Monitor Directory Object Access with Event ID 4662 –
Detect AD Permission Abuse Early
Track Event ID 4662 to monitor access to Active Directory objects, detect unauthorized changes, and identify early signs of privilege misuse or DCSync attempts—helping you stay ahead of potential breaches and misconfigurations before they escalate into serious security incidents.
*Fully functional 30 day free trial. No Credit Card Required
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
What is Event ID 4662?
Event ID 4662 is logged whenever a user accesses an Active Directory object—such as reading or modifying properties—if the appropriate System Access Control List (SACL) is configured. It includes information like subject user, object type and name, operation type, access mask, and accessed properties.
Why Monitoring Event Code 4662 Matters
While frequent, this event contains critical signals when filtered correctly:
- Excessive 4662 events often stem from normal AD activity or tools like admin consoles—yet writes involving permissions can indicate abuse.
- Monitoring write-access events on Group Policy, delegate permissions, or DCSync privileges can help detect advanced attacks.
- According to trustedsec’s research, correlating 4662 with high-privilege DACL changes helps detect DCSync and credential compromise attempts.
Tracking Event ID 4662 enables you to:
- Detect unauthorized modifications to critical AD objects (e.g. GPOs, DCSync-enabled accounts)
- Identify suspicious property or ACL changes
- Support compliance with NIST, CIS, PCI DSS, ISO and internal audit policies
According to Verizon DBIR 2024, "Credentials are a core component of compromising organizations"
- making Event ID 4662 (detailed object‑access events) your essential alert for anomalous access to sensitive resources.
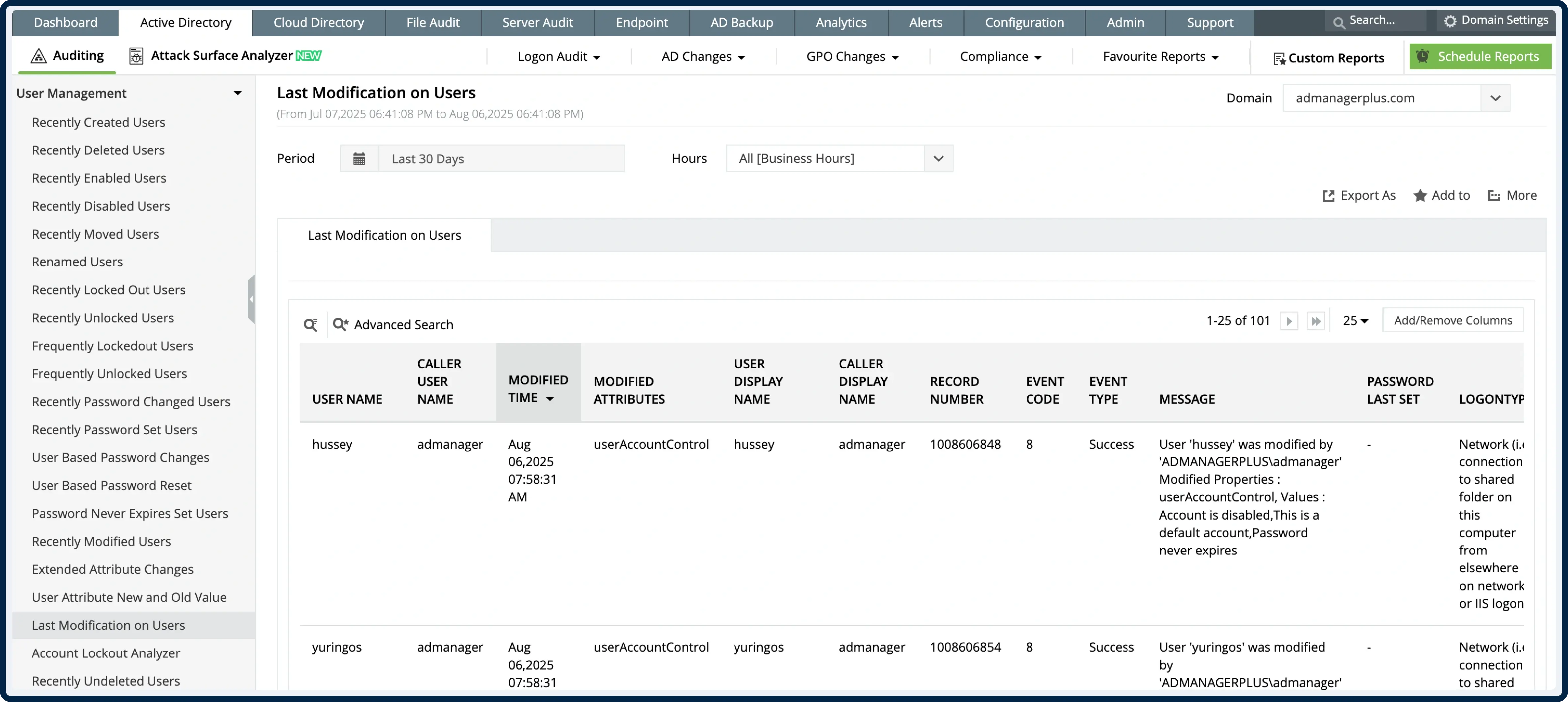
How ADAudit Plus Strengthens 4662 Monitoring
Real‑time alerts on permission changes
Get notified when write-access occurs on critical OUs or policy objects—especially outside maintenance windows
Centralized 4662 dashboard
View all directory object access events across domain controllers—filtered by user, object name/type, operation, and access mask
Event correlation for context
Link Event 4662 with logon events (4624), handle requests (4661), or other security events like 5136 (object changes) to trace misuse. ([turn0search14][turn0search6])
Noise reduction with smart filtering
Suppress routine read events or benign accesses—highlight only high-risk accesses like DACL modification or AD schema editing
Compliance-ready reporting & retention
Leverage built-in templates to generate audit reports by object type, user, operation, or time-frame, meeting regulatory requirements
*Fully functional 30 day free trial. No Credit Card Required
Manual Logging vs ADAudit Plus
Trusted by IT Teams Globally
Trusted by over
18,000+ IT teams
worldwide
Gartner Peer Insights Customers' Choice
Compliance-ready platform with ISO 27001 standards
Over 280,000 organizations across 190 countries trust ManageEngine to manage their IT.




Monitor Directory Service Access with Precision –
Start Tracking Event ID 4662 Today
- 30-day fully functional free trial.
- No user limits.
- Free 24*5 tech support.
*Fully functional 30 day free trial. No Credit Card Required