Apple App Management
This document explains the various steps involved in managing Store and enterprise Apple Apps. Ensure these ports and domains are allowlisted for managing Apple apps. In case you've already setup ABM in another MDM service, you can migrate it to ME MDM as explained here.
Supported OS:
iOS, tvOS, macOS & iPadOS
Types of Apps supported:
| Platform | VPP Apps | Store Apps |
|---|---|---|
| iOS |  |
 |
| iPadOS |  |
 |
| Shared iPad |  |
 |
| tvOS |  |
 |
| macOS |  |
 |
Note:
Adding apps to app catalog is not supported for macOS.
Managing App Store apps for Apple devices
The App Store has a multitude of apps which include free apps and paid apps. Free apps can be added directly to the App Repository, using the app name or bundle identifier of the app. In case of paid apps, the app licenses need to be purchased as explained in the next section, after which they can be added to the App Repository. To add the apps to the Repository, refer these steps.
App Management and Distribution using ABM
Apple has introduced Apple Business Manager (ABM) and Apple School Manager (ASM) which gives an integrated platform to manage devices and apps in organizations and schools respectively. Volume Purchase Program (Apple VPP) available with ABM and ASM is a free program for managing free and paid Store apps. It simplifies managing apps with Managed Distribution using which the admin can approve licenses on these portals and distribute the apps to devices. These licenses can be revoked and reused if the app is removed from the user's devices. Other advantages include:
- Silent distribution of apps to the devices.
- App installation without associating an Apple ID to devices.
NOTE: The steps for configuring Apple Business Manager mentioned in this document are also applicable for Apple School Manager.
Using ABM, administrators can manage app licenses by assigning or revoking the apps distributed to a user at any point of time and reusing the licenses to distribute the app to another device. This is done by registering the corporate Apple ID to generate a sToken. This sToken should be uploaded in the MDM server. Whenever an app, is purchased using the corporate Apple ID, the license details are synced with the MDM server. You can also manually sync the license details by clicking on Sync License button under the specific app details view.
Ensure the Apple account used for ABM is not associated with any other device.
Purchasing apps
You can purchase licenses in bulk for both free and paid apps, using ABM and then distribute it to the devices. App License(s) refers to the number of devices to which the app needs to be distributed to. For example, if you want to distribute the ME MDM app to 300 devices, you should purchase 300 app licenses.
Note: To migrate unused VPP Redemption codes to Managed Distribution, refer this.
Apps can be purchased through Managed Distribution as explained below.
- Login to ABM portal
- Approve app licenses
- Download server token
- Upload server token in the MDM Web Console
Login to Apple Business Manager Portal
Ensure you use a unique corporate Apple account for ABM and also do not associate this account with any other Apple device.
- Login to ABM portal using your corporate ID.
If you do not have a corporate Apple account for ABM, click on Enroll now, to create an account for your organization. To upgrade your VPP account to the ABM portal and to know more about the upgrade, follow the steps given here.
If you are already using VPP with MDM, MDM automatically migrates your apps to ABM once you have upgraded. Prior to the expiry of the server token, you'll have to renew the token from the ABM portal to continue managing your apps.
Approve app licenses
With ABM, you can approve licenses for free apps and purchase paid apps, for distribution to devices. On the ABM portal, under Content, click on Apps and Books. Search for the required apps and enter the required number of licenses to approve or purchase. Once ABM is set up, MDM syncs with ABM every day, to automatically add any new purchases to MDM. You can also navigate to the App Repository, click the Sync Apps button and choose Sync ABM Apps to manually sync the apps with MDM
- To know more about distributing unlisted iOS apps to devices, refer here.
- Apple currently doesn't permit in-app purchases on apps added using ABM.
