Allowlist & blocklist
Endpoint Central's application control is a vital cybersecurity measure that enables organizations to manage and regulate the execution of software applications, enhancing security and operational efficiency by preventing the use of unauthorized software and limiting access based on enterprise specific needs.
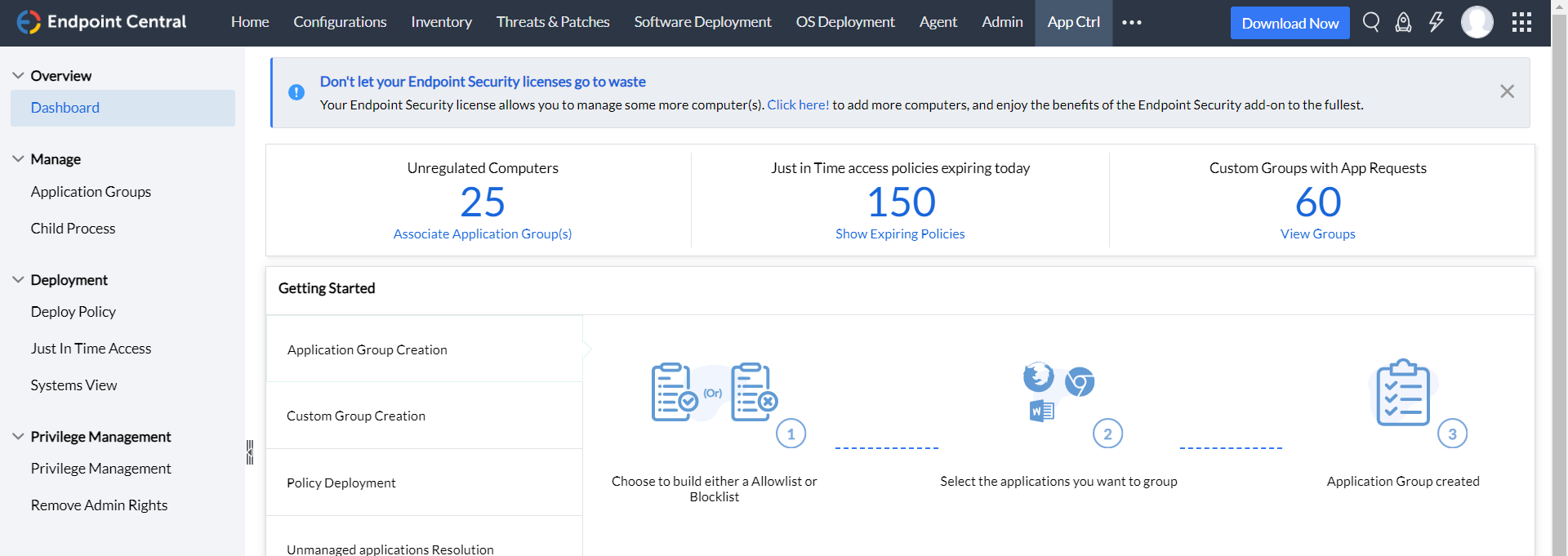
Allowlisting and blocklisting are the two approaches through which an enterprise can have control over their applications. If the admin opts for the allowlisting approach, he will have to create a list and only all those applications that make it to this list will be allowed to run, while every other application will be blocked from running in the network. On the contrary, if blocklisting is opted as the preferred mode of application control, the list made by the admin will comprise of the applications that he wishes to block. Keeping applications in check by allowlisting is done to tighten security, while blocklisting is more of a technique to maintain productivity in an enterprise.
- Enhanced security
It serves as a robust security measure, reducing the attack surface by allowing only trusted applications to execute, which significantly lowers the risk of cyber threats.
- Efficient resource management
By allowing applications based on the user's role and job requirements, it streamlines inventory management, prevents unused applications from consuming storage, and simplifies license and patch management.
- Customized access
Application allowlisting allows organizations to tailor application access according to user roles, ensuring a more secure and efficient digital environment. Unauthorized application prohibition: Application blocklisting involves identifying and restricting unauthorized, risky, or malicious applications from running on the network or managed devices.
- Mitigating security risks
It acts as a protective measure against known security threats by prohibiting applications with potential vulnerabilities.
- Control and compliance
Blocklisting offers administrators control over which applications are permitted, helping organizations maintain compliance with security policies.
- Reduced attack surface
By preventing known problematic applications from executing, blocklisting minimizes the risk of cybersecurity incidents and data breaches.
Application Privilege Management
- Restrict Admin Rights
Implement a security practice to reduce unnecessary admin rights, limiting the potential attack surface and preventing privilege elevation or credential compromise attacks.
- Least Privilege Model
Maintain a least privilege model without hindering productivity, ensuring that users only have the access they require to perform their roles effectively.
- Application-Specific Privilege Elevation
Enable controlled privilege elevation for business-critical applications, allowing users to access elevated privileges only when needed for specific tasks, enhancing security without compromising operational efficiency.
- Just-in-Time Access
Address interim user needs by providing just-in-time privileged access to applications, with an automatic revocation mechanism after a predefined period, minimizing security risks associated with extended privileges.
- Per-App VPN
Implement secure connections with granular control, ensuring data in transit is protected and optimizing network resources.
- Conditional Access
Restrict network and application access based on user identity, device health, or location, enhancing security by allowing access only when predefined conditions are met.
- Secure Data Transmission
Per-App VPN guarantees secure data transmission for individual applications, reducing the risk of data interception.
- Adaptive Control
Conditional access policies dynamically allow or deny access based on real-time conditions, enhancing security while maintaining user experience.
- Enhancing Office 365 security
Gain visibility into the devices accessing the Office 365 applications and grant access only from authorized devices.

"We are using this product from last 11 year and it had made the day to day running IT operation very easy and having simple process which help to understand the tool feature easily even for new IT engineer. We are managing all endpoint, servers, VM & think client along with license and mobile device, and as an IT admin I feel it have very detailing about the product and services which increase our productivity. We have compared other tool, but this is the best tool with lots of new feature update like integration with other tool and security management."
Ajay K,
Automotive industry,
Review collected by and hosted on G2.