Next-generation firewalls: The key to future-proof security in 2026
Summary
This article explains how a next generation firewall (NGFW) addresses the limitations of traditional firewalls in modern, distributed IT environments. It outlines key capabilities such as application awareness, deep packet inspection, intrusion prevention, and identity-based controls that enable more effective threat detection and response.
The article also explores how NGFWs work, compares them with traditional firewalls, and highlights their business benefits, from reducing breach risk to improving visibility and operational efficiency. It further covers common implementation challenges, what to look for when choosing a solution, and best practices for successful deployment, positioning NGFWs as a critical component of modern cybersecurity strategy.
Modern cyberthreats no longer announce themselves. Malicious activity increasingly hides within legitimate applications, trusted users, and encrypted traffic, making it harder than ever for traditional security controls to keep up.
In a recent report by IBM, 97% of organizations reported an AI-related security incident while lacking proper AI access controls, highlighting a growing gap between evolving threats and outdated defenses.
This is where a next generation firewall becomes critical. By bringing context, intelligence, and real-time analysis into network security, it enables organizations to detect and stop threats that conventional firewalls simply cannot see.
What is a next-generation firewall?
A next-generation firewall (NGFW) is an advanced network security solution that goes beyond traditional firewalls by combining deep packet inspection, application awareness, and intelligent threat prevention.
Unlike legacy firewalls that rely mainly on IP addresses and ports, NGFWs understand who, what, and how traffic is flowing across the network.
Key features of a next-generation firewall
An NGFW stands out from traditional firewalls through a set of advanced capabilities that provide deeper visibility, smarter control, and proactive threat prevention.
Application awareness and control
NGFWs can identify and control applications regardless of port or protocol, giving teams far greater visibility into how the network is actually being used. Instead of blanket rules, administrators can define granular policies based on specific applications, usage patterns, or risk levels. This helps reduce shadow IT and ensures bandwidth and access are prioritized for critical services.
Example: Allow Microsoft Teams for collaboration but restrict unauthorized file-sharing or high-risk apps that could expose sensitive data.
Deep packet inspection
Deep packet inspection (DPI) goes beyond basic header checks to analyze the actual payload of network traffic. This allows NGFWs to uncover threats hidden inside seemingly legitimate requests, such as malware embedded in HTTP or encrypted traffic patterns that indicate suspicious behavior. DPI is essential for detecting attacks that evade traditional signature-based defenses.
Integrated intrusion prevention system
NGFWs come with built-in intrusion prevention system (IPS) capabilities that continuously monitor traffic for known attack signatures and exploit techniques. They can automatically block malicious activity—such as buffer overflow attempts or vulnerability exploitation—before it reaches critical systems. This real-time protection reduces reliance on separate security tools and speeds up response times.
User identity awareness
Instead of relying solely on IP addresses, NGFWs map network activity to individual users and roles by integrating with identity providers like Active Directory. This enables more precise policy enforcement—for example, allowing developers access to specific resources while restricting the same access for other users. It also improves auditability and accountability across the network.
Advanced threat protection
Modern NGFWs incorporate multiple layers of advanced threat defense, including sandboxing, threat intelligence feeds, and behavioral analysis. Suspicious files can be executed in isolated environments to detect zero-day threats, while continuous updates from global threat intelligence help identify emerging attack patterns. This layered approach ensures protection against both known and unknown threats.
