Detect, investigate, and mitigate threats like malicious logins, lateral movement,
privilege abuse, data breaches, and malware.
-
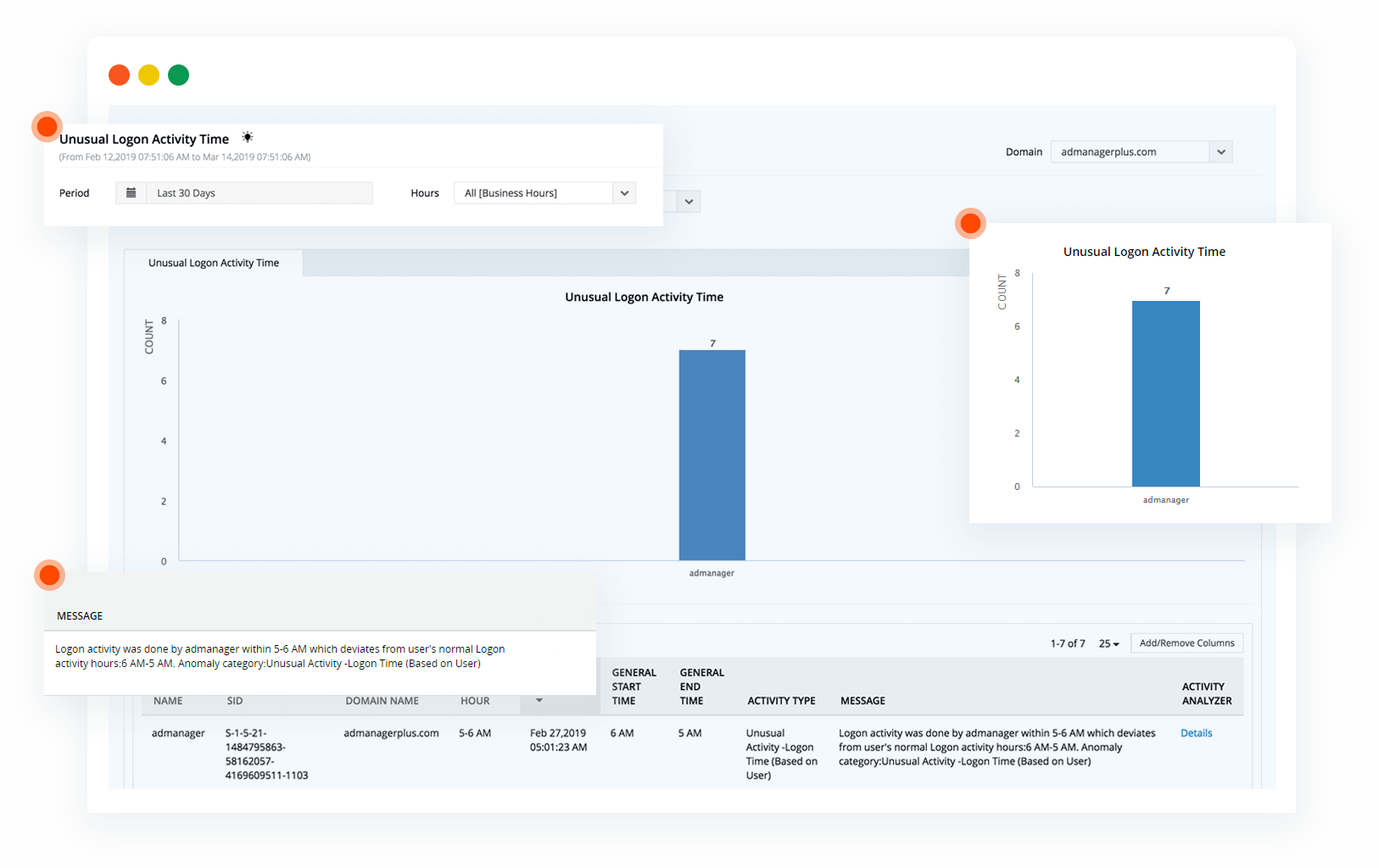
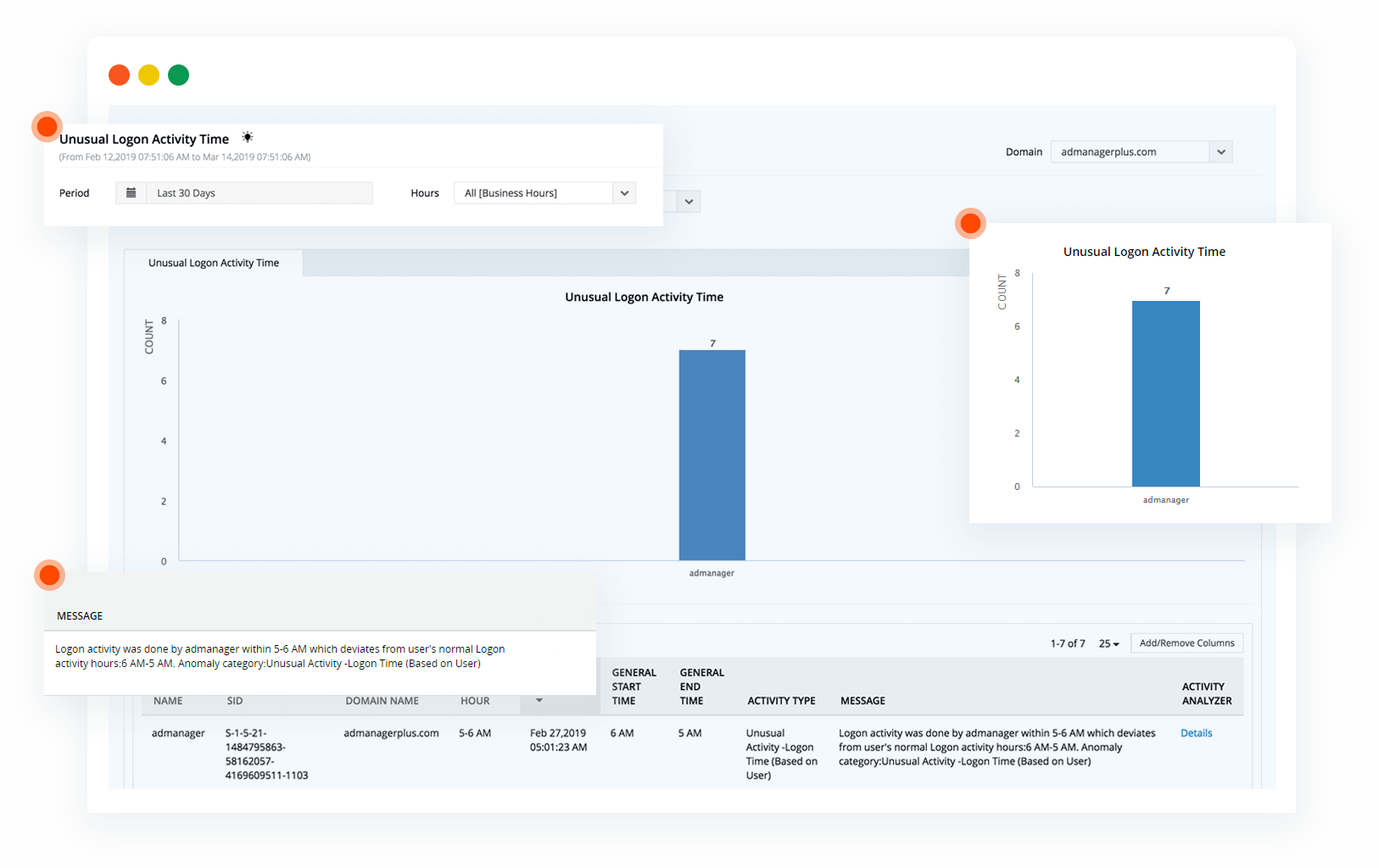
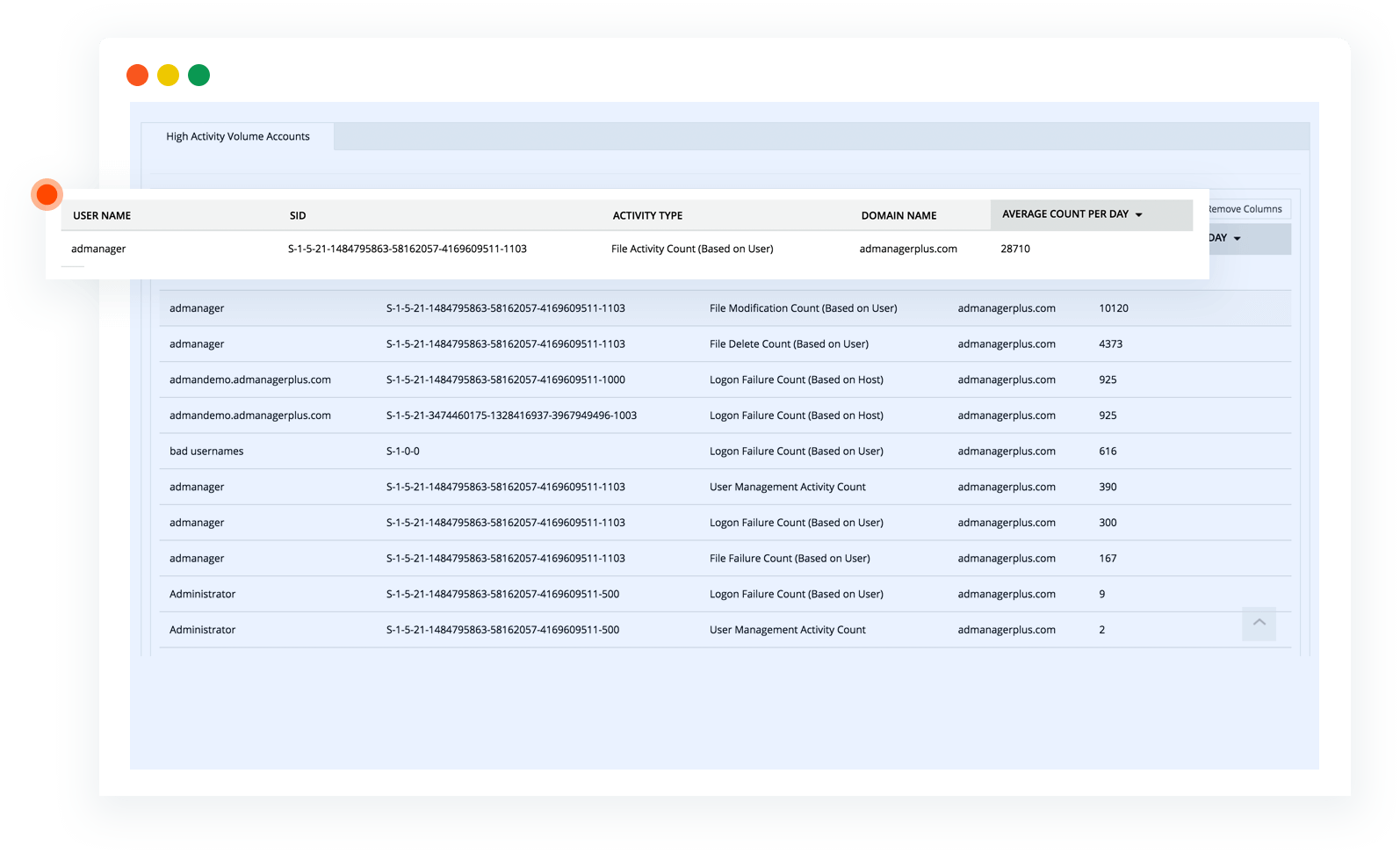
Malicious logins
Receive notification if a critical server is accessed during unusual hours, or when there's been an unusual number of login failures.
