# Endpoint Central helps comply with DORA
COMPLIANCE > DORA
## Endpoint Central : Your partner in navigating DORA requirements
## Key Highlights
- **759,000**
financial entities across europe
- **$6.08 million**
average cost of data breach in financial sector
- **20**
types of financial industries covered by DORA
- **5 pillars**
laying foundation for operational resilience
- **63 articles**
of DORA ensuring comprehensive coverage
With financial entities embracing the digital age, they face constant threats from cyberattacks, operational disruptions, and data breaches. A robust cybersecurity framework is then essential to ensure operational resilience, safeguard customer trust, and meet regulatory expectations. The financial sector needs solutions that can proactively manage ICT (Information and Communication Technologies) risks, address incidents efficiently, and maintain operational continuity.
Recognizing the importance of cybersecurity, the European Union introduced the Digital Operational Resilience Act (DORA) on 27 December 2022. DORA aims to strengthen the digital resilience of financial entities by setting unified standards for managing ICT risks, ensuring continuity, and responding effectively to disruptions.
DORA is applicable to a wide range of financial institutions across Europe, since 17th January 2025.
## Why Choose Endpoint Central for DORA Compliance?
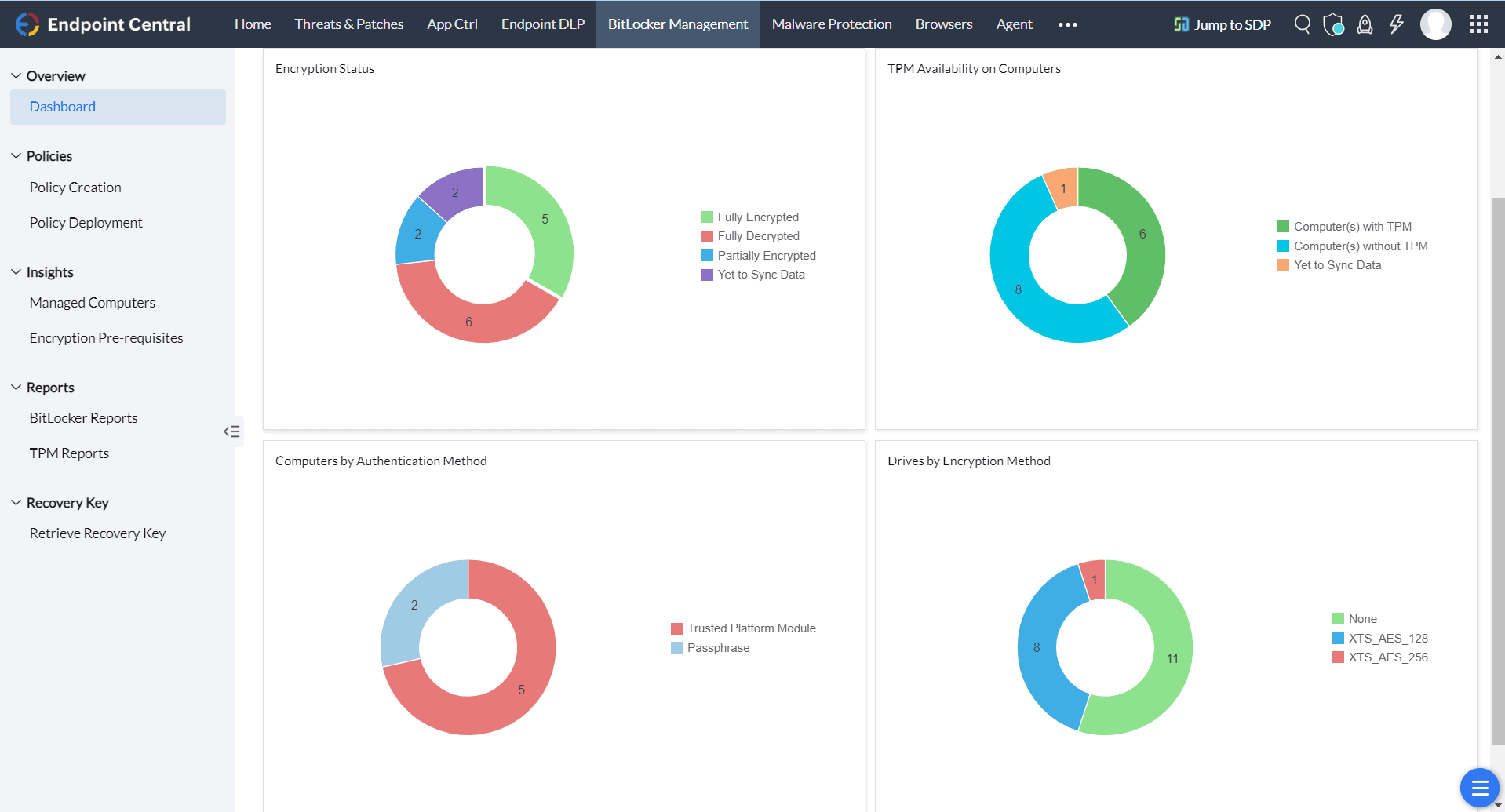
### Maintain Cyber hygiene
Endpoint Central provides all the tools you need to uphold the highest standards of cyber hygiene. From patching devices and encrypting data to blocking unauthorized privilege escalation, preventing data leaks, and managing USB access, it ensures a secure IT environment.
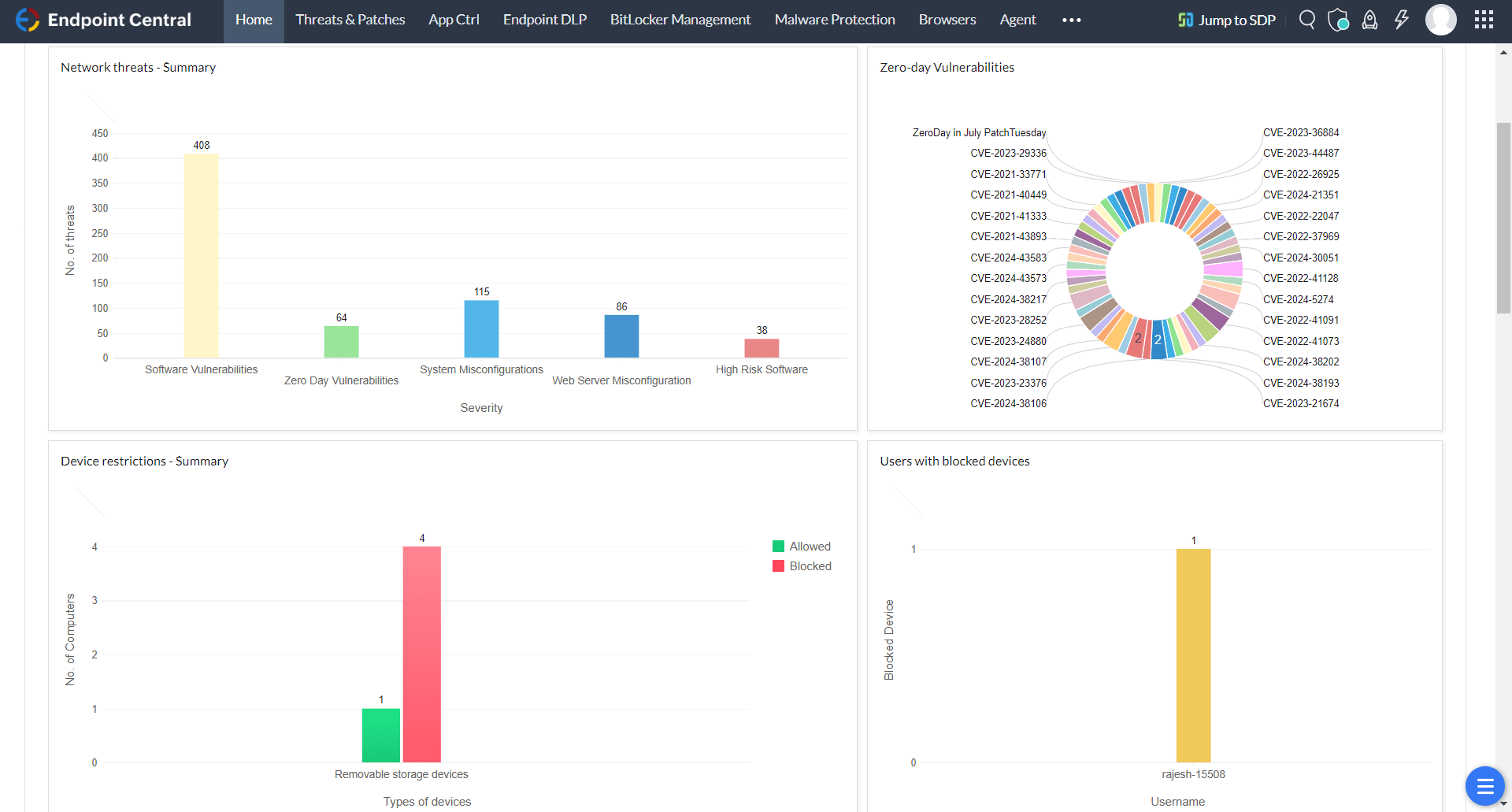
### Simplified Compliance process
Designed for effortless compliance, Endpoint Central offers audit-ready reports and dynamic dashboards, giving you real-time insights into risks and vulnerabilities across your IT infrastructure.
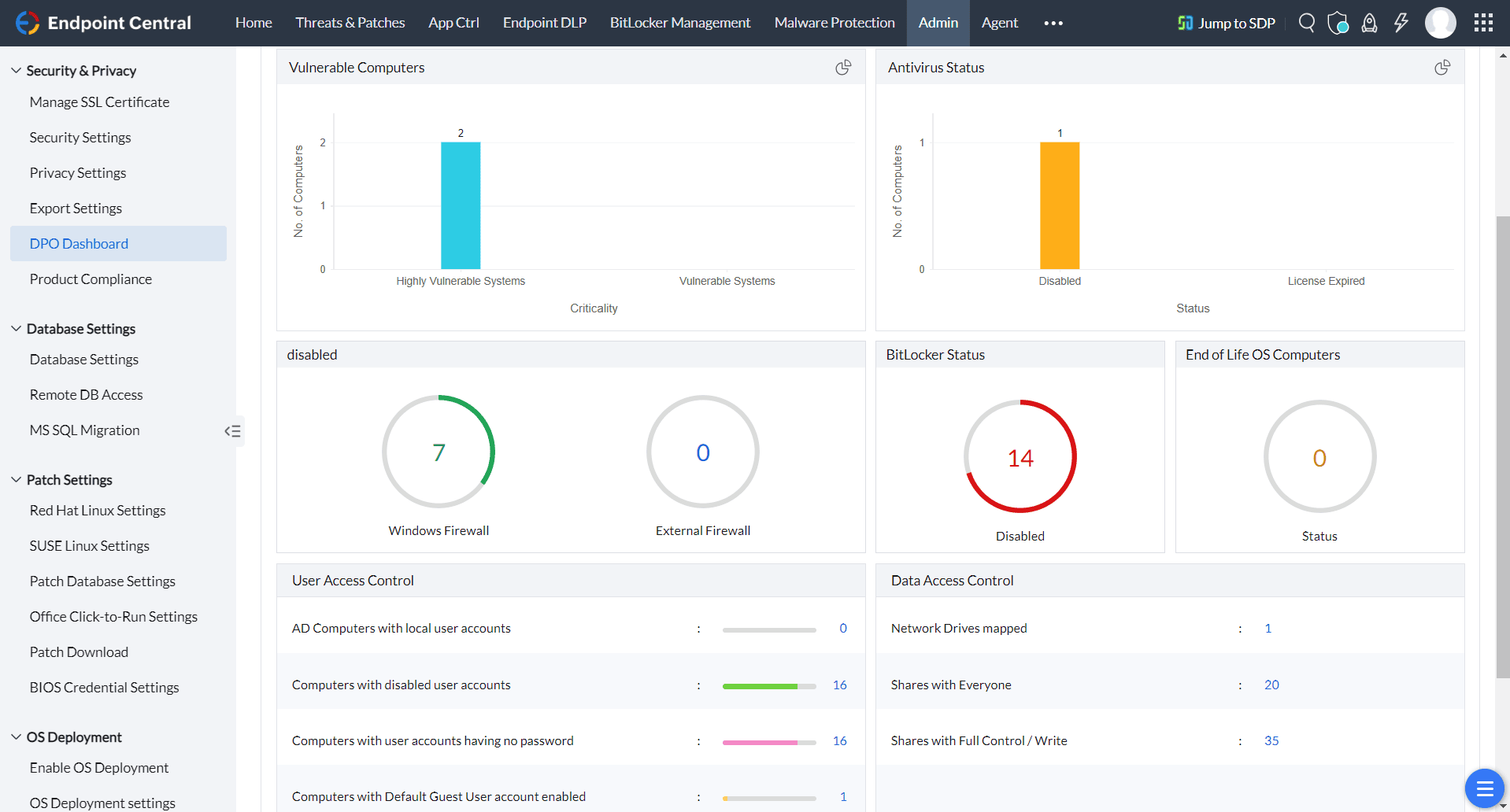
