Zooming in on UEBA: Answering the “what” and the “how”
What is UEBA?
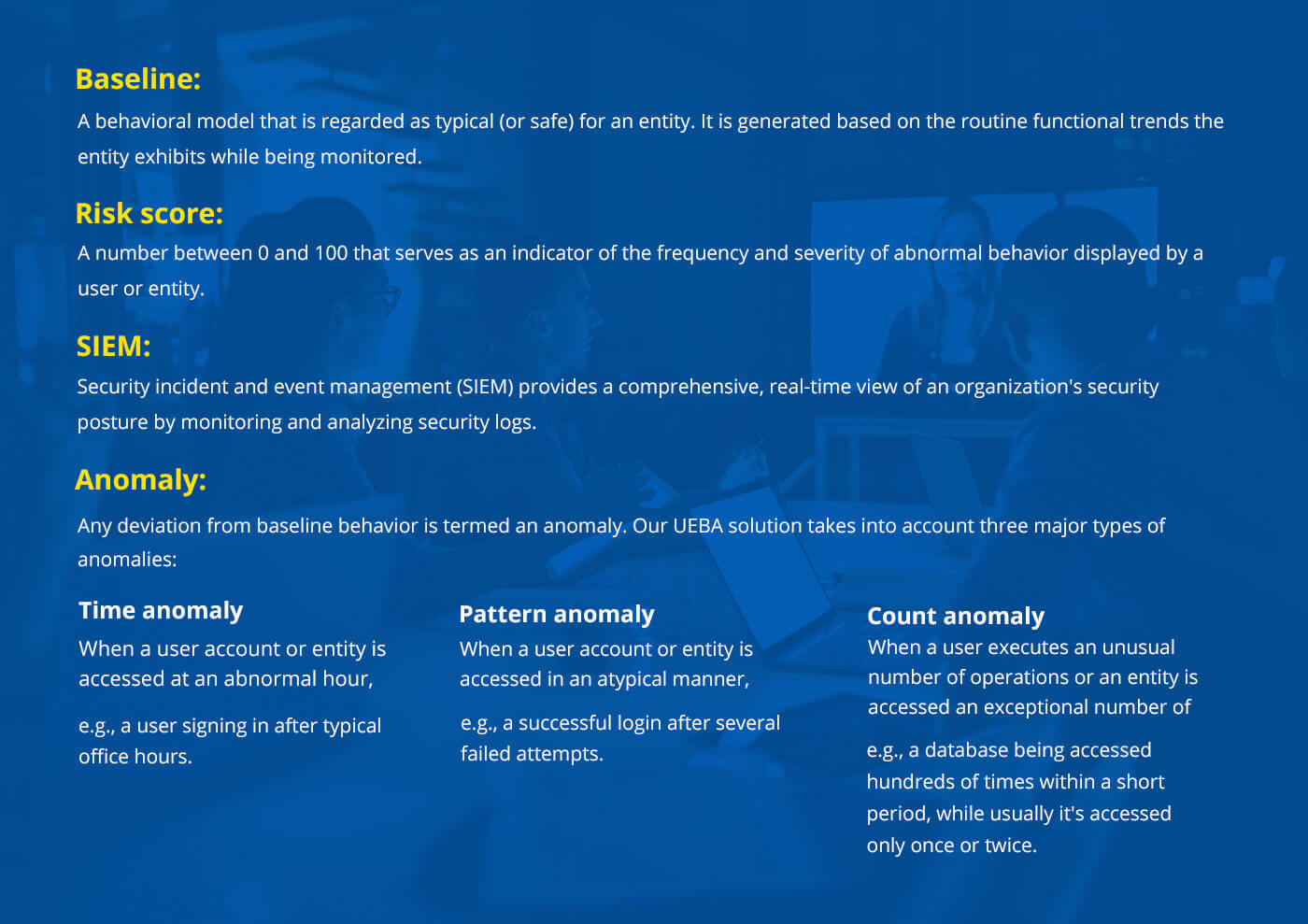
User and entity behavior analytics (UEBA) is a relatively new category of cybersecurity tools that utilize machine learning (ML) algorithms to detect abnormalities in the behavior of the users and entities that belong to an enterprise network. UEBA monitors and continuously learns from the behavior of various user accounts and devices in the network, and establishes a baseline behavioral profile for each using statistical and probability models. Following this, any action performed by a user or entity is compared with the baseline to determine if it’s normal or anomalous. Whenever an anomaly is identified, the risk score of the corresponding entity is increased, indicating to the network administrator that there’s a potential threat.