Download Server Token
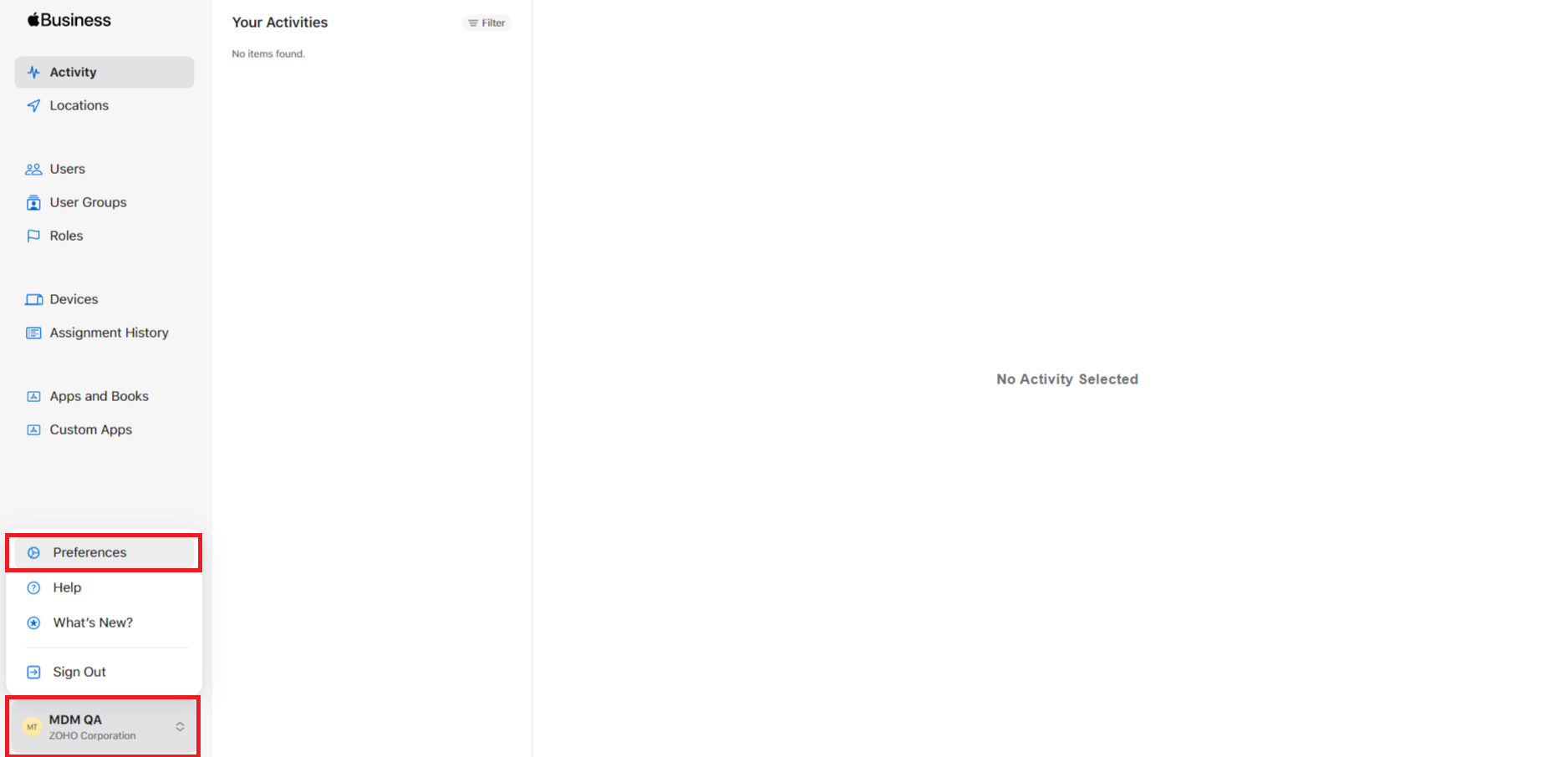
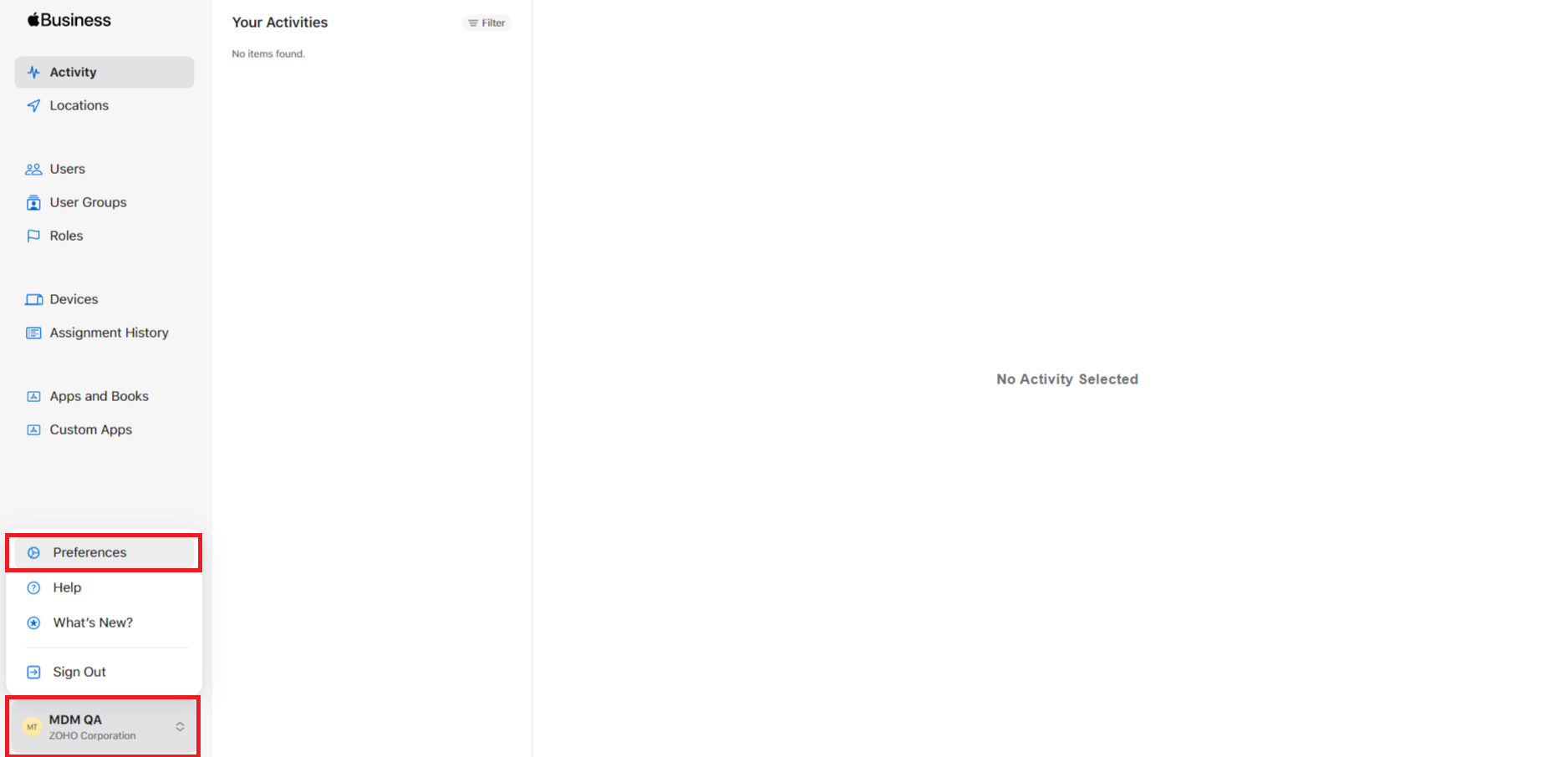
