Businesses adopt new techniques to keep their network security in check for zero-day vulnerabilities. Unlike the physical layer that gives immediate indication on problems, hacking attempts can go unnoticed and become severe until there is a holistic visibility into network traffic. You can track traffic flow for its source and destination through real-time monitoring, but viewing the "who", and "how" of historical traffic pattern data is valuable for helping you troubleshoot bandwidth bottlenecks.
The solution you choose should enable you to review each metric individually to pinpoint the source of an issue or potential issue. For example, the granular details of a traffic spike can help you determine the severity of an issue and isolate the weak points in your network. This is where network forensics comes in. These efforts can ultimately help you develop a hack-proof network. So, what is network forensics, and why is network forensics used? Let's take a look at these aspects now.
Network forensics, a subset of digital forensics, captures and analyzes network traffic to discover useful information helpful for investigating security breaches. A cyberattack in an organization can be unknown until it impacts a major data source. But to make sure that it doesn't occur again, admins might need to collect network traffic data from the past, determine the scope of the problem, and identify what went wrong, especially any security vulnerabilities and configuration problems.
As a network administrator, you know how well-established and effective the security tools firewalls and intrusion detection systems (IDS) are. But how does it make them less efficient when compared to network forensic analysis tools (NFAT)? The answer involves the basic working principle followed by both of these security systems.
An ideal firewall will allow and restrict traffic flowing to and from particular IP address, network, or port numbers, based on an admin's pre-configured rules. But there are protocols that can sidestep specific ports. Therefore violating port-based security is easier for the hackers, and allows them to gain access to your network. Even the internal users can access malicious websites.On the other hand, an ideal IDS works by typically blocking the traffic that doesn't match the preconfigured security policies. But not every intrusion can be detected.
Network forensic solutions improve on both of these methods by collecting the entire flow of traffic to uncover anomalies. These tools concentrate only on the piece of information that is necessary to detect troubles and determine the root cause of the issues. This is because network forensic analysis tools follow two basic methods: The first method is where you receive a complete picture of the traffic to maintain records and find the underlying issues; the second method is where it quickly analyzes the traffic of interest, and shares the relevant information regarding it.
Security
Since the network forensics process depends on the collection of evidence, you can find malicious domains, URLs, and detect threats with raw data. You can discover the origin of the traffic and who might be behind the suspicious traffic. With granular details, you can track the growth pattern to determine if the irregularity results from excessive bandwidth usage or a hacking attempt.
Traffic analysis
Although security is one inevitable reason for choosing network forensics, it can also help troubleshoot issues with in-depth traffic analysis. Imagine a three-minute traffic spike at 5:45 pm on Saturday. With forensics, you can get a picture of why there's a traffic spike outside business hours, what protocols contributed to the traffic spike, and know the source and target machines so you can troubleshoot the issue. You can find the information related to bandwidth use by protocols, devices, and users.
Performance
Network forensics techniques are primarily based on storing the traffic data for a longer time to understand how the trends change. Say an organization's application server is unresponsive and many messages or traffic has been lost, forensics helps you investigate this by providing information about traffic load over time so you can detect unnoticed anomalies or application errors. Since network forensics collects the entire picture of network traffic, you can pinpoint a source, or look at the signs of bottlenecks to identify if it was an hacking attempt or a persisting congestion issue.
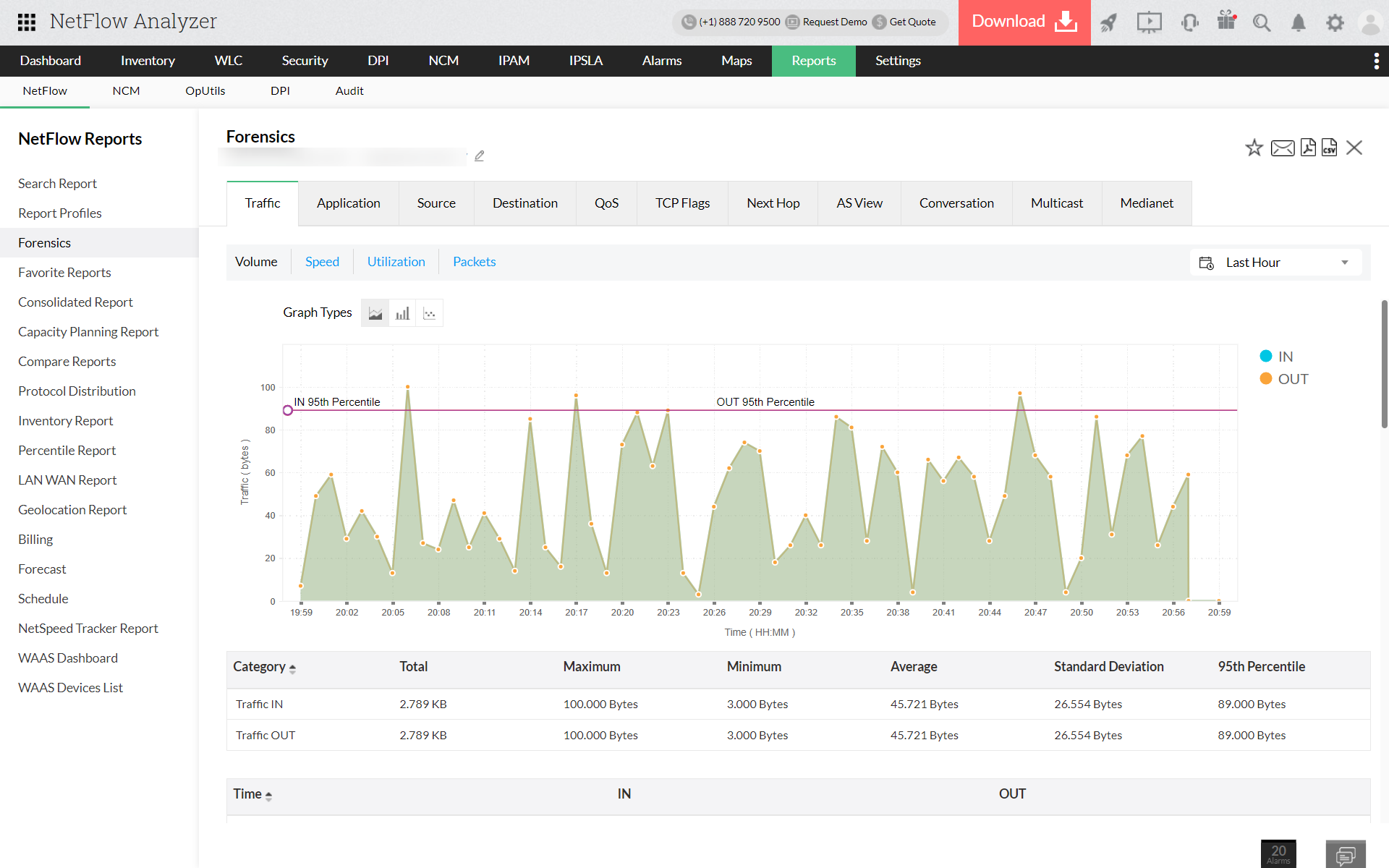
NetFlow Analyzer is a network forensic analysis tool that captures the raw data and provides you with accurate insights about the bandwidth usage, security, and performance of your network. You can leverage the tool to receive forensics reports that go back in time so you can determine the root cause of bottlenecks and see how the patterns have changed. This can help you build policies and restrict certain harmful traffic from penetrating your network.
Other advantages for utilizing NetFlow Analyzer: