How ADManager Plus can help prevent privilege abuse?
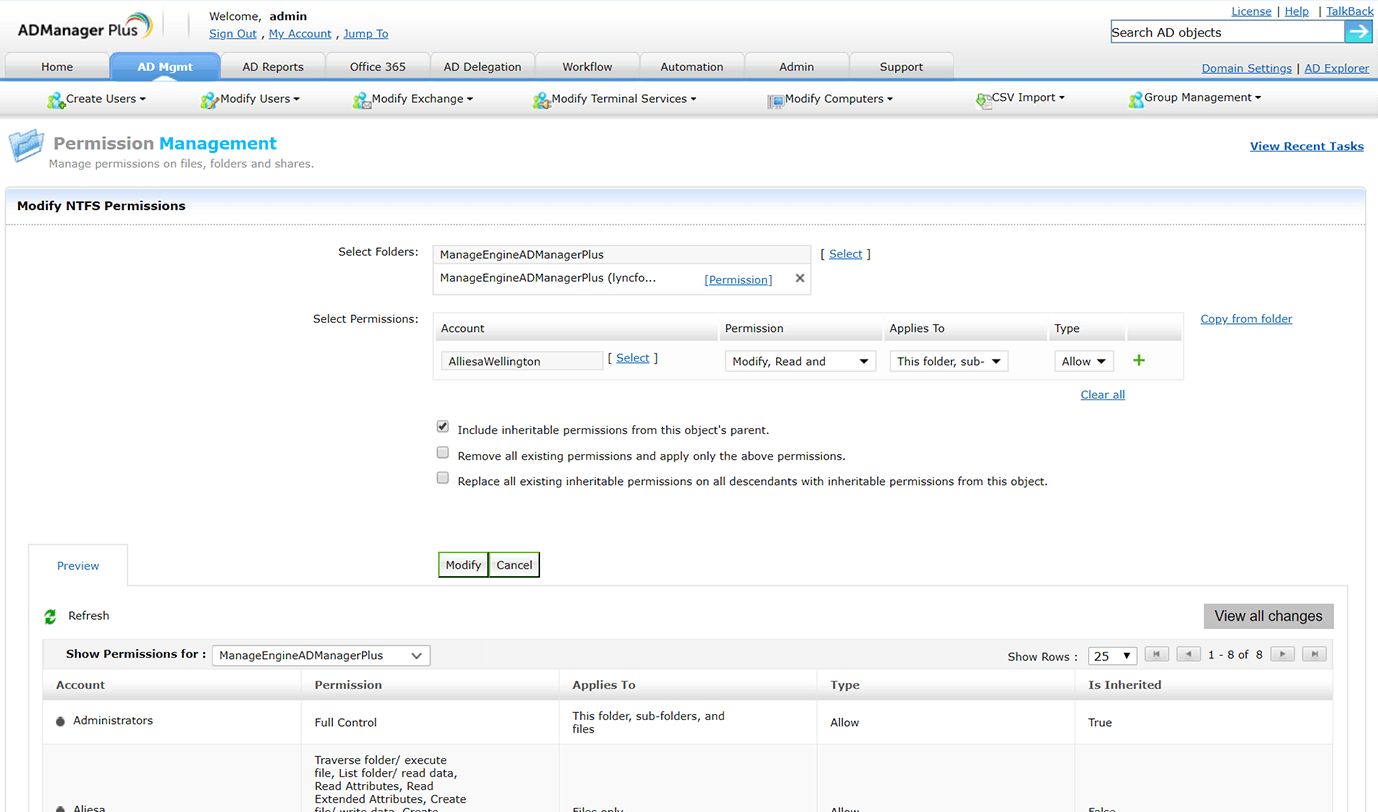
Comprehensive NTFS management and reporting
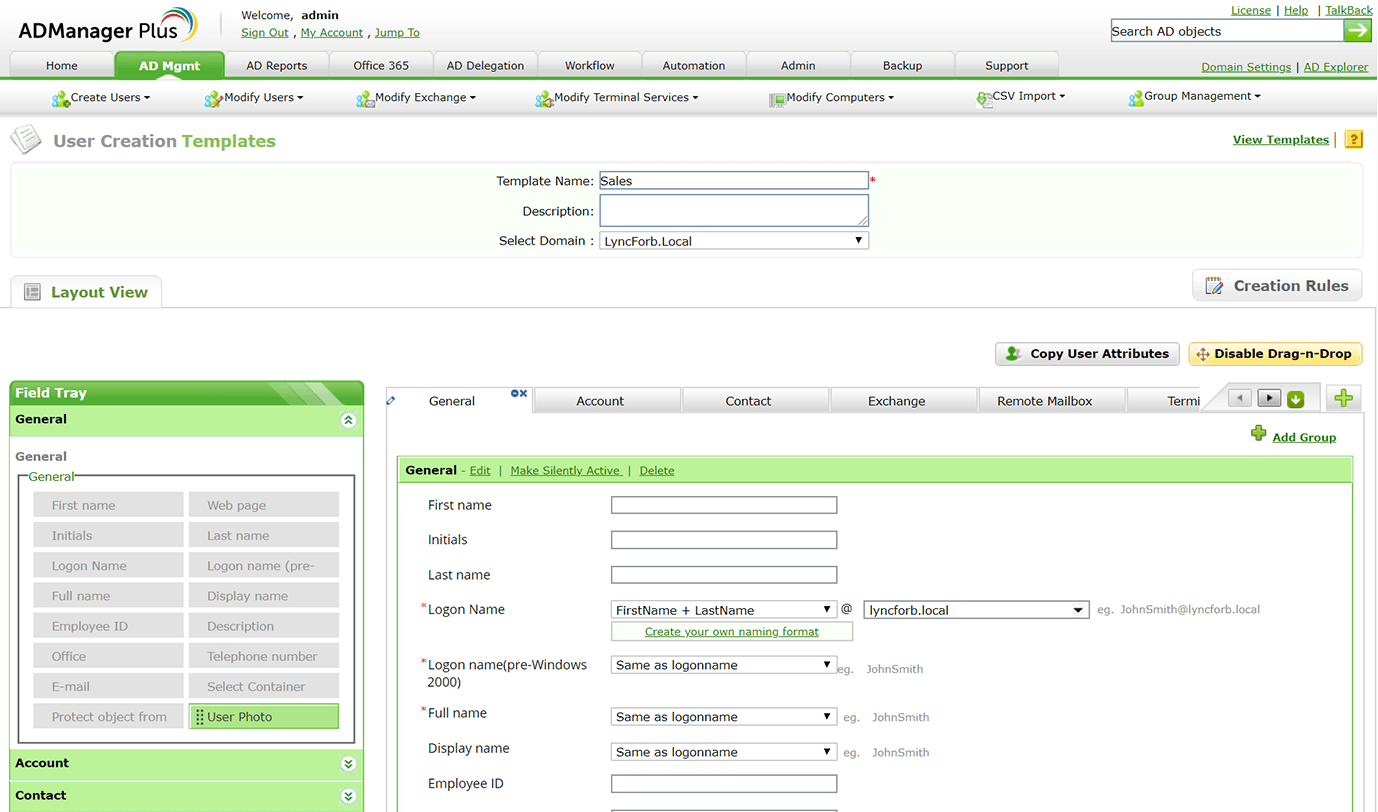
Template-based provisioning