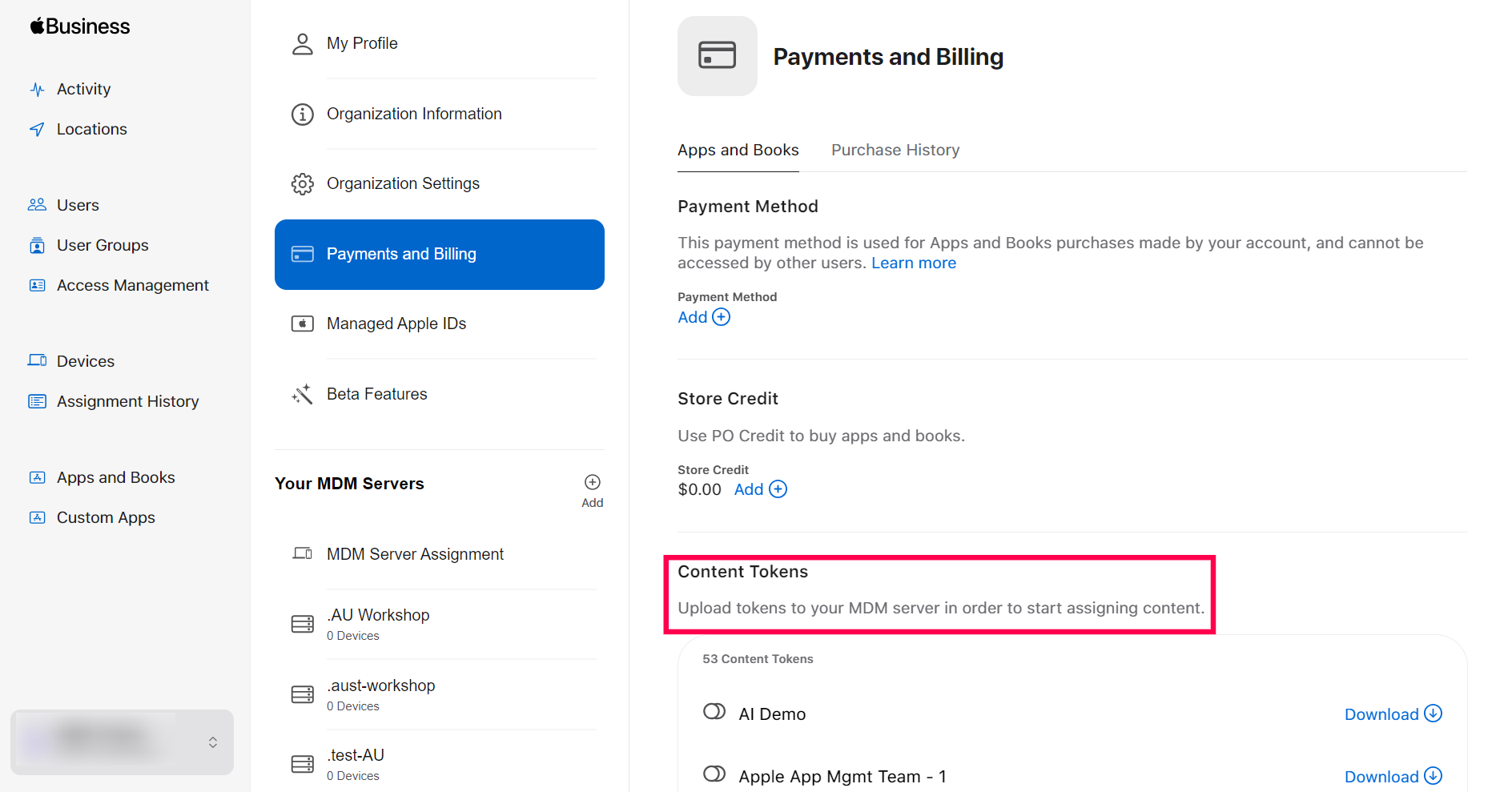
- On the ABM portal, click on your account on the bottom left corner and select Preferences.
