ManageEngine named a Challenger in the 2024 Gartner ® Magic Quadrant ™ for Privileged Access Management
What is centralized management?
Centralization or centralized management in IT terms is when critical decisions and policies are enforced by a few top leaders within the organization from a single point of control.
The need for centralized, secure remote access
Today’s complex and heterogeneous corporate environments require security heads to manage and govern access to a growing inventory of remote servers, computers, and other IT assets. However, relying on multiple legacy remote access tools is inefficient and presents huge security risks. This calls for a simple, secure remote access solution that streamlines privileged access to critical systems, irrespective of their disparate network topologies.
A single point of control
- Access Manager Plus facilitates centralized administration of distributed remote IT assets through a web-based solution.
- Privileged users can update, troubleshoot, and manage remote servers centrally. These activities are recorded and stored as video files and audit logs within the application.
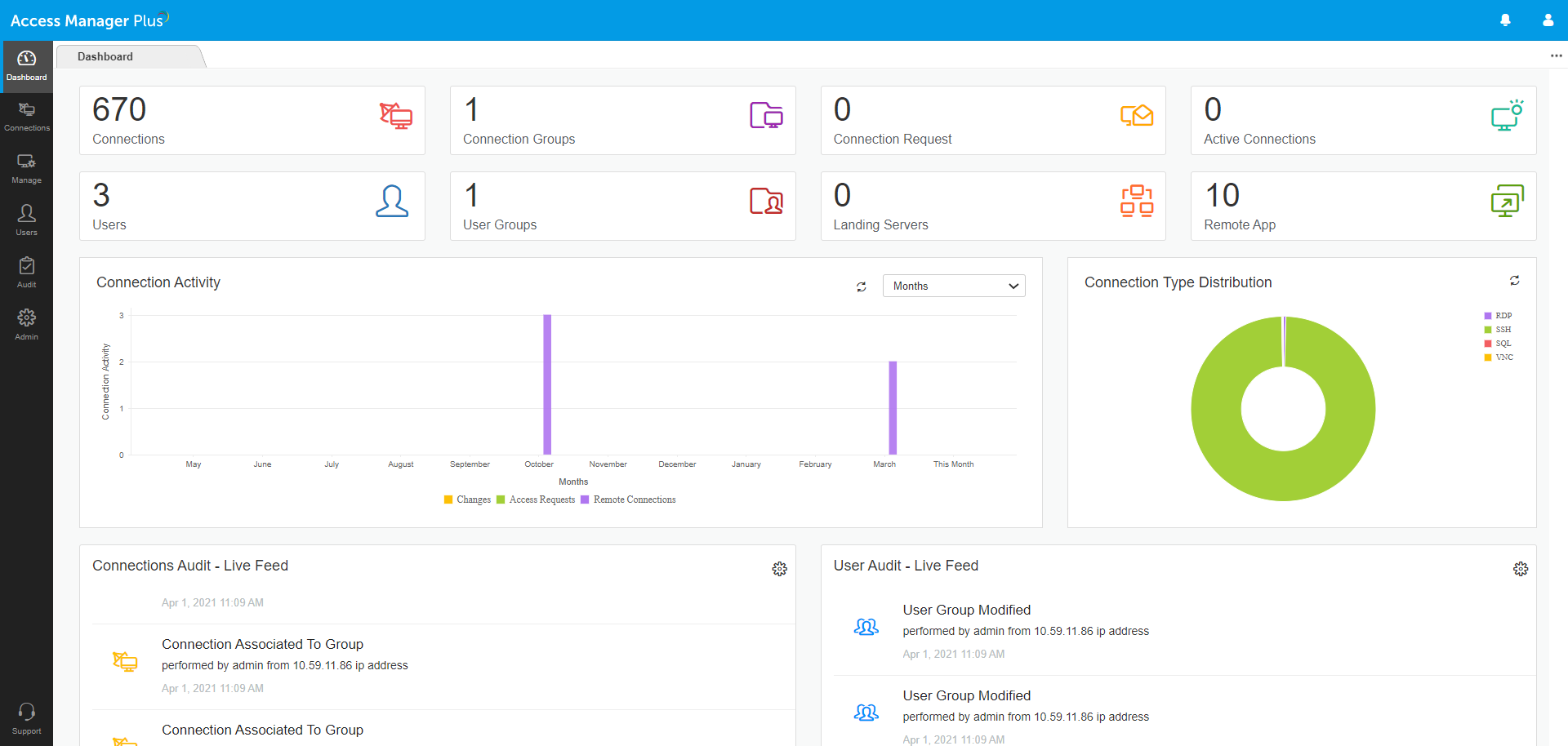
- The dashboard displays at-a-glance information on privileged access activities, which helps with quick, efficient administration.
