Endpoint Privilege Management
Privileges within an organization are typically split between two basic levels of hierarchy in an enterprise: standard users and administrators. Domain Administrators are usually given the highest level of privilege with the ability to both modify and gain access to all standard user machines, where as local administrators have complete access to their particular endpoint and the data within it. Administrators in general also have exclusive privileges to run certain applications with elevated privileges.
Now imagine that a standard user needs to run an application that works only in administrator mode. Traditionally, enterprises would just provide this user with admin credentials or elevate the entire organizational-level privilege of that particular user, however, this would not only give them access to that particular application but also to all the top-level privileges the admin has.
In an ideal cyber-crime-free world, this would be fine. However, recent research reveals that out of all the security breaches that occurred in 2018, a whopping 34 percent of them were due to insider attacks, which highlights how risky granting admin credentials to just any standard user is. So, what can admins do instead? ManageEngine Application Control Plus essentially solves this crisis with it's built-in endpoint privilege management solution.
Establish endpoint privilege management seamlessly
How does Endpoint Privilege Management work?
Endpoint privilege management is the process of governing privileges so that admin privileges aren't excessively distributed among users.This prevents users from exploiting functions beyond their requirements, which is a common risk of elevating the entire user account privilege.With 80 percent of security breaches involving privileged credentials, endpoint privilege management is crucial for effective security. If an attacker gets their hands on a set of privileged credentials, they would be able to access all the endpoints present in your organization in no time, easily stealing data or injecting malware.
With POLP, endpoint privilege management can be used to reduce the attack surface by removing unnecessary local administrator accounts from devices and allowing only required user accounts to retain privileges. This feature ensures that prioritizing security doesn't affect productivity, as it enables select users to self-elevate their application-specific privileges when required.
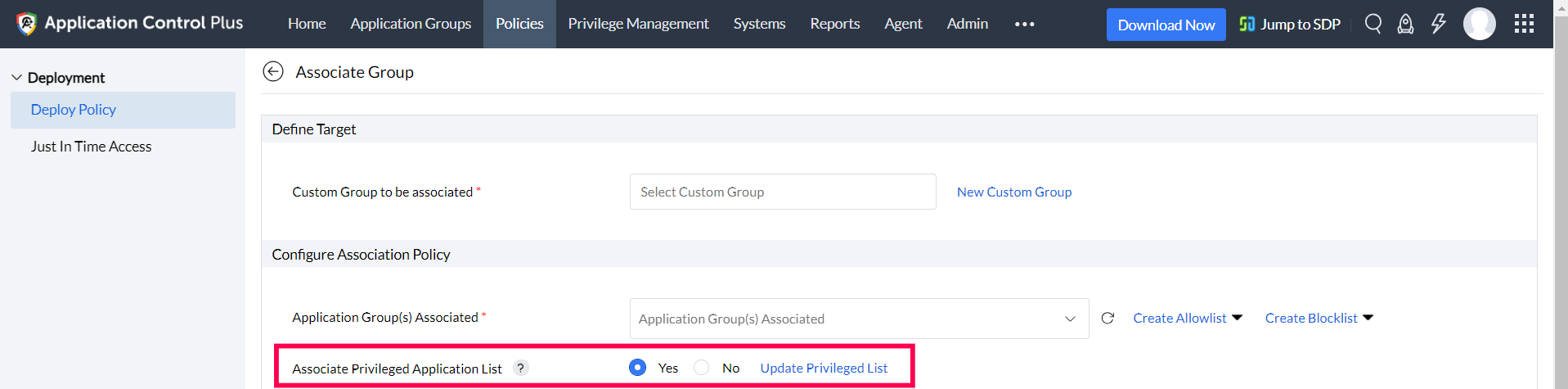
Using the Endpoint Privilege Management feature of Application Control Plus, after eliminating unnecessary local admin accounts, organizations can allow users of the chosen Custom Groups to self-elevate their privileges while running applications from the Privileged Application List.
