10 cloud security threats CXOs can’t ignore in 2026

Summary
This article breaks down the top 10 cloud security threats enterprises face today, from misconfigurations and identity abuse to supply chain compromises, DDoS-driven EDoS attacks, and advanced persistent threats. It explains how these risks translate into real business impact such as regulatory penalties, downtime, rising cloud spend, and customer trust erosion, while outlining practical steps CXOs can take to strengthen governance, resilience, and cloud security posture at scale.
Cloud adoption has matured across every industry, but the threat landscape around cloud environments has evolved even faster. Attackers exploit even the tiniest identity gaps, misconfigurations, exposed APIs, and automation pipelines that were never designed with adversarial behavior in mind.
For CXOs, cloud security threats directly affect business continuity, regulatory exposure, customer trust, and the organization’s ability to scale safely.
What are cloud security threats?
Cloud security threats are risks that target cloud-hosted workloads, data, identities, and services across public cloud, private cloud, hybrid environments, and SaaS platforms. These threats can originate from external attackers, insider misuse, third-party compromise, or unintentional misconfiguration.
Unlike traditional security, cloud security threats are heavily driven by these factors:
Identity and access control failures
Shared responsibility gaps
Misconfigured cloud services and policies
API-first architectures and automation pipelines
Why are cloud security threats are rising?
Cloud providers secure the infrastructure. Enterprises still own security for:
IAM policies and access governance
Application logic and APIs
Data classification and encryption
Configuration, monitoring, and incident response
This is why many cloud breaches occur without any “hack” in the traditional sense. The attacker simply finds an exposed storage bucket, a leaked access token, or an over-permissioned workload identity.
The most common cloud security threats enterprises face today
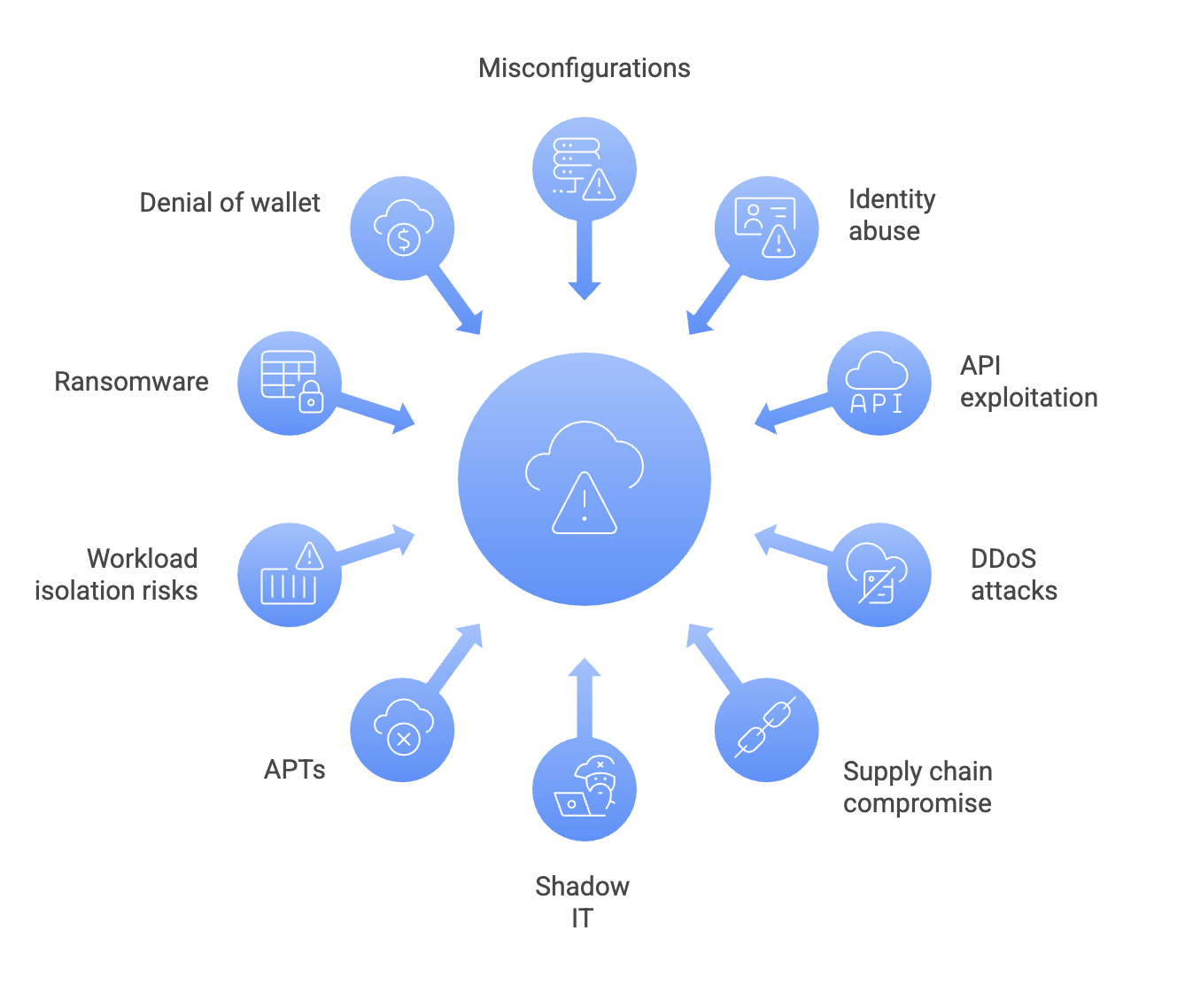
1. Misconfigurations and exposed cloud services
Misconfigurations remain the most common cause of cloud breaches because cloud environments frequently change through automation and self-service. Exposed buckets, unsecured dashboards, and permissive security groups regularly leak sensitive data.
