Track Sensitive Privilege Use with Event ID 4673 –
Detect Elevated Access Abuse in Real Time
Monitor Event ID 4673, which is triggered when a process or user invokes a sensitive privilege, such as SeDebugPrivilege or SeTcbPrivilege. Tracking this event helps you detect misuse of elevated rights by administrators, automated scripts, or threat actors—before it leads to privilege escalation or system compromise.
*Fully functional 30 day free trial. No Credit Card Required
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
What is Event ID 4673?
Event ID 4673 is logged when a user or process calls a sensitive privilege—such as SeTcbPrivilege or SeDebugPrivilege—to perform high-impact actions. It includes details like account identity, process name, privilege list, and context of the call.
Why Monitoring Event Code 4673 Matters
Even legitimate services may invoke these privileges, but abnormal usage can reveal stealthy attacks:
- Privilege abuse is often leveraged for token manipulation, credential access, or lateral movement, especially via PowerShell. One case involved a user invoking SeDebugPrivilege via PowerShell—indicating possible code injection or credential attack.
- According to Graylog best practices, Event ID 4673 is among the essential Windows events to monitor for security posture tracking.
Tracking Event ID 4673 enables you to:
- Detect elevated privilege usage beyond usual operations
- Spot scripts or tools abusing rights like token creation or debugging
- Identify anomalous privilege activity outside normal patterns
- Support compliance with NIST, CIS, GDPR, PCI DSS, and ISO frameworks
According to Verizon DBIR 2024, "Stolen credentials remain a favorite tool for privilege escalation and lateral movement"
- making Event ID 4673 (privileged service calls) a vital indicator of potential abuse of high-level privileges.
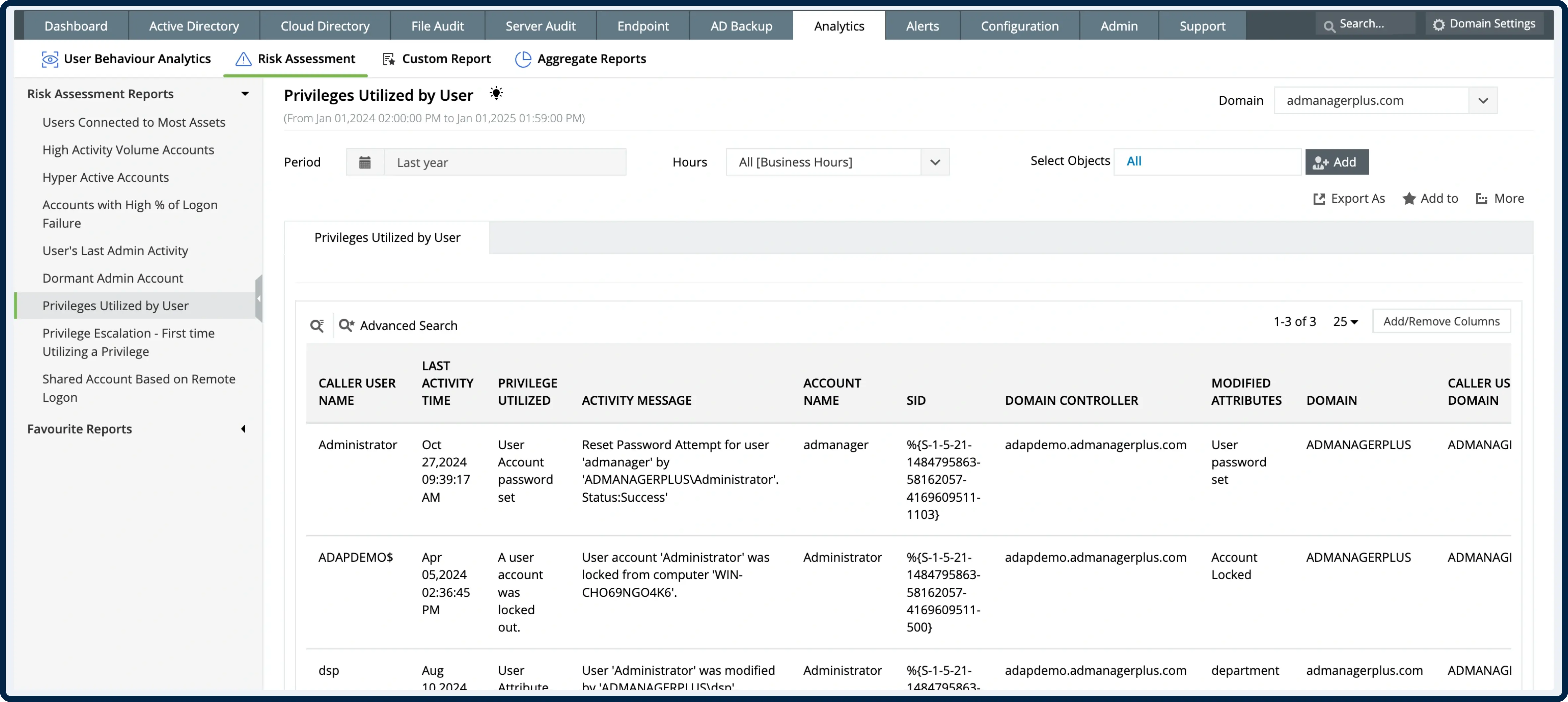
How ADAudit Plus Enhances 4673 Visibility
Real-time alerts on sensitive privilege use
Receive immediate notifications when high-risk privileges like SeTcbPrivilege or SeBackupPrivilege are exercised—especially from unexpected processes or outside working hours
Centralized 4673 dashboard
Review privileged service calls across servers, filterable by subject account, service/process name, privilege used, and timestamp
Correlation with related log events
Link Event ID 4673 with 4624 (logon), 4688 (new processes), 4672 (privileges assigned) and 4663/4664 (object access) to build a full attack chain view
Noise reduction via smart filtering
Suppress repetitive benign privileges while flagging unexpected privilege use, reducing alert fatigue and focusing on actionable anomalies
Compliance-ready reporting & archival
Export reports on sensitive privilege usage by account, privilege type, process, and time—aligned with audit conventions
*Fully functional 30 day free trial. No Credit Card Required
Manual Logging vs ADAudit Plus
Trusted by IT Teams Globally
Trusted by over
18,000+ IT teams
worldwide
Gartner Peer Insights Customers' Choice
Compliance-ready platform with ISO 27001 standards
Over 280,000 organizations across 190 countries trust ManageEngine to manage their IT.




Monitor Privileged Service Calls with Confidence –
Start Tracking Event ID 4673 Today
- 30-day fully functional free trial.
- No user limits.
- Free 24*5 tech support.
*Fully functional 30 day free trial. No Credit Card Required