-
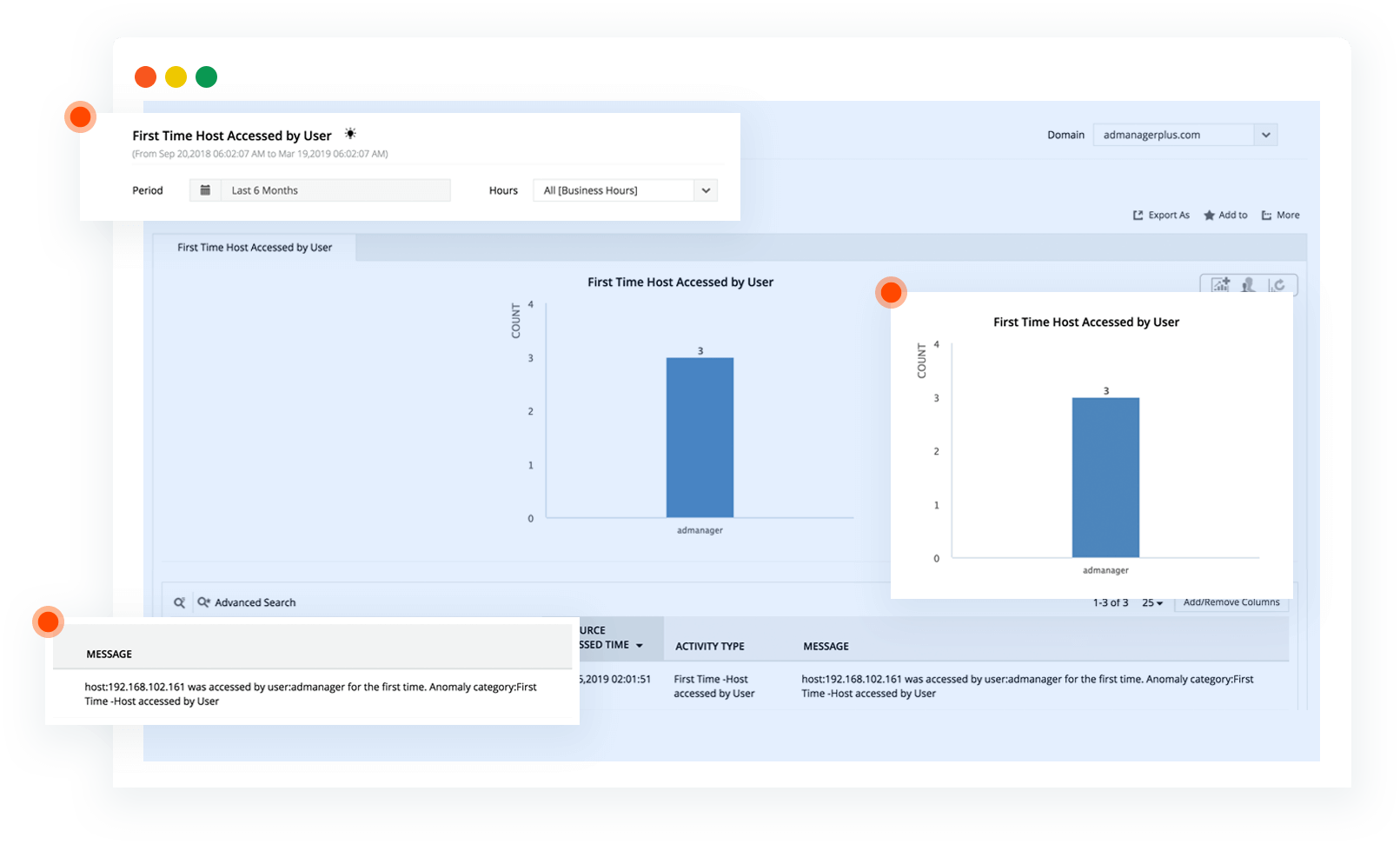
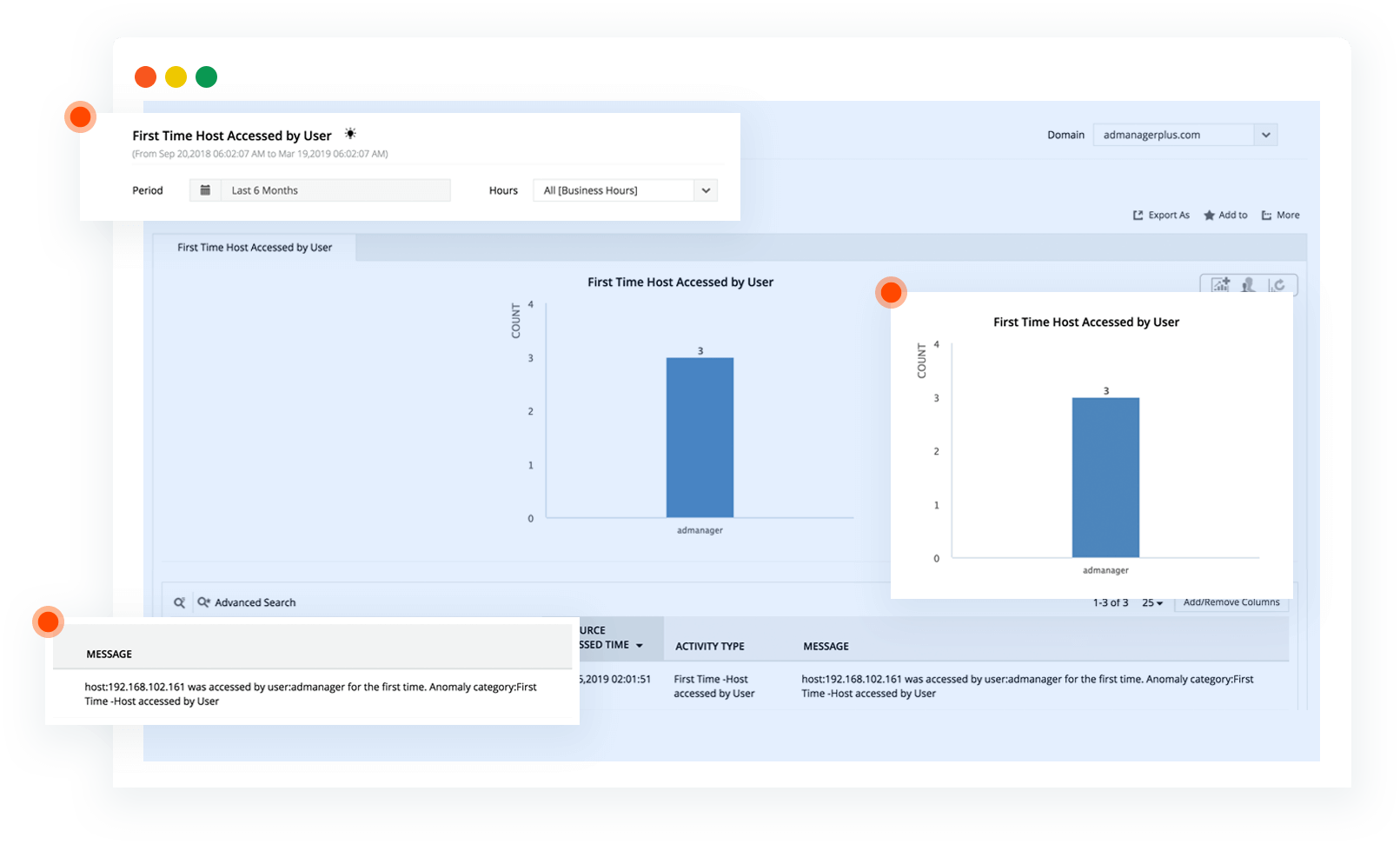
Lateral movement
Receive notification when a machine is accessed for the first time, or a dormant user account becomes active.
