Identity360 provides one-click, secure access to enterprise applications with single sign-on (SSO).
About 59% of employees use the same password on multiple accounts.*
Approximately 51% of users have difficulty remembering their work and personal passwords †
The hassle of logging in has caused approximately 26% of IT employees to give up doing something ‡
Identity360 equips and empowers your organization with modern SSO capabilities.
Here's how SSO works in Identity360 when a user tries to access resources:
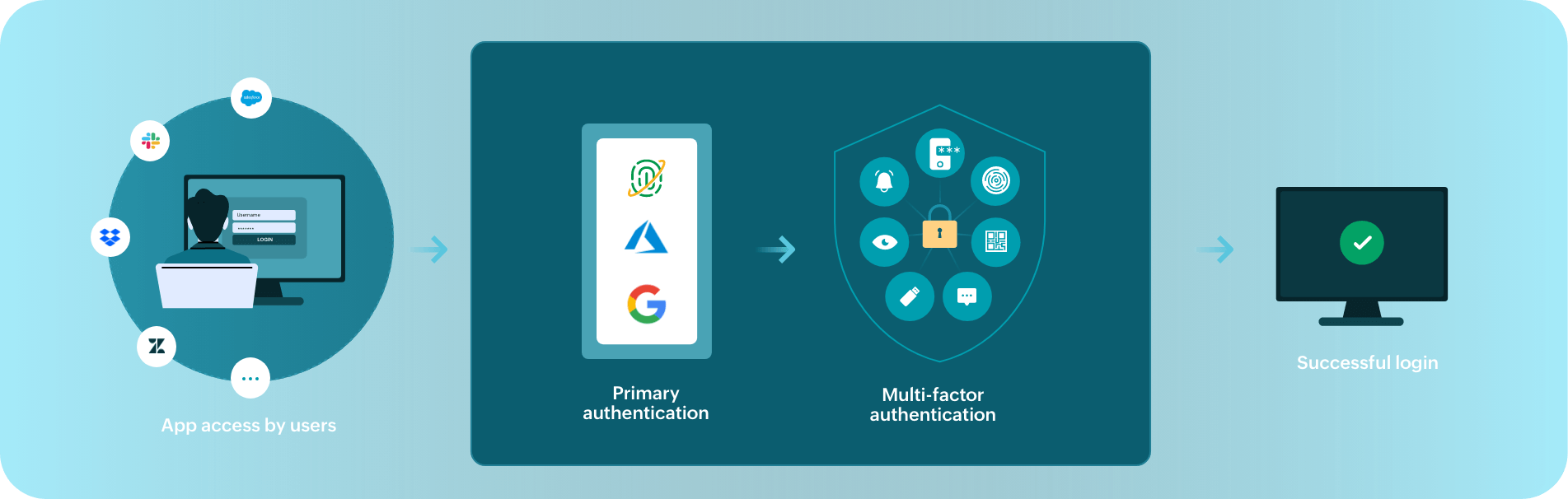
Identity360 offers both IdP- and SP-initiated SSO. With IdP-initiated SSO, users sign in to Identity360 with MFA, then access the apps assigned to them from the dashboard. In SP-initiated SSO, users go to the app's login page, then get redirected to Identity360 for authentication.
For both IdP- and SP-initiated SSO via Identity360, users undergo two-step identity verification: primary and secondary authentication.
In primary authentication, the user's credentials are verified against their primary directory through the OIDC protocol.
Secondary authentication is performed after the successful completion of the primary authentication, where they have to verify with admin-configured MFA methods.
Upon successful completion of MFA, the user gains access to all enterprise applications assigned to them through SSO.
Identity360 provides users with one-click access to enterprise apps, thereby eliminating password fatigue and time-consuming login processes.