“Identities can be forged, but not behavior” is the premise on which UEBA operates.
Before we dive deeper, let’s have a look at some UEBA terminologies
UEBA observes and adapts
UEBA closely monitors the activities of each user and entity belonging to a network, and learns their mannerisms or operational patterns. Our UEBA solution works in association with SIEM solutions by using activity logs to derive insights about the normal behavior of the entities.
Risky or not risky: UEBA decides
The following figure depicts a typical day at work for George Langdon, who works as a marketing intern at ABC Corp.

As we saw earlier, when there is a deviation from expected behavior, the risk score of the entity will increase. Let's assume that George's system is still active past 4pm. While this could be an intruder who has gained illicit access to George's computer, the possibility of George himself working longer hours to complete his work cannot be ruled out. If the latter is the reason for the system being accessed at an unlikely hour, increasing the risk score serves as a false alarm.
To prevent situations like these, UEBA evolves seamlessly. It learns from the entities, and is capable of altering what is considered normal behavior. In this case, UEBA will first increase George's risk score, but keep check on his logs. As working for longer hours becomes his routine, UEBA recognizes the pattern and brings down the risk score in turn.
Advanced analytics: The brain behind UEBA
The continuous evolution of UEBA is made possible with the help of ML, both supervised and unsupervised. In supervised ML, the system is provided with a set of desirable and undesirable behaviors. When UEBA detects any undesirable behavior, it increases the risk score. Unsupervised ML for UEBA is the smarter version, which identifies typical and anomalous behaviors on its own. It employs two main statistical models, robust principal component analysis (RPCA), and Markov chains to conclude if an action is normal or not.
RPCA:
RPCA is a variation of the widely used principal component analysis (PCA) technique. It's a statistical procedure that uses an orthogonal transformation to convert a set of observations of possibly correlated variables (data points) into linearly uncorrelated variables called principal components. The line of best fit is established for the set of principal components, and the data points that deviate from this line of best fit are termed to be anomalous.
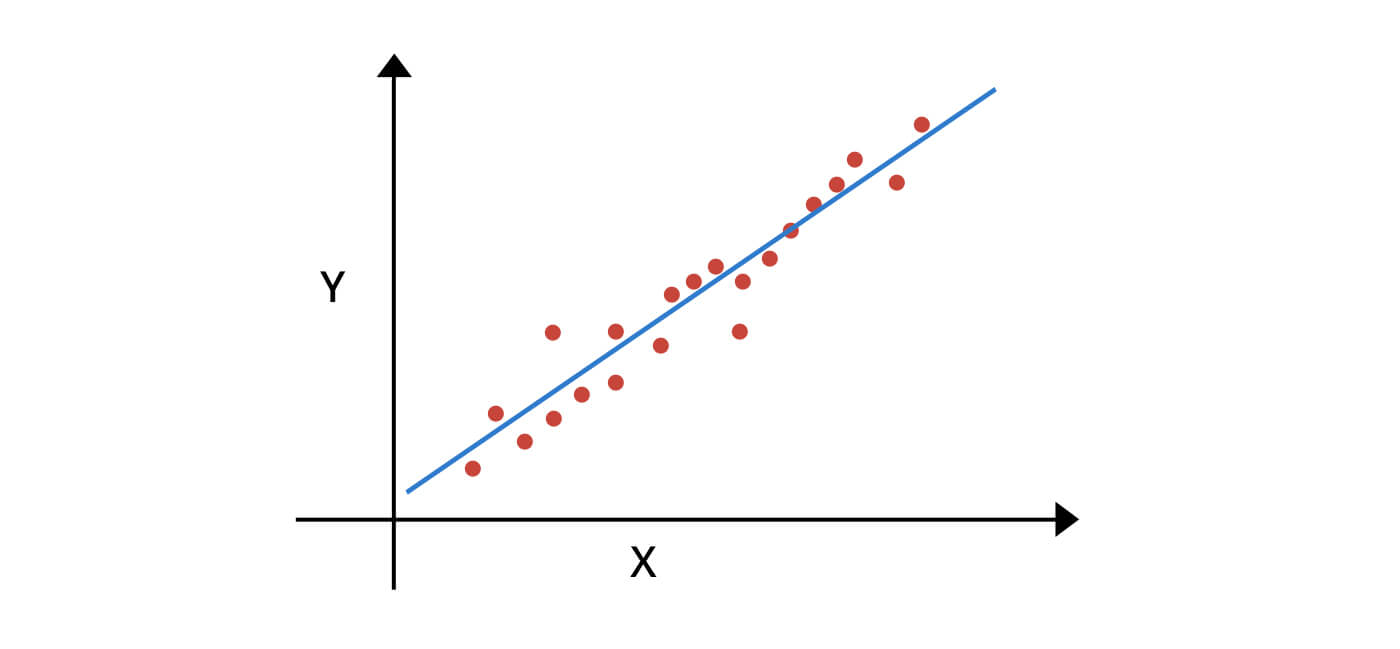 RPCA finds the direction of "the line of best fit" for a set of data points
RPCA finds the direction of "the line of best fit" for a set of data points
Markov chains:
A Markov chain is defined as a sequence of stochastic events where the probability of the next event in a chain is dependent only on the state of the current event. A list is created by determining the successive state of occurrences of events. Further, as each event unfolds, it's compared with the predicted sequence of events. If any event deviates from the probable list of events, it's considered an anomaly, and the risk score of the corresponding entity is increased.
