Track Explicit Credential Logons with Event ID 4648 –
Gain Insight into Hidden Access Attempts
Event ID 4648 reveals when a process attempts to use explicit credentials—offering critical visibility into script-based logons, service account misuse, and early signs of lateral movement or credential abuse.
*Fully functional 30 day free trial. No Credit Card Required
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
What is Event ID 4648?
Event ID 4648 is generated when a logon attempt is made using explicit credentials, such as through the RUNAS command or scheduled tasks. It logs the initiating user, the target account, the process used, and network context—making it crucial for detecting impersonation, privilege misuse, and lateral movement.
Why Monitoring Event Code 4648 Matters
This event is a leading indicator of credential misuse:
- Attackers use 4648 to execute lateral movement or impersonation via scheduled tasks or remote execution.
- Numerous 4648 events with differing usernames in a short period often signal password spraying from domain‑joined systems.
- Monitoring explicit credential use helps detect misuse of service accounts, automated scripts, and privilege escalation attempts.
According to Verizon DBIR 2024 "The use of stolen credentials was involved in 77% of breaches within basic web application attacks"
—making Event ID 4648 your key signal for detecting credential theft in action
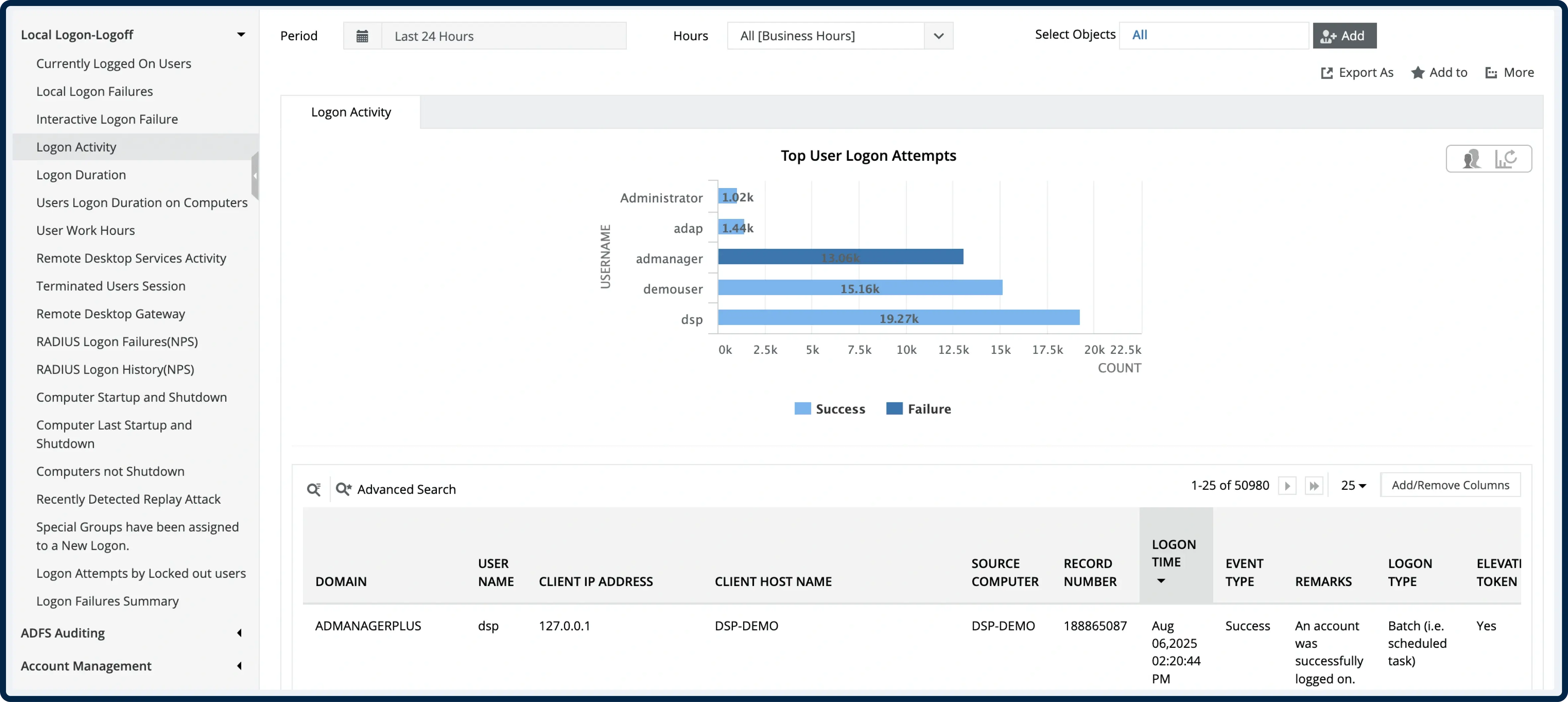
How ADAudit Plus Helps You Monitor Event ID 4648
Real-time alerts on explicit credential use
Alert on sudden spikes in Event ID 4648 actions—especially from service accounts or outside business hours.
Centralized 4648 dashboard
Fully searchable logs of explicit logon attempts, filterable by subject user, target account, process name, server, and IP.
Correlation with related security events
Connect 4648 events with 4624 (successful logon), 4625 (failed logon), 4672 (privileged access), and 4649 (replay attack) to trace escalation paths.
Behavior analytics and anomaly detection
Suppress routine explicit logons (e.g. scheduled tasks), highlight unusual patterns like lateral movement or service abuse.
Compliance-ready reporting & retention
Use prebuilt templates to report on explicit credential use by account, time, and system—ready for audits.
*Fully functional 30 day free trial. No Credit Card Required
Manual Logging vs ADAudit Plus
Trusted by IT Teams Globally
Trusted by over
18,000+ IT teams
worldwide
Gartner Peer Insights Customers' Choice
Compliance-ready platform with ISO 27001 standards
Over 280,000 organizations across 190 countries trust ManageEngine to manage their IT.




Gain Full Visibility on Explicit Credential Use –
Start Monitoring Event ID 4648 Today
- 30-day fully functional free trial.
- No user limits.
- Free 24*5 tech support.
*Fully functional 30 day free trial. No Credit Card Required