On this page
Hybrid identity environments are designed to keep access working across all applications. Federation, synchronization, and conditional access connect cloud and on-premises systems so users can move across applications without thinking about infrastructure boundaries. That operational continuity is essential for business productivity. It is also one of the primary reasons lateral movement has become harder to detect.
Modern attackers rarely need to break authentication; they inherit it. They leverage valid credentials obtained through phishing, token theft, consent abuse, or password reuse. They do not need to escalate privileges loudly if privileges already exist through nested group memberships, delegated administrative paths, OAuth consent, service principals, or long-lived tokens. They do not always need malware if they can operate entirely with legitimate accounts.
This shift is reflected in modern threat frameworks. In the MITRE ATT&CK® framework, lateral movement and credential access are explicitly defined as core tactics used after initial access. These tactics rely heavily on valid identities rather than exploit-driven compromise. The infrastructure behaves as designed while trust is being misused.
That reality is why identity threat detection has emerged as a distinct discipline. Traditional IAM controls answer whether access is allowed at a point in time. Identity analytics answers a harder, more operational question: whether the way access is being used still aligns with the expected role, entitlement, and behavioral context.
Lateral movement is rarely a single event. It is a pattern that crosses identity planes, trust relationships, and privilege boundaries. Identity analytics exists to surface that pattern early enough for defenders to intervene precisely rather than react after the impact.
Identity-driven lateral movement in recent attacks
Recent incidents demonstrate how lateral movement through identity compromise unfolds in practice.
1. The ShinyHunters campaign targeting enterprise SSO environments (2026)
In early 2026, a campaign linked to the ShinyHunters collective targeted enterprise SSO environments. According to public advisories and threat intelligence reporting, attackers relied on voice phishing and credential harvesting rather than exploiting software vulnerabilities. Once SSO credentials and MFA codes were captured, threat actors accessed enterprise dashboards and moved laterally into connected SaaS platforms such as Salesforce and Microsoft 365.
The infrastructure functioned as designed. Authentication attempts succeeded. Authorization checks were passed. It was the abuse of federated trust relationships that enabled cross-application traversal.
2. The BlackCat/ALPHV ransomware attack on Change Healthcare (2024)
The February 2024 BlackCat/ALPHV ransomware attack on Change Healthcare illustrates the same identity-driven expansion pattern inside a hybrid enterprise network. Public reporting indicated that stolen credentials were used to gain initial access. After authenticating themselves legitimately, attackers moved laterally across internal systems before deploying ransomware, leading to a nationwide healthcare disruption and a reported ransom payment of approximately $22 million.
In both cases, the authentication events were valid. Authorization checks were passed. Movement occurred within permitted trust relationships. The problem was not broken access control. It was unexamined identity expansion across adjacency boundaries. This is precisely where the detection gap emerges.
Why identity controls miss lateral movement
Most security systems evaluate discrete events. An authentication attempt either succeeds or fails. An authorization system either permits or denies access. A privileged action either occurs or does not. These discrete decisions are necessary building blocks, but lateral movement rarely violates them outright.
In hybrid enterprises, most identity activity is successful by design. Users authenticate themselves repeatedly across SaaS applications, VPNs, collaboration platforms, and internal systems. Service accounts and workload identities authenticate themselves continuously through APIs and automation workflows. Tokens are refreshed and reused legitimately. Conditional access policies are evaluated and satisfied. When success is normal, exploitation blends into it.
Credential-based intrusions dominate modern breach investigations because valid accounts generate valid logs. The infrastructure appears healthy. The control challenge shifts from detecting failure to detecting identity drift. That is where identity analytics becomes essential.
To understand how that works, it helps to clarify where identity analytics fits within the broader identity security architecture.
Identity analytics as the control layer between governance and detection
Modern identity security spans multiple domains. Identity governance and administration (IGA) platforms define roles, enforce separation of duties (SoD), and conduct access certification. User and entity behavior analytics (UEBA) systems profile behavioral patterns and detect anomalies. SIEM platforms aggregate logs across infrastructure and cloud systems. Identity threat detection and response (ITDR) solutions focus specifically on identity-centric detection and response workflows.
Identity analytics, in this context, refers to the coordinated use of behavioral modeling, entitlement analysis, risk scoring, predictive access modeling, and cross-system correlation to evaluate identity-related risks. It functions as a control layer between governance and detection.
Governance platforms establish structural baselines through role definitions and certification. Behavioral systems observe deviations from routine activity. SIEM platforms provide cross-system visibility. ITDR solutions prioritize and orchestrate responses. Identity analytics systems bind these components together by correlating governance data, behavioral telemetry, and access events to form a unified identity risk narrative.