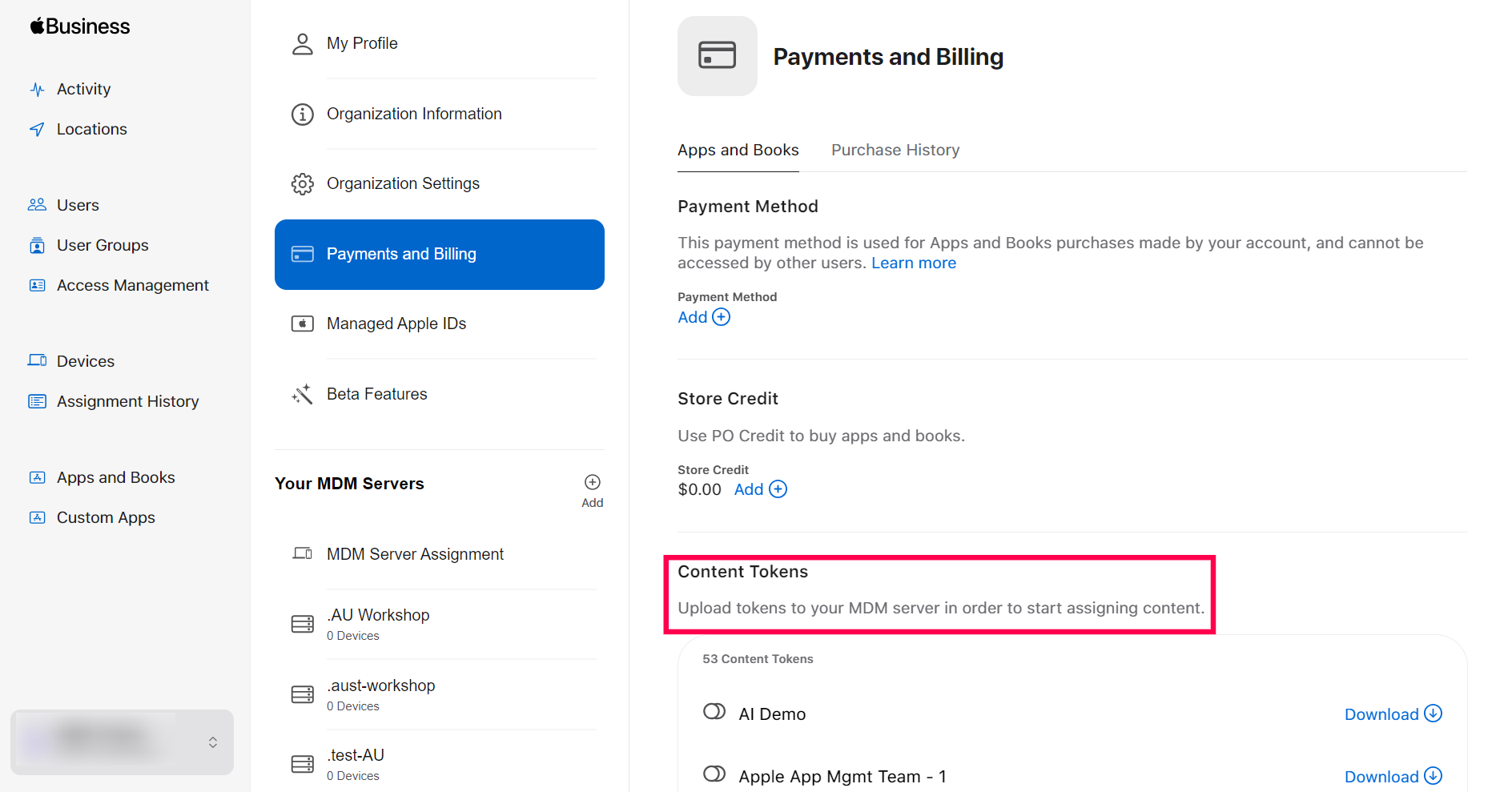
- Click on Payments and Billing > Apps and Books > Server Tokens and click Download on the server token to be downloaded.
