How to check password change history in Active Directory
Get it Done with ADAudit PlusNative auditing
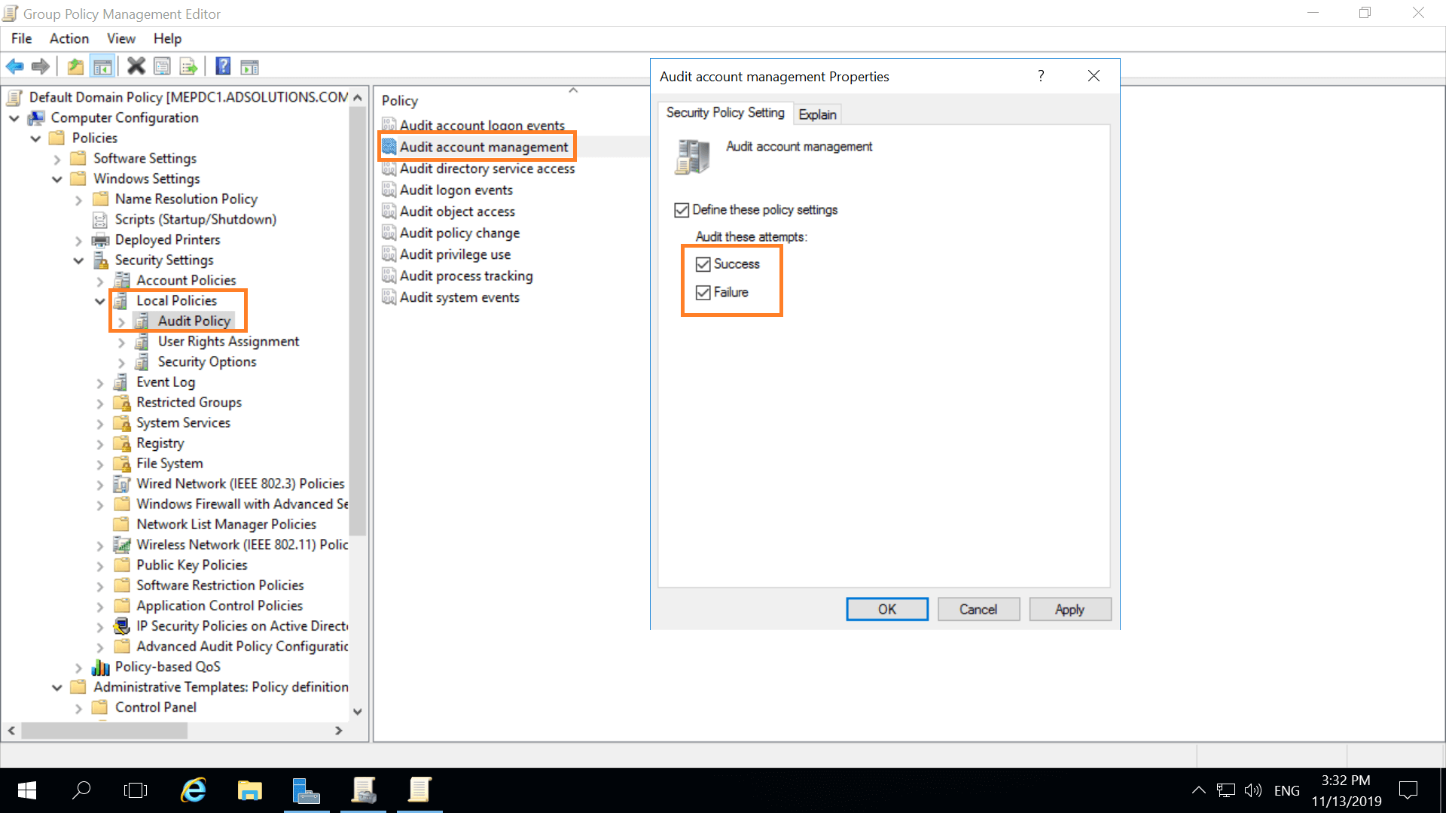
Step 1: Turn on auditing for password changes
Run GPMC.msc. Open Default Domain Policy → Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Audit Policy: Audit account management, and define Success and Failure.
