How to enable MFA for Windows login
In this article:
Objective
By following this article, administrators can:
- Learn how to enable MFA for Windows login using ADSelfService Plus
- Protect domain-joined and remote Windows machines from credential-based attacks
- Enforce strong identity verification during Windows logins.
Enabling MFA for Windows using ADSelfService Plus can secure the following scenarios:
- Local and remote Windows domain login
- Windows lock screen during system unlock
- User Account Control elevation prompts
This ensures users verify their identity before accessing enterprise machines.
Prerequisites
System requirements for Windows MFA
The following Windows servers and client versions are supported for MFA with ADSelfService Plus.
| Windows servers |
Windows clients |
| Windows Server 2025 |
Windows 11 |
| Windows Server 2022 |
Windows 10 |
| Windows Server 2019 |
Windows 8.1 |
| Windows Server 2016 |
Windows 8 |
| Windows Server 2012 R2 |
Windows 7 |
| Windows Server 2012 |
|
| Windows Server 2008 R2 |
|
Dependencies
- Your ADSelfService Plus license must include Endpoint MFA. Visit the store to purchase Endpoint MFA.
- SSL must be enabled: Log in to the ADSelfService Plus web console with admin credentials. Navigate to the Admin tab > Product Settings > Connection. Select the ADSelfService Plus Port [https] option. Refer to this guide to learn how to apply a SSL certificate and enable HTTPS.
- Access URL must be set to HTTPS: Navigate to Admin > Product Settings > Connection > Connection Settings > Configure Access URL and set the Protocol option to HTTPS.
- Enable the required authentication methods. For steps on enabling the authentication methods, refer to this page.
- Install ADSelfService Plus login agent on the machines where you want to enable Windows login MFA. Click here for steps to install the ADSelfService Plus login agent.
- Offline MFA is supported only for Windows machines (except Windows 10 version 1803) and macOS logins. For remote logins, offline MFA is not supported for Windows RDP-client authentication.
- Please make sure that the login agent installed on your machines meets the required version: version 6.3 or above for Windows, and version 3.0 or above for macOS. If not, update the agent to the latest version by following these steps. If you have not installed the login agent yet, please configure offline MFA before doing so to ensure that the changes are updated.
Steps to setup MFA for Windows login
Configure MFA for Windows login
- Log in to the ADSelfService Plus web console with admin credentials.
- Navigate to Configuration > Self-Service > Multi-factor Authentication > MFA for Endpoints.