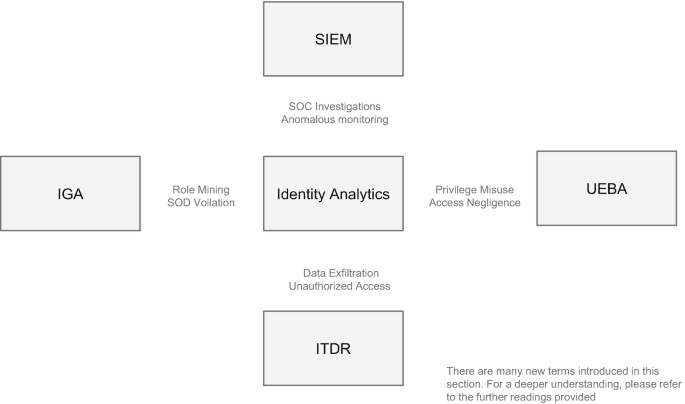
Source: Bhoyar, N. (2025). Fundamentals of Identity Analytics. In: Identity Analytics. Apress, Berkeley, CA. https://doi.org/10.1007/979-8-8688-1745-8_2
The diagram above illustrates this architecture clearly. Governance defines what access should look like. Behavioral analytics systems observe what access does look like. Security monitoring platforms capture the raw events. Identity analytics systems correlate those inputs and determine whether the identity activity reflects legitimate business behavior or the early stages of lateral movement.
Without that correlation layer, lateral movement remains indistinguishable from routine operational success.
Identity analytics is an evidence system
Identity analytics is not a single detection algorithm. It is an evidence system composed of reinforcing analytical capabilities that evaluate identity behavior in structural and contextual terms.
In mature hybrid environments, this evidence system typically draws on six core capabilities: anomaly detection in access patterns, risk scoring for users and entitlements, predictive analytics for access needs, automated role mining and engineering, continuous access certification, and behavioral biometrics.
These capabilities are not independent silos. They reinforce one another. An anomaly without entitlement context may be benign. A privilege without a behavioral deviation may be legitimate. Correlated signals, however, create explanatory power.
1. Anomaly detection in access patterns
Anomaly detection in identity environments extends beyond simple impossible travel alerts. In modern hybrid systems, the more meaningful deviations involve shifts in the privilege footprint, authentication patterns, and lateral access paths.
Every identity develops a behavioral baseline. A finance user interacts consistently with financial systems and productivity tools. An engineer accesses development platforms and repositories. A service identity performs predictable noninteractive API calls at regular intervals. These patterns form stable access clusters.
Lateral movement disrupts these clusters. An identity begins accessing systems that sit outside its historical adjacency set. A service principal that normally calls application APIs begins invoking directory management endpoints. A user account starts accessing administrative portals inconsistent with its job function.
The sequence is often more revealing than the geography. Real users follow routines shaped by their workflow. Attackers exploring adjacent trust boundaries introduce subtle sequence changes as they pivot across systems. Even when they pass each authentication and authorization check, a deviation from established access clusters signals expansion.
Anomaly detection provides the first indication that identity behavior is diverging from expectations.
2. Risk scoring for users and entitlements
Anomalies alone are insufficient for prioritization. Risk scoring translates deviations into measurable exposure.
Risk scoring evaluates both the behavioral context and entitlement structure. A privilege is not simply present or absent. It carries a risk weight depending on its adjacency to sensitive systems, frequency of use, and alignment with role expectations.
Dormant privileges are particularly important. Many identities possess entitlements they rarely exercise. Nested group memberships, delegated administrative rights, stale role assignments, and long-lived OAuth permissions accumulate over time. When those dormant privileges become active in the context of behavioral deviations, risk increases significantly.
Risk scoring bridges governance data from IGA platforms with behavioral signals observed by UEBA systems and event telemetry captured by SIEM platforms. It evaluates the blast radius, adjacency to high-impact assets, and velocity of the behavioral shift. Rather than generating isolated alerts, it contextually identifies identity risk elevation.
This contextualization is what enables ITDR systems to prioritize meaningfully rather than react to noise.
3. Predictive analytics for access needs
Access control determines whether access is allowed. Predictive analytics evaluates whether access is expected.
Over time, identities follow predictable trajectories shaped by their role, workflow, and automation purpose. A developer accesses repositories following code commits. A salesperson interacts with a CRM system during business hours. A workload identity calls APIs within a defined application boundary.
A predictive analytics capability models these trajectories and detects divergence. Lateral movement often appears not as forbidden access but as adjacency exploration. An attacker leverages valid credentials to access systems that are technically allowed but operationally inconsistent with the expected role behavior.
A deviation from predicted access paths often results in earlier detection than a policy violation alone. Predictive modeling strengthens anomaly detection by grounding behavior in forward-looking expectations rather than only historical averages.
4. Automated role mining and engineering
Behavioral detection is only as strong as the structural baseline it measures against. Automated role mining analyzes entitlement clustering across identities and engineers stable role definitions.
When roles are poorly defined and entitlements sprawl across departments, anomaly detection loses clarity. Access expansion appears normal because structural boundaries are weak. Role engineering creates meaningful segmentation.
