Combating threats with UEBA: Cyberattacks in manufacturing
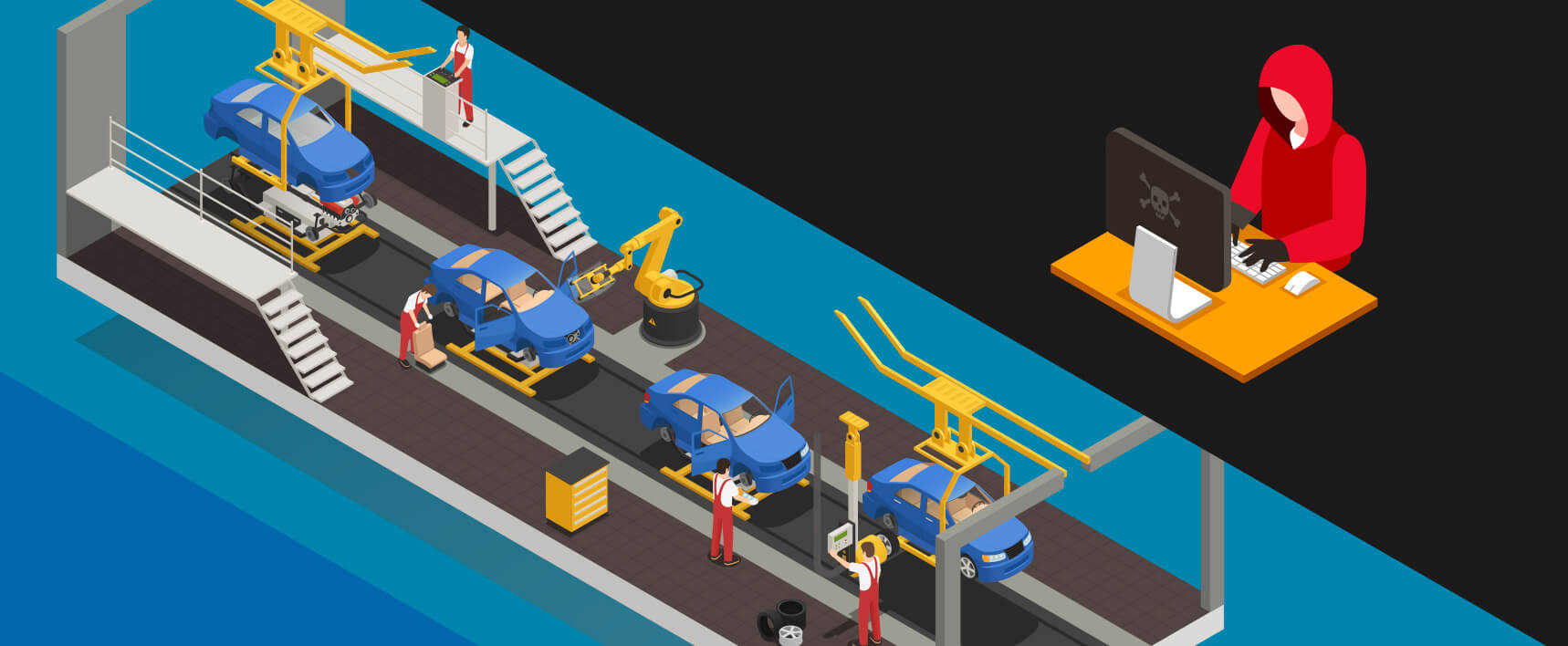
In this four-part series, we explore hypothetical cyberattacks inspired by real-life events in four different industries: healthcare, finance, manufacturing and education. We'll take a look at unforeseen security attack scenarios, and discover how user and entity behavior analytics (UEBA) can be leveraged to safeguard organizations. In the third post of the series, we'll examine cyberattacks that threaten the manufacturing sector.
Manufacturing menaces
We're in the midst of Industry 4.0, the fourth industrial revolution where connected computer systems are disrupting the way in which industries operate. With the emerging prevalence of high speed internet connectivity, the cloud, industrial internet of things (IIoT) devices, smart sensors that capture almost every detail, and other technological advances, the manufacturing sector has seen some major benefits.
While accuracy, scale, and efficiency of production have increased tremendously, this fusion of physical and cyber states also exposes the manufacturing sector to sophisticated cyberthreats. Let's discuss some of the potential cyberattacks in this sector and how UEBA can help IT administrators combat them.
The watering hole
Dr. Ryan Cooper is a product development scientist at Ecocog, one of the most prominent electric vehicle manufacturing companies in the world. Cooper regularly downloads design applications from vendor websites for research purposes.