- Select a policy from the Choose the Policy drop-down. This will determine which authentication methods are enabled for which sets of users.
Note: ADSelfService Plus enables you to create OU and group-based policies. To create a policy, go to Configuration > Self-Service > Policy Configuration > Add New Policy. Click Select OUs/Groups, and make the selection based on your requirements. You need to select at least one self-service feature. Finally, click Save Policy.
- In the MFA for Machine Login section, check the Enable __ factor authentication box, select the number of authentication methods, and specify which ones you'd like to use from the drop-down.
- To enable Offline MFA: Check the Choose authenticators for Offline MFA box and select the authentication methods you prefer to use.
- Click Save Settings.
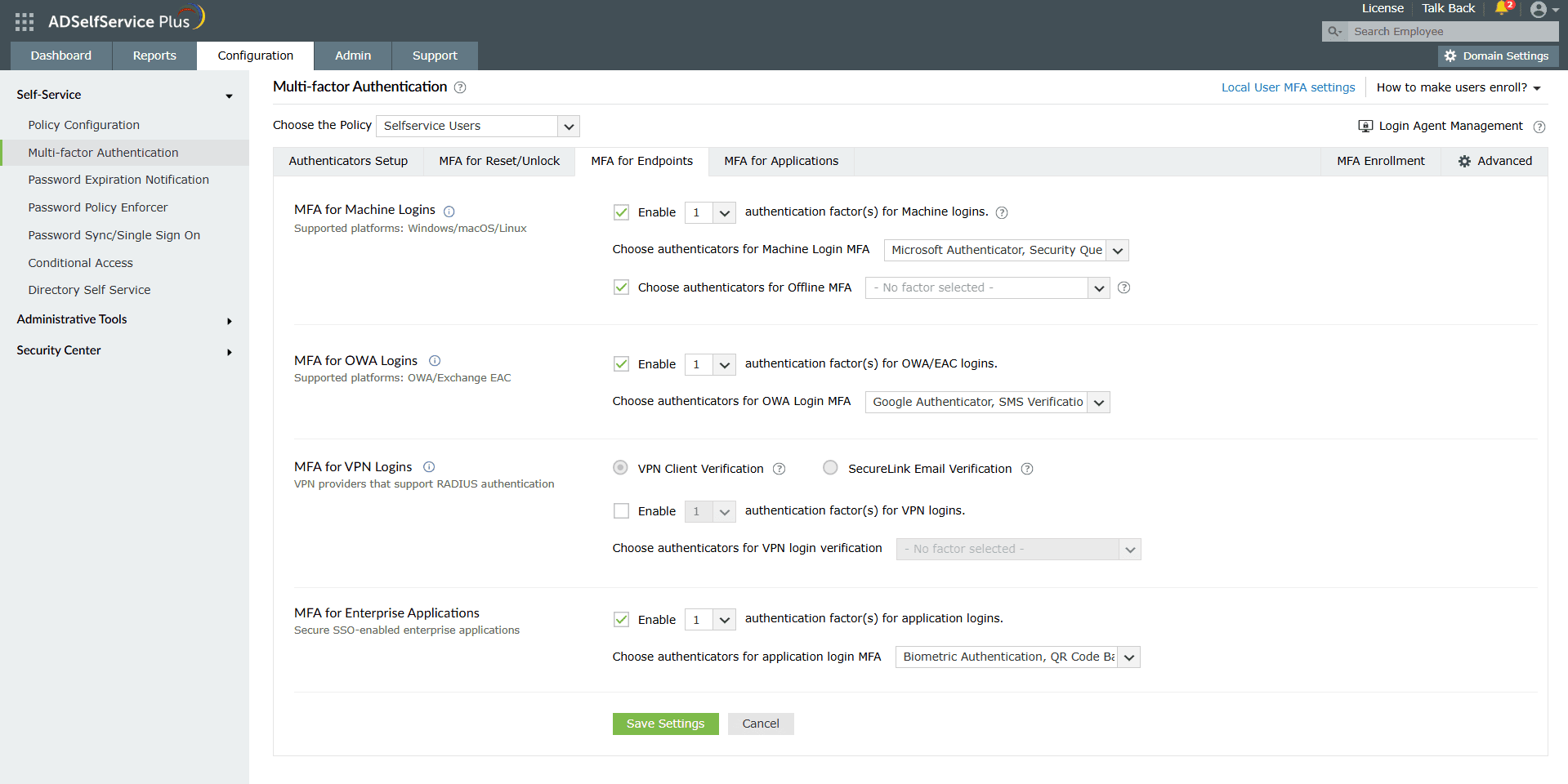
Image 1. MFA for Windows configuration
Secure ancillary Windows endpoints with MFA
Extend MFA protection beyond initial logins to User Account Control prompts, machine unlocks, and Remote Desktop sessions for comprehensive Windows endpoint security.
- Secure User Account Control prompts with MFA : Elevating privileges via UAC is a common attack vector; enforcing MFA here prevents unauthorized admin actions and strengthens least-privilege enforcement. To enable this feature go to Advanced > Endpoint MFA, then select User Account Control from the Enable MFA for _ drop-down.
- Protect machine unlocks against unauthorized access : Unlocked machines expose sensitive data to physical threats; MFA adds a vital second factor to thwart shoulder-surfing or stolen credentials.To enable this feature go to Advanced > Endpoint MFA, then select the Machine Unlocks from the Enable MFA for _ drop-down.
- Safeguard RDP sessions from lateral attacks : RDP is a top exploit target for ransomware; MFA ensures only verified users establish remote connections, blocking credential-stuffing attacks.
To enable, go to Advanced > Endpoint MFA, select the Enable MFA for Remote Desktop access during checkbox.
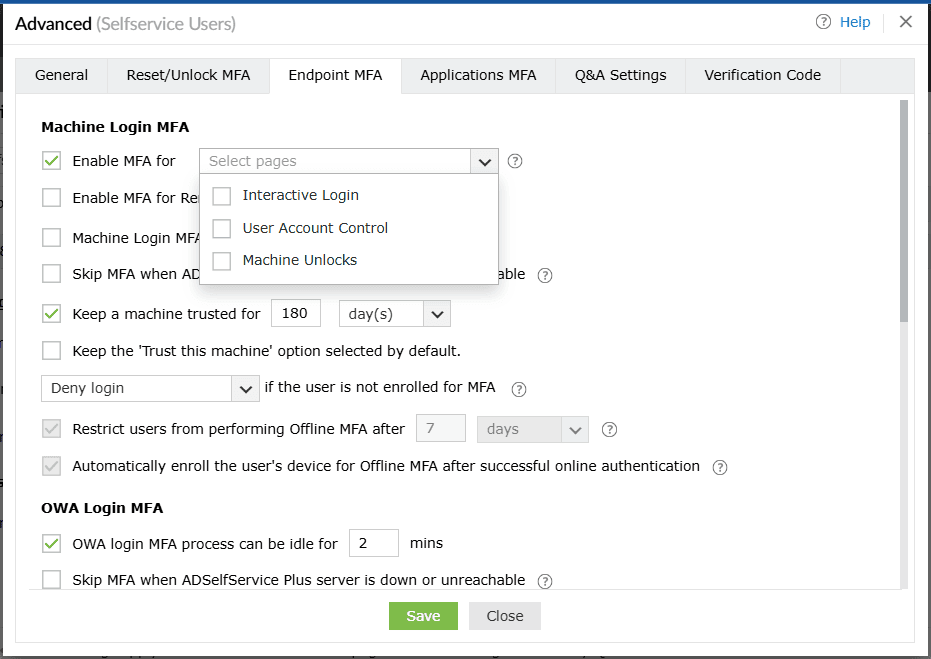
Image 2. Enable MFA for drop-down
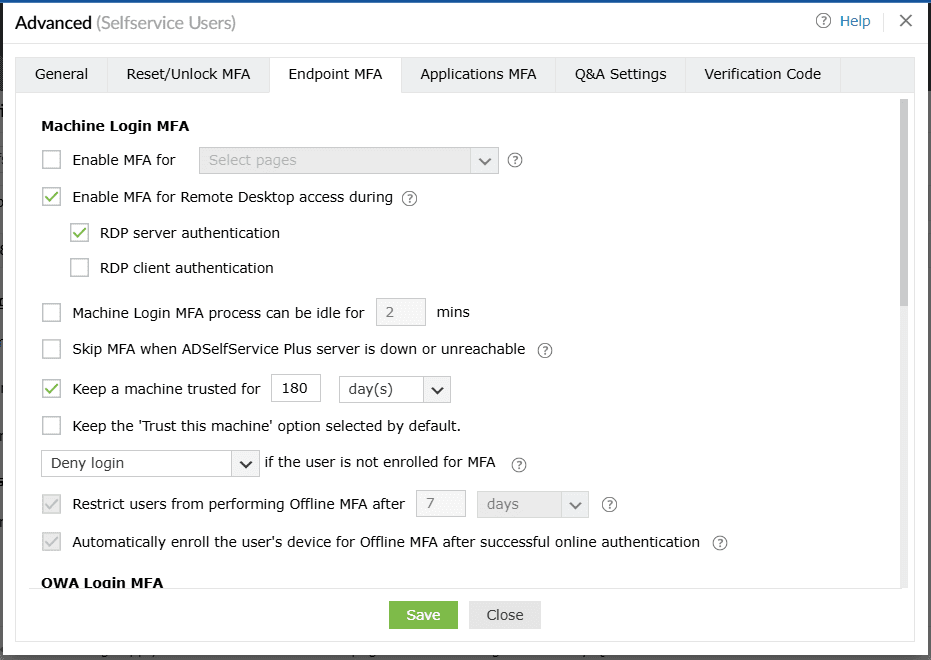
Image 3. Enable MFA for Remote Desktop access during checkbox
Streamline Windows MFA policies for seamless machine logins
To enable create a holistic MFA policy, go to Advanced > Endpoint MFA, and configure advanced settings such as:
- Idle time limit: Set a time limit for users to complete the MFA process when logging into their machines using the The Machine login MFA process can be idle for __ min setting.
