×![]()
×
×![]()
×
×
Device Control Trusted Devices
"Trusted Devices" is a list of approved peripheral devices within the organization’s network considered secure for accessing and handcsvling sensitive data.
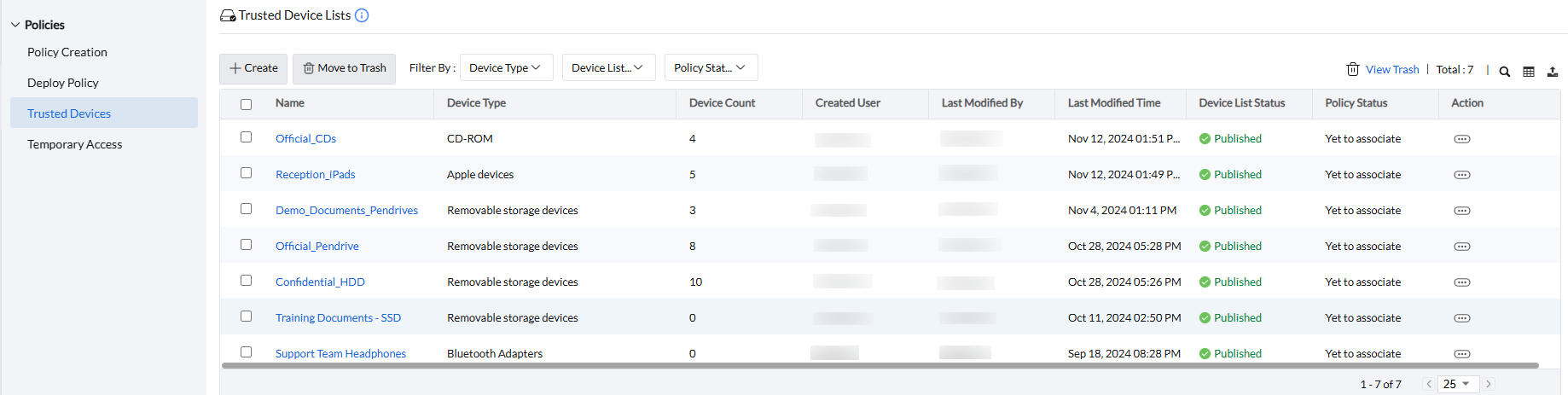
To create a Trusted Devices list, Navigate to Policies -> Trusted Devices -> Create.
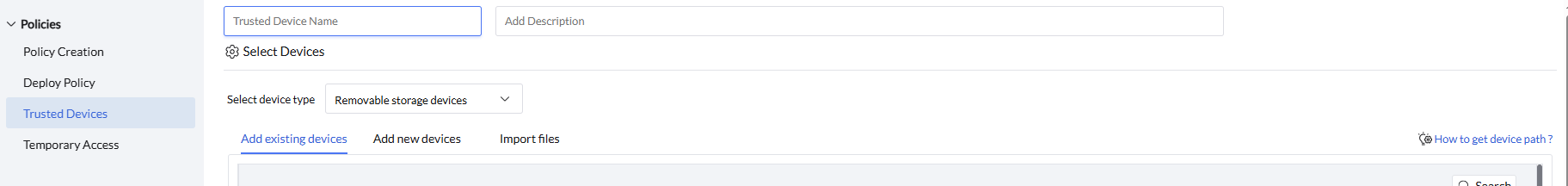
- Policy name:
Enter a name for the Device list to be created. - Description (optional):
Add a description to clarify the device list's purpose.