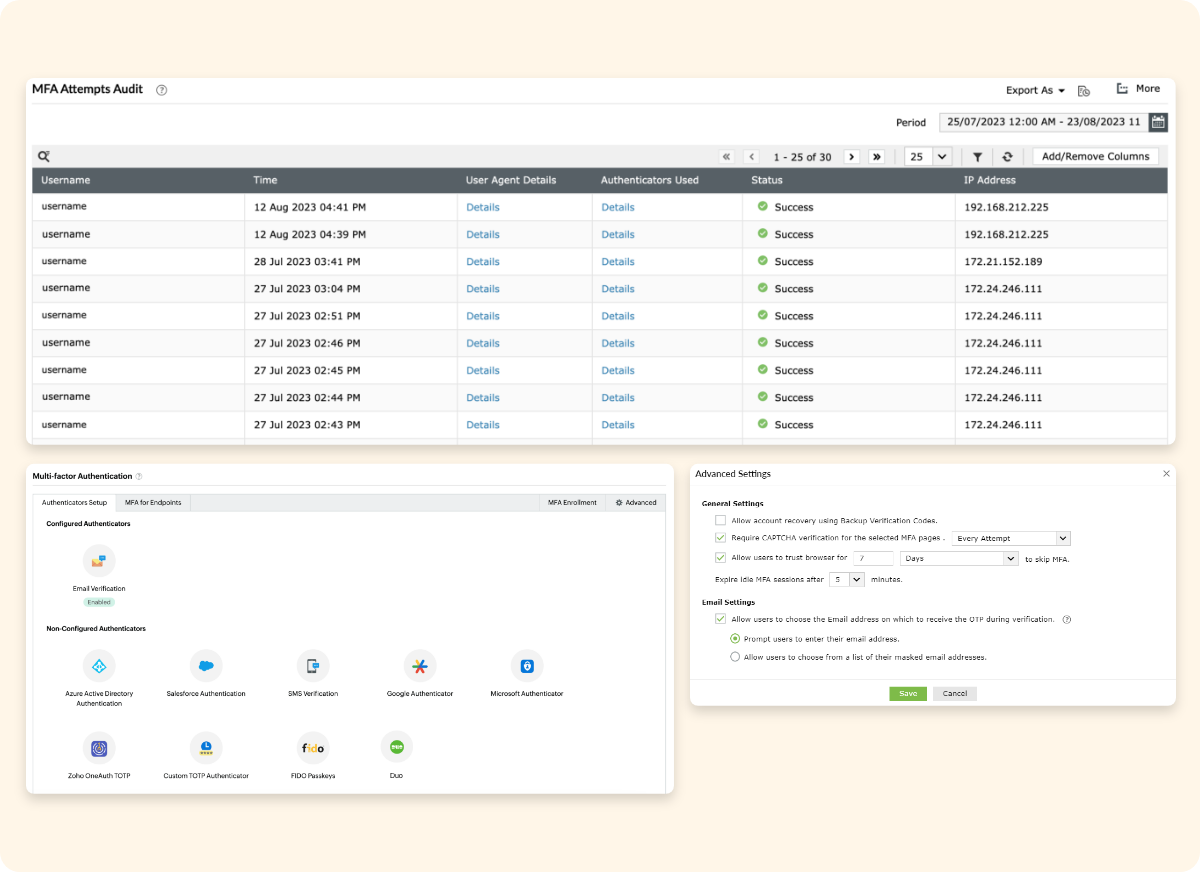
With modern MFA authenticators and granular MFA customization capabilities, each SSO attempt is well protected against potential security threats.