-
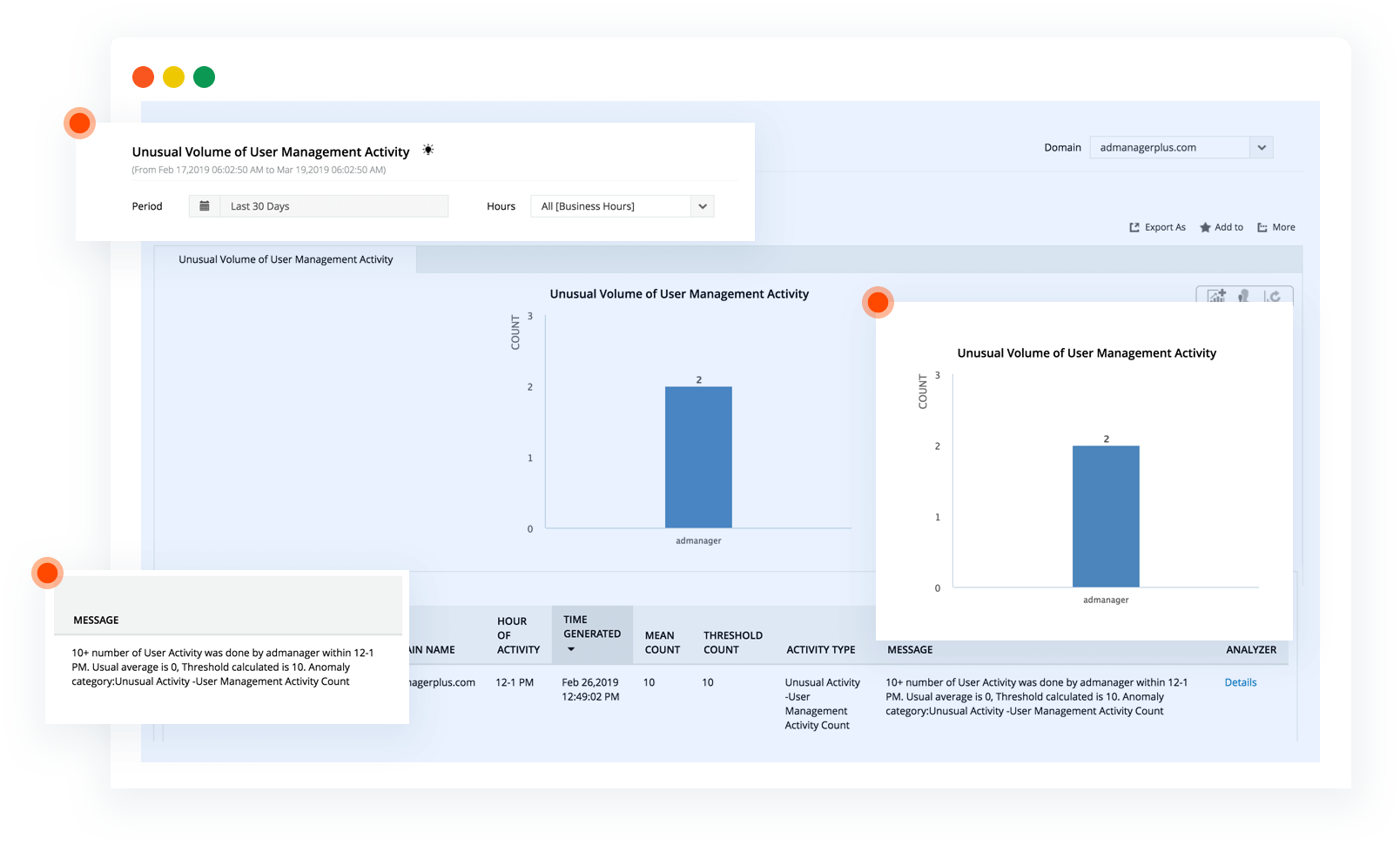
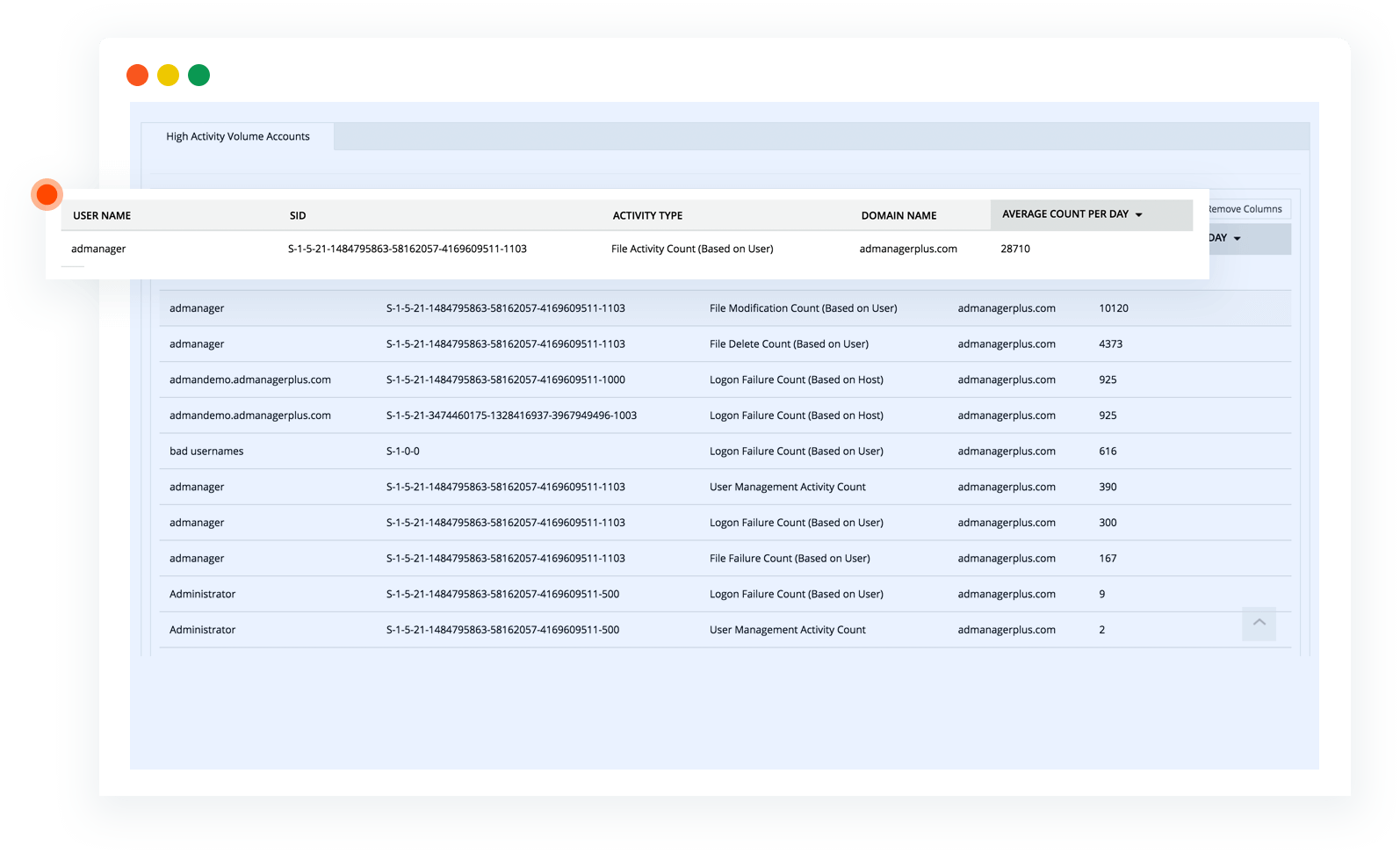
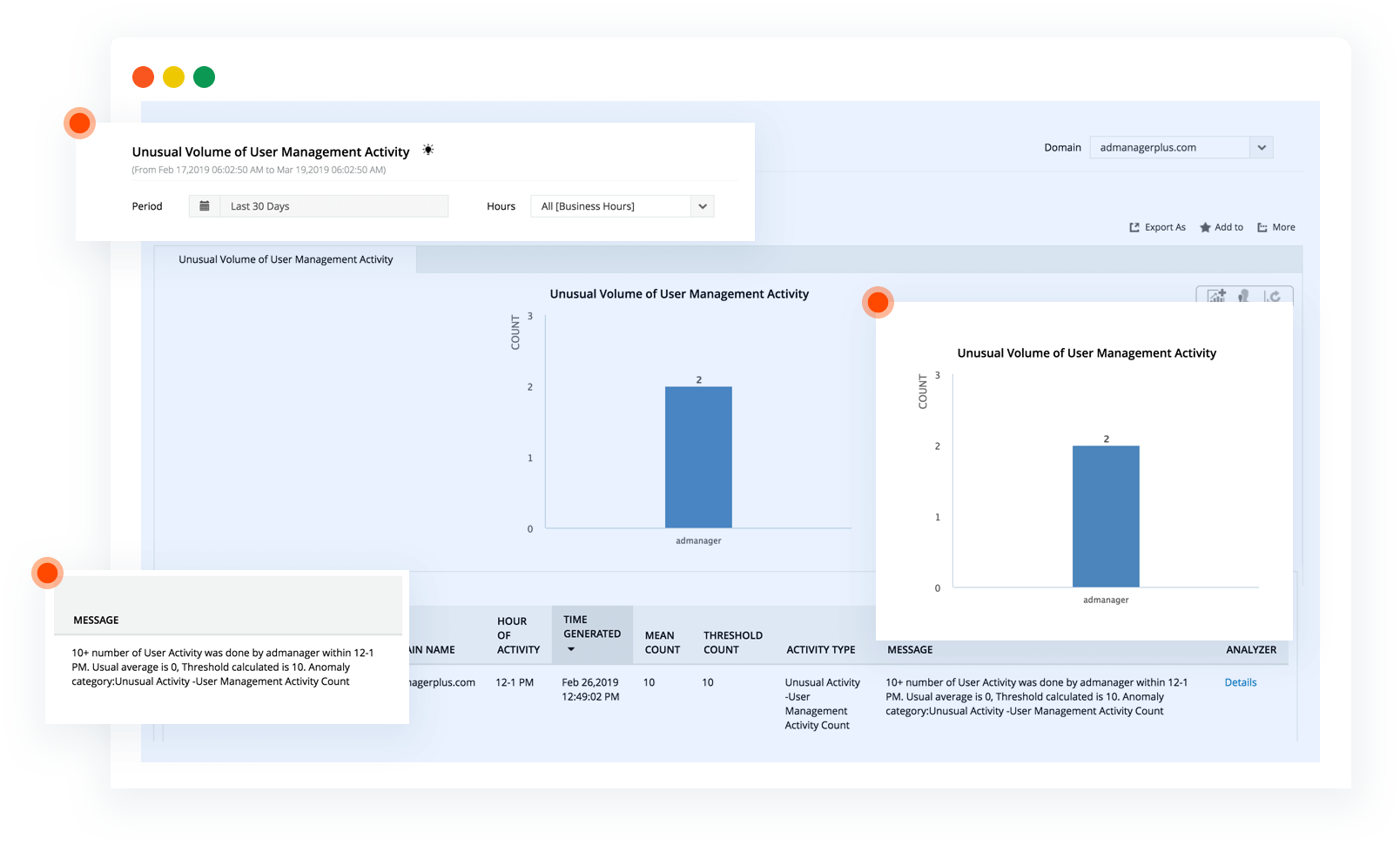
Privilege abuse