There are three ways to create a device list:
Add Existing Devices
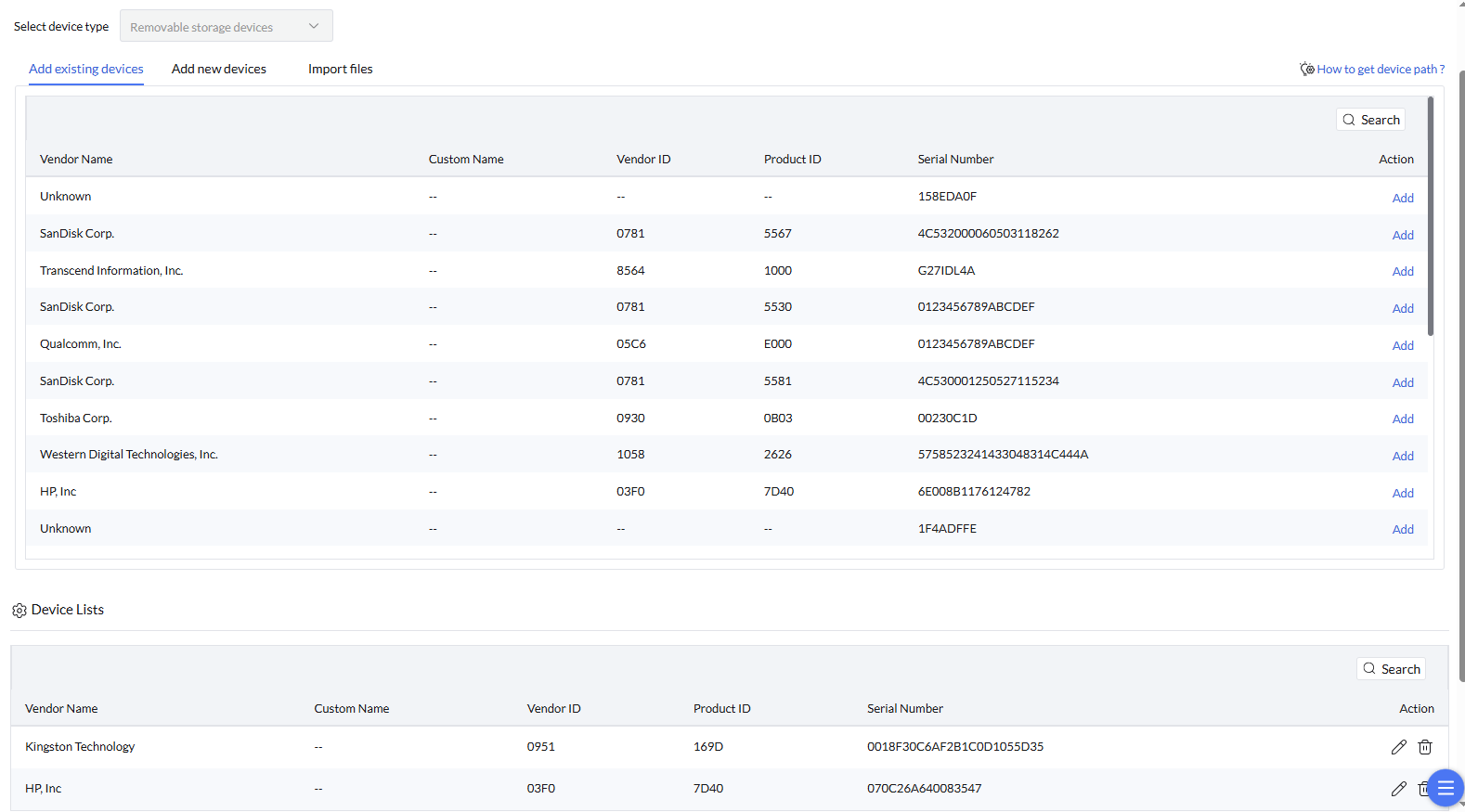
Add Existing Devices allows the admin to select devices already recognized within the network, simplifying the process of building a trusted device list.
- Select the device type
- From the list of recognized devices, click on "Add" to include the device in the device list.
- Click on "Save" to confirm and store the device list.
