What is DNS and why is it used?
The Domain Name System (DNS) is a core component of the internet that translates human-readable domain names into IP addresses. Computers communicate using numerical IP addresses — such as 142.250.80.46 — but users access websites using domain names like google.com. DNS bridges this gap by resolving domain names to their corresponding IP addresses, enabling browsers to locate and load the correct web resources.
DNS operates automatically in the background every time a user accesses a website, sends an email, or uses an internet-connected application. It is a distributed system, meaning the work of resolving domain names is handled by a global network of servers rather than a single central database.
Beyond basic name resolution, DNS plays a significant role in network performance, service availability, and security — making it a critical infrastructure component for organizations of any size.
How DNS works
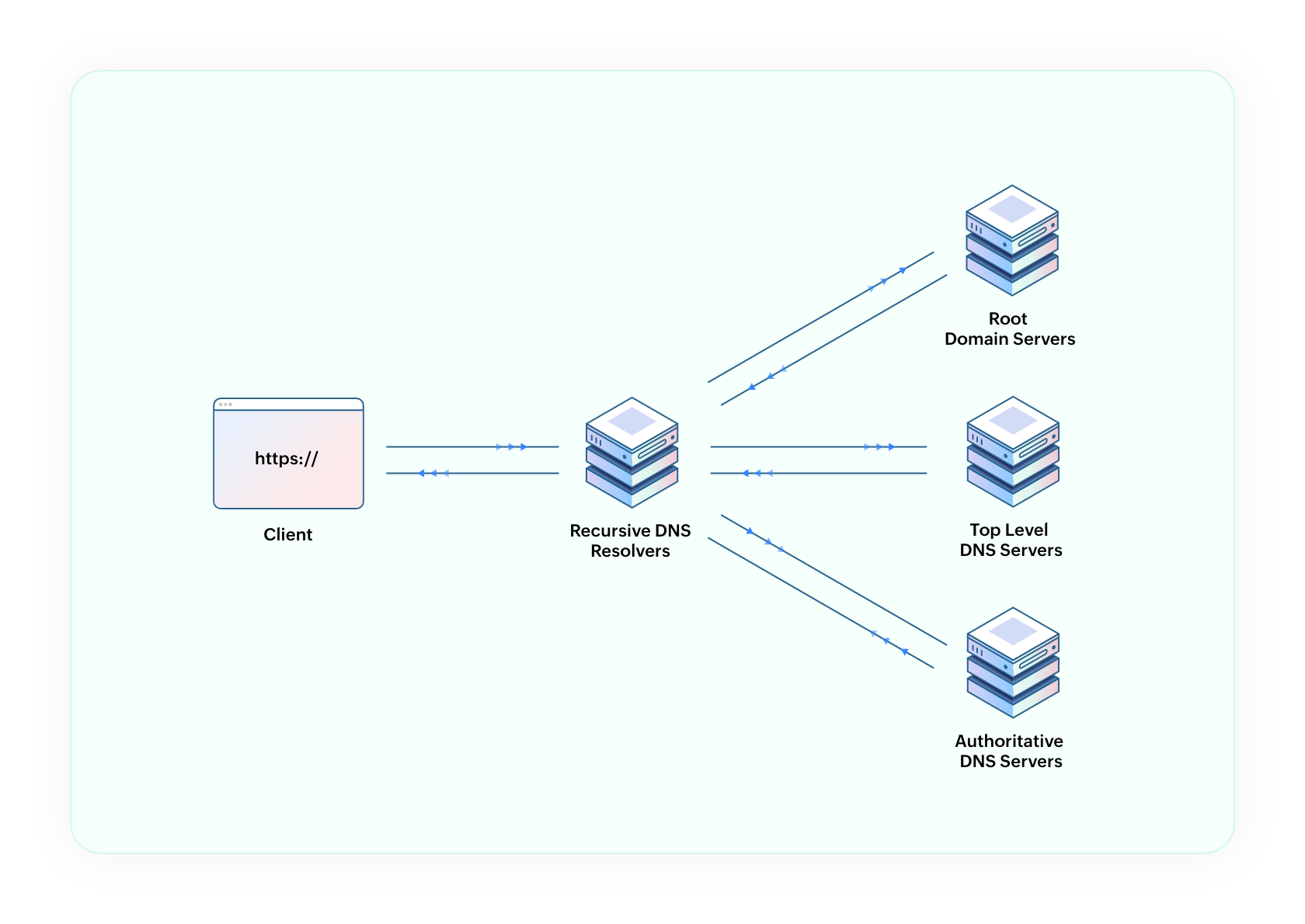
When a user enters a domain name into a browser, a DNS resolution process begins. This process involves multiple servers working in sequence to locate and return the correct IP address. The entire exchange typically completes in milliseconds.
The DNS resolution process
Browser cache check
The browser first checks its local cache for a previously resolved IP address for the requested domain. If a valid cached record exists, the process ends here and the website loads immediately.
Query sent to DNS resolver
If no cached record is found, the request is forwarded to a DNS resolver — typically provided by the user's ISP. The resolver is responsible for completing the lookup on behalf of the client.
