- Free Edition
- Quick Links
- Active Directory Auditing
- Active Directory auditor
- Active Directory monitoring
- Account lockout analyzer
- Login monitoring software
- Active Directory change notifier
- User logon audit reports
- AD logon logoff tracker
- User logon failure auditing
- Login history tracking tool
- AD change auditor
- Insider threat detection software
- Permissions change auditing
- Entra ID reporting
- Privileged user monitoring
- User behavior analytics tool
- Active Directory security monitoring
- Group Policy auditing tool
- GPO change auditor
- Entra ID auditing
- Audit user account management
- OU change auditor
- Audit group membership changes
- Active Directory auditing and reporting tool
- GPO reporting tool
- Remote desktop monitoring software
- PowerShell logging and auditing
- Azure password protection auditing
- Azure sign-in risk detection
- File Server Auditing
- Windows Server Auditing
- Employee Tracking
- Workstations Auditing
- Compliance Auditing
- Other features
- SIEM Integration
- Windows DNS - Schema Auditing
- Windows security event log monitoring
- SIEM audit solution
- Schedule Active Directory change reports
- Reports from Archived Data
- Aggregated summary reports
- AD new/old attribute changes
- Audit trail
- Audit Active Directory LAPS
- Scheduled Reports & Alerts
- Account lockout examiner
- Industry
- Documents
- Success Stories
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
File share auditing with ADAudit Plus
Track user activity in shared files on Windows File Servers, NAS devices, Azure Files, and more.
Track every file share access event
ADAudit Plus records file read, create, modify, delete, move, rename, and copy-and-paste operations with the user name, source machine, and target file path. With the right filters, you can easily have the full access timeline, not just the current state.
Monitor share permission changes
Capture changes to folder permissions (DACL) and audit settings (SACL) with old and new values. Permission changes that would otherwise go unnoticed surface immediately with full attribution.
Detect ransomware activity
Baselines file activity volume and times for each user and alerts you when modification or deletion volumes spike beyond the user's normal pattern. This is usually a verified indicator of ransomware activity or deliberate data destruction.
Audit across 14 server and NAS types
One console covers Windows file servers, Windows file clusters, NetApp, EMC Isilon, Synology, QNAP, Nutanix Files, Qumulo, Amazon FSx, Azure File Share, and more. You will not require separate consoles for each platform.
Real-time alerts on critical events
Pre-configured alert profiles get triggered the moment a critical file event occurs. You can also customize alerts for your specific needs. Alerts route to email, SMS, or your ITSM platform automatically.
Meet compliance requirements
Canned reports map directly to GDPR, HIPAA, SOX, PCI-DSS, GLBA, FISMA, and ISO 27001 requirements for file share activity. Custom report profiles let you save specific user, action, and filter combinations for recurring audit requests.
Investigate failed access attempts
Denied attempts to read, write, and delete files are captured, making it easy to identify repeated failures that signal unauthorized access probing before a breach occurs.
Summarize activity by user or process
Aggregate file activity by user or by process to identify which accounts or applications are generating the most activity on your file servers and include findings in investigations and reviews.
What ADAudit Plus audits on file shares
ADAudit Plus captures every create, read, modify, delete, move, rename, and copy-and-paste access event across every layer of your file share environment, from individual file operations to share-level permissions and account access patterns.
Track all file and folder activity
Every file event on your Windows file servers is tracked by ADAudit Plus and is searchable by user, server, share, file type, or time window. You do not need to log in to individual servers or correlate events manually; all activity flows into a single reporting console, making monitoring and analysis easier.
File share access and modification events
- Identify every user who read a specific shared file, with the exact time and the machine they accessed it from.
- Trace file share modifications back to the account, machine, and user so you can determine exactly what changed and who changed it during an incident.
- Confirm whether a shared file was deleted intentionally or as part of a regular process by comparing the deletion event against the user's normal activity baseline.
- Track copy-and-paste operations as distinct events separate from create or modify events, so data movement between shares is audited without relying on DLP tools.