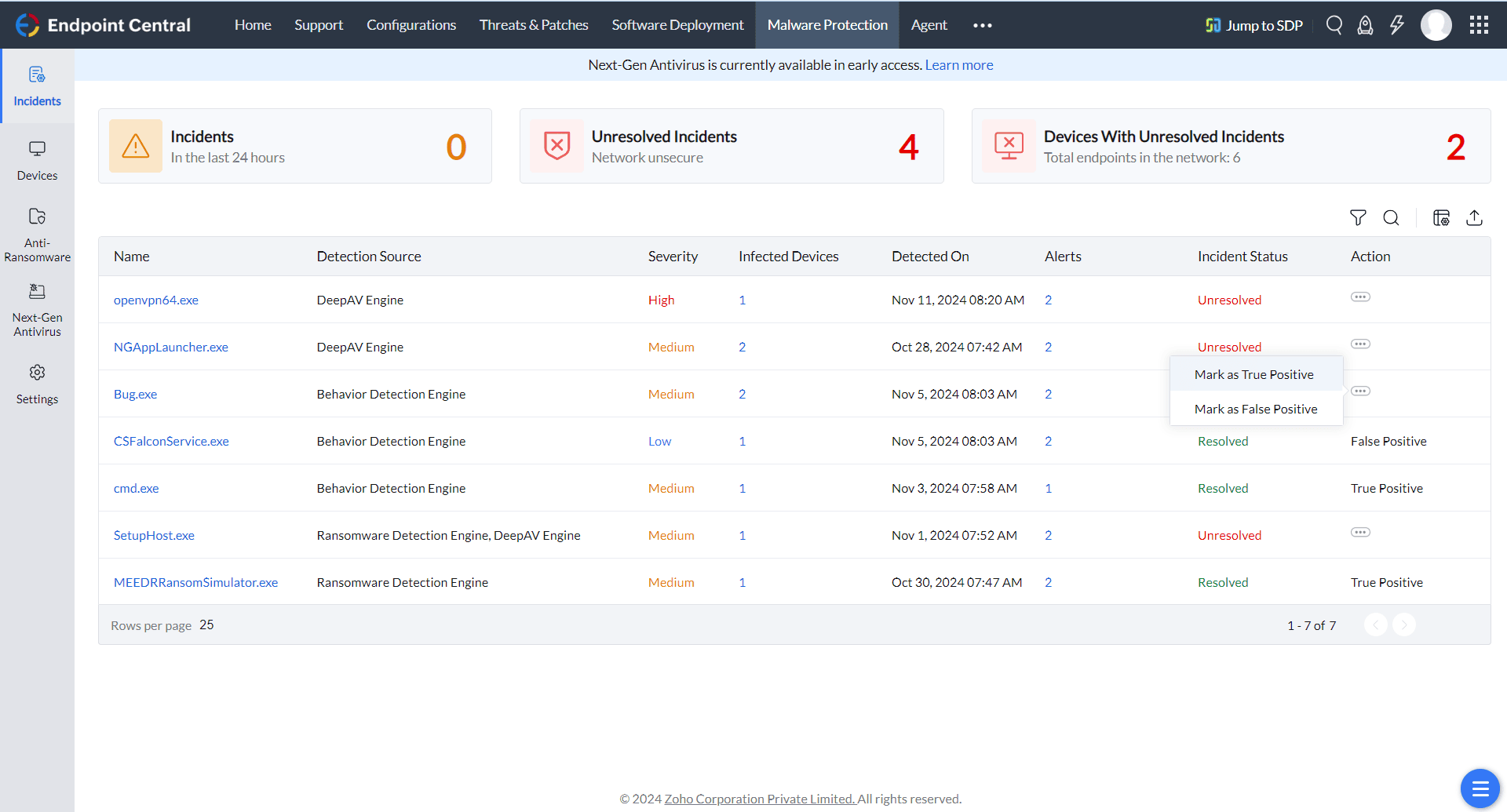
### Comprehensive IT Visibility
Gain complete visibility into your IT environment through advanced asset management features. Endpoint Central also strengthens security with robust anti-malware capabilities, one-click data restoration, and endpoint quarantine, minimizing disruptions and ensuring seamless operations.
[SEE ALL FEATURES](https://www.manageengine.com/products/desktop-central/features.html)
## Who falls under DORA's umbrella?
Twenty one categories of financial institutions and service providers fall within the scope of the Digital Operational Resilience Act (DORA).
- **Financial Institutions:** Credit institutions, payment institutions, electronic money institutions, investment firms, and insurance undertakings.
- **Market Infrastructure:** Central securities depositories, central counterparties, trading venues, and trade repositories.
- **Asset and Fund Management:** Alternative investment fund managers, management companies, and institutions for occupational retirement provision.