- Administrators can view live updates on privileged remote access and the number of connections, landing servers, access requests, etc. right from the dashboard.
- Ensure improved quality of work and better accountability through standardized policies and efficient supervision.
Discover, add, and organize remote connections
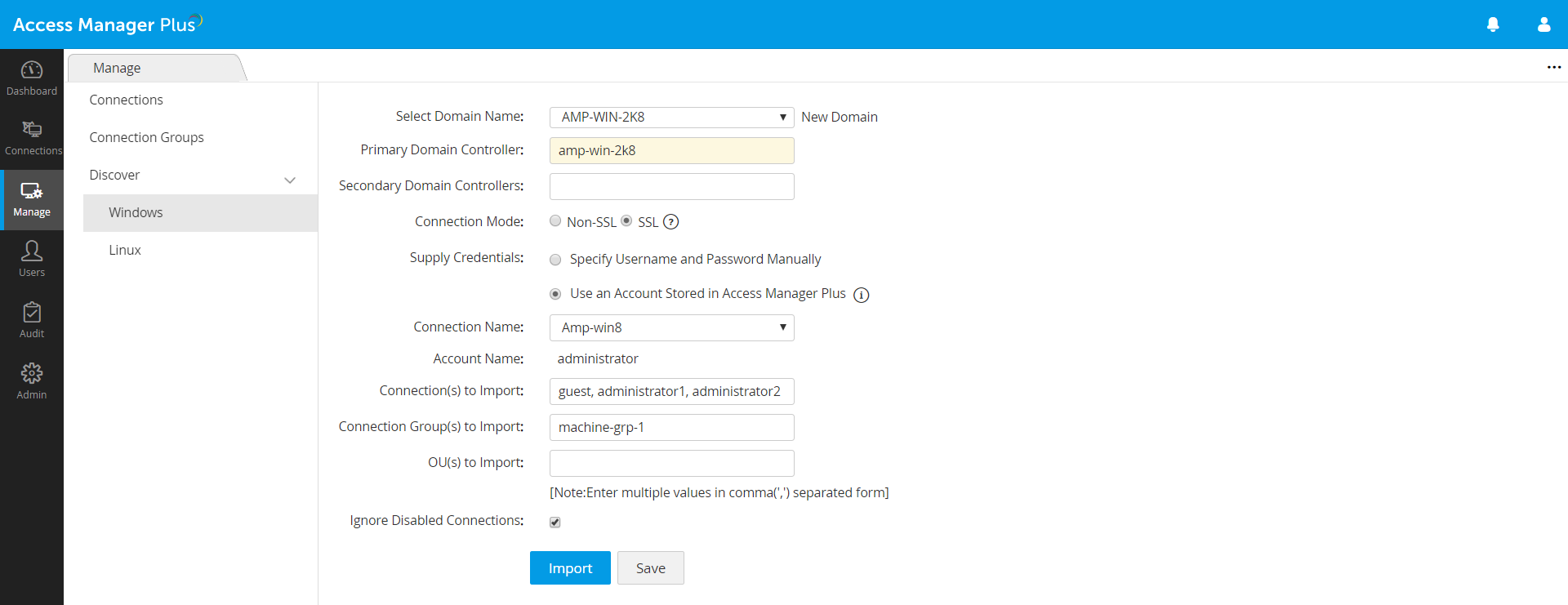
- Scan networks and automatically discover flavors of Windows and Linux systems, along with their associated privileged accounts, and add them as remote connections in Access Manager Plus.
- You can also manually add connections or import them from a CSV file.
- Declutter your database with Access Manager Plus’ grouping options. Organize your connections into groups, and configure the required settings for all the connections associated with a particular group at once.
Establish central control on access pathways
- Do away with multiple remote access tools, and enable VPN-less connections to remote servers and systems through secure RDP, SSH, SQL, and VNC pathways.
- Provide users with role-based access to critical systems based on preset user privileges and access controls.
- Allow or restrict specific client system access to Access Manager Plus by whitelisting or blacklisting IP addresses.