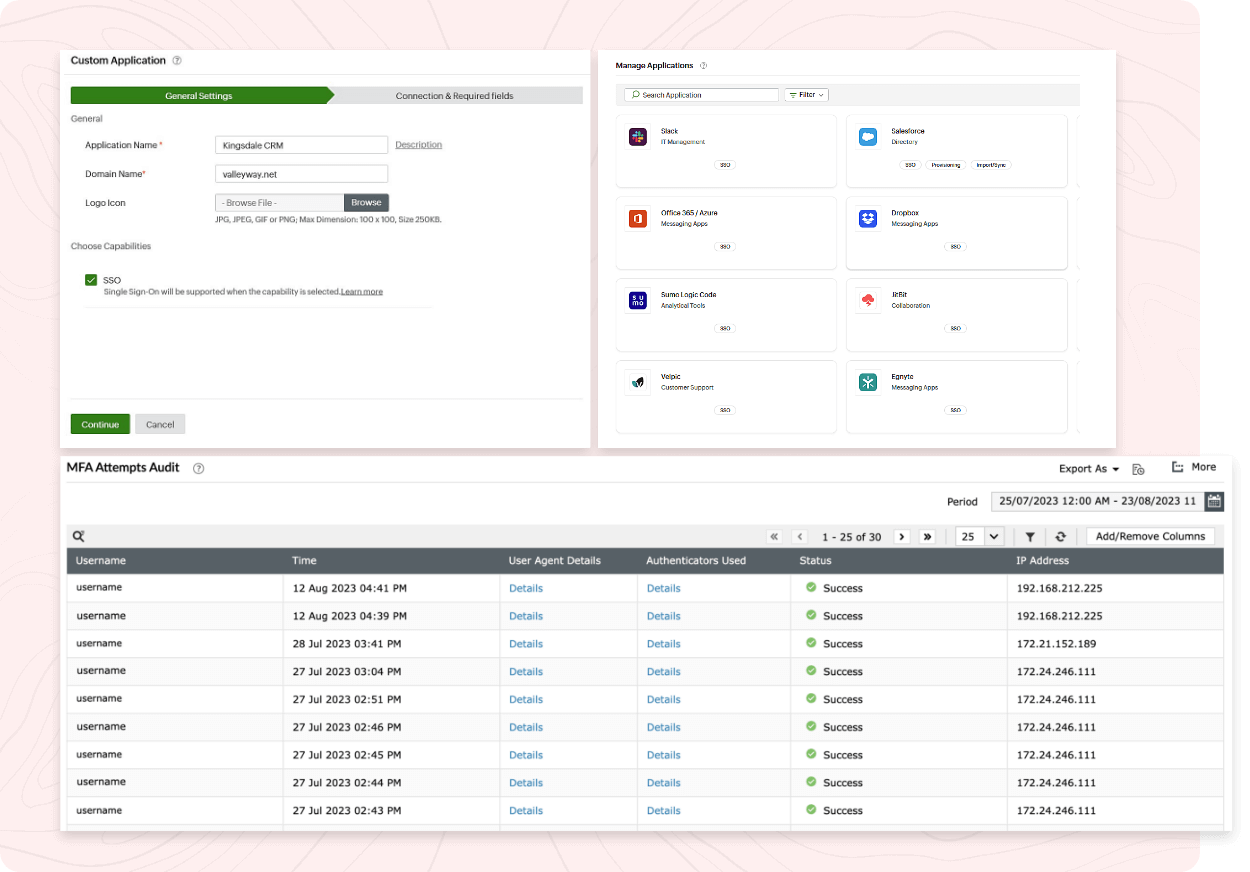
Identity360 provides secure SSO to a range of enterprise applications, both pre-integrated and custom, in just a few easy configuration steps.
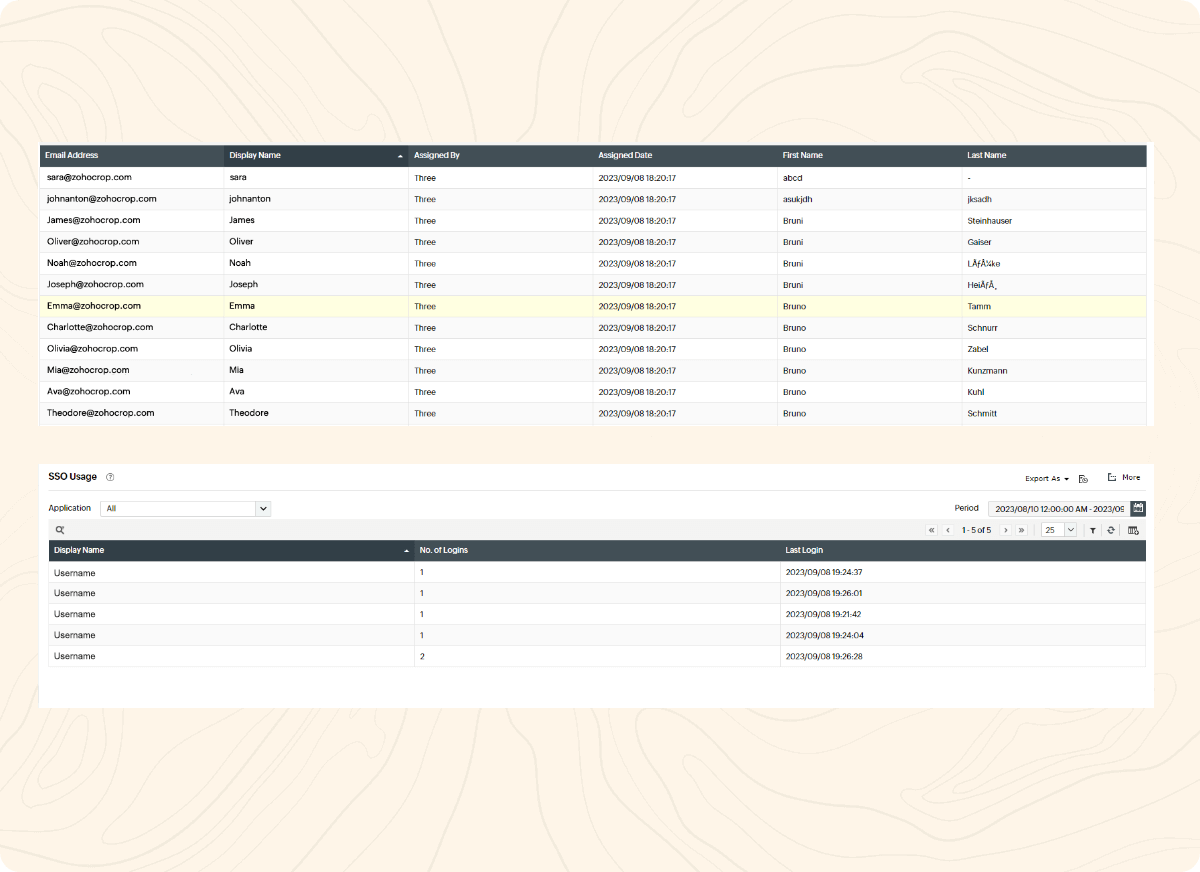
Users can conveniently access necessary applications from a centralized dashboard that provides a consolidated view of all applications assigned to them.
Without an SSO solution, your users will have multiple credentials to manage every day. Repeated logons to various platforms causes fatigue in users and decreases their productivity. Moreover, users handling multiple credentials themselves almost always means increased password management workload for admins. Identity360 gives your users secure, one-click access to enterprise applications using SSO. A vast range of pre-integrated and custom applications are supported, and each SSO attempt is secured with customizable MFA techniques.
Single sign-on, or SSO, is the process of giving users one-click access to multiple enterprise resources after an initial identity verification step. SSO allows users to access the resources assigned to them for a specific duration, and afterward they have to re-authenticate.
SSO, when backed by strong authentication factors, provides a reliable way to protect resources and improve the user experience at the same time. To fortify SSO in your organization, you can implement granular SSO controls. These controls include limiting the duration of each SSO session, allowing users to enable browser trust only for known and trusted devices, and providing them with SSO access to the right resources.