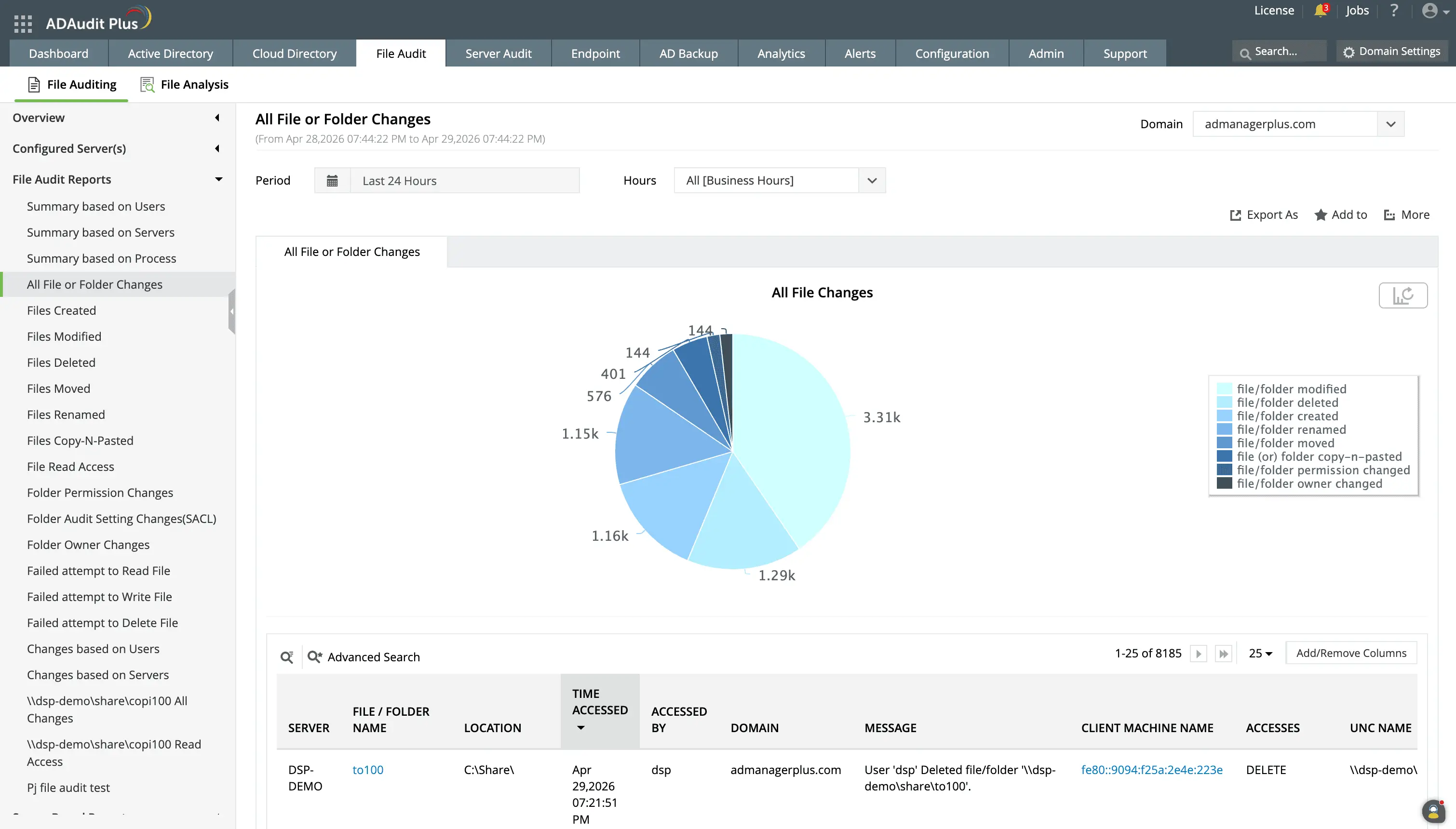
Know who made what change in which file, and when.
Track every file action, including file creation, modification, moves, renames, copy-and-paste, and permission change.
Filter reports by user, type of action, server, time period, and more for easier analysis.
Failed file share access attempts
- Detect unauthorized access attempts by surfacing repeated failed file read, write, and delete events before they escalate to a successful breach.
- Identify which accounts are generating the most failed access attempts, a pattern that often precedes a targeted attack.
Folder permission and ownership changes
- ADAudit Plus captures every change to folder-level permissions and ownership with before-and-after permission values. You can see exactly what was changed, who changed it, and when, without log-diving.
- Detect permission escalations the moment they occur, so an unauthorized change to a shared folder's access control does not go unnoticed until an audit.
- Verify ownership transfers with full context; folder ownership changes affect permission inheritance across all child objects, making them a high-impact event even when the change appears routine.
- Review the complete permission change history for a specific folder or share when preparing for a compliance audit, without reconstructing events from individual server logs.