Receive notification when there is an unusual (and possibly unauthorized) volume of user management activity.
-
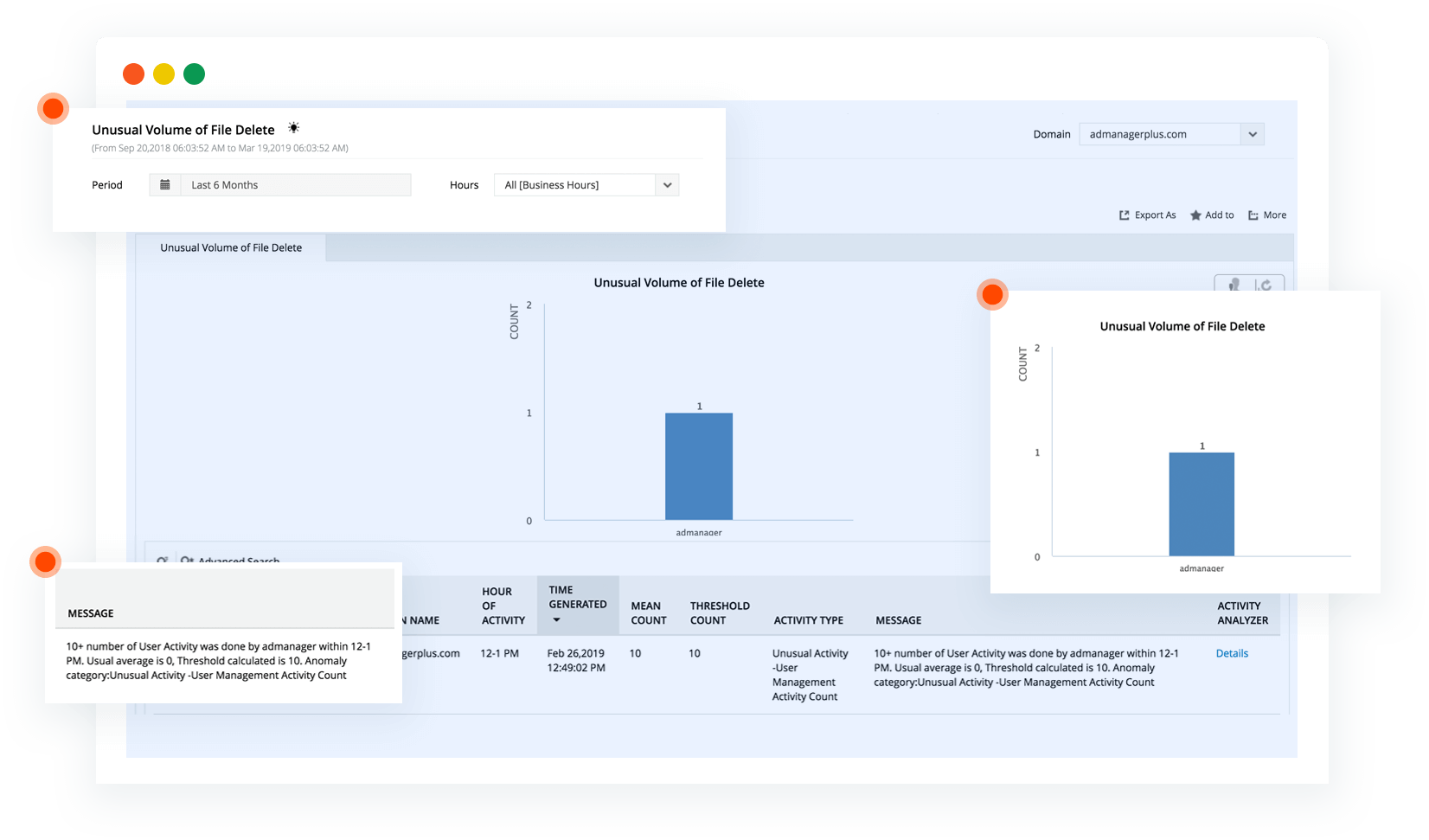