Unbeknown to Cooper, a hacker group called Red Panda has been trying very hard to gain entry into Ecocog's network. After numerous failed attempts to penetrate the network through phishing attacks, Red Panda decides to utilize the watering hole technique, which involves infecting websites that the target visits frequently, to gain entry. To the group's delight, Cooper downloads industrial design software from a vendor's website compromised by Red Panda.
 Red Panda tries to steal information about Ecocog's SCADA devices
Red Panda tries to steal information about Ecocog's SCADA devices
The downloaded software contains malware that includes an open platform communication (OPC) scanning module and a remote access Trojan (RAT) that work in tandem to relay information about the supervisory control and data acquisition (SCADA) devices in the network to the hackers' command and control (C&C) server. Once the software is downloaded, the malware begins running in the background. The OPC scanner sends multiple queries to the remotely connected SCADA devices and creates numerous text files to store the returned values.
While Red Panda eagerly waited for the malware to send them information about the manufacturing units, the user and entity behavior analytics (UEBA) solution, which Ecocog had recently incorporated, detected pattern and count anomalies as the malware made multiple queries to the SCADA servers and created numerous text files in quick succession. Once the anomalies were detected, the risk score of Cooper's workstation spiked, alerting the IT administrators who quarantined the system before it could transmit information to the C&C server, once again successfully thwarting Red Panda's attempt to steal sensitive data.
The wiper
Thomas Vegetable Oil Inc., a major player in the edible oil manufacturing industry, was in the news recently as it succumbed to a wiper attack. In this attack, malware completely erased the master boot record of thousands of computers belonging to the network, bringing the company to a complete standstill. The hackers made their way into the industrial floor of the network by compromising the organization's connected gas leakage sensor using password spraying.
From the sensor, which is a peripheral device, they moved laterally into the network, gaining access to the central server to which the sensor routinely transmits data, and tactically planted the malware. Even though the company had all its data backed up, recovery proved to be time-consuming. Thomas Vegtable Oil Inc. incurred steep losses when the plant was shut down for the several days it took to recover from the attack.
 Thomas Vegetable Oil Inc faces complete data loss due to the wiper attack
Thomas Vegetable Oil Inc faces complete data loss due to the wiper attack
Such a catastrophe could have been completely prevented had Thomas Vegetable Oil Inc. had an efficient UEBA tool in place. UEBA is adept in monitoring not just the user accounts but also various IIoT devices that form a manufacturing company's ecosystem. By feeding the logs generated by fire and gas leakage sensors into a UEBA solution, pattern and count anomalies would have been spotted the moment hackers performed the password spray attack. Consequently, the risk score of the targeted entities would have gone up, notifying the IT administrators of a potential threat.
The data thief
Jeff Carter is a newly hired sales trainee at Quikseal. Quikseal is an adhesive manufacturing company that recently made waves by creating an biodegradable duct tape. Unknown to the recruiters, Carter's true intention to join the organization was to steal information about the company's manufacturing technique. He wins the trust of George Simon, a quality engineer, who has access to the production files. Carter keeps a close eye on Simon and discovers his account password.
One day Carter stays back after office hours and uses his PC to sign in to Simon's account. He accesses several files to locate the documents that contain information about the duct tape. As he spots the folder containing the information he wants and is about to copy it to his USB stick, the organization's information security officer pays him a visit. Carter was unaware that Quikseal employed UEBA to monitor its network. The UEBA solution efficiently identified time and pattern anomalies, as it was unusual for Simon's account to be accessed after working hours and from a workstation other than his own. The risk scores of Simon's account and Carter's PC increased substantially, warning the IT administrators of a potential mishap.
 Carter is being arrested for attempting to steal Quikseal's trade secrets
Carter is being arrested for attempting to steal Quikseal's trade secrets
While Carter was sentenced to prison for attempting to steal intellectual property, Simon was warned and received customized cybersecurity training on cyber hygiene and best practices to protect account misuse.
Organizations in the manufacturing sector are no longer targeted by only individuals or groups of hackers for monetary or personal gains. With nations competing against one another, extremely sophisticated, state-sponsored attacks have become all too real. The antagonists in scenarios like these may be far more dangerous than Red Panda or Jeff Carter, and the repercussions could be even more devastating as the state of a country's economy is significantly dependent on the state of its manufacturing sector.
Proactive cybersecurity measures like implementing a UEBA solution are a vital part of safeguarding the critical infrastructure of manufacturing units.