- **Data and Reporting Services:** Credit rating agencies, data reporting service providers, and administrators of critical benchmarks.
- **Emerging Technologies:** Crypto-asset service providers and crowdfunding service providers.
- **ICT Services:** ICT third-party service providers, including providers of essential technological services.
## The five pillars of DORA
- ICT Risk Management
- Incident Response and Reporting
- Digital Operational Resilience Testing
- Management of ICT Third-Party Risk
- Information Sharing Arrangements
With Endpoint Central, you can seamlessly address the requirements of DORA’s first two pillars.
## DORA articlewise mapping
With advanced ICT risk and incident management, Endpoint Central helps organizations comply with DORA while strengthening their digital resilience. It simplifies cybersecurity by automating key security functions, reducing risks, and ensuring continuous monitoring. We could elaborate further on its capabilities, but that’s why we have provided an **article-wise mapping** for better clarity. Here is a complete overview of how Endpoint Central helps you achieve the measures mentioned in DORA.
[Click here](https://www.manageengine.com/products/desktop-central/how-endpoint-central-helps-with-dora-compliance.html)

## Implementing and delegated acts
The European Supervisory Authorities (ESAs)—comprising the European Banking Authority (EBA), the European Insurance and Occupational Pensions Authority (EIOPA), and the European Securities and Markets Authority (ESMA)—are jointly developed the Implementing and delegated acts. These will provide detailed guidance on implementing DORA's requirements.
Regulatory Technical Standards on ICT risk management tools, methods, processes, and policies and the simplified ICT risk management framework, focuses on ICT risk management tools, methods, processes, and policies.
Learn how Endpoint Central comprehensively supports the requirements outlined in this RTS.