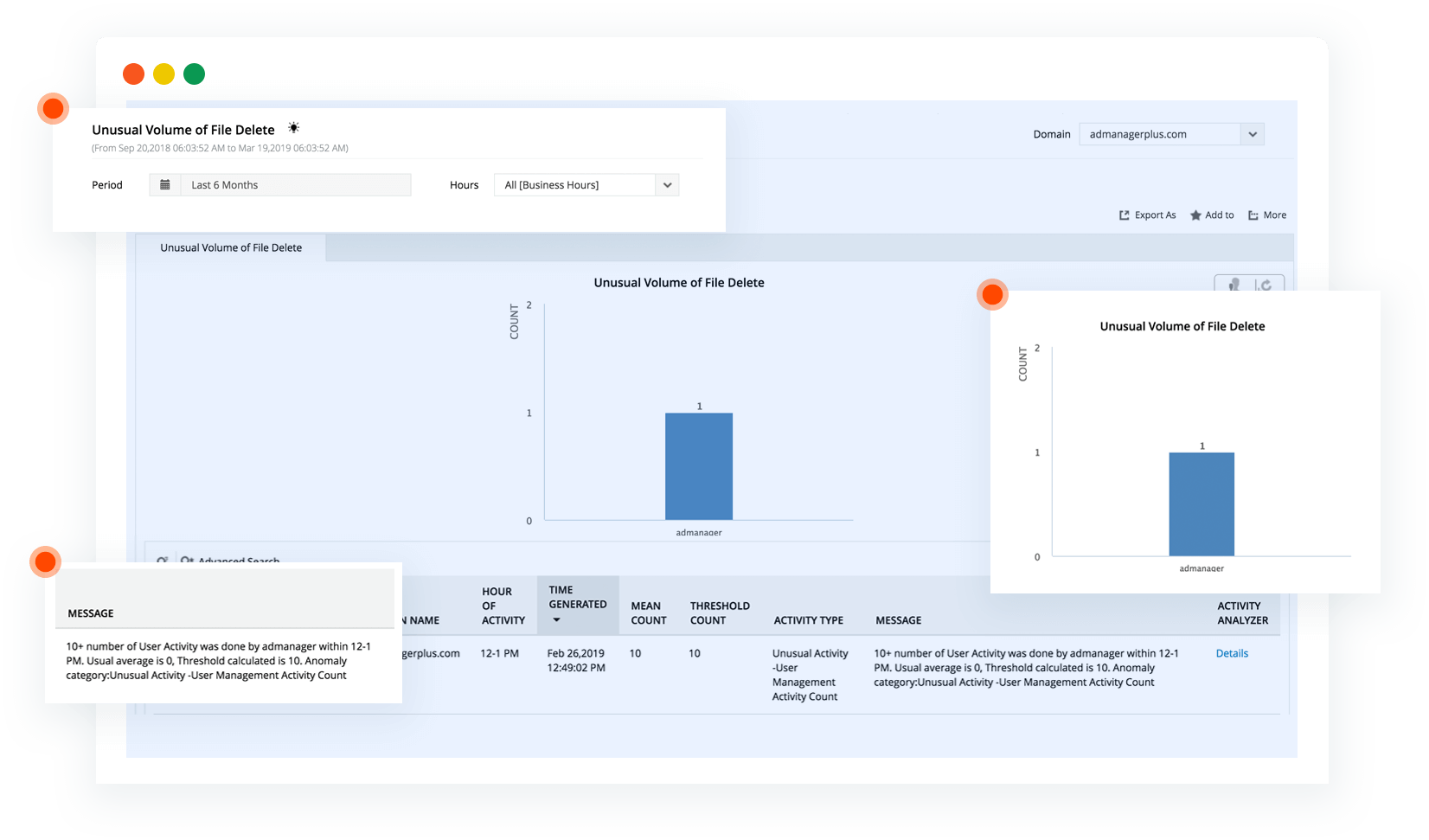
Data breaches
Receive notification if there's been an attempt to exfiltrate or delete data.