Root nameserver contacted
The resolver queries a root nameserver, which does not hold the final IP address but directs the resolver to the appropriate Top-Level Domain (TLD) server based on the domain's extension (e.g., .com, .org, .in).
TLD server queried
The TLD server identifies the authoritative nameserver responsible for the specific domain being requested and directs the resolver accordingly.
Authoritative nameserver returns the IP address
The authoritative nameserver holds the definitive DNS records for the domain. It returns the IP address to the resolver, which passes it back to the browser. The browser then establishes a connection to the web server at that address.
What is a DNS lookup?
A DNS lookup is the complete process of querying the DNS system to resolve a domain name to an IP address. Each lookup may involve multiple queries across several servers, though caching mechanisms reduce the frequency of full lookups for commonly visited domains.
What is DNS caching?
DNS caching is the temporary storage of resolved DNS records by a browser, operating system, or DNS server. Cached records are retained for a duration defined by the record's Time to Live (TTL) value. Caching reduces resolution time for repeat queries.
DNS servers explained
DNS resolution involves four distinct server types, each serving a specific function in the lookup process.
DNS resolver (recursor)
The resolver is the first server to receive a DNS query from a client device. It acts as an intermediary, querying other DNS servers on behalf of the client until the correct IP address is found. DNS resolvers are typically managed by ISPs or third-party DNS providers.
Root nameserver
Root nameservers sit at the top of the DNS hierarchy. There are 13 root nameserver sets distributed globally. They do not resolve domain names directly but direct resolvers to the appropriate TLD server based on the domain extension.
TLD (Top-Level Domain) server
TLD servers manage all domains within a specific extension, such as .com, .org, or country-specific domains like .in. They direct DNS resolvers to the authoritative nameserver for the requested domain.
Authoritative nameserver
The authoritative nameserver is the final authority for a domain's DNS records. It holds the actual IP address and other DNS data for the domain and provides the definitive response to the resolver's query.
Authoritative vs. recursive nameservers: A recursive resolver searches for the answer by querying multiple servers on the client's behalf. An authoritative nameserver holds the answer and provides it directly. Both are essential to the DNS resolution process but serve distinct roles.
What are DNS records?
DNS records are data entries stored within a DNS zone that provide information about a domain. Each record serves a specific purpose — from mapping domain names to IP addresses, to routing email, to verifying domain ownership. DNS records are held on authoritative nameservers and returned in response to DNS queries.
| Record Type | Description |
|---|---|
| A record | Maps a domain name to an IPv4 address. The fundamental record type used by most websites to direct traffic to their server. |
| AAAA record | Maps a domain name to an IPv6 address. Used by networks and services that support the newer IPv6 protocol. |
| CNAME record | Creates an alias from one domain name to another. Commonly used to map subdomains to a root domain without duplicating records. |
| MX record | Specifies the mail server responsible for handling email for a domain. Required for email routing to function correctly. |
| TXT record | Stores arbitrary text data associated with a domain. Widely used for domain verification, email security policies (SPF, DKIM), and ownership confirmation. |
| NS record | Identifies the authoritative nameservers for a domain. NS records determine which servers hold DNS authority for the domain. |
Additional record types — including PTR, SRV, CAA, SPF, and DS — serve specialized functions such as reverse DNS lookups, service discovery, certificate authority authorization, and DNSSEC validation.
What is a DNS zone?
A DNS zone is an administrative segment of the DNS namespace managed by a specific organization or administrator. Each zone contains the DNS records for one or more domains and their subdomains, and is hosted on one or more authoritative nameservers.
For example, an organization managing "companyname.com" would maintain a DNS zone containing all records for that domain and any associated subdomains, such as mail.companyname.com or support.companyname.com. Dividing the DNS namespace into zones allows different administrators to manage separate portions of the hierarchy independently.
What is a DNS zone file?
A DNS zone file is a structured text file stored on an authoritative nameserver that contains all DNS records for a given zone. It serves as the definitive source of DNS data for the domains within that zone. Administrators update zone files when adding new services, changing server locations, or modifying existing records. Changes to a zone file propagate to other DNS servers according to the TTL values defined within it.
DNS security
DNS was designed primarily for functionality, with limited consideration for security. As a result, it is one of the most frequently targeted components of network infrastructure.
Common DNS attacks
DNS spoofing (cache poisoning)
An attacker injects fraudulent DNS records into a resolver's cache, redirecting users to malicious servers. Users visiting a legitimate domain are silently routed to a counterfeit site, where credentials and sensitive data can be harvested.
DNS DDoS attacks
Distributed Denial of Service attacks against DNS infrastructure flood servers with high volumes of requests, degrading or completely preventing resolution for legitimate users.
DNS tunnelling
DNS tunnelling exploits the DNS protocol to encode and transmit data within DNS queries and responses. Since DNS traffic is rarely inspected or blocked by firewalls, attackers use this technique to exfiltrate data.
What is DNSSEC?