By grouping consistent access patterns into engineered roles, organizations establish clearer baselines. Lateral movement becomes more visible because it crosses defined role boundaries rather than floating within ambiguous entitlement sprawl.
Role mining also improves governance hygiene by reducing unnecessary privileges and strengthening SoD enforcement. This reduces the number of exploitable adjacency paths available to attackers.
5. Continuous access certification
Access that is never reviewed becomes a latent risk. In hybrid environments, responsibilities evolve rapidly. Projects conclude. Integrations change. Service identities accumulate permissions without corresponding deprovisioning.
Continuous access certification ensures that entitlements remain aligned with business necessity. When an identity exercises a permission that has not been recently validated, that activity carries different analytical weight.
Certification data provides business context to anomaly detection and risk scoring. It distinguishes legitimate new access from neglected privilege drift. Many breach investigations reveal escalation paths provided by stale entitlements that were never actively monitored because they were assumed to be benign. Continuous certification narrows such blind spots.
6. Behavioral biometrics
Credential validation confirms possession. Behavioral biometrics provides continuous verification.
Even when credentials are valid and an authentication attempt succeeds, behavioral characteristics such as the interaction rhythm, typing cadence, device consistency, and session timing can diverge from established patterns. These signals add depth to identity analytics by helping validate whether the behavior aligns with the historical identity signature.
In environments where credential theft and token abuse are common, behavioral validation reduces reliance on binary authentication outcomes and introduces an additional context layer.
Correlation as the decisive layer
None of these analytical capabilities alone can prove the occurrence of lateral movement. Role changes, project transitions, or legitimate administrative tasks can produce anomalies. Risk scoring may fluctuate due to benign events. Certification gaps may reflect process delays. Correlation transforms weak signals into coherent identity narratives.
A lateral movement sequence in a hybrid environment often includes authentication drift, access expansion into new adjacency clusters, the activation of dormant entitlements, a rising risk score, and traversal across trust boundaries identified through attack path analysis. Individually, these signals are explainable. In sequence, they become compelling.
Attack path analysis, a concept increasingly referenced in identity security research and industry reporting, maps trust relationships and entitlement adjacency across environments. It reveals how identities can traverse privilege paths even when individual systems appear properly configured.
Correlation engines weigh how many identity analytics dimensions shift simultaneously and how quickly. They evaluate the identity type, privilege depth, and adjacency to sensitive control planes. Governance data, behavioral analytics, and event telemetry converge during this risk evaluation process.
This is where identity analytics justifies its central position in the architecture. It integrates governance and detection to provide actionable identity intelligence.
What identity threat detection changes operationally
When identity analytics functions as a true control layer, investigations shift from event triage to identity narrative analysis. Analysts evaluate identity drift across cloud and on-premises systems rather than focusing on isolated log entries. They assess whether access aligns with engineered roles, certified entitlements, and predicted trajectories. They examine how adjacency movement unfolds across trust boundaries.
Containment becomes more precise. Rather than disabling accounts broadly, teams can revoke specific tokens, constrain particular entitlements, enforce step-up authentication, or isolate privilege edges while maintaining operational continuity.
This precision is strategically important. If responses consistently disrupt business access, organizations hesitate. When lateral movement becomes legible through identity analytics, responses become measured and confident. As identity ecosystems scale across humans, services, and machine accounts, this demand for structured evidence becomes nonnegotiable.
Identity analytics is foundational to securing an ever-expanding identity surface
Over the last few years, the identity surface has expanded far beyond human users. AI agents, automation pipelines, service accounts, APIs, and machine identities are growing exponentially, increasing the authentication volume and making threats harder to trace and contain. These identities operate continuously, inherit permissions dynamically, and traverse trust relationships at machine speed. Governing and accounting for them through periodic reviews or static policy enforcement is no longer sufficient.
Without an identity analytics system correlating the entitlement structure, behavioral drift, certification state, and attack path adjacency, the misuse of non-human identities can go unnoticed because it resembles routine system activity.
As non-human identities begin to dominate authentication activity, discrete policy checks and isolated anomaly alerts lose explanatory depth. Continuous correlation across governance baselines, behavioral modeling, and privilege relationships is what enables organizations to interpret identity behavior coherently across humans, machines, and AI systems.
In modern hybrid enterprises, identity analytics separates normal access activity from the early stages of privilege expansion across trust boundaries.
Related solutions
ManageEngine AD360 is a unified IAM solution that provides SSO, adaptive MFA, UBA-driven analytics, and RBAC. Manage employees' digital identities and implement the principles of least privilege with AD360.
To learn more,
Sign up for a personalized demoManageEngine Log360 is a unified SIEM solution with UEBA, DLP, CASB, and dark web monitoring capabilities. Detect compromised credentials, reduce breach impact, and lower compliance risk exposure with Log360.
To learn more,
Sign up for a personalized demoThis content has been reviewed and approved by Ram Vaidyanathan, IT security and technology consultant at ManageEngine.