Just-In-Time Access
Table of contents
Just-In-Time Access Explained
Just-in-Time (JIT) access in Endpoint Central enables administrators to provide users with temporary, scoped privileges only when required for specific tasks — eliminating the need for standing administrative rights. JIT access supports two models of elevation: admin-configured policies that proactively grant access based on predefined criteria, and a request-based model where users can initiate elevation on demand with a justification and a defined time duration. In both cases, access is tightly controlled, time-bound, and can be scoped to specific applications using a wide range of criteria such as vendor, file hash, folder path, and more.
The Importance of Just-In-Time Access
Granting permanent administrative rights is one of the most common contributors to security vulnerabilities — it expands the attack surface and increases the risk of both insider threats and unauthorized access. JIT access directly addresses this by ensuring that elevated privileges are granted only when needed, only to the right users, and only for as long as necessary. The request-based elevation model adds a further layer of accountability, as users must provide a justification before access is approved, creating a clear and auditable trail of privilege usage. Together, these capabilities help organizations enforce the principle of least privilege, strengthen their overall security posture, and significantly reduce the likelihood of data breaches.
Configuring Just-In-Time Access
The temporary access can be provided to specific computers through the following steps:
- Navigate to Just in Time Access under Policies.
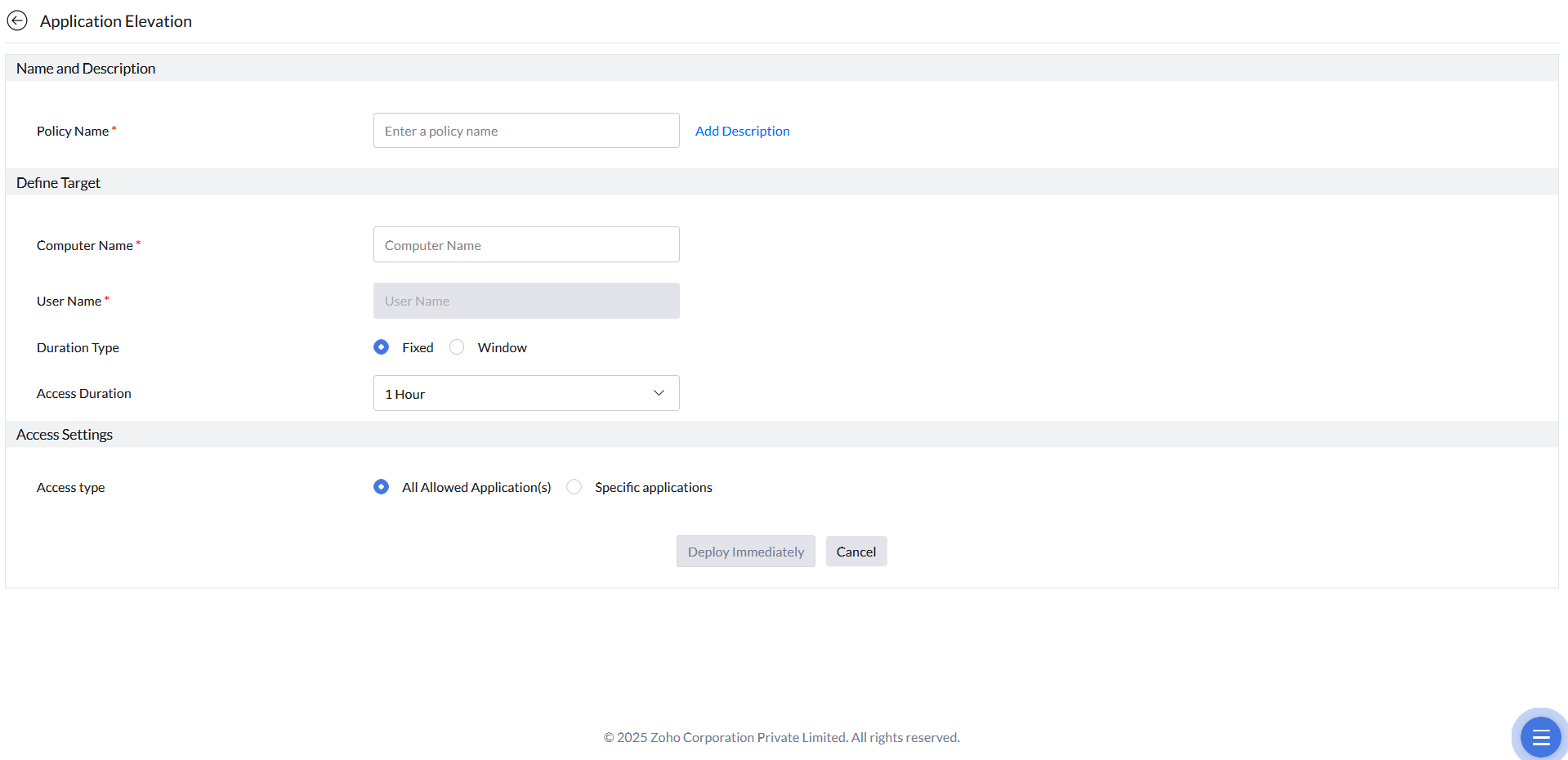
- Click Create to delegate a new JIT access policy and select Application Elevation.
- Provide the Name and Description for the policy.
- Provide the Computer Name for which you want to provide JIT access and select the User Name.