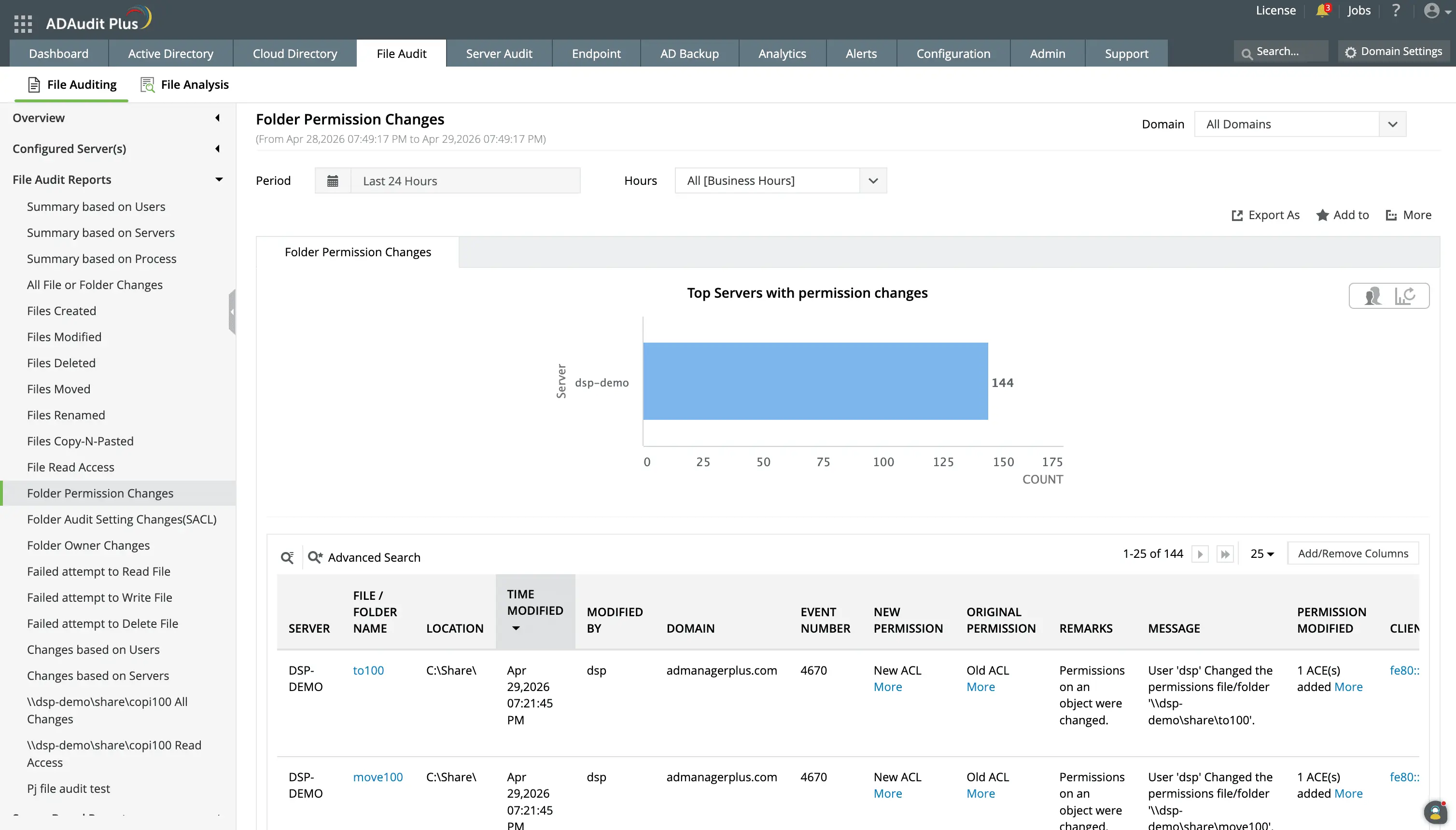
View the ACL values before and after each permission change.
Track each administrative user's permission change actions and hold them accountable for unusual or high-impact permission changes.
Audit setting changes (SACL)
- Changes to folder audit settings (SACL) can disable your visibility into specific file share activity without triggering an access event. ADAudit Plus captures SACL changes as distinct events, so any modification to your audit configuration is itself auditable.
- Confirm that audit policies on critical shares have not been modified since your last review, a check that typically requires manual GPO verification but is automated by ADAudit Plus.
- Identify attempts to disable auditing on specific folders as a precursor to malicious activity, and act before any covered operations occur.
Detect ransomware and other threats
Ransomware, insider activity, and other malicious threats are rarely obvious in real time. They become visible when an unusual volume of file operations, including mass deletions, bulk modifications, or abnormal read access patterns, appears in your audit data. ADAudit Plus applies machine learning to file activity to identify these patterns while you still have time to contain them.
