- Overview
- Features
- Solution
- Case studies
- Next step
Overview
Protecting patient data and streamlining IT care
In today's healthcare landscape, the digital transformation has led to a significant shift towards online access for medical care and information. This transformation to a digitally interconnected industry has brought numerous complex IAM challenges.
One of these challenges revolves around managing identities and access privileges for various user groups, including patients, clinicians, researchers, and third parties. These are all essential for healthcare organizations. Addressing secure access for remote healthcare services, while adhering to strict regulations like HIPAA and HITECH, and effectively managing temporary access requirements remains an ongoing challenge. Furthermore, the necessity for patient engagement and privacy protection adds complexity to the IAM landscape within healthcare.
Navigate the Future of Access Management
Watch the discussion between ManageEngine and KuppingerCole for a holistic view of access management in the age of hybrid identity and AI agents.
Watch on demandFeatures
Streamline third-party accessFacilitating secure, controlled access for external partners, including insurance companies and laboratories, is essential within the healthcare sector. Different positions require varying levels of access to internal systems and patient data. AD360 streamlines the approval workflow, ensuring that all requests for creations, modifications, and access undergo thorough supervision before approval. This effectively prevents unauthorized changes.
- Build a customized workflow structure within the healthcare organization, incorporating roles such as requesters, reviewers, approvers, and executors. This structure should be aligned with the healthcare provider's operational needs and patient care standards.
- Enable real-time notifications for healthcare staff via email during critical task execution, including patient account updates and access permission changes. This facilitates seamless communication across various healthcare departments, ensuring effective patient care and streamlined healthcare governance.
- Develop automated workflows in healthcare systems by utilizing orchestration actions, webhooks, and customizable notification templates. Customize scripts for health data processing and integrate clinical administrative actions seamlessly with a user-friendly, drag-and-drop interface.
Patients and healthcare professionals often send emails for password resets and account changes, resulting in delays as admins struggle to resolve these tickets promptly. In addition, frequent account lockouts frustrate clinicians, partners, and patients. Using AD360, healthcare staff and patients can manage passwords, unlock accounts, and update personal information on their own.
- Enable convenient password resets and account unlocks for healthcare staff and patients by integrating a Password Reset or Account Unlock option in the login interface.
- Easily update locally stored credentials following a remote password reset, ensuring uninterrupted access to patient data and critical healthcare systems.
- Implement conditional access to ensure that only verified users, such as medical professionals or registered patients, can modify their passwords and update their personal information in the system directories.
- Provide SSO access to multiple healthcare applications, simplifying healthcare authentication. Eliminate the need for multiple login credentials, enhancing accessibility and productivity in healthcare.
The healthcare sector hires temporary staff, such as traveling nurses and visiting physicians, to address staffing shortages. An increase in joiners, movers, and leavers will impact patient care and increase cybersecurity risks if not handled properly. In addition, clinicians may move between departments or roles and require different access levels. AD360 allows admins to easily update and manage user roles and permissions. This ensures that every user has access to the resources they need while maintaining organizational security.
- Provide access permissions to temporary accounts, such as consultants, contractors, and temporary healthcare staff to ensure they can access necessary medical and administrative systems within the specified time frame.
- Regularly assess and adjust access levels for contractors and temporary healthcare staff, ensuring they have the appropriate level of system entry to perform their duties effectively. All while maintaining the security and confidentiality of patient data.
- Easily manage temporary access rights for contractors and other temporary users in healthcare, enabling healthcare institutions to efficiently handle access provisioning and deprovisioning processes.
Healthcare organizations store a vast amount of sensitive data, including patient information, hospital records, insurance details, biomedical research findings, and medical test results. This attracts cybercriminals who profit by stealing and selling this data on the dark web. With AD360, users must verify their identity before gaining access using adaptive MFA.
- Implement adaptive MFA in healthcare IT systems to fortify the security of Windows, macOS, Linux, VPN, and OWA logins, ensuring robust protection of sensitive patient information.
- Customize authentication methods in healthcare settings based on the user's behavior, location, and device.
- Enforce password policies to meet healthcare sector standards: limit character repetition, avoid dictionary words, prohibit palindromes, and include complex requirements for data security and patient confidentiality.