Example: In late 2025, Security researchers discovered that Ernst and Young had around 4 TB of SQL server data publicly accessible on Azure due to misconfiguration. The incident highlighted how simple cloud setup errors can expose massive volumes of sensitive data, even when hosted on enterprise cloud infrastructure.
2. Identity and access abuse (IAM failures)
Identity is the new perimeter in cloud. Compromised credentials, leaked API keys, and over-privileged service accounts are primary targets. Attackers can escalate privileges and access sensitive data without breaking into infrastructure.
Example: The Snowflake data theft campaign in 2024 targeted over 100 enterprise customers, including Ticketmaster and Santander Bank. Attackers used stolen credentials to bypass systems that lacked enforced MFA, leading to the theft of hundreds of millions of customer records.
3. Cloud API exploitation and API abuse
Cloud environments expose APIs for automation, microservices, and third-party integrations. Weak authentication, missing rate limiting, or business logic flaws in APIs enable credential stuffing, data scraping, and unauthorized access.
Example: TransUnion experienced a breach in July 2025 impacting 4.4 million customers. Attackers exploited misconfigured API permissions within a third-party Salesforce integration, allowing them to pull sensitive credit-related data without triggering standard access alerts.
4. DDoS and application-layer traffic attacks
Distributed Denial of Service attacks have evolved from network floods to sophisticated application-layer assaults aimed at API endpoints and login services. These can degrade performance without infrastructure downtime. In 2025, Cloudflare reported a huge surge in DDoS attacks, totaling up to an unprecedented 47.1 million, mitigating an average of over 5,300 attacks hourly.
5. Cloud supply chain compromise (CI/CD, containers, dependencies)
Modern cloud applications depend on third-party libraries, container images, and CI/CD pipelines. Attackers now target these upstream components to insert malicious code that propagates downstream to production workloads. To reduce this risk, enterprises should standardize SBOMs, enforce artifact signing, and integrate dependency + container scanning into build and deployment workflows to prevent compromised components from reaching production.
6. Shadow IT and unsanctioned SaaS usage
Employees frequently adopt SaaS tools and integrations without IT oversight, creating blind spots in security and data governance. These unsanctioned systems often bypass logging, access controls, and compliance measures.
7. Advanced persistent threats (APTs) targeting cloud environments
APTs operate quietly over long periods, often targeting cloud identity, management consoles, and privileged services. Their objective is long-term access and data exfiltration rather than immediate disruption.
8. Insecure workload isolation (multi-tenant and container escape risks)
Cloud platforms depend on strong isolation between containers, serverless runtimes, and tenants. If isolation breaks due to a vulnerability or weak runtime controls, attackers can escape a compromised workload and access other services or data. This is especially risky in Kubernetes-heavy environments.
9. Ransomware and cloud backup destruction
Modern ransomware actors extort victims by encrypting cloud-hosted data and then targeting backup and recovery systems to force payment. Losing backups often leaves enterprises without a path to recovery.
10. Denial of Wallet (cost-exhaustion attacks)
Cloud billing models introduce a new attack surface where adversaries deliberately trigger excessive scaling, API calls, or serverless executions to drive runaway costs rather than downtime. These attacks directly impact financial operations. This is where Economic denial of sustainability (EDoS) becomes critical. EDoS attacks intentionally push workloads into auto-scaling loops, forcing organizations to burn compute, bandwidth, and API usage until cloud spend spikes massively. Even if availability is maintained, the business impact shows up through unexpected bills, degraded service performance, and forced throttling decisions.
Emerging threats
Along with traditional cloud security threats, 2026 is seeing a growing class of AI-driven risks. One of the biggest is Shadow AI, where teams adopt external GenAI tools, copilots, or hosted model APIs without formal security review. This can lead to unintentional data leakage, regulatory violations, and loss of control over sensitive prompts, logs, and outputs.