DNSSEC (Domain Name System Security Extensions) is a suite of extensions that adds cryptographic authentication to DNS responses. Each DNS record is digitally signed by the zone owner, allowing resolvers to verify that the response received is authentic and has not been modified in transit.
It is important to note that DNSSEC validates the integrity of DNS responses but does not encrypt them. For encryption, protocols such as DNS over HTTPS (DoH) or DNS over TLS (DoT) are used.
DNS filtering and block lists
DNS filtering is a security measure that prevents users and devices from resolving known malicious domains. Organizations configure their DNS resolvers to check incoming queries against a blocklist — a regularly updated list of domains associated with malware, phishing, botnets, or other threats. Queries matching the blocklist are denied resolution before any network connection is established.
Why DNS visibility matters for security
Every device and application on a network generates DNS queries before initiating any connection. This makes DNS traffic a valuable source of security intelligence. By monitoring DNS query logs, security teams can identify compromised devices communicating with malicious domains, detect early indicators of attack activity, and investigate suspicious behavior across the network.
Benefits of DNS
DNS provides several operational and security advantages that extend well beyond basic name resolution. For organizations managing large or complex networks, DNS is a foundational element of performance, availability, and access control.
Faster performance
DNS caching stores resolved records locally, reducing lookup time for frequently accessed domains and improving response speed for end users.
Scalability
DNS records can be added, updated, or removed without disrupting the broader network, making it straightforward to scale infrastructure as requirements change.
Enhanced security
DNS filtering and DNSSEC allow organizations to block malicious domains and verify the integrity of DNS responses at the infrastructure level.
Load distribution
DNS can resolve a single domain to multiple IP addresses, distributing traffic across servers and preventing any single server from becoming a performance bottleneck.
Failover and continuity
DNS failover mechanisms redirect traffic to backup servers automatically when a primary server becomes unavailable, maintaining service continuity during outages.
Access control
Organizations can customize DNS responses to restrict access to specific domains, enforcing acceptable use policies and content filtering at the network level.
Section 08
ManageEngine DDI Central
As networks scale, managing DNS manually becomes increasingly complex and error-prone. A single misconfigured record can cause service disruptions. Unmonitored DNS activity creates security blind spots. Tracking changes across multiple zones and providers lacks consistency without a centralized system. ManageEngine DDI Central provides a unified platform for managing DNS, DHCP, and IP address management (IPAM) — giving IT teams the visibility, control, and automation needed to manage DNS infrastructure reliably and securely.
Real-time DNS visibility and monitoring
Monitor all DNS activity across the network from a centralized dashboard. Track query volumes, identify anomalies, and detect issues before they impact users or services.
DNS threat detection and security
Automatically detect and block malicious domains. DDI Central analyzes DNS traffic for indicators of spoofing, tunneling, and volumetric attack activity, providing security teams with DNS-layer threat intelligence.
Automated DNS management and audit logging
Configure and update DNS records, automate the scavenging of stale entries, and maintain a complete audit log of all changes — including who made them and when. Reduces manual workload and minimizes the risk of configuration errors.
Zone migration and multi-provider support
Manage DNS zones hosted by multiple third-party providers from a single interface. DDI Central simplifies zone migrations and ensures consistent management across distributed DNS environments.
Unified DNS, DHCP, and IPAM
DNS, DHCP, and IP address management are interdependent. DDI Central integrates all three into a single platform, eliminating silos and giving administrators a complete, accurate view of network addressing at all times.
Frequently asked questions
A DNS recursor, also referred to as a DNS resolver, is the server that receives DNS queries from client devices and performs the recursive lookup process. It queries the root nameserver, TLD server, and authoritative nameserver in sequence until it retrieves the correct IP address, then returns the result to the client.
DNS caching is the storage of previously resolved DNS records by a browser, operating system, or DNS server. Cached records are retained for the duration specified by the record's TTL value. Caching reduces resolution latency and decreases the volume of queries sent to upstream DNS servers.
A DNS query is a request sent from a client device to a DNS resolver asking for the IP address associated with a specific domain name. Queries are initiated automatically by browsers and applications whenever a domain name needs to be resolved.
DNS load balancing is a method of distributing network traffic by associating a single domain name with multiple IP addresses. The DNS server cycles through or selects from these addresses when responding to queries, spreading the load across multiple servers and improving availability and performance.
DNSSEC (Domain Name System Security Extensions) is a set of cryptographic protocols that digitally signs DNS records, allowing resolvers to verify that responses are authentic and have not been tampered with. It protects against attacks such as DNS spoofing and cache poisoning by establishing a verifiable chain of trust from the root nameserver to individual domains.
Free DNS servers provide standard name resolution with limited performance tuning and security features, suitable for general consumer use. Paid DNS servers offer enhanced performance through lower latency and higher availability, advanced security capabilities including DDoS protection and threat filtering, customizable DNS responses, and dedicated technical support — making them more appropriate for business and enterprise environments.
Take control of your DNS infrastructure
Try ManageEngine DDI Central and simplify DNS, DHCP, and IP address management from a single platform.
Get started free