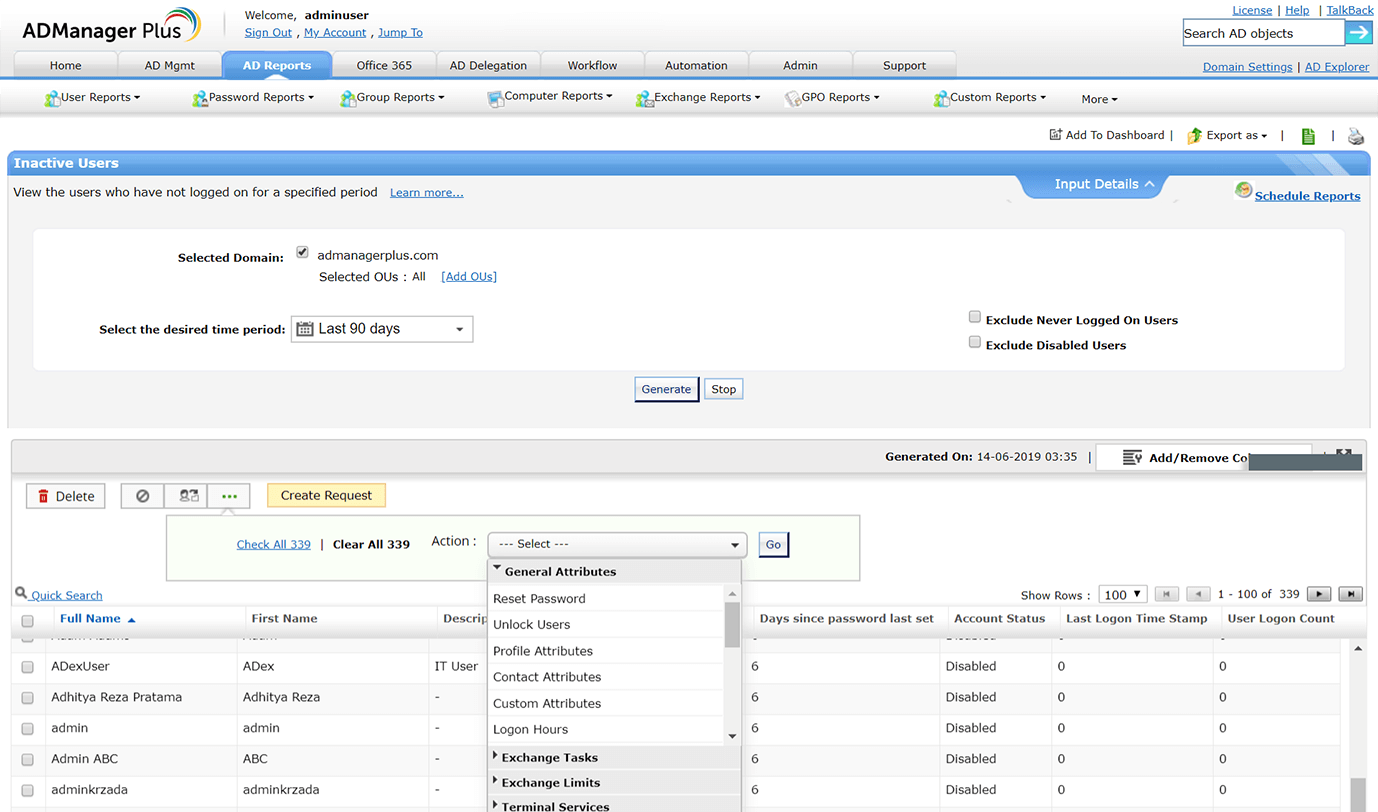
Inactive user management