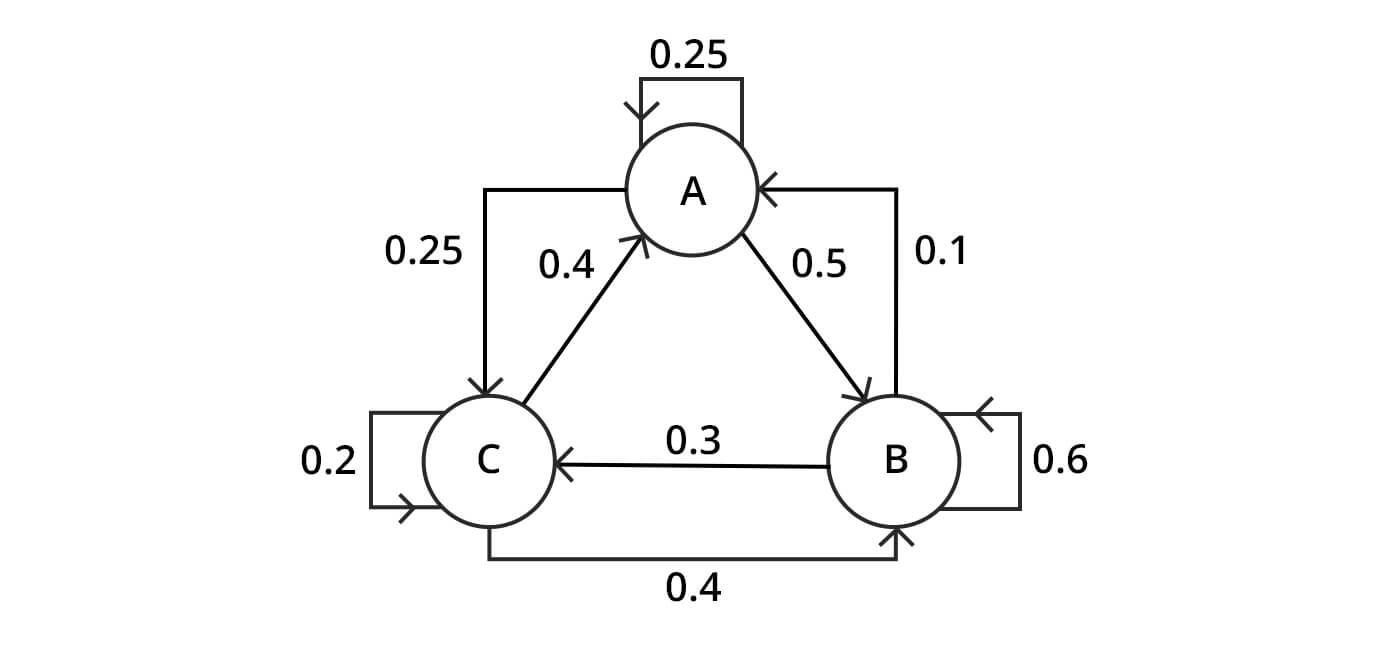 A three-state Markov process, with the states labeled A, B and C.
A three-state Markov process, with the states labeled A, B and C.
UEBA protects against a myriad of cyberattacks, such as brute force attacks, insider threats, lateral movement, hacking, and more.
Learn more about how UEBA defends your enterprise by reviewing our previous post, UEBA: The intelligent guardian of your business.