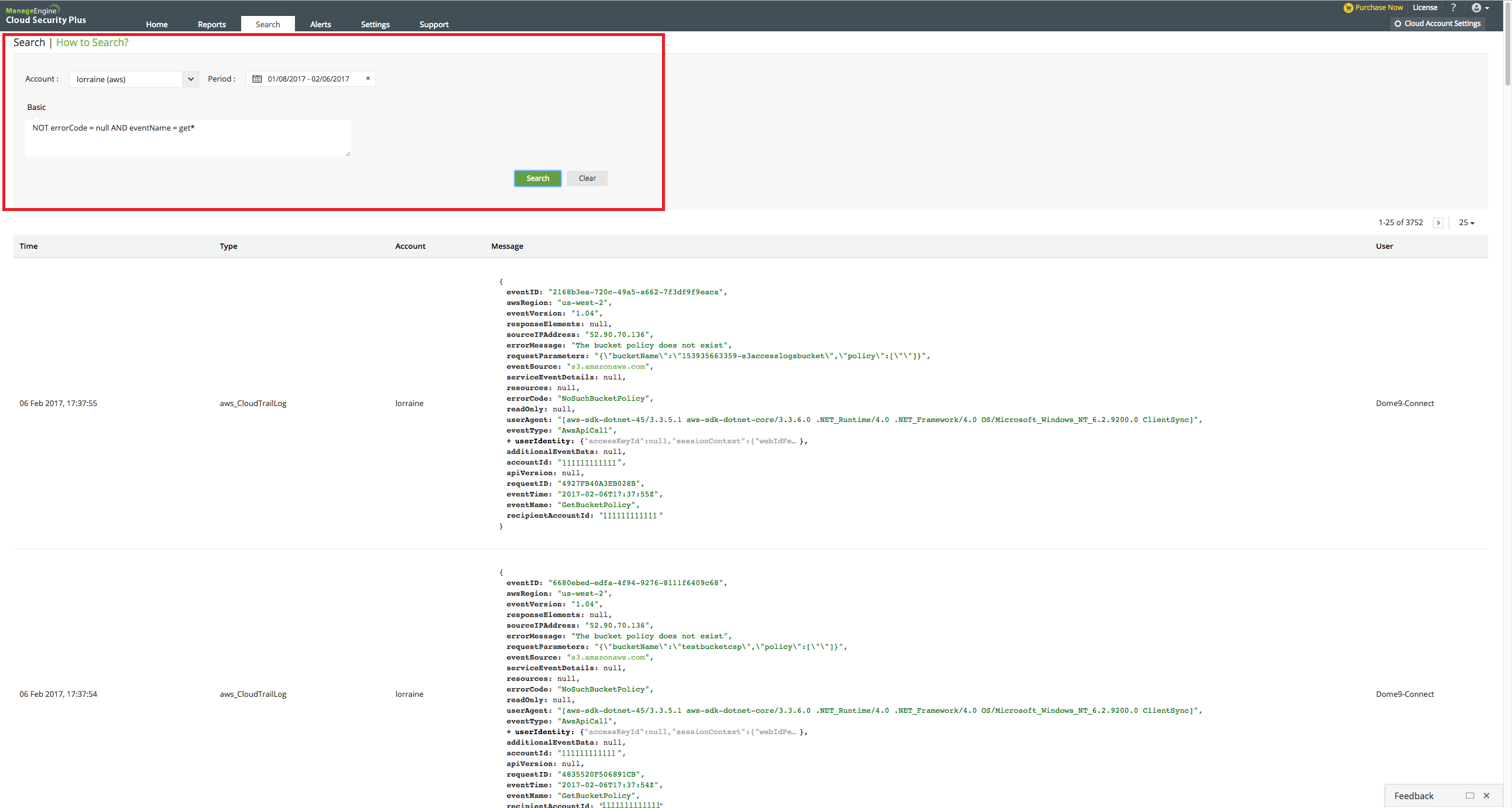
Cloud Security Plus enables you to search the log data collected from your cloud account.
Steps to perform a search:
- From the drop-down list, choose the cloud account whose logs you wish to search.
- Select the specific time period.
- In the provided space, enter the search term.
- Click on “Search.”
