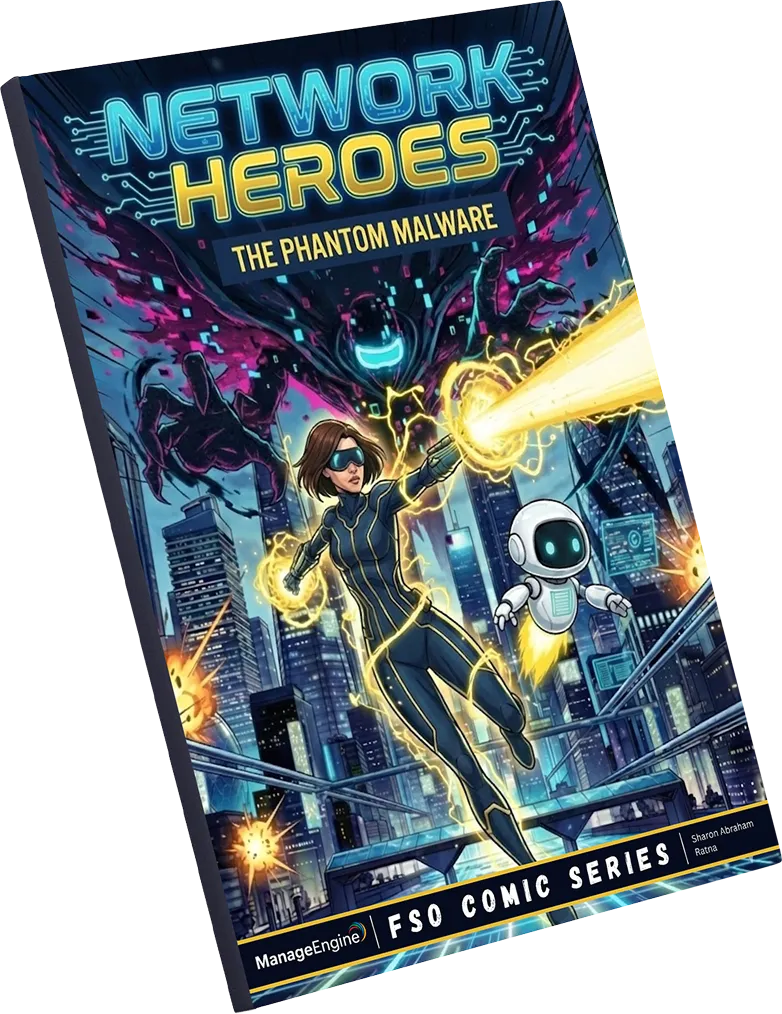
Gear up for a high-stakes cyber chase
The Threat
A threat signature that doesn't exist in any known database is moving fast toward the core vault.
The Hunt
Dive into the network layer where Eva and Zia use deep packet inspection to hunt down the polymorphic threat.
The Win
Witness how our advanced security analytics expose the invisible enemies lurking in your traffic.
Here's a sneak peak inside
Experience the Full Narrative
See how polymorphic threats evade signatures and how you can hunt them with network traffic analytics.
Download the Comic