At the same time, attackers are increasingly using AI to scale phishing, automate reconnaissance, and generate more convincing social engineering payloads, making identity compromise faster and harder to detect.
How cloud security threats translate to business risk for CXOs
Cloud security threats can no longer stay contained within the technology team. In cloud environments, security failures typically spill into compliance, finance, customer trust, and operational continuity. For CXOs, this makes cloud security a board-level risk that directly impacts business performance.
Cloud threats create measurable business consequences:
Regulatory penalties and audit failures
Misconfigurations, weak access controls, and poor logging can quickly become compliance violations, especially in regulated industries like banking, healthcare, and telecom. Even without a breach, failing an audit can lead to fines, delayed product launches, or loss of certifications that customers and regulators expect.Downtime and revenue loss
Cloud attacks such as DDoS, ransomware, or identity compromise can take critical services offline. Even short outages can cause lost transactions, reduced productivity, and SLA penalties. For digital-first businesses, downtime is not just disruption, it is immediate revenue leakage.Data breach notification costs
When sensitive data is exposed, the cost is not limited to remediation. Organizations face mandatory breach notification requirements, legal fees, forensic investigations, and customer support overhead. In many cases, the long-term cost comes from reputational damage and customer attrition, not the breach response itself.Increased cyber insurance premiums
Cyber insurers are tightening underwriting requirements for cloud security controls such as MFA, identity governance, logging, and incident response readiness. A major incident or weak security posture can increase premiums significantly, reduce coverage, or introduce stricter exclusions.Brand damage and customer churn
In cloud-native environments, breaches often become public quickly. Customers may lose confidence even if the incident is contained. This is especially damaging in competitive markets where trust is a differentiator and switching costs are low.Higher cloud spend from abuse or inefficiency
Cloud threats can directly inflate operational costs. Examples include cryptomining malware, resource hijacking, and denial of wallet attacks that intentionally trigger usage-based billing spikes. Even non-malicious gaps like poor access governance and lack of policy enforcement can lead to uncontrolled sprawl and wasted spend.
The bottom line
Cloud security is now a governance and resilience issue. The organizations that handle it well treat cloud security as part of business continuity, financial control, and risk management, and not as a technical checkbox.
Best practices for CXOs to reduce exposure to cloud security threats
Cloud security is rarely compromised because a single control failed. It usually breaks down due to gaps across identity, configuration, workload protection, and visibility. The strongest cloud security programs treat protection as a continuous operational process, not a periodic audit. CXOs can stay ahead of threats with the following practices:
Start with identity as the primary security perimeter. Most cloud incidents still begin with stolen credentials, weak access governance, or overly broad permissions. Enforcing least privilege, reducing standing access, and adopting just-in-time privileged access models significantly limits how far an attacker can move even after an account is compromised.
Make misconfiguration management continuous, not reactive. Cloud environments evolve too quickly for annual assessments or manual audits to keep up. Organizations should use CSPM capabilities to detect risky configurations in real time, prioritize high-impact exposures such as public storage and open security groups, and automate remediation wherever possible.
Extend protection to workloads and runtime behavior. Securing cloud infrastructure alone is not enough when modern attacks target containers, Kubernetes, APIs, and serverless runtimes. A strong cloud security posture includes segmentation to reduce lateral movement, runtime monitoring for suspicious execution, and policy enforcement for deployment hygiene such as image scanning and workload identity controls.
Treat APIs as the modern attack surface. Since cloud-native systems are heavily API-driven, teams must build API security into the architecture itself. This includes strong authentication, rate limiting, request validation, and protections against automated abuse. These controls reduce the likelihood of API exploitation, credential stuffing, and cost-driven attacks such as denial of wallet scenarios.
Secure the software supply chain and CI/CD pipeline. Attackers increasingly target build systems because they provide indirect access to production environments. CXOs should ensure that pipelines follow strong controls around secrets management, dependency scanning, artifact integrity, and restricted permissions, so a pipeline compromise does not become a cloud-wide breach.
Improve detection by centralizing cloud telemetry and correlating threats. Many organizations technically collect logs but lack the ability to detect threats early. Centralizing identity events, workload logs, cloud audit trails, and network telemetry into a unified detection layer is essential for faster investigation and containment.
Plan for disruption as a business scenario, not just a technical one. DDoS attacks, cloud service degradation, and region-level failures are increasingly common. Resilience strategies should include DDoS protection, autoscaling safeguards, failover planning, and tested incident response playbooks that reduce both downtime and uncontrolled cloud spend during attacks.
Cloud threats are inevitable, but the chaos is optional. CXOs must decide whether to view cloud security as a collection of tools or as a comprehensive system of controls. The enterprises that reduce breach exposure and downtime will always be the ones that harden identity, enforce guardrails, validate continuously, and operationalize security into everyday cloud decisions.