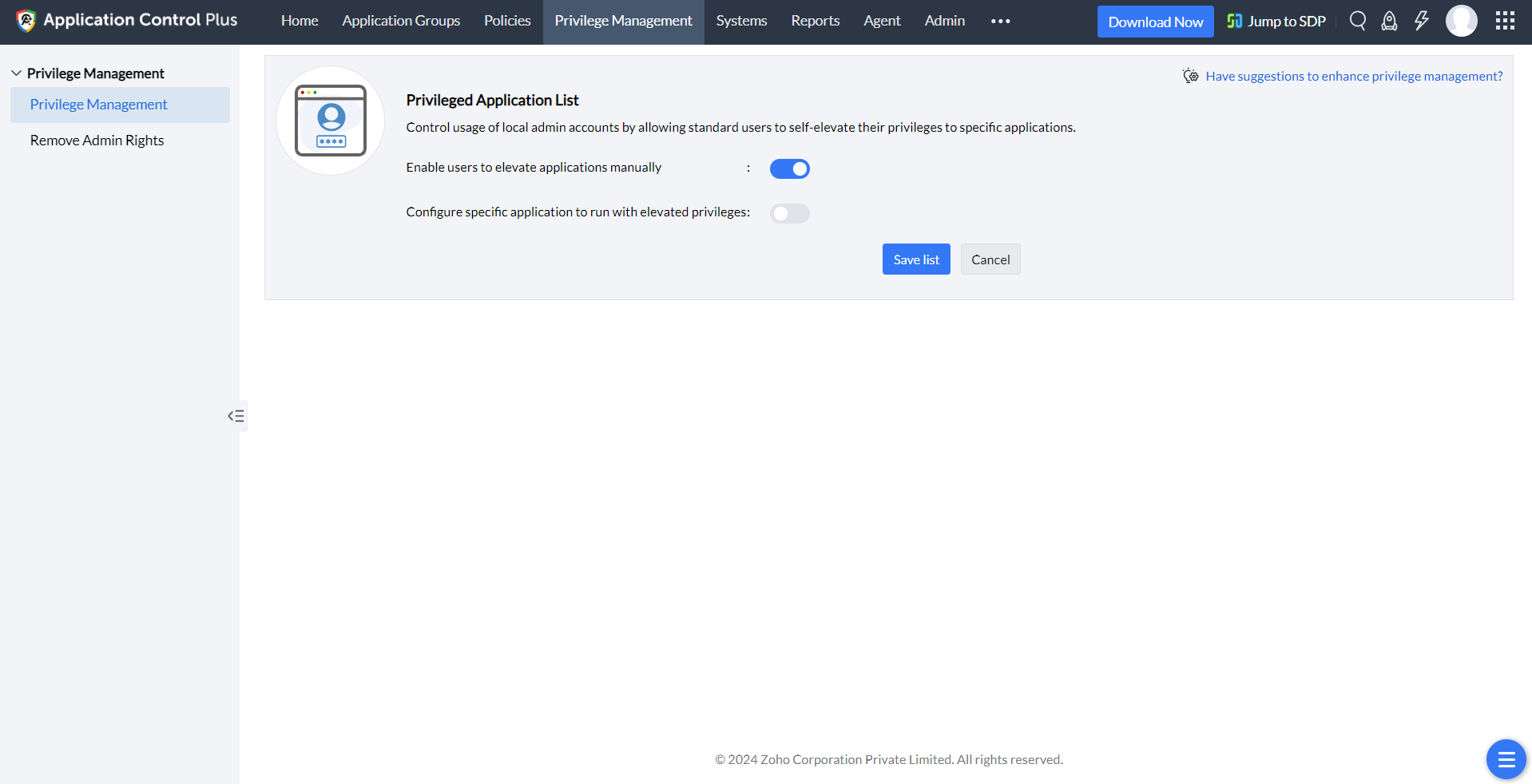
Create a Privileged Application List
Allow self-elevation of privileges to all applications
Administrators have the option to allow users to elevate their user privileges by providing a justification. The provided justification will be logged, and this capability can be configured for specific applications or all allowlisted applications.