You can implement SSO with Identity360, which secures all application logins with modern MFA methods. It provides fine-grained MFA and SSO controls that can be customized to suit your organizational needs. Identity360 supports both IdP- and SP-initiated SSO to applications supporting SAML 2.0, OAuth, and OpenID Connect SSO protocols. Using consolidated SSO reports, you can track details such as the applications assigned to each user, the number of logons, failed logon attempts, and the last logon time of a user against each application.
To gain a better understanding of Identity360's SSO capability, please schedule a personalized web demo with our solution experts.
Unlocking efficiency with Universal Directory
Leverage identity storage for your organization with Universal Directory.
Learn moreRobust MFA techniques to secure your organizational identities
Identity360 provides comprehensive MFA capabilities to secure your enterprise against threats.
Learn moreEnhance workforce productivity through effective identity management
Identity360 provides end-to-end identity life cycle management capabilities.
Learn moreEmpower your IT admins to focus on tackling critical issues
Identity360 assists you in achieving delegation of routine management tasks with ease.
Learn moreCross-platform access management capabilities
Identity360 streamlines cross-platform access management for admins and end users.
Learn moreGain a comprehensive view of your organization's security and identity analytics through reports
Access valuable insights with detailed identity analytics reports.
Learn moreSource: *LastPass Article: Psychology of Passwords Report, †YubicoArticle: State of Password and Authentication Security Behaviors Report, ‡1Password Article: Unlocking the login challenge: How login fatigue compromises employee productivity, security and mental health