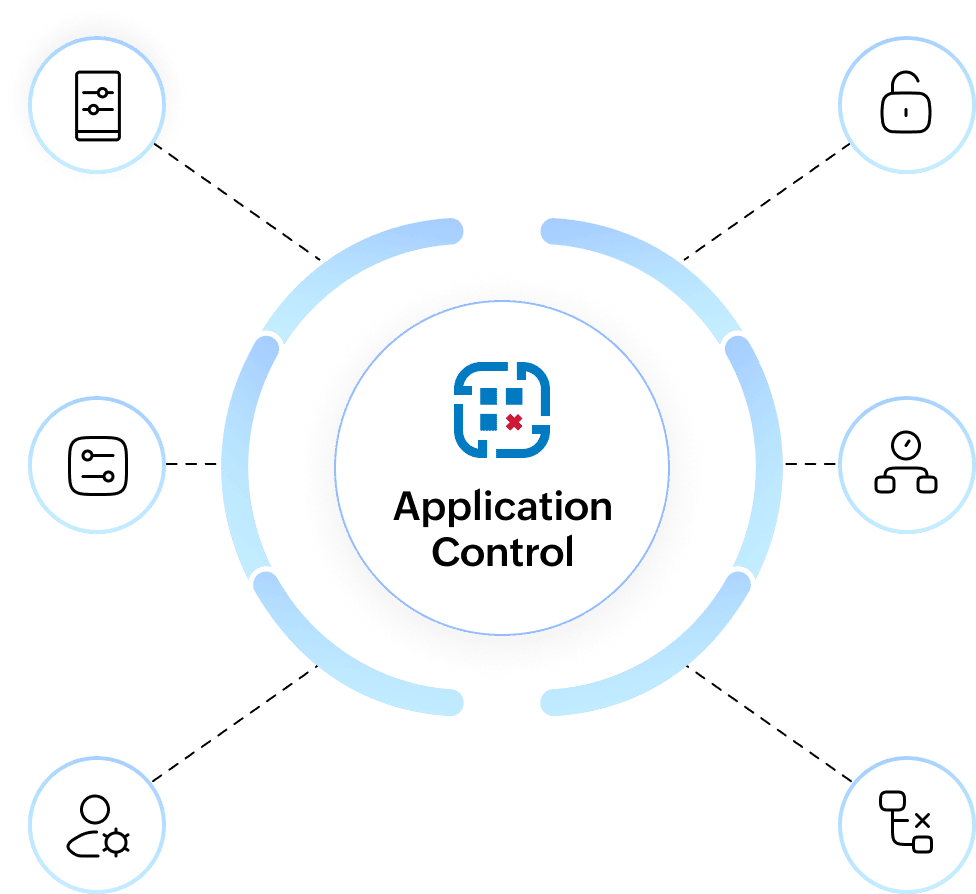
Apply least-privilege by default. Users get elevated rights only for sanctioned apps or approved tasks.
Temporary, time-bound elevation with full auditability. No more 24×7 access or long-lived privileges.
Built-in elevation requests with routing, approvals, expiry timers, and activity logs.

Extensive action library
Experience insights
Endpoint Monitoring

Data security
Vulnerability management
patch management
Browser security