User behavior analytics for file activity
- ADAudit Plus establishes a per-user baseline of normal file activity volume, timing, and patterns. When behavior deviates from that baseline, ADAudit Plus alerts administrators quickly.
- Catch ransomware activity in progress: a spike in file modifications that exceeds a user's normal baseline triggers the Unusual Volume of File Modification alert, a verified indicator of ransomware encryption behavior.
- Identify data destruction attempts through the Unusual Volume of File Deletions alert, which fires when deletion activity significantly exceeds a user's baseline and cannot be explained by routine operations.
- When total file activity spikes well beyond a user's normal volume, the Unusual Volume of File Activity alert fires, a recognized signal of data exfiltration in progress
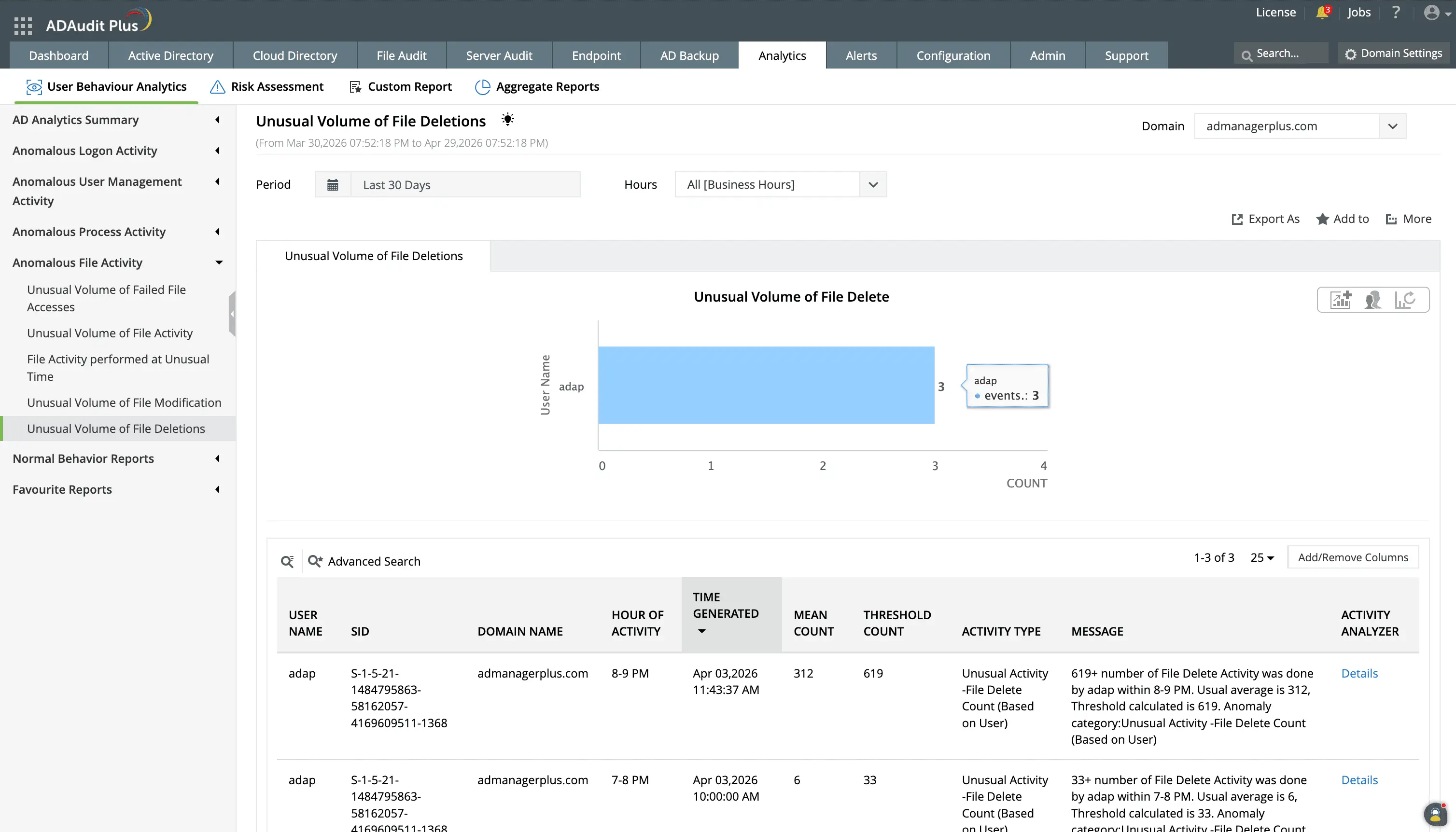
Track who deleted a file, what was deleted, and when it occurred to prevent unauthorized data loss, aid in forensic investigations, and ensure adherence to regulatory standards.