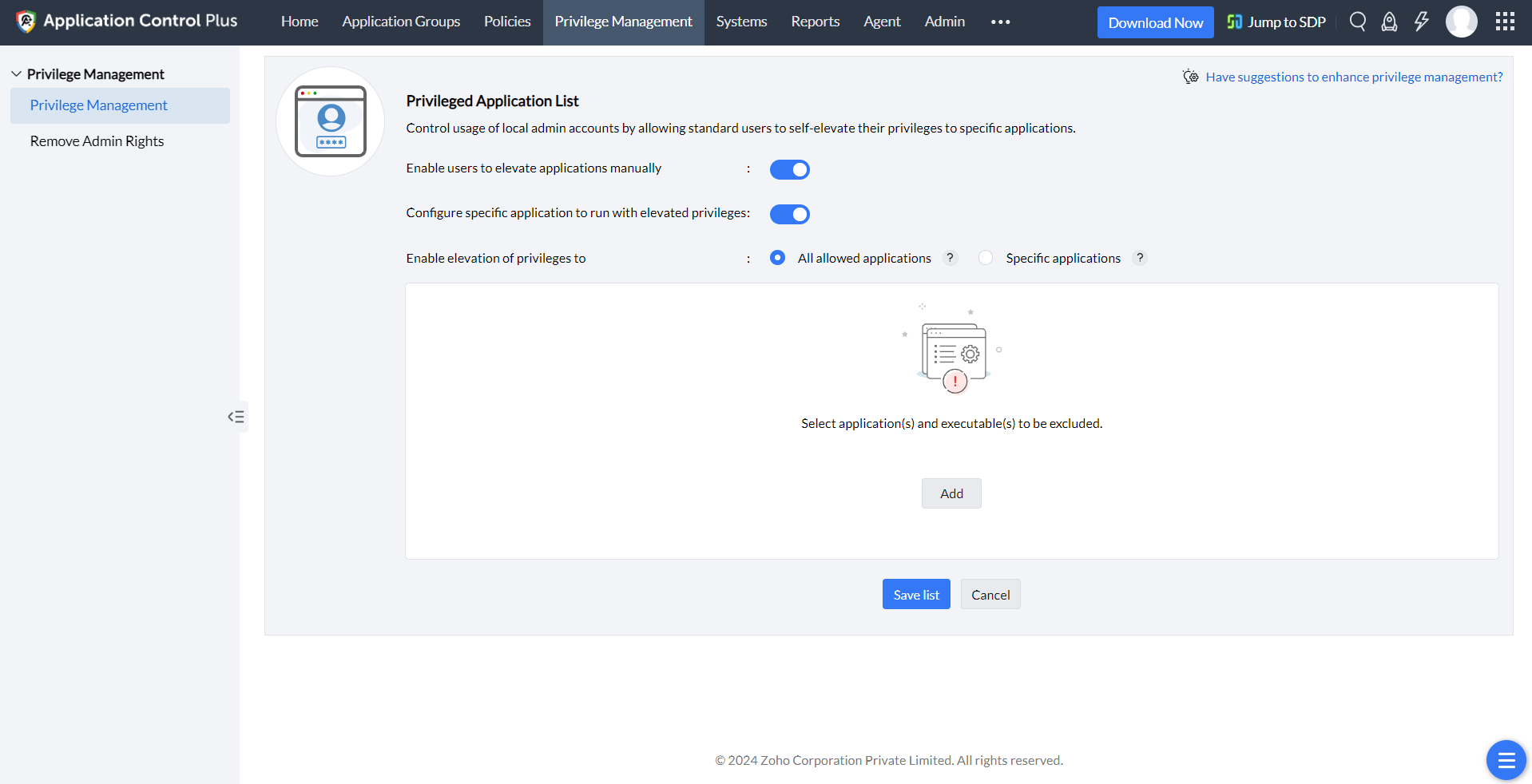
Allow elevation of privileges to all allowed applications
All allowlisted applications will get added to the Privileged Application List. Custom Groups associated with this list during policy deployment will be allowed to elevate their privileges to all applications that are allowlisted specifically to them. Administrators can choose the applications or executables to be excluded.