- Download the required server token.
Upload Server Token on MDM console
Follow the steps mentioned below to upload the sToken in the MDM server:
- On the web console, select App Repository.
- Click on Apple App Management.
- Upload Server Token.
- Provide your e-mail address to receive notifications prior to the expiry of the server token.
- Click Save to complete the process.
You have successfully created/renewed the server token on the MDM server. You can now distribute apps to the managed devices, assign or revoke licenses as per your requirement.
Managing multiple location tokens
You can also upload multiple location tokens on the MDM console to manage department or location specific app purchases. To upload new tokens, navigate to App Repository -> Apple App Management -> Add Location Token -> Upload Token. Once uploaded, MDM will sync the apps added to the location token via ABM.
Note: If you need to add a new location in ABM portal, go to Locations and click on Add a new location. It is recommended to give the location a descriptive name, for easier identification purposes.
Each location token is valid for one year. When nearing expiration, it is essential that the token is renewed to distribute apps using the location tokens. You can renew the location token by logging in to ABM, downloading the location token again and uploading the token back in MDM by following the same steps as mentioned above.
If the location token is already in use,
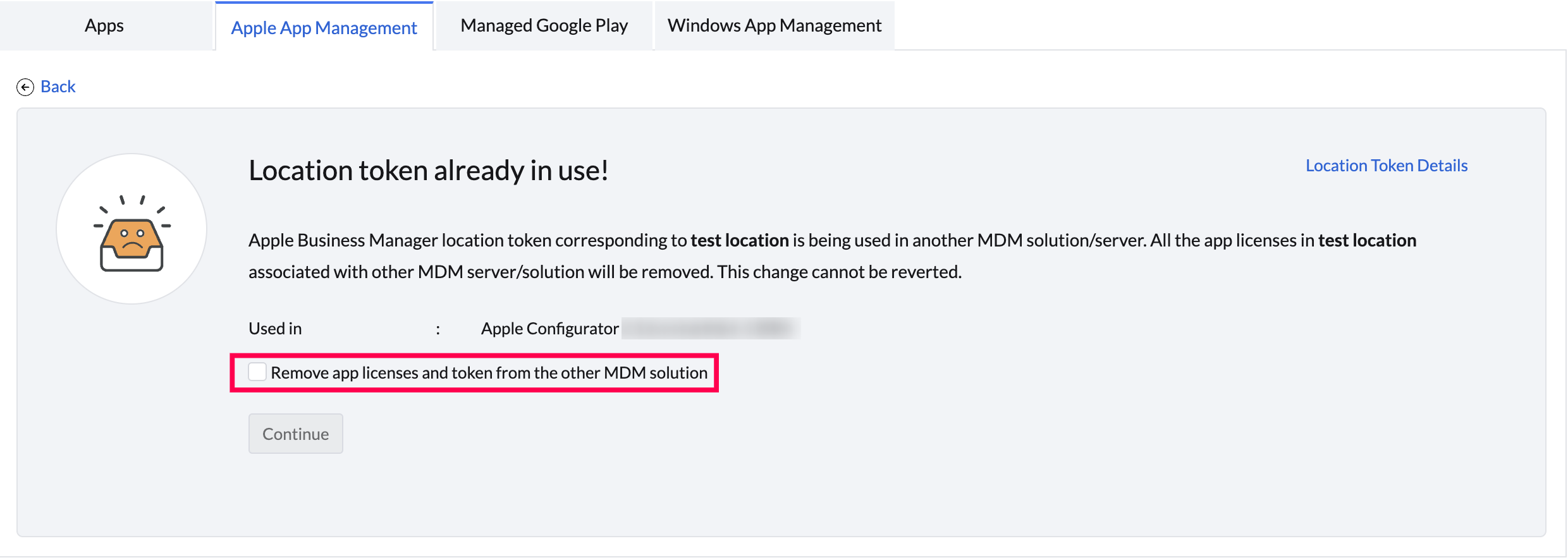
- When the VPP token is used in another MDM Server: If the same token is uploaded and synced with other MDM Server then a prompt will be shown saying the token had already been used in another MDM Server, checking the box will remove the app licenses linked with other the MDM server too.
- When the VPP token is used in Apple Configurator: If the user signs into the Apple Configurator using the Apple ID and syncs the apps of VPP token then a prompt will be shown saying the token had already been used in another MDM Server. Checking the box will remove associated license from Apple Configurator and sync in the present MDM Server.
Note: While distributing apps via Apple Configurator, it is suggested to create and maintain a separate VPP token.