How a next-generation firewall works
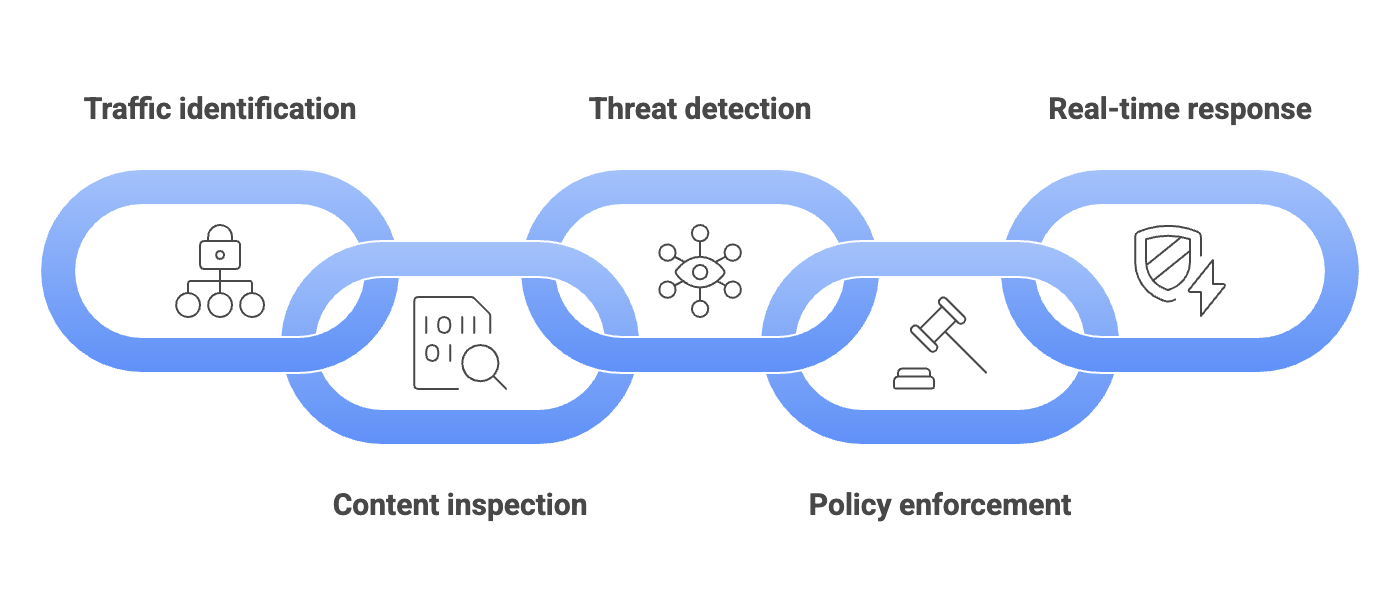
At a high level, an NGFW operates by combining multiple layers of inspection, context, and intelligence to evaluate every piece of traffic before allowing it through. Instead of making decisions based on isolated parameters, it continuously correlates data across users, applications, and behaviors.
Traffic identification
The NGFW first identifies who and what is generating the traffic and maps it to specific users, devices, and applications rather than just IP addresses. This allows it to distinguish between sanctioned SaaS tools and unauthorized shadow IT, even when both use the same ports and protocols.
Content inspection
Using DPI, the firewall analyzes the actual content within data packets, including encrypted traffic where possible. By examining payloads in detail, it can uncover malware hidden within file uploads or detect suspicious patterns in otherwise legitimate web traffic.
Threat detection
The NGFW correlates traffic with known attack signatures, behavioral patterns, and threat intelligence feeds to identify both known and emerging threats. It can also detect anomalies, such as unusual lateral movement within the network or unexpected communication with external command-and-control servers, before they escalate.
Policy enforcement
Based on this context, the firewall enforces granular security policies that factor in application type, user identity, device posture, and risk level. This enables organizations to allow access to sensitive systems like financial platforms only for authorized users while restricting the same access for others or limiting high-risk applications on unmanaged devices.
Real-time response
Finally, the NGFW takes immediate action, blocking malicious traffic, alerting security teams, or isolating affected systems. This rapid response helps stop threats like ransomware before they can encrypt critical data and prevents compromised endpoints from spreading attacks across the network.
Next-generation firewalls vs. traditional firewalls
| Aspect | Traditional Firewalls | Next Gen Firewalls |
|---|---|---|
| Traffic inspection | Primarily based on IP addresses, ports, and protocols | Deep, context-aware inspection, including applications, users, and content |
| Application visibility | Limited or none; cannot distinguish apps using same ports | Full application awareness, even for apps using non-standard ports |
| Threat detection | Relies on basic rule sets; limited ability to detect advanced threats | Advanced detection using IPS capabilities, DPI, behavioral analysis, and threat intelligence |
| User awareness | No user-level visibility; policies tied to IP addresses | Identity-based policies mapped to users, roles, and groups |
| Encrypted traffic handling | Minimal or no SSL/TLS inspection | Can inspect encrypted traffic to detect hidden threats |
| Policy enforcement | Static and coarse-grained rules | Granular, dynamic policies based on context (user, app, device, and risk) |
| Intrusion prevention | Often requires separate solutions | Built-in IPS with real-time threat blocking |
Business benefits of a next generation firewall
Beyond technical capabilities, an NGFW delivers tangible business value by strengthening security while supporting operational efficiency.