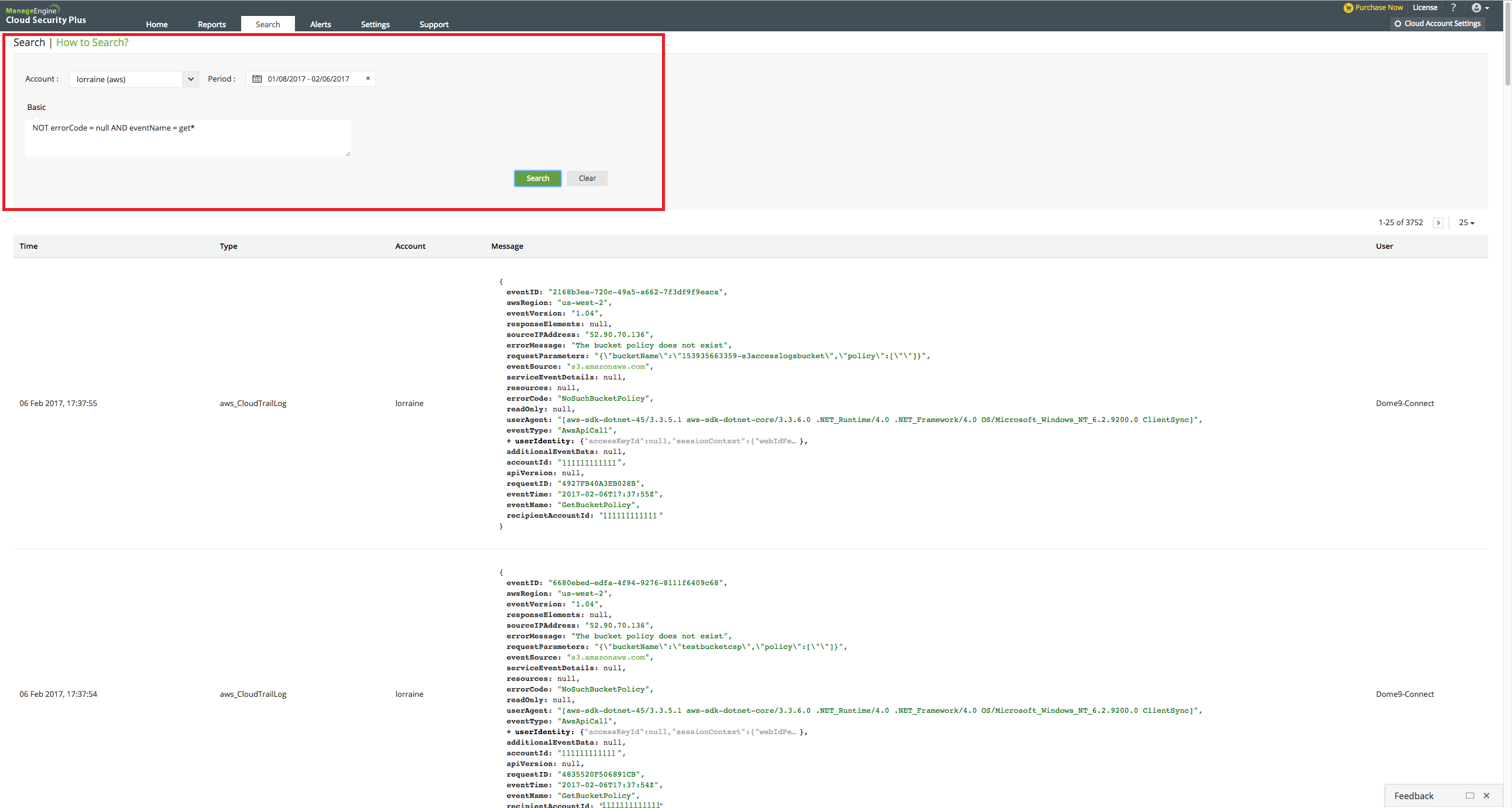
Search terms:
- Specific field search: Type the field name followed by = and then the term you are looking for. Example: eventName = ConsoleLogin
- Multiple character wildcard search: Use the " * " symbol. Example: To list all the "describe" events, enter eventName = Describe*
- hrase searches: Enclose the phrase in double quotes.
- Boolean searches: Use the operators AND, OR, NOT. Example: To list all the successful events enter NOT errorCode = null
- Grouped searches: To list all the successful update events enter NOT errorCode = null AND (eventName = add* OR eventName = put* OR eventName = update*)
- Range searches: Search for a range of values using square brackets. Example: bytesSent = [ 2000 TO 3000 ] will return all the logs (S3 server access) with 'Bytes sent' between 2000 and 3000.