Add New Devices
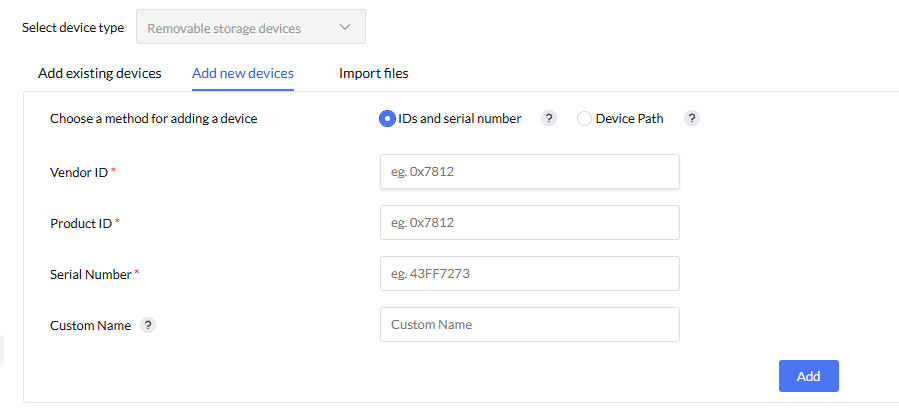
- Select the device type
- Choose a method for adding a device: you can add a device using its ID and serial number, or by specifying the device path.
- For "IDs and Serial Number": Enter the Vendor ID, Product ID, and Serial Number.
- For "Device Path": Enter Parent device instance path and the device instance path
- Enter a custom name for the new device.
- Click "Add" to include the device in the device list and then click "Save"
To learn about how to get device paths, IDs, and serial numbers, Click here.
Add Trusted Devices using Wildcard Pattern
Instead of specifying individual devices, use a common wildcard pattern to trust an entire group of similar devices.
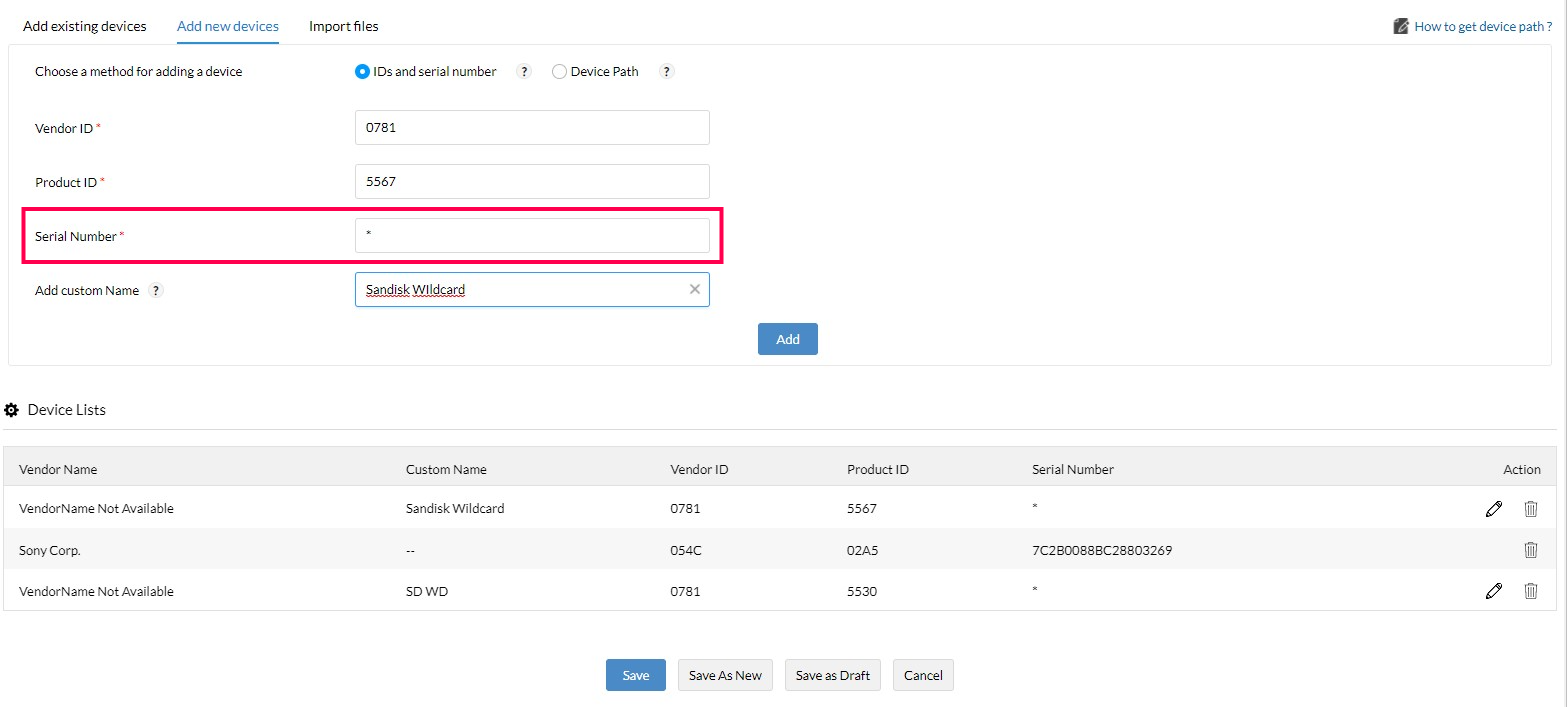
To create a Wildcard pattern:
- Navigate to Policies -> Trusted devices -> Create New -> Add New Devices.