[Click here](https://www.manageengine.com/products/desktop-central/dora-rts.html)

## NIS2 , DORA and GDPR - Europe's cybersecurity trifecta
While NIS2 is a comprehensive cybersecurity directive, many organizations in the European Union are required to comply with other significant compliances and legislations. Here is a very basic run down of NIS2, GDPR and DORA and how they complement each other.
| Article 21 | NIS2 (Network and Information Security) 2 | DORA (Digital Operational Resilience Act) | GDPR (General Data Protection Regulation) |
|---|---|---|---|
| Scope | Extends to Essential and Important entities in the EU ([Ref Article 3](https://www.nis-2-directive.com/NIS_2_Directive_Article_3.html)) | Extends to all the financial entities in the EU | Extends to all the organizations across the globe that deal with personal data of European citizens |
| Purpose | This directive is intended to raise cybersecurity standards across the EU | As the name indicates, this is to strengthen cybersecurity resilience across the financial sector | GDPR builds on the Right to Privacy, which is widely recognized as a fundamental right worldwide. |
| Relation with NIS 2 | - | - According to the [Commission's Guidelines on Article 4 (1) and (2) of the NIS 2 Directive](https://www.nis-2-directive.com/), the cybersecurity and incident reporting rules under the NIS 2 Directive do not apply to sectors already covered by sector specific laws.
- For financial entities, **DORA (Digital Operational Resilience Act)** acts as a sector-specific law. This means organizations covered by DORA are not subject to the cybersecurity and reporting requirements of the NIS 2 Directive. | The cybersecurity framework of NIS 2 overlaps with GDPR requirements, helping organizations work towards GDPR compliance more effectively. |
| Penalties | Essential entities can face fines up to **€10 million or 2% of global turnover**, while important entities risk fines up to **€7 million or 1.4% of global turnover**. | The DORA Act does not explicitly specify penalties. However, regulatory authorities in the EU and its member states will have the authority to enforce and impose them. | - Severe Violations: **Up to €20 million or up to 4% of their total global turnover** of the preceding fiscal year.
- Less Severe Violations: **Up to €10 million or up to 2% of their total global turnover** of the preceding fiscal year. |
## Endpoint Central helps in achieving the following compliances
- [CIS](https://www.manageengine.com/products/desktop-central/cis-compliance.html)
- [FERPA](https://www.manageengine.com/products/desktop-central/ferpa-compliance.html)
- [NIST](https://www.manageengine.com/products/desktop-central/nist-compliance.html)
- [UK CYBER ESSENTIALS](https://www.manageengine.com/products/desktop-central/ncsc-uk-cybersecurity-essentials.html)
- [NCA](https://www.manageengine.com/products/desktop-central/nca-compliance.html)
- [ISO 27001](https://www.manageengine.com/products/desktop-central/iso-compliance.html)
- [PCI DSS](https://www.manageengine.com/products/desktop-central/pcidss-compliance.html)
- [NIST 2.0 CSF](https://www.manageengine.com/products/desktop-central/nist-csf-2.html)
- [HIPAA](https://www.manageengine.com/products/desktop-central/hipaa-compliance.html)
- [DORA](https://www.manageengine.com/products/desktop-central/digital-operational-resilience-act-compliance.html)
- [GDPR](https://www.manageengine.com/products/desktop-central/gdpr-compliance.html)
- [NIS2](https://www.manageengine.com/products/desktop-central/nis2-compliance.html)
- [RBI](https://www.manageengine.com/products/desktop-central/rbi-bank-compliances.html)
- [Essential 8](https://www.manageengine.com/products/desktop-central/acsc-essential-eight.html)
## Recommended reads
- [GDPR compliance made easy with Endpoint Central](https://www.manageengine.com/products/desktop-central/gdpr-compliance.html)
- [Strengthen your cybersecurity posture with NIS2 compliance](https://www.manageengine.com/products/desktop-central/nis2-compliance.html)
- [Compliance and cybersecurity are two sides of the same coin](https://www.manageengine.com/products/desktop-central/webinars/cybersecurity-and-compliance-with-endpoint-central.html)