-
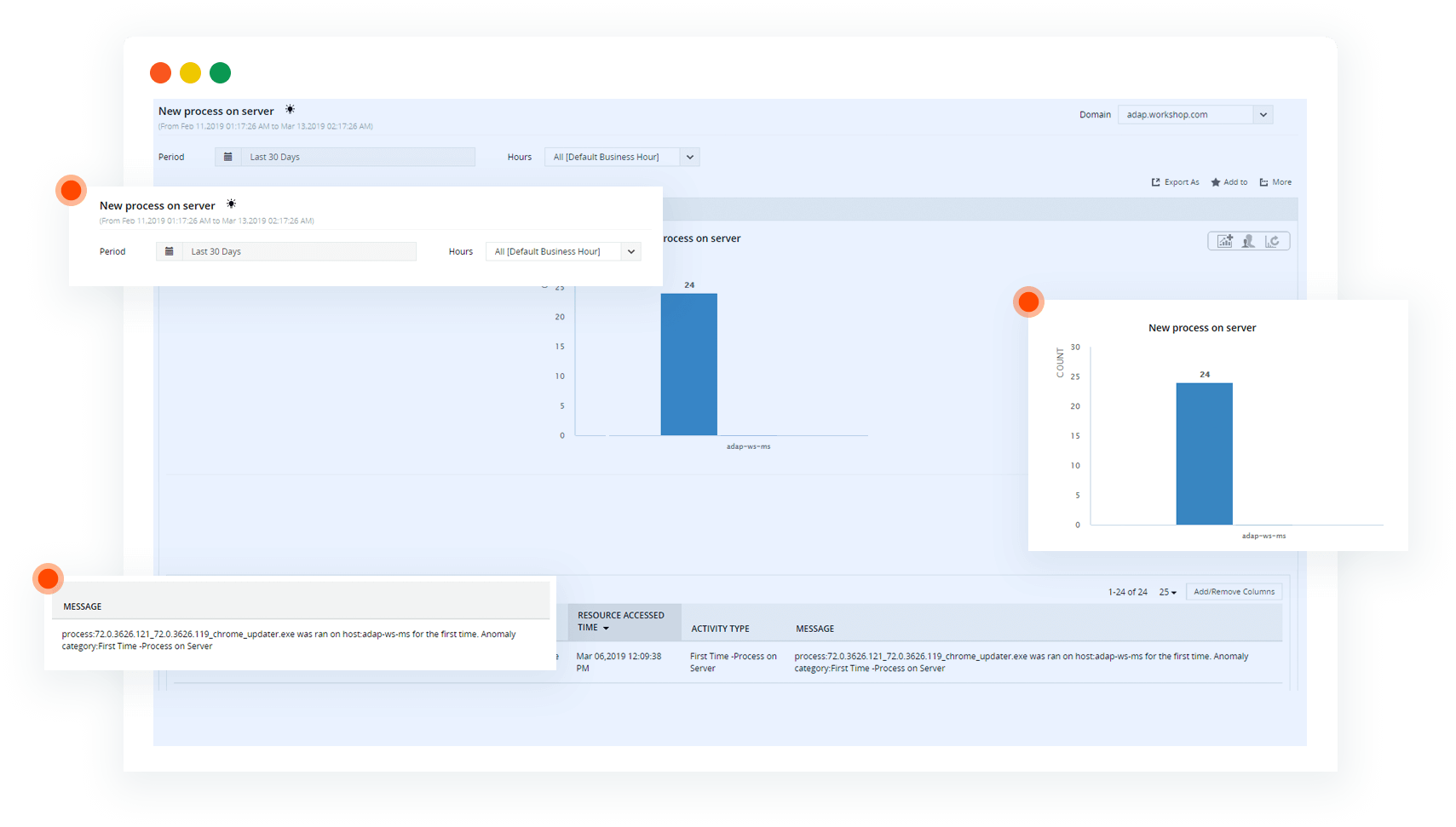
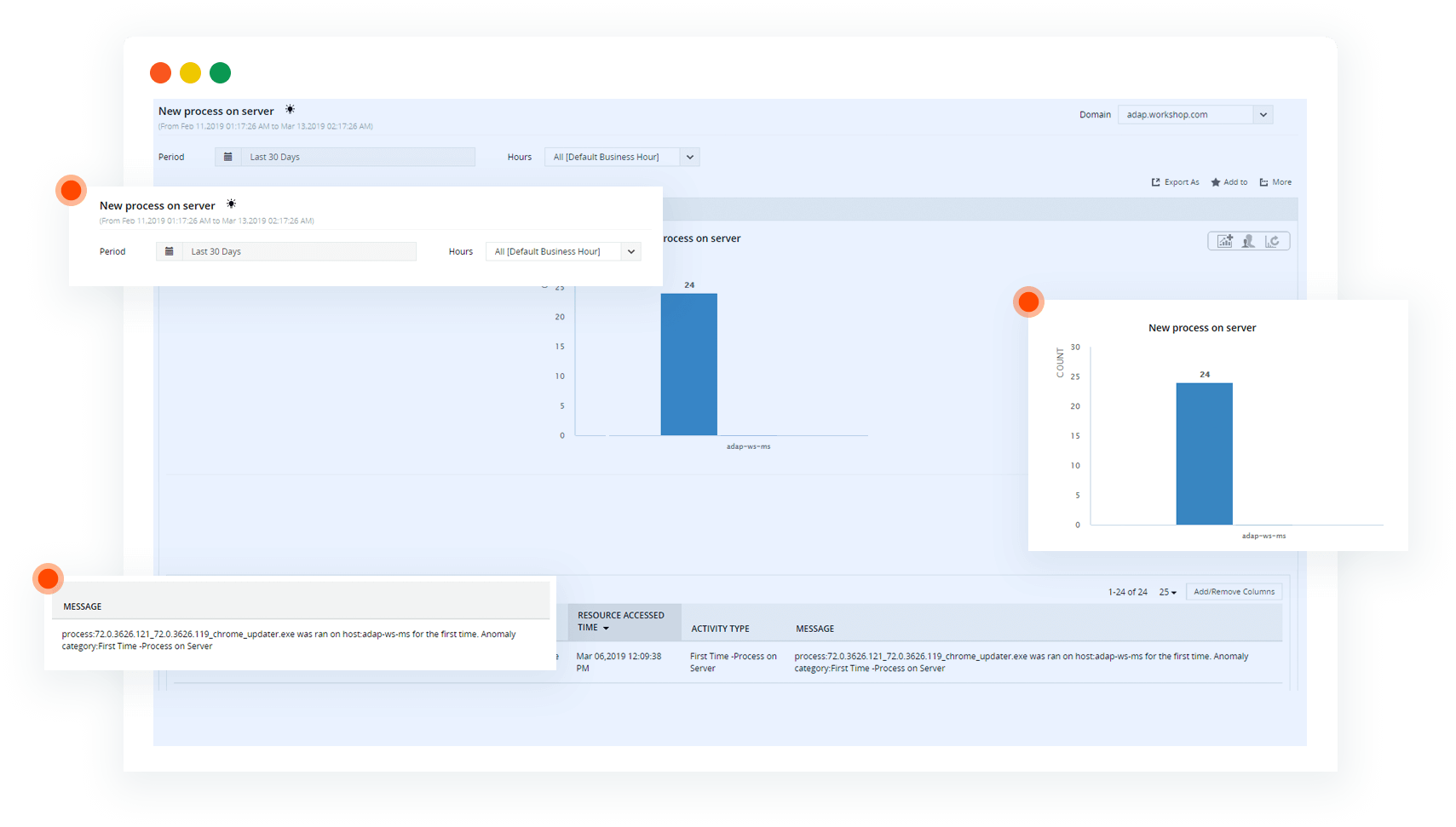
Malware
Receive notification when there is an unusual process running on a machine.
-
Investigate anomalies
See who did what, when, and where, along with other details surrounding each anomaly.
