- Home
- Logging Guide
- The importance of firewall logging and monitoring in network security.
The importance of firewall logging and monitoring in network security.
In this page
- Significance of firewall logs
- - Identifying malicious activities
- - Verifying firewall rules
- - Bandwidth planning
- - Blacklisting malicious sources
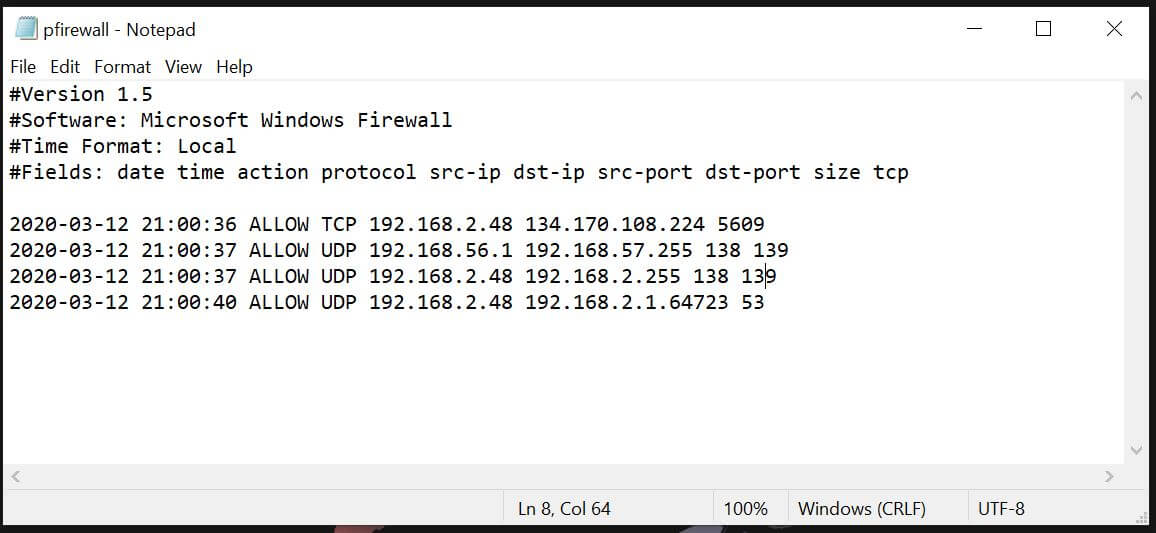
A firewall monitors the traffic to and from the network and protects the network in which it's deployed from malicious traffic. It is a network security system that monitors incoming and out going traffic based on some predefined rules. It records information on how it manages the traffic in the form of logs. The log data contains the source and destination IP address of the traffic, port number, protocols, and more. To protect your network from security attacks effectively, it's essential that you collect and analyze these firewall logs.
Significance of firewall logs
Understanding when and how firewall logs can be used is a crucial part of network security monitoring. Here are some use cases where firewall logging can be useful.
- Monitoring the network traffic and identifying malicious activities
The foremost function of a firewall log is to provide information on network traffic. This includes information about the nature of the incoming and outgoing traffic and the security threat attempts at the periphery of the network, based on which remediation actions can be initiated. Firewall logs also provide information on malicious activities happening within the network. However, the source of the activity cannot be identified with the minimal information that the firewall logs provide.
- Verifying the newly added firewall rules
A firewall rule allows or denies traffic from or to a specific IP address. However, just configuring firewall rules isn't enough to protect the network. These rules should be augmented with a logging feature so that you get to analyze if the rules are working properly and any changes made to the rules are legitimate.
- Bandwidth requirement planning
Based on the information about the bandwidth usage across the firewall, the bandwidth requirement can be planned.
- Blacklisting of malicious sources
Threat intelligence provides the information about known malicious actors. The threat feeds from sources such as STIX, TAXII, etc. can be used to identify known malicious IPs. Enabling logging and monitoring of firewall logs can help you detect an access attempted from such an IP address, and block it right away using a firewall rule.
Also, if there are multiple unsuccessful requests to access the firewall or any other high profile system in the network from a single IP address (or from a group of IP addresses), this could probably be a security threat. After carefully analyzing the logs, a new rule can be defined to block that IP.
In short, firewall logs provide information about the network traffic and help to identify and block malicious sources that try to intrude a network, thereby ensuring network security.