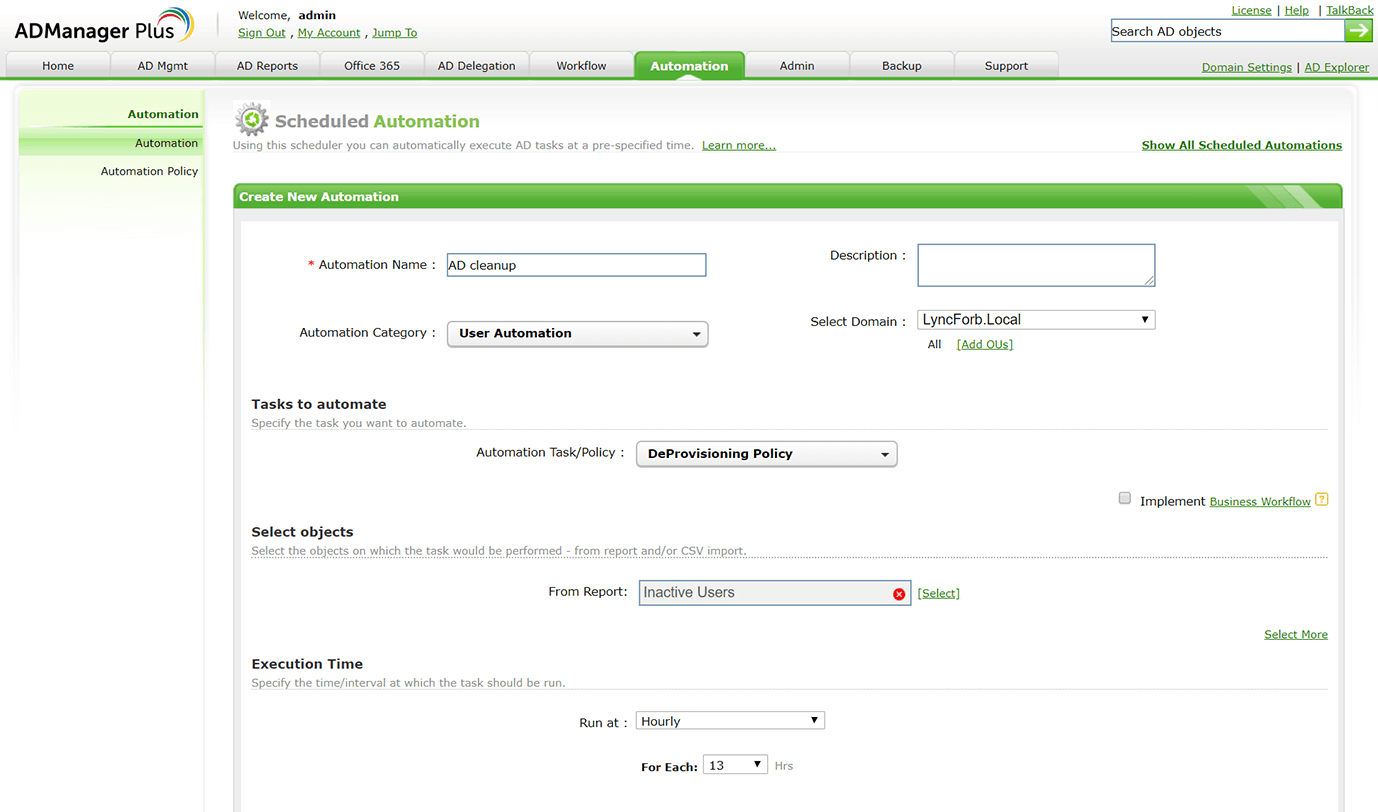
Automated deprovisioning policies
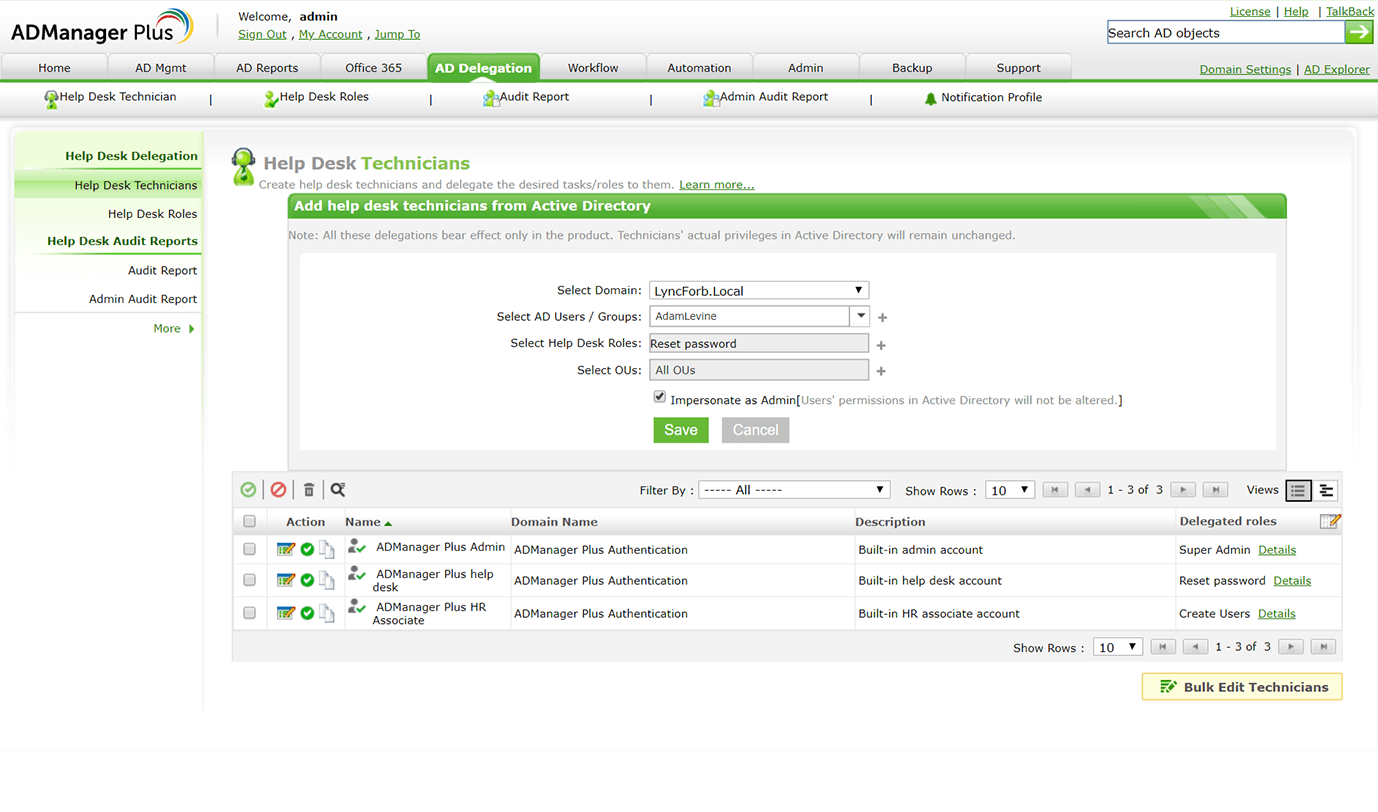