- Choose ID's and Serial Number method
- Provide the Product and Vendor ID, and then specify the wildcard pattern "*" and "?" for Serial Number and Click "Add".
Note
Use '?' to replace a single variable character.
Use '*' to replace more than one variable character.
Use '*' to replace more than one variable character.
Import files
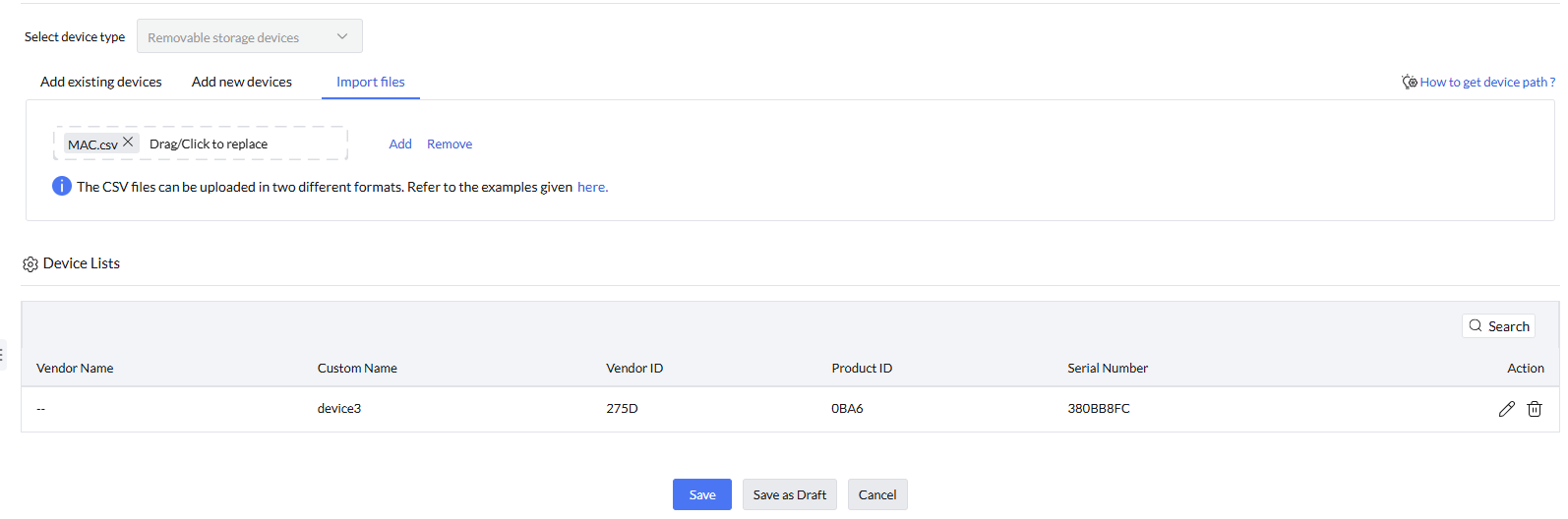
- Select the device type
- Select the CSV file containing trusted devices data and click "Add"
CSV files can be uploaded in two supported formats. Refer to the format examples provided here. - Once devices are added to the list, click Save to confirm and store the changes.