Reduced risk of breaches: By combining deep inspection, threat intelligence, and real-time response, NGFWs can identify and stop advanced threats such as ransomware or application layer attacks before they disrupt operations or lead to data loss.
Improved operational efficiency: Instead of managing multiple stand-alone tools (firewall, IPS, and application control), teams can rely on a single, unified platform. This simplifies management, reduces tool sprawl, and frees up IT resources for higher-value initiatives.
Better visibility and control: With detailed insights into applications, users, and traffic behavior, organizations gain a clearer understanding of how their network is being used. This enables more informed decision-making, faster troubleshooting, and tighter policy enforcement.
Support for modern work environments: NGFWs are designed for today’s distributed environments, securing remote users, cloud applications, and hybrid infrastructures without compromising performance or the user experience.
Cost optimization over time: While initial investment may be higher, consolidating multiple security functions reduces licensing, maintenance, and integration costs. Additionally, preventing security incidents helps avoid the significant financial and reputational impact of breaches.
Challenges of implementing a next-generation firewall
While an NGFW offers significant security advantages, organizations may encounter a few practical challenges during deployment and ongoing operations:
Increased complexity: NGFWs combine multiple capabilities—DPI, IPS, application control, and more—into a single platform. This added functionality can make configuration and management more complex, especially for teams without specialized security expertise.
SSL/TLS inspection challenges: Inspecting encrypted traffic is essential for modern security, but it can be resource-intensive and raises privacy and compliance considerations. Improper handling may also break certain applications or user experiences.
Policy management complexity: With granular, context-aware policies comes the risk of overly complex rule sets. Misconfigurations can lead to security gaps, unintended access, or disruptions to legitimate business applications.
Cost considerations: Compared to traditional firewalls, NGFWs can involve higher upfront costs, licensing fees for advanced features (like threat intelligence or sandboxing), and ongoing maintenance expenses.
Skilled resource requirements: Operating and optimizing an NGFW effectively requires trained personnel who understand both networking and advanced security concepts. Organizations may need to invest in training or rely on managed services.
What should you look for in a next-generation firewall?
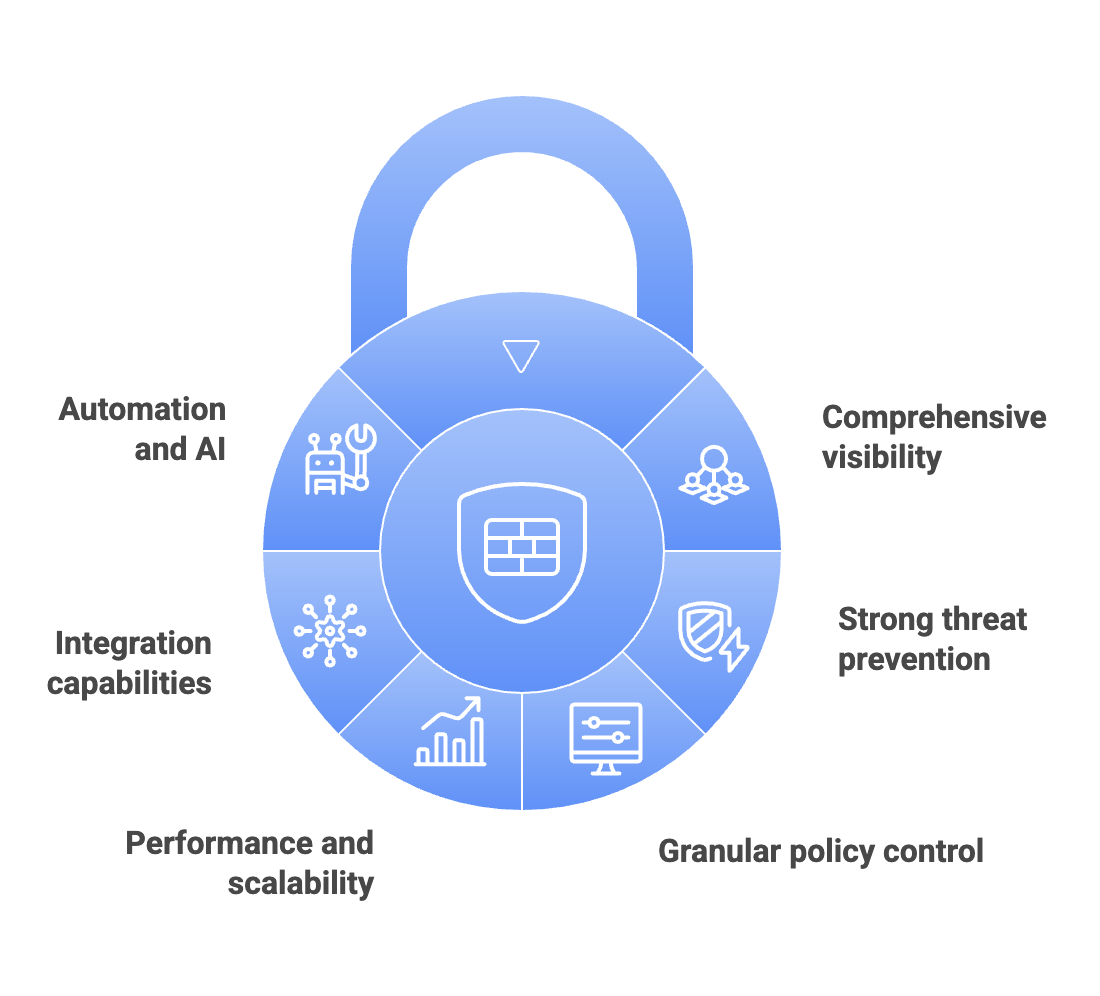
