What is data exfiltration?
Data exfiltration is the unauthorized transfer of data from within an organization to outside of it by an individual who may or may not be a part of the organization. This unauthorized transfer of data can originate from workstations, servers, databases, or network devices.
Data exfiltration can be carried out manually or automatically. It can occur manually when someone with physical access to an important server or database copies the data on to an external storage device or uploads it to the cloud. It can occur automatically over the network as the result of a successful malware script that leaks the data out.
For many organizations in today's digital transformation era, thousands of data transfers happen every single day. This, of course, makes detecting the unauthorized data transfers among the authorized ones a very challenging task.
How to prevent data exfiltration
The best way to prevent data exfiltration is to:
- Perform a comprehensive risk assessment and identify all the valuable data assets.
- Get an inventory of all the endpoints where this data resides.
- Estimate the business impact of an exfiltration of each of these data assets.
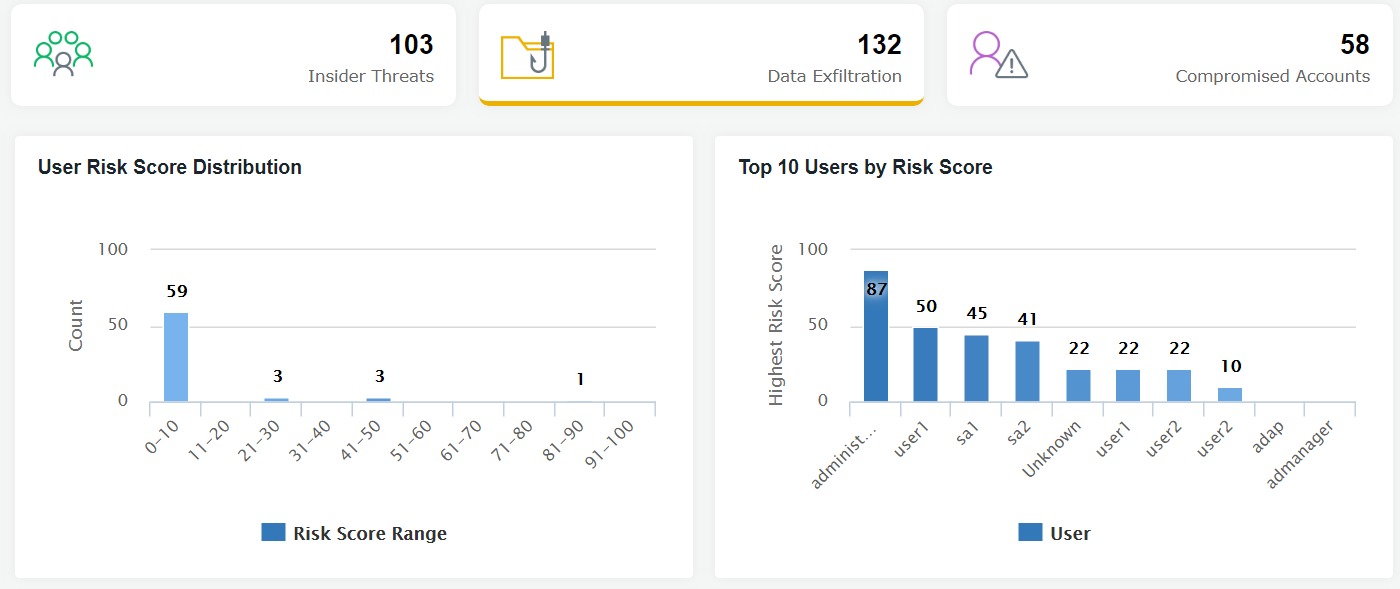
- Monitor important endpoints for indicators that an attack is progressing towards data exfiltration using a user and entity behavior analytics (UEBA) solution.
- Look for anomalies in time, count, and patterns in user and entity behavior.