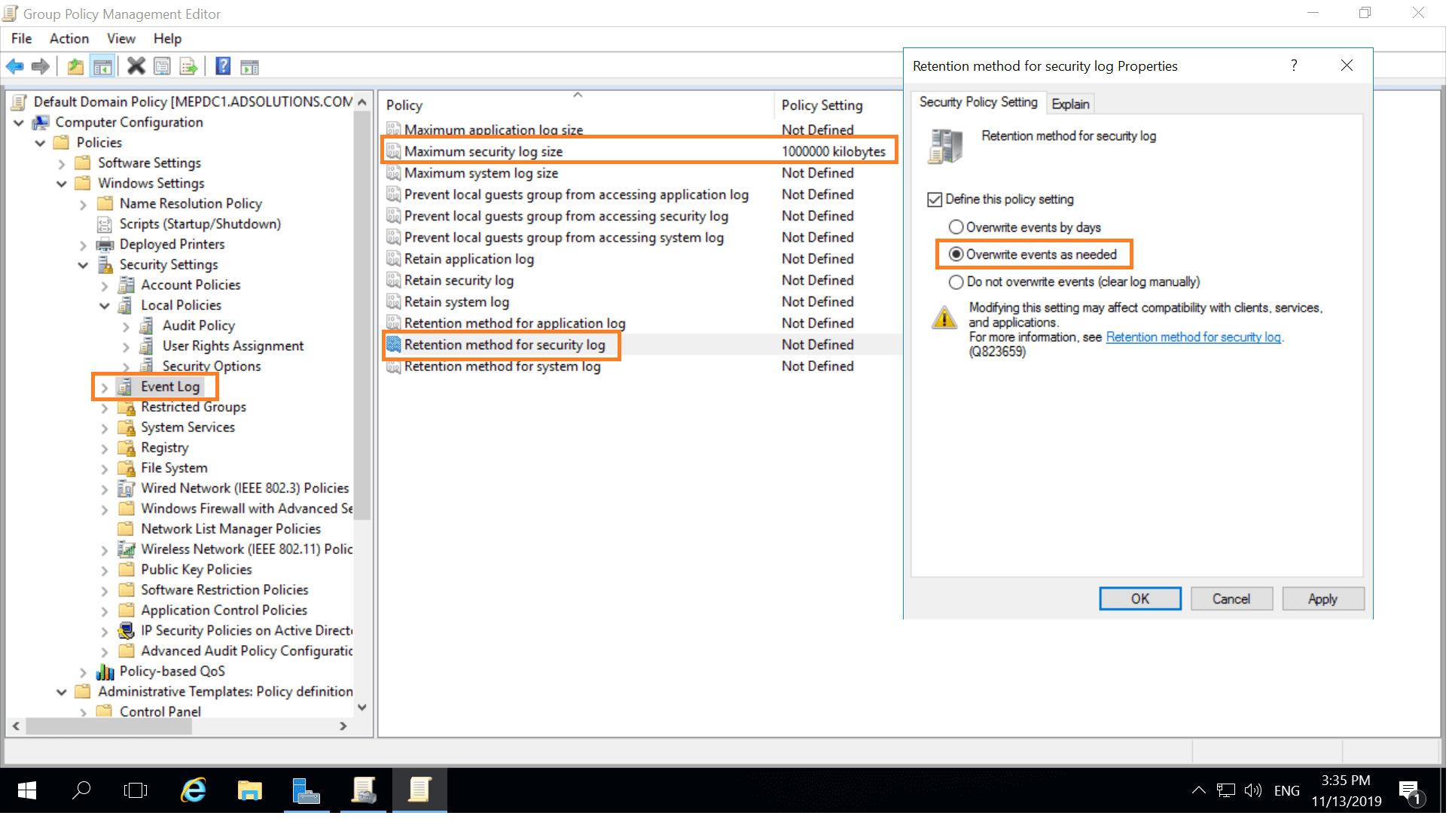
Step 2: Set up your Event Viewer to accommodate all the password changes.
