Track Kerberos TGT Requests with Event ID 4768 –
Decode Authentication Activity Proactively
Monitor Event ID 4768 to uncover Kerberos Ticket Granting Ticket (TGT) requests—spot user enumeration, brute-force attempts, misconfigured services, or lateral movement early.
*Fully functional 30 day free trial. No Credit Card Required
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
What is Event ID 4768?
Event ID 4768 is recorded on a domain controller whenever a Kerberos authentication ticket (TGT) is requested or issued.
If the request succeeds, the Result Code equals 0x0; if it fails, a non-zero Result Code indicates failure.
This event captures key details—TargetUserName, ClientAddress, TicketOptions, Result Code, and encryption types—essential for Kerberos visibility.
Why Monitoring Event Code 4768 Matters
Event 4768 reflects both valid and anomalous TGT requests—making it central to Kerberos attack detection:
- TGT requests with result code 0x6 (unknown user) may indicate user-account enumeration or password spraying.
- Splunk threat research flagged unusual 4768 volumes as signs of reconnaissance or lateral movement.
- Misconfigured certificates or legacy protocols can trigger floods of 4768 events—hiding real attacks.
Tracking Kerberos authentication event ID 4768 helps you:
- Detect suspicious or repeated TGT requests
- Identify potential Kerberos enumeration or brute‑force activity
- Pinpoint anomalous TGT requests tied to legacy systems or smart‑card issues
- Produce audit trails aligned with NIST, CIS, PCI DSS, and ISO standards
According to Verizon DBIR 2024 "Use of stolen credentials is still the top action in data breaches"
—making Event ID 4768 (Kerberos TGT requests) your earliest warning sign of credential misuse.
How ADAudit Plus Enhances 4768 Monitoring
Default Windows logs don’t deliver the correlation and context needed. ADAudit Plus gives you:
Real-time alerts on Kerberos ticket anomalies
Trigger alerts when a single source generates numerous invalid TGT requests (e.g. 0x6), or requests originate off‑hours or outside defined IP ranges.
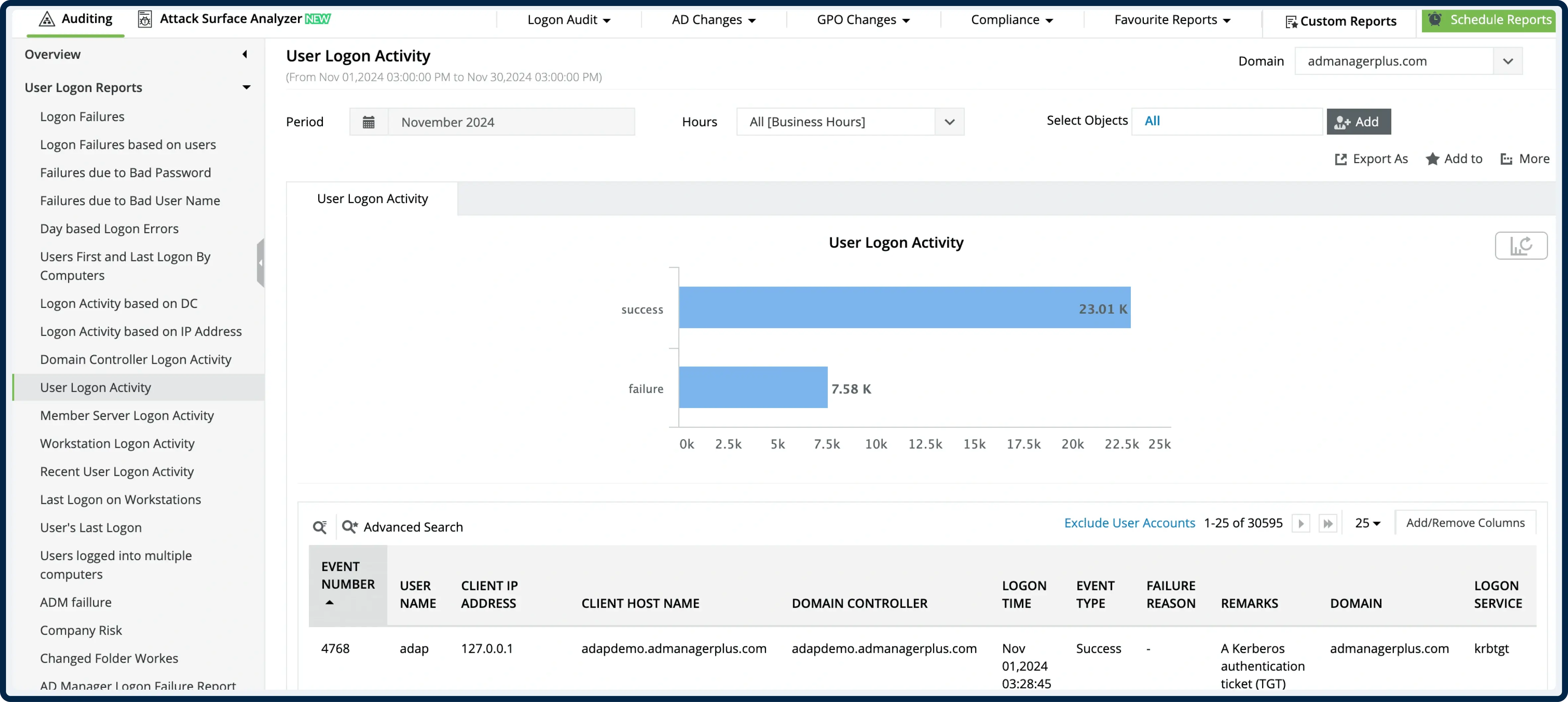
Unified Event ID 4768 dashboard
View all TGT request events—success and failure—with filters for Result Code, account name, encryption type, client IP, and timestamp.
Cross-event correlation
Link Event 4768 with related events—such as event 4771 (pre-auth failures), 4625 (failed logon), and 4672 (privilege use)—to reconstruct attacker patterns.
Behavior analytics
Suppress legitimate high-volume TGT traffic (e.g. smart‑card renewals) while flagging unusual bursts tied to enumeration or lateral movement.
Compliance-ready reporting
Leverage built-in templates to archive and export Kerberos TGT requests by account, type, and time-period—ready for auditor review.
*Fully functional 30 day free trial. No Credit Card Required
Manual Logging vs ADAudit Plus
Trusted by IT Teams Globally
Trusted by over
18,000+ IT teams
worldwide
Gartner Peer Insights Customers' Choice
Compliance-ready platform with ISO 27001 standards
Over 280,000 organizations across 190 countries trust ManageEngine to manage their IT.




See What Kerberos TGT Requests Can Reveal –
Start Monitoring Event ID 4768 Today
- 30-day fully functional free trial.
- No user limits.
- Free 24*5 tech support.
*Fully functional 30 day free trial. No Credit Card Required