- MFA server downtime: Ensure users aren't left stranded on their machine login screens during the MFA process when the ADSelfService Plus server is down or unreachable using the Skip MFA when the ADSelfService Plus server is down or unreachable option. This setting is skipped when:
- Offline MFA is configured and the user is enrolled with offline MFA on their device.
- Machine-based MFA is enforced in the device.
- Trusted device: Enable users who have logged in once using MFA for Windows login to skip going through MFA authentication during subsequent logins using the Keep a machine trusted for _ days setting.
- Unenrollment mitigation: Determine the authentication flow for the user when they have not enrolled for any of the authenticators for Windows MFA using the _ if the user is not enrolled for MFA setting. One of the following actions can be enabled occur:
- Allow logins: The user will be permitted to bypass machine login MFA and gain access to the machine.
- Deny logins: The user will be restricted from access.
- Force enrollment: The user will be required to enroll with the authenticators for online MFA and offline MFA only after successful primary authentication.
Validation and confirmation
- Apply a policy to a test OU or group and user.
- Log on to a target Windows machine with AD credentials; confirm the Windows authentication MFA prompt appears and succeeds with enrolled authenticator.
- Test offline MFA by disconnecting from the internet—verify enrollment and logon work.
- Review MFA Enrolled Users Report for status and backup codes.
Tips
- Use phishing-resistant authenticators like YubiKey or biometrics for high-security endpoints.
- Enforce authenticator enrollment via advanced settings to ensure compliance.
- Configure backup codes to prevent user lockouts if a primary authenticator is unavailable.
Highlights of ADSelfService Plus
Allow Active Directory users to self-service their password resets and account unlock tasks, freeing them from lengthy help desk calls.
Get seamless one-click access to 100+ cloud applications. With enterprise single sign-on, users can access all their cloud applications using their Active Directory credentials.
Intimate Active Directory users of their impending password and account expiry via email and SMS notifications.
Synchronize Windows Active Directory user passwords and account changes across multiple systems automatically, including Microsoft 365, Google Workspace, IBM iSeries, and more.
Strong passwords resist various hacking threats. Enforce Active Directory users to adhere to compliant passwords by displaying password complexity requirements.
Enable Active Directory users to update their latest information themselves. Quick search features help admins scout for information using search keys like contact numbers.