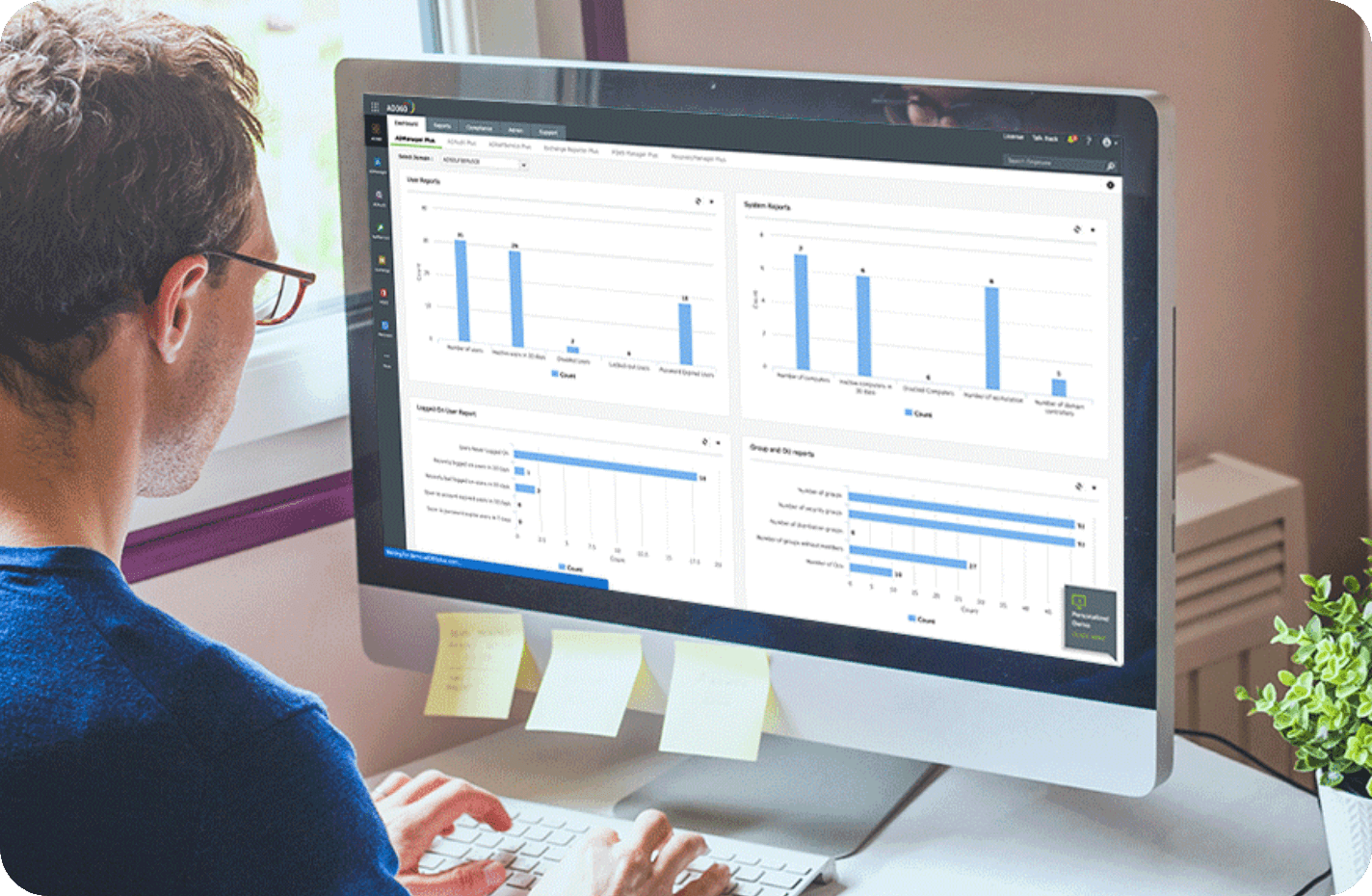
Maintaining compliance is paramount in healthcare, particularly with the stringent HIPAA and HITECH regulations governing ePHI protection. Many organizations grapple with the complexities of achieving HIPAA compliance, as evidenced by over $84 million in fines over the past five years. AD360 offers a streamlined solution with out-of-the-box reports, making HIPAA and HITECH compliance easily attainable for healthcare organizations.
- Simplify compliance management in healthcare with tailored reporting templates, easing the tracking of industry-specific regulations, and enhancing patient data protection.
- Export over 150 pre-installed reports specific to your healthcare organization's AD infrastructure, from login and folder permission reports to group membership insights, enhancing data visibility and control.
- Stay healthcare-compliant by continuously monitoring and receiving real-time alerts, allowing proactive responses to potential breaches or regulatory issues and bolstering patient and staff information security.
Solution
Enhance patient data security
Implement robust security measures, including MFA and role-based access control, to ensure that sensitive patient data is accessible only to authorized personnel. This is crucial for HIPAA and HITECH compliance.