OU-based delegation
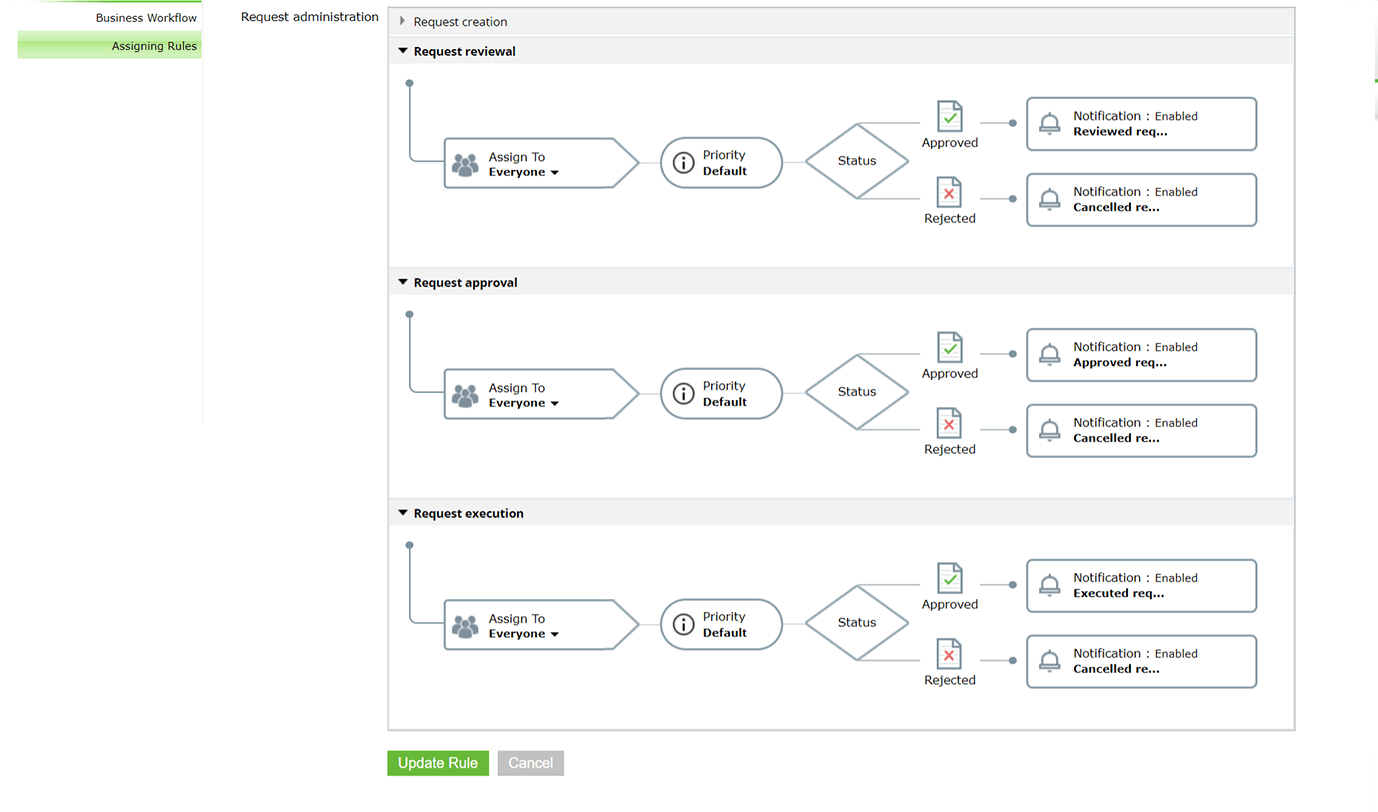
Multi-tier request approval process