Run GPMC.msc and open Default Domain Policy → Computer Configuration → Policies → Windows Settings → Security Settings → Event Log:
- Set Maximum security log size to 1GB.
- Set Retention method for security log to Overwrite events as needed.
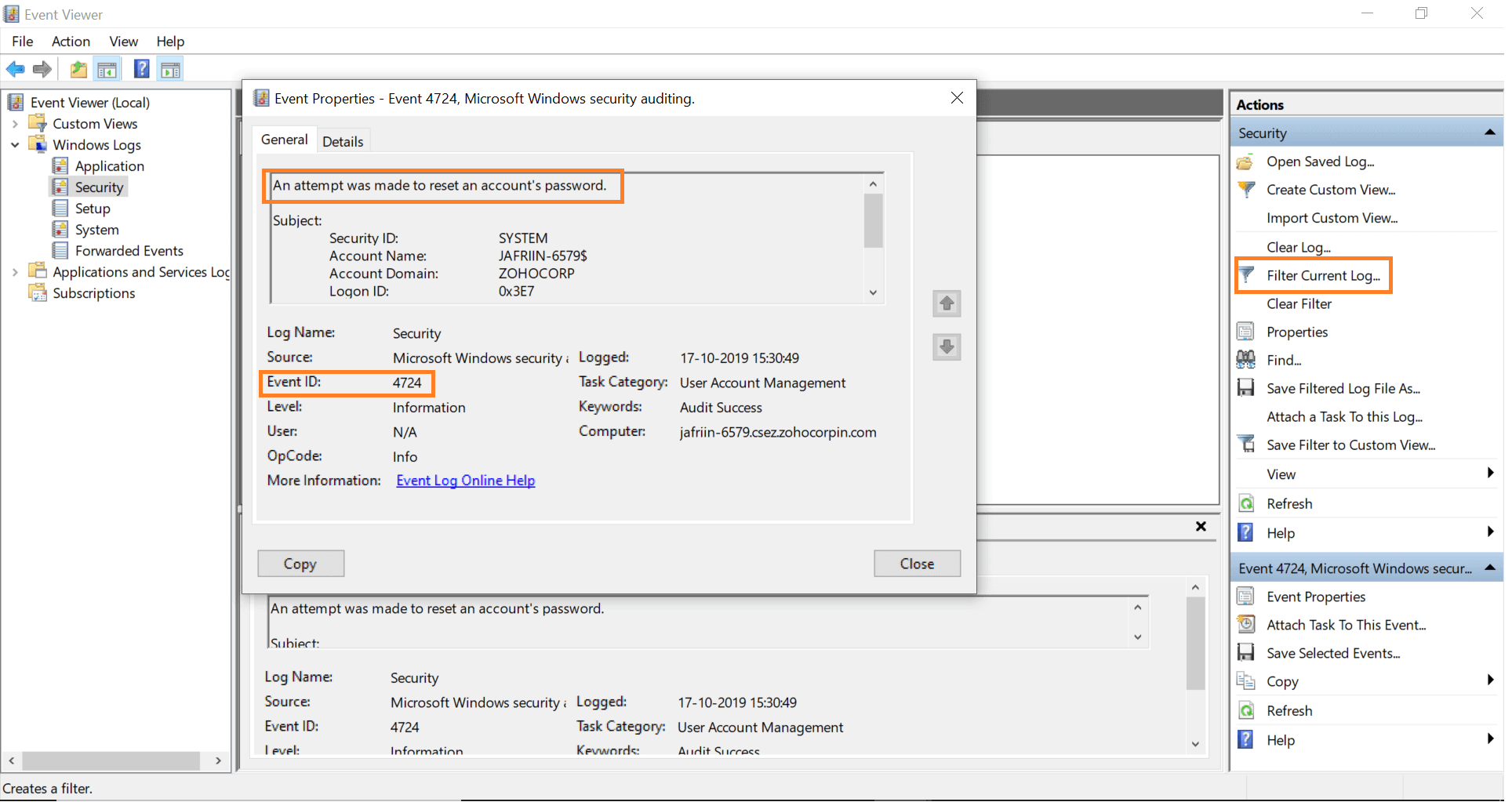
Step 3: Open Event Viewer, and search the security logs for event IDs:
- 4724 – password reset attempt by administrator
- 4723 – password change attempt by user
Simplified password change monitoring with ADAudit Plus
With ADAudit Plus' simple, easy-to-read reports, a single click is all it takes to pull up the complete details of who changed/set passwords, when, and from which machine. These reports can be exported and scheduled to be automatically generated at specified times and delivered to your inbox.