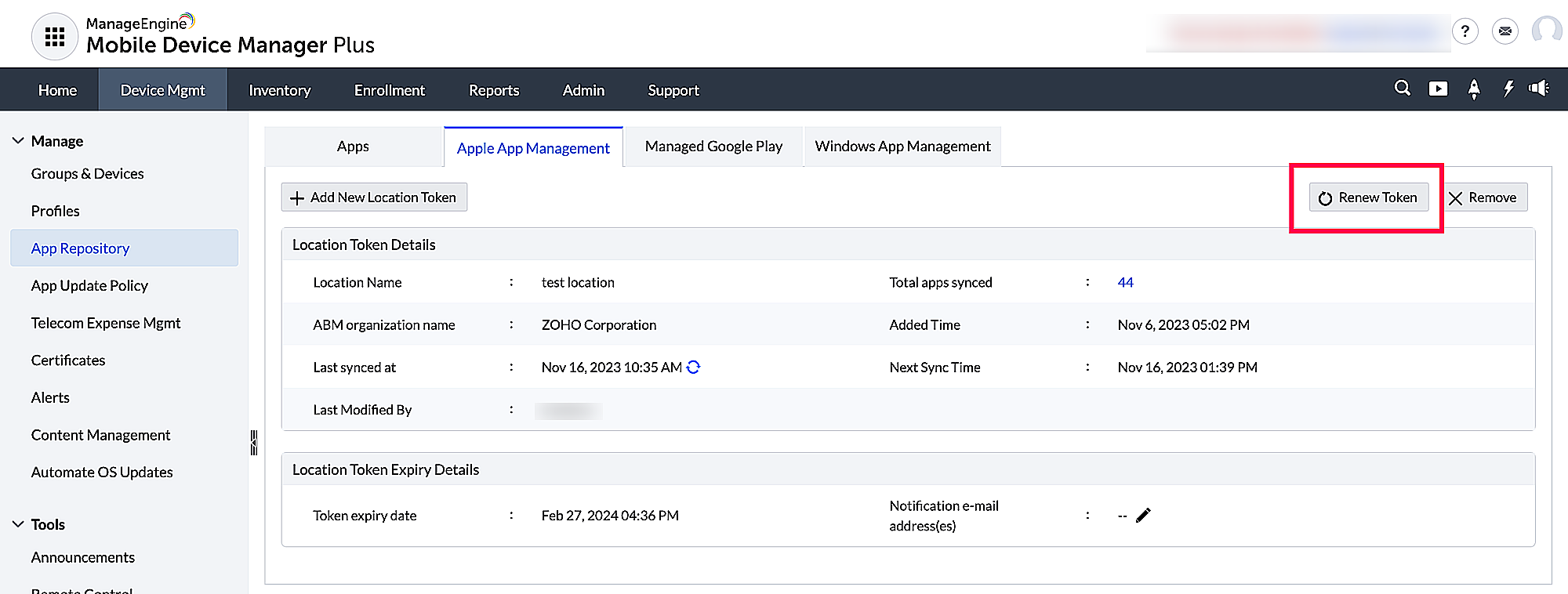
Renewing the location token
The location token is valid for one year. You can renew the token by downloading the token from the ABM portal and uploading them in the MDM server. Follow the steps below to renew the token.
- On the ABM portal, click on your account on the bottom left corner and select Preferences.
- Click on Payments and Billing > Apps and Books >Server Tokens and download the server token that has to be renewed.
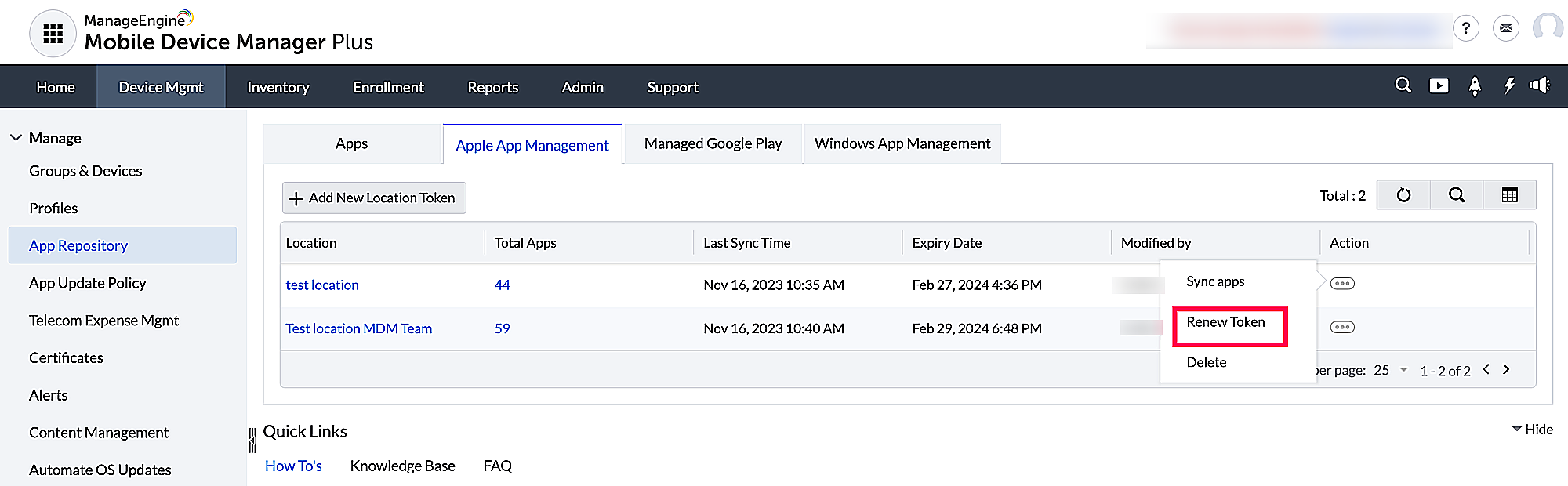
- To upload the location token on the MDM server, go to Device Management -> App repository ->Apple app management . Choose the required location token and click on Renew Token.