Secure remote access
IAM solutions enable secure remote access to healthcare systems, which is vital for telehealth and remote services, while maintaining data security and privacy.
Improve compliance
Automate identity management processes such as user provisioning and deprovisioning to save time and resources for healthcare providers and allow healthcare staff to focus more on patient care and less on administrative tasks.
Enable SSO for healthcare
Provide healthcare professionals with access to multiple applications and databases through SSO, streamlining workflows and improving the user experience.
Empower self-service capabilities
Allow healthcare professionals to reset passwords independently or manage account aspects, reducing IT support's reliance on routine tasks.
Case studies
East and North Herts CCG enhances security compliance with AD360
East and North Hertfordshire NHS Trust offers a wide range of general and specialist healthcare services. Notable for its top cancer treatment center and childbirth services, it treats around 500,000 patients annually with a commitment to excellence.
"[AD360 is] a great solution, well worth the money we pay compared to other solutions out there."
- Callixtus Muanya, Windows administratorBusiness challenges
The company needed a solution to track Active Directory (AD) changes, which is a stringent security compliance mandate across the UK healthcare industry standards.
How AD360 helped
The organization recognized the AD auditing solution of AD360 as a solution that fits its IT requirements, considering its ease of use, configuration, and maintenance.
The NHS organization found the comprehensive reports offered by AD360 highly valuable and effective, and appreciated how easy it was to generate the existing ones and create custom ones.
Read the full storyAdaptimmune secures critical business data with AD360
Adaptimmune Therapeutics is a biopharmaceutical company that specializes in T-cell therapy and the development of pioneering cancer immunotherapy products.
Business challenges
Adaptimmune handles a large amount of confidential data regarding research, drug composition, intellectual property, patient data collected for drug trials, and more in its Microsoft 365 setup. Without a secure system in place, the company runs the risk of data breaches that could cause huge financial losses and long-lasting damage to its reputation.
How AD360 helped
Adaptimmune's search for an Microsoft 365 auditing tool ended with Microsoft 365 management module for AD360.
The Microsoft 365 audit and monitoring report scheduler of AD360 helped Adaptimmune's sysadmins receive reports directly in their inbox. AD360's reporting and content search capabilities helped its IT teams save valuable time while looking for compliance breaches and security threats.
Read the full storyAD360 helps CAMH annually save thousands of dollars spent on IT helpdesk calls
Centre for Addiction and Mental Health (CAMH) is Canada's largest mental health and addiction teaching hospital, as well as one of the world's leading research centers in the area of behavioral health.
"CAMH will be able to save close to $26,000 a year on service desk calls related to active directory password resets and locked accounts, and will see a return on investment within the first six months of product implementation"
Business challenges
The majority of CAMH’s IT services, including assisting users with Active Directory password resets and account unlocks, were outsourced to a Managed Service Provider (MSP), who charged them on a per-call basis. For CAMH, the number of password related calls made to the service desk were too high and consequently pushed up its IT management costs.
How AD360 helped
CAMH picked AD360's self-service password management module because of its unique capabilities, which include: the facility to push the GINA extension (for password reset/account unlock from Winlogon screen) from a central console, the self-update layout, and a customizable self-service portal.
With password resets done by users themselves with AD360's self-service credential update feature, CAMH predicted that they will be able to maximize their ROI potential with AD360 within the first six months of implementation.
Read the full storyAD360's security capabilities help East Coast Community Healthcare navigate the COVID 19 pandemic
The East Coast Community Healthcare CIC (ECCH) is a staff-owned social enterprise, providing community-based NHS and social care in Norfolk & Suffolk. Comprising a staff strength of over 700 professionals and 6 sites, it is also the second largest single-payer healthcare system in the world.
"Fairly easy to use and very intuitive, AD360 is very good for managing and tracking resources."
- Andrew Webster, IT support Engineer, ECCHBusiness challenges
ECCH witnessed an increase in the number of remote employees due to the COVID-19 nationwide lockdown, and its single AD domain structure's data security risk is at an all time high, with sensitive medical files being accessed by remote workers from different locations. With an influx in patients happening during the time, the cyber space of East Coast Community Healthcare could not risk a data loss or downtime in network.
How AD360 helped
After witnessing a favourable experience with ManageEngine's offerings, ECCH chose AD360 for its comprehensive auditing and user monitoring capabilities that helped them track all file accesses, modifications, and deletions.
Andrew Webster, the IT support engineer of ECCH, exclaimed that AD360, along with other ManageEngine solutions, helped his organization secure, manage and track their security resources, adding that his team has been using AD360 for its security and auditing needs.
Read the full story