Credential Hardening
Table of contents
When an attacker gains access to a computer, their first objective is almost always the same: steal user credentials. Credentials are the keys to the kingdom. Once compromised, they allow attackers to impersonate legitimate users, escalate privileges, move laterally across the network, and ultimately gain control over critical systems.
This is why credential protection is one of the most important pillars of endpoint security.
After initial access attackers typically:
- Extract the logged-in user's credentials
- Attempt privilege escalation
- Harvest cached or stored credentials from the system
- Move laterally to other machines
- Compromise domain accounts and servers
Credential theft enables attackers to operate under trusted identities, making detection more difficult and damage more severe.
How Windows Stores Credentials
On Windows systems, sensitive authentication data is stored in specific system components, including:
- LSASS Memory: The Local Security Authority Subsystem Service (LSASS) stores authentication credentials in memory. This includes password hashes, Kerberos tickets, and other security tokens.
- SAM Hive: The Security Account Manager (SAM) hive stores local account password hashes. If an attacker gains access to the SAM database (online or offline), they can attempt to crack password hashes and reuse them elsewhere in the network.
What is Credential Hardening?
Credential hardening is a security approach designed to protect these sensitive credential storage locations from unauthorized access.
Instead of waiting for credential dumping to succeed, credential hardening:
- Restricts access to LSASS memory
- Protects the SAM hive from unauthorized reads
- Monitors processes attempting to access these locations
- Blocks or kills suspicious processes immediately
- Logs and alerts administrators in real time
This ensures that even if malware lands on the machine, it cannot easily extract credentials.
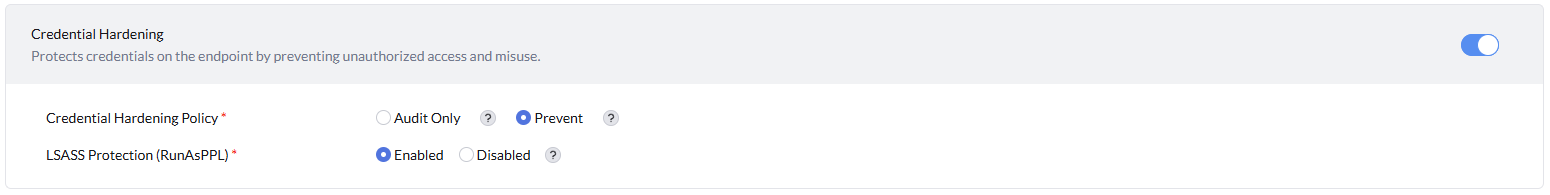
Configuring Credential Hardening Policy
- Audit Only: Monitors credential access and reports suspicious activity.
- Prevent: Blocks unauthorized access to credentials and prevents credential theft.
LSASS Protection (RunAsPPL) prevents unauthorized access to the Local Security Authority Subsystem Service (LSASS) process, which is responsible for enforcing security policies and storing sensitive credentials.
- Enabled: Restricts DLL's or other processes from accessing LSASS memory.
- Disabled: Allows DLL's/ processes to access LSASS memory, increasing the risk of credential theft.