- If multiple location tokens are present on the MDM server, click on the token to be renewed, choose Actions and Renew Token.
Removing server token
The server token associated with the MDM server can be removed by navigating to App Repository ->Apple Business Manager ->Remove. On removing the server token from MDM server, all the apps synced from MDM are moved to Trash. Further, the apps synced from ABM and distributed to the devices are removed from the devices as well. On moving these back to App Repository from Trash, they'll be considered as normal apps added to App Repository via the App Store.
App Installation
The app is associated with the device instead of the user's Apple ID. This lets you install apps without the Apple ID on devices. Additionally, if the devices are Supervised you can install apps silently on the devices. The approved licenses are counted based on the number of devices the app has been distributed to. For example, if you distribute the app to 5 devices, 5 licenses are used.
Distributing ME MDM app silently to managed devices
ME MDM app must be installed on managed Apple devices to locate the devices, detect jail-broken devices, and for various other features. Using ABM, ME MDM app can be purchased, distributed to devices and installed silently on Supervised devices, and without requiring an Apple ID in Non-Supervised devices.
Updating Apple Apps
It is also important for the IT administrator to ensure the apps distributed stay up to date with all the critical updates installed on time. If the apps are distributed to the devices using ABM, then the App Store is completely in the control of the IT administrator, and the updates are not available to the user on the devices directly. Hence, the admin has to distribute these updates to the devices to make them available to the user.
Follow the steps given here to distribute app updates to devices.
App Configurations
MDM lets you modify the configurations of the app to be distributed to the device, effectively restricting the capabilities and features of the app. App Configurations lets you customize the apps to suit the needs of the organization. You can also secure devices by restricting apps from accessing data and/or resources of the managed devices. The app developer names and specifies a set of configurations as an XML file, which is uploaded to the MDMserver and is automatically pushed along with the app. The app developer must support app configurations for the app, to implement it using MDM.
Follow the steps given below to apply app configurations:
- Click on App Repository from the Device Mgmt tab.
- Select the app from the repository or add the app.
- Click on the ellipsis button under Action and select Modify App for existing apps. For new apps, you can directly upload the XML file with the required configurations under the Configurations section.
- Save the changes.
Pushing app configurations based on user-specific/device-specific parameters such as e-mail, UDID etc., to different users can be a cumbersome task as the app configuration needs to be modified every time before it is pushed. However, MDM supports dynamic variables which ensure once the app configurations with user-specific/device-specific parameters are setup using dynamic variables, they needn't be configured again as the dynamic variables fetch all the required data from the enrollment details.
Here is the table of parameters for which MDM supports dynamic variables:
| PARAMETER | DYNAMIC VARIABLE |
|---|---|
| Device UDID | %udid% |
| Device Name | %devicename% |
| User Name | %username% |
| %email% | |
| Domain name | %domainname% |
| Serial Number | %serialnumber% |
| IMEI | %imei% |
| Exchange ID | %easid% |
Sample XML file
The app configuration file is an XML file which contains details regarding the configurations supported by the app. A sample XML file is shown below:
|
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<key>serverURL</key>
<string>myServerUrl.myDomain.com</string>
<key>username</key>
<string>%username%</string>
<key>domain</key>
<string>%domainname%</string>
<key>email</key>
<string>%email%</string>
</dict>
</plist>
|
To meet your organizational needs, you can create app configurations for the following applications.
App Policies
MDM lets you to modify the App policies for App Store and Enterprise apps. App policies are helpful in protecting the corporate app data when the MDM profile is removed from the device or when you migrate from one MDM server to another etc.