You can also configure alerts to notify you when passwords of privileged users are changed. This way you can take action immediately.
- Log in to ADAudit Plus. Go to the Reports tab.
Under User Management Reports, navigate to the Recently Password Changed Users report.
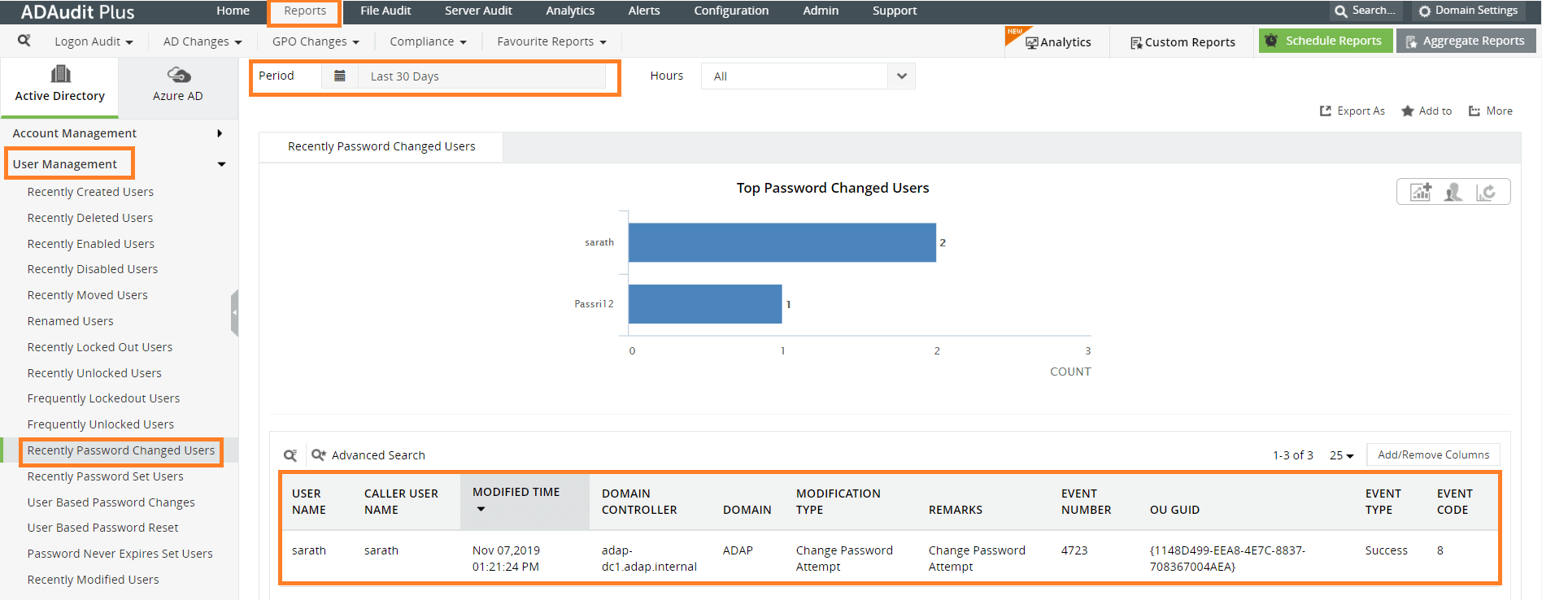
The details you can find in this report include:
- Name of the user whose password was changed
- Name of the user who modified the password
- Time at which the password was modified
- Domain controller at which the password change was made
To learn more about how ADAudit Plus simplifies Active Directory (AD) reporting and auditing, visit: https://www.manageengine.com/products/active-directory-audit/.
Native auditing becoming a little too much?
Simplify file server auditing and reporting with ADAudit Plus.
Download for Free