Choosing the right next generation firewall requires evaluating how well the solution fits your organization’s security needs, scale, and operational model.
Comprehensive visibility
Look for a firewall that provides clear visibility into applications, users, devices, and traffic patterns. The ability to monitor encrypted traffic and generate actionable insights is critical for effective threat detection.
Strong threat prevention capabilities
Ensure the NGFW includes integrated features like intrusion prevention, malware detection, sandboxing, and access to up-to-date threat intelligence. These capabilities should work together seamlessly to detect both known and unknown threats.
Granular policy control
The solution should support context-aware policies based on user identity, application type, device posture, and risk level. This allows for precise control without disrupting legitimate business activities.
Performance and scalability
Evaluate how the firewall performs under load, especially with advanced features like DPI and SSL inspection enabled. It should be able to scale with your organization’s growth without introducing latency.
Integration capabilities
The NGFW should integrate smoothly with your existing ecosystem—identity providers, SIEM tools, endpoint security, and cloud platforms—to enable unified visibility and faster incident response.
Automation and AI-driven insights
Modern NGFWs increasingly incorporate automation and AI to reduce manual effort, prioritize alerts, and improve threat detection accuracy. This can significantly enhance efficiency for security teams.
The takeaway for CXOs
While adopting an NGFW can introduce challenges, the benefits significantly outweigh them, and can be effectively managed with a thoughtful implementation strategy.
A successful rollout typically includes:
Start with visibility: Monitor traffic and application usage before enforcing strict policies.
Adopt a phased approach: Gradually enable features like IPSs, application control, and SSL inspection.
Align with business needs: Define policies based on critical applications, users, and risk levels.
Invest in skills: Train internal teams or leverage managed services for effective operation.
Integrate with existing tools: Connect with identity systems, SIEM tools, and endpoint security platforms for better context,
Plan for scale: Ensure the firewall is sized to handle current and future traffic loads.
Ultimately, in an environment where threats increasingly hide within legitimate traffic, an NGFW provides the context, intelligence, and real-time response that traditional approaches lack. It transforms network security from a reactive control point into a proactive, strategic capability and helps organizations stay secure while continuing to scale and innovate.