MDM allows you to configure the following app policies:
- Remove app on MDM profile removal: When this option is enabled, all the apps distributed via MDM will be automatically removed from the device, when the MDM profile is removed.
- Restrict backup for app data in iTunes and iCloud:You can protect the app data by restricting users from taking backup on their iTunes and iCloud account.
Note: If you modify these app policies after distributing the app,
- Devices with the latest version of app installed on them will be automatically updated with the modified app policies.
- Devices with the lower version of app installed on them will not get the modified app policies updated until the devices are updated with the latest version.
Enterprise apps for Apple
Enterprise apps are also called as in-house apps. Enterprise apps are those which are specific to an organization and are used internally. These apps are owned by the company and are not listed in the App Store. Enterprise apps are commonly a collection of computer programs with business applications or tools for modeling the organizational work. These apps are developed exclusively for distinguished platforms, like Apple & Android. Refer to this, to know more about adding enterprise Apps in the App repository and installing them on devices without user intervention. To test and deploy Apple enterprise apps seamlessly using multi app version management refer to this link.
Steps for silent installation of enterprise apps:
- Ensure https://ppq.apple.com is allowlisted on your external firewall to ensure the added enterprise apps are trusted on the device.
- Enterprise apps distributed by MDM, (including the ME MDM app) need to be verified by ppq.apple.com only once. They do not need to be re-verified by the user each time the device connects to the Internet.
Any enterprise app added to the App Repository and associated to devices, gets automatically trusted and does not require the user to manually trust the app on the device.
Custom apps for Apple
Custom apps are tailor-made apps developed to specifically cater to the needs of an organization. The basic difference between enterprise apps and Custom apps is, the former is developed in-house while the latter usually involves third-party developers. Further, Custom apps are provided only through ABM, so your organization must have an ABM account. To know more about Custom apps, refer this.
Provisioning Profiles for iOS Enterprise Apps
What is a provisioning profile?
A provisioning profile is a collection of digital entities that uniquely ties developers and devices to an authorized iPhone Development Team and enables a device to be used for testing.
Why provisioning profiles?
Unlike Android, you can’t install any app on an iOS device. It has to be signed by Apple first. However, when you’re developing an app, you probably want to test it before sending it to Apple for approval. Provisioning profile act as a link between the device and the developer account. During development, you choose which devices can run your app and which app services your app can access. A provisioning profile is downloaded from your developer account and embedded in the app bundle, and the entire bundle is code-signed. A Development Provisioning Profile must be installed on each device on which you wish to run your application code. If the information in the provisioning profile doesn’t match certain criteria, your app won’t launch.
Types of provisioning profiles:
There are several types of iOS app provisioning profiles, each serving a different purpose. Here are the most common types:
- Development Provisioning Profile: This profile is used during the development phase of an app. It allows you to install and run your app on physical devices for testing purposes. It is typically associated with a specific set of devices and tied to a development certificate.
- Ad-Hoc Provisioning Profile: An ad hoc provisioning profile allows you to distribute your app to a limited number of specified devices for testing outside the App Store. It is useful for beta testing or sharing the app with a select group of users. Ad hoc profiles are associated with a distribution certificate and require the UDIDs (Unique Device Identifiers) of the target devices.
- In-House Provisioning Profile: This type of provisioning profile is used when developing apps for in-house or enterprise distribution within an organization. It allows you to distribute apps to devices within your organization without going through the App Store. In-house provisioning profiles are associated with an enterprise distribution certificate.
- App Store Provisioning Profile: This profile is required for distributing your app on the App Store. It is associated with a distribution certificate and is used to sign your app for submission to Apple's review process. App Store provisioning profiles allow you to reach a broader audience by making your app available to users worldwide.
- MDM server is not able to contact ABM to sync apps.
Check if vpp.itunes.apple.com is allowlisted along with other domains and ports listed here. Ideally, it is recommended to Allowlist *.apple.com for seamless management of Apple devices. Also, verify the availability of the required Apple services.
- Info.plist not found
- An SSL error has occurred and a secure connection to the server cannot be made.
In MDM, uploading enterprise apps build with Development/In-house/Ad-Hoc provisioning profiles is only possible.
For an app to be installed in all compatible Apple Devices, without registering their UDIDs like Ad-hoc and Development provisioning profiles, the In-house provisioning profile must be used. To create an In-house provisioning profile, one must have been enrolled in Apple Developer Enterprise Program.
iOS app management
Apps can be installed, updated, managed, and uninstalled on iOS devices using the above specified methods.
Troubleshooting Tips
While trying to upload an enterprise app, you receive the error message Info.plist not found. This error occurs when the .ipa file is extracted from an invalid source. Contact your developer to get the valid .ipa file.
This error happens due to network failure. Ensure that you have a stable network connectivity throughout the app distribution.