-
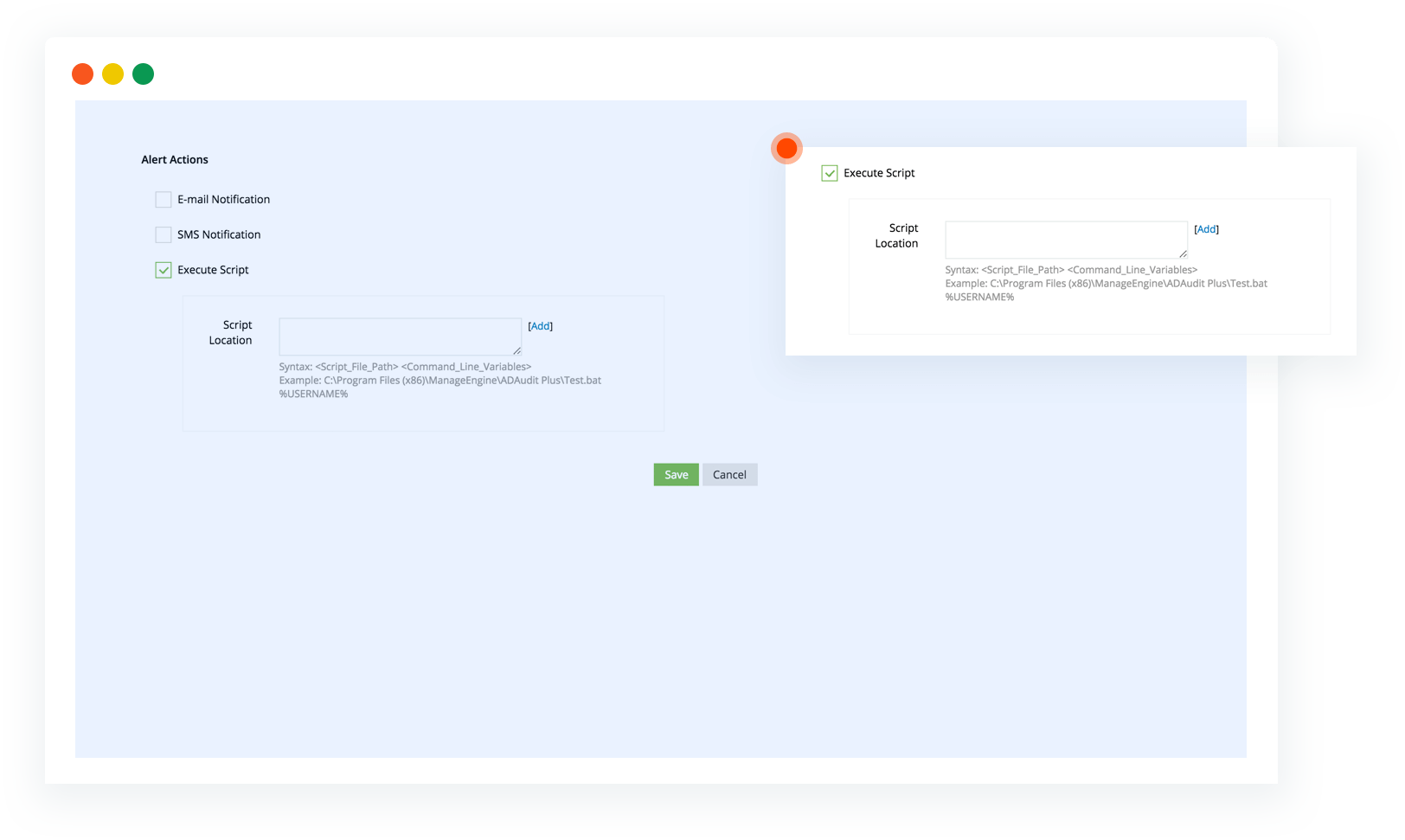
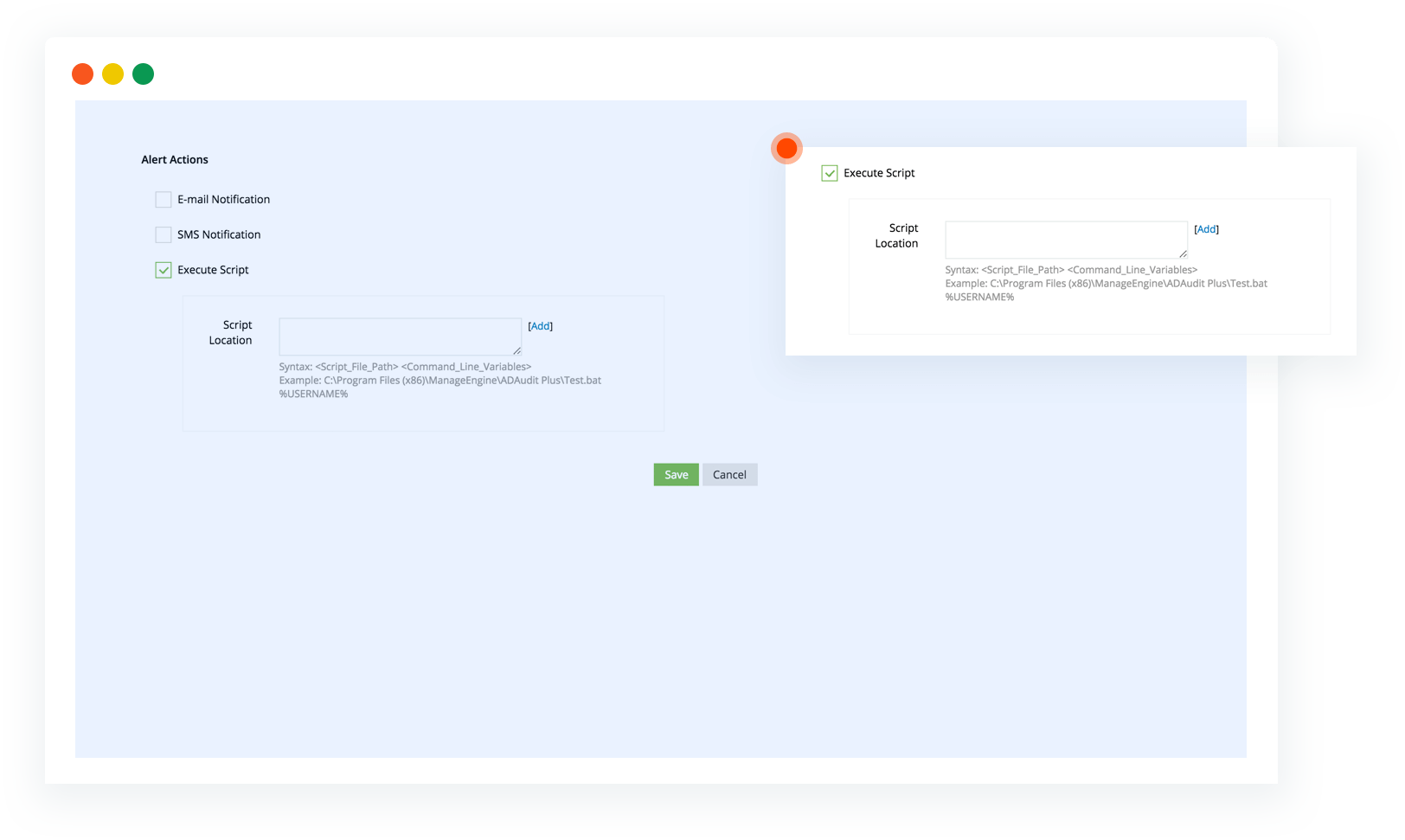
Mitigate threats
Configure ADAudit Plus to execute a predetermined action when an anomaly gets detected.