Attack Surface Analyzer: ransomware detection
Beyond behavioral baselines, ADAudit Plus's Attack Surface Analyzer detects file modification and deletion patterns consistent with ransomware encryption across your monitored file servers. When the pattern matches, ADAudit Plus triggers an alert alert with the event timeline, the affected files, and the account responsible.
Get real-time alerts on critical file share events
Auditing file share activity has limited value if you only review events after the fact. Critical events require real-time alerts and ADAudit Plus provides just that.
With both pre-configured alert profiles and custom alerts, you can cover the events most likely to require immediate attention:
- Changes in critical shares
- Ransomware indicators
- Failed attempts to access shares
- File share accesses at unusual times, and so on.
You can receive alerts via email or SMS and trigger workflows in ITSM platforms such as ServiceNow, Jira, or ManageEngine Service Desk Plus.
Extend file share auditing to NAS devices and cloud storage
Most file activity does not happen exclusively on Windows file servers. Data sits across NAS appliances, cloud file storage services, and hybrid environments where on-premises and cloud access overlap.
From a single console, ADAudit Plus audits file activity across:
Windows File Server and Windows File Cluster, NetApp Server (7-Mode and C-Mode), EMC Isilon, EMC Server, Hitachi NAS, Huawei OceanStor, Synology NAS, QNAP NAS, CTERA Edge Filers, Nutanix Files, Qumulo NAS, Amazon FSx, Azure File Share
Meet compliance requirements for file share access
GDPR, HIPAA, SOX, and PCI-DSS all impose file access logging requirements, and audit requests that arrive without notice require an immediate response. ADAudit Plus provides pre-configured compliance reports that map directly to each standard's file access requirements. These reports are available for HIPAA, PCI-DSS, GDPR, SOX, FISMA, GLBA, and ISO 27001.
4 compelling reasons to choose ADAudit Plus
Widely recognized
ADAudit Plus has been recognized as a Gartner Peer Insights Customers' Choice for Security Incident & Event Management (SIEM) for four consecutive years.
Easy deployment
Go from downloading ADAudit Plus to receiving predefined reports and alerts in under 30 minutes, without any professional help.
Competitive pricing
ADAudit Plus is licensed per-server, unlike other IT auditors which are licensed per-user. With per-server licensing, even with a growing number of users each year, you can continue to ingest log data without additional costs.
Unified visibility
ADAudit Plus consolidates auditing, security, and compliance across Active Directory, Entra ID, Windows servers, workstations, and file servers into a single pane of glass, eliminating the need to juggle multiple tools.
Frequently asked questions
File share auditing is the process of tracking, recording, and monitoring access to shared files and folders on a network. It involves recording who accessed, modified, deleted, or failed attempts to access shared resources, identifying potential security breaches and insider threats, and ensuring compliance.
Windows has two different levels of auditing; audit file share, which produces one entry for each time someone connects to a shared directory, and audit detailed file share, which produces an entry for every file or subdirectory accessed in that shared directory. Audit detailed file share produces substantially more entries than audit file share. However it produces the per-file detail necessary for investigative purposes. Only detailed file share auditing will provide the level of access logging required by HIPAA, GDPR, and PCI-DSS for organizations that are subject to those regulations through handling regulated information such as medical records, financial information, and personally identifiable information (PII).
ADAudit Plus allows you to automate collecting, aggregating and analyzing Windows security event log data from your Windows file servers, failover clusters and many different NAS devices. Instead of having to parse individual windows security event logs in individual servers, you can generate pre-configured reports, receive real-time alerts and utilize machine learning-based anomaly detection from a single console.
On a single Windows file server, you can enable audit detailed file share via Group Policy and then search the Security event log for the relevant Event IDs. The limitation is that this works per server only; there is no native way to search file access events across multiple servers simultaneously, and the Security event log does not retain events indefinitely.
For multi-server and hybrid file storage environments, ADAudit Plus collects file access events from all monitored Windows file servers and NAS devices into a single console, where you can search by user, file path, server, or time window across your entire environment.
Enabling file share auditing on Windows Server involves two main steps: activating the "Audit File Share" or "Audit Detailed File Share" auditing policy in Group Policy and configuring the System Access Control List (SACL) on specific files or folders. This allows tracking of user actions like reading, writing, and deleting files, with events logged in the Security Event Viewer.
The manual configuration process requires access to each file server and ongoing maintenance as shares are added or changed. Tools like ADAudit Plus automate audit policy verification and collects events centrally once the audit policy is in place, so you are not managing log collection manually in each server.