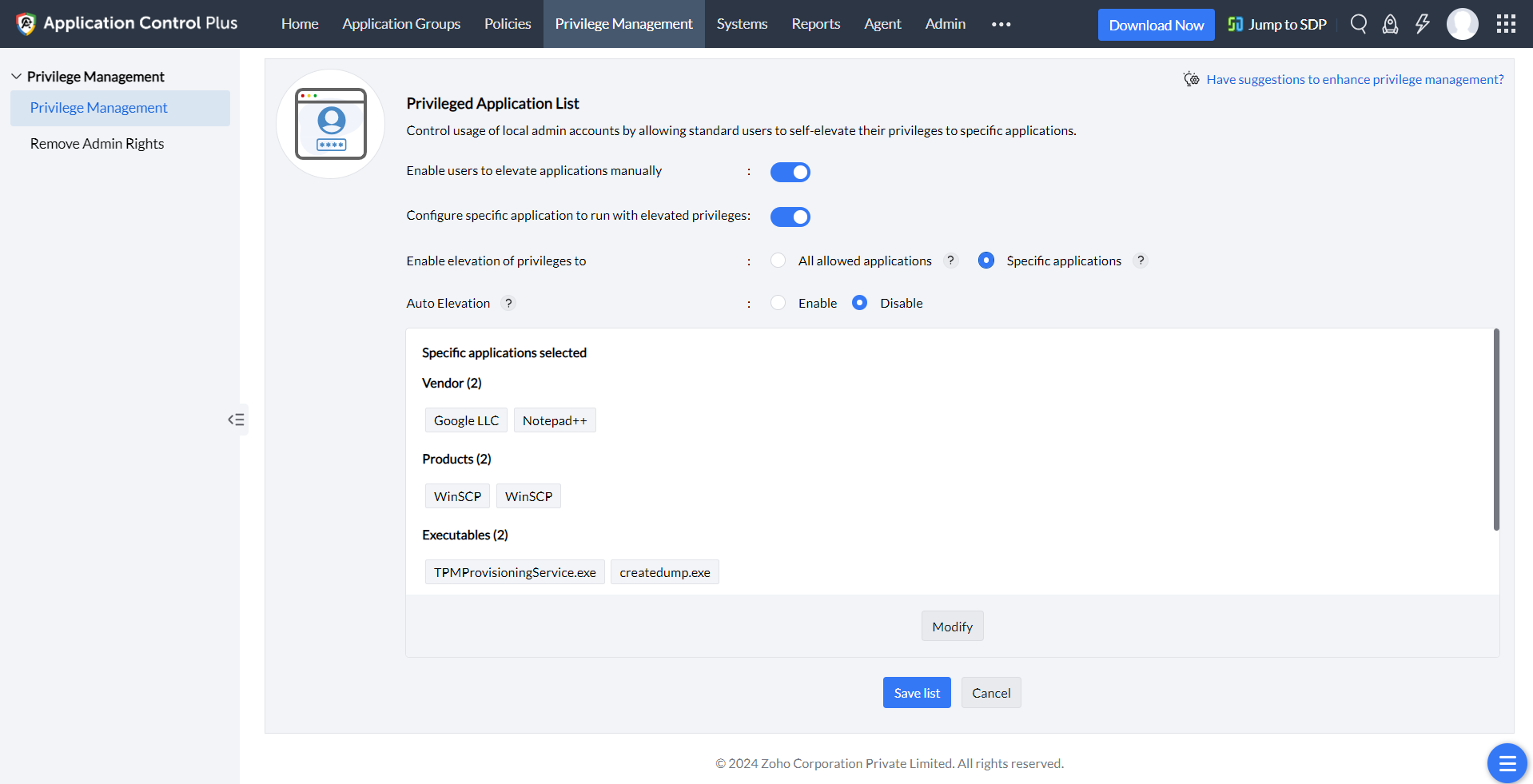
Allow elevation of privileges to specific applications
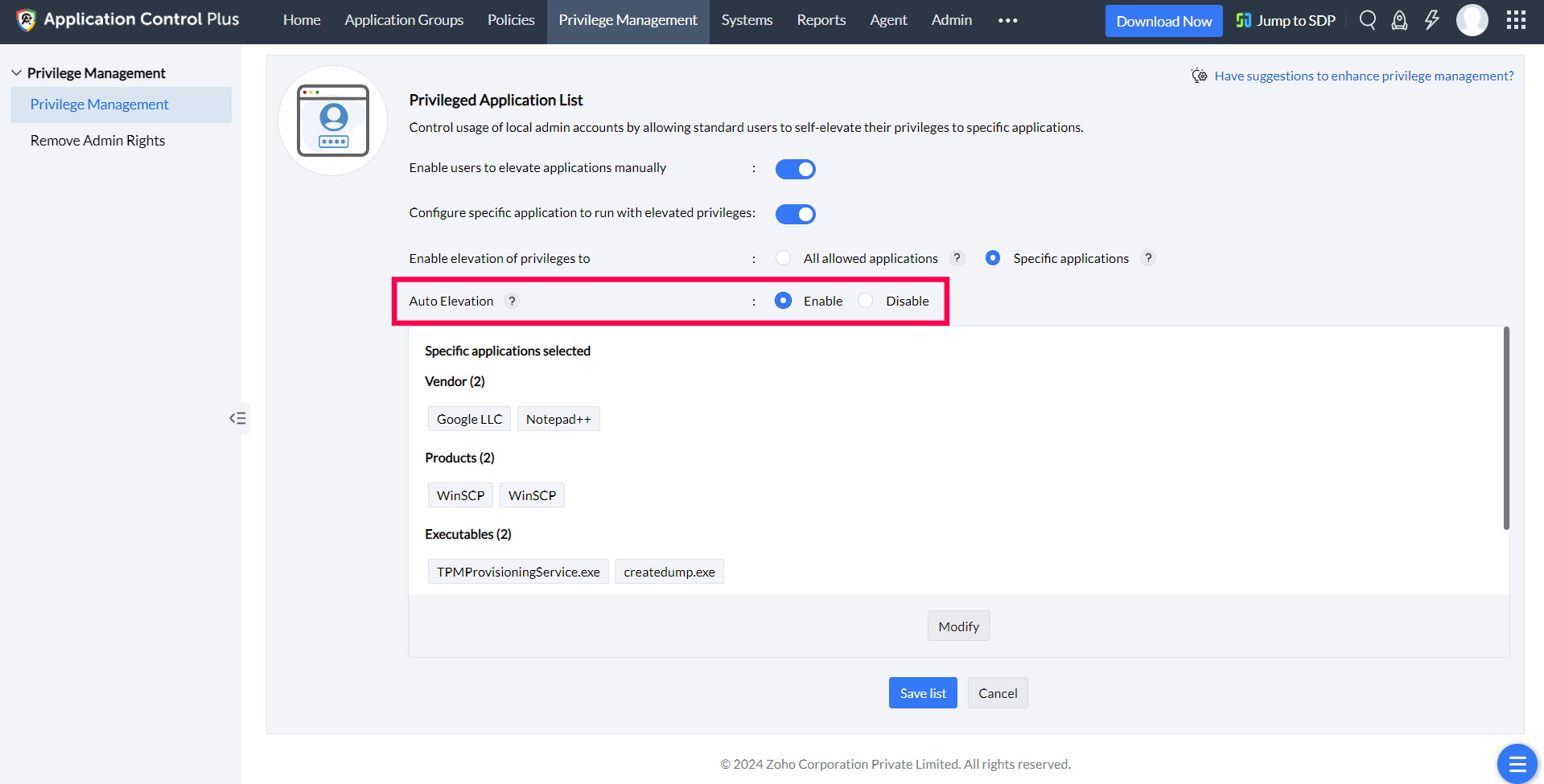
Specific applications can be added into the Privileged Application List based on the enterprise's requirements. Admins can view the existing applications that are running with elevated privileges before they proceed to build this list. This ensures that there won't be any loss of productivity. Once an application has been elevated all the child processes invoked by the application will gain the elevated privilege. Custom Groups associated to the Privileged Application List during policy deployment will be allowed to elevate their privileges only to the specific applications chosen.
Allow auto-elevation of privileges to applications
Custom Groups associated with the Privileged Application list during policy deployment will be allowed to automatically run applications with elevated privileges.
Enable Privileged Access
All end-user devices that need privileged access to applications can be clustered into a Custom Group and associated with the Privileged Application List during policy deployment.
Admins can also both allowlist and blocklist applications with the highest level of security and customization possible. The Just-in-time Access feature gives the admin flexibility to create temporary policies made specifically for interim needs.
Enable Elevation for Control Panel and System Components
Not every administrative task involves a traditional executable. Standard users often need to perform actions like changing network settings or adding printers. These tasks are governed by COM objects rather than .exe files. Granting full local admin rights for these one-off tasks defeats the purpose of least privilege.
Application Control Plus lets you elevate these system components directly using their COM Class ID (CLSID) instead of executable paths, with a pre-populated list of common system components to choose from. For components not in the list, you can also create custom CLSID rules by entering the system component name and its CLSID. Because CLSIDs target registered COM objects directly, this approach offers more precision and stability than path-based rules. Learn how you can configure this.
Try out Application Control Plus, an application control software offering integrated endpoint privilege management solution. Get started now!