- Select the specific user or to grant access to all users on this computer, select All users.
- Select the duration type: Fixed or Window. If the duration type is fixed, provide the duration of access and if it's a window, provide a window time frame for which you want to provide the JIT Access.
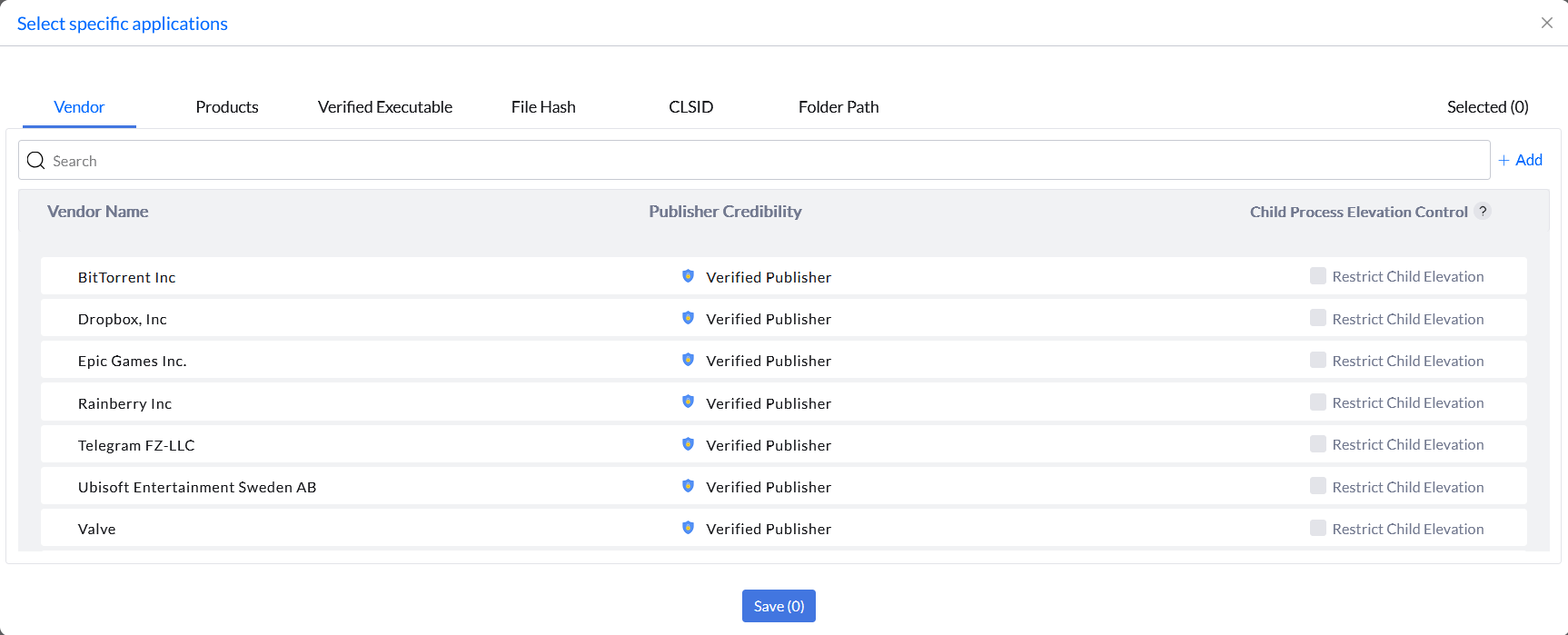
- In the Access Settings, the Just In Time Access for self-elevation option will grant the user to self-elevate their privileges to all allowed applications or specific applications. If you choose All Allowed Application(s), the user can self-elevate any allowlisted application. If you choose Specific applications, the user can self-elevate only the applications selected. The specific applications for elevation can be added using the rule types such as Vendor, Products, Verified Executable, File Hash, CLSID, and Folder Path.
- Click Deploy Immediately.
User-Initiated Elevation Requests
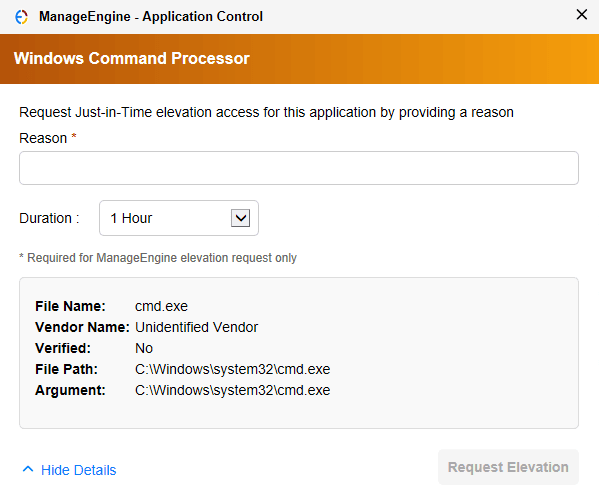
In addition to admin-configured JIT policies, Endpoint Central also supports a request-based elevation model where users can initiate privilege elevation on their own. This gives end users the flexibility to request temporary access when needed, while keeping administrators in full control of what gets approved.
When a user attempts to run an application that requires elevated privileges, they are presented with a prompt to submit a Just-In-Time elevation request. The user must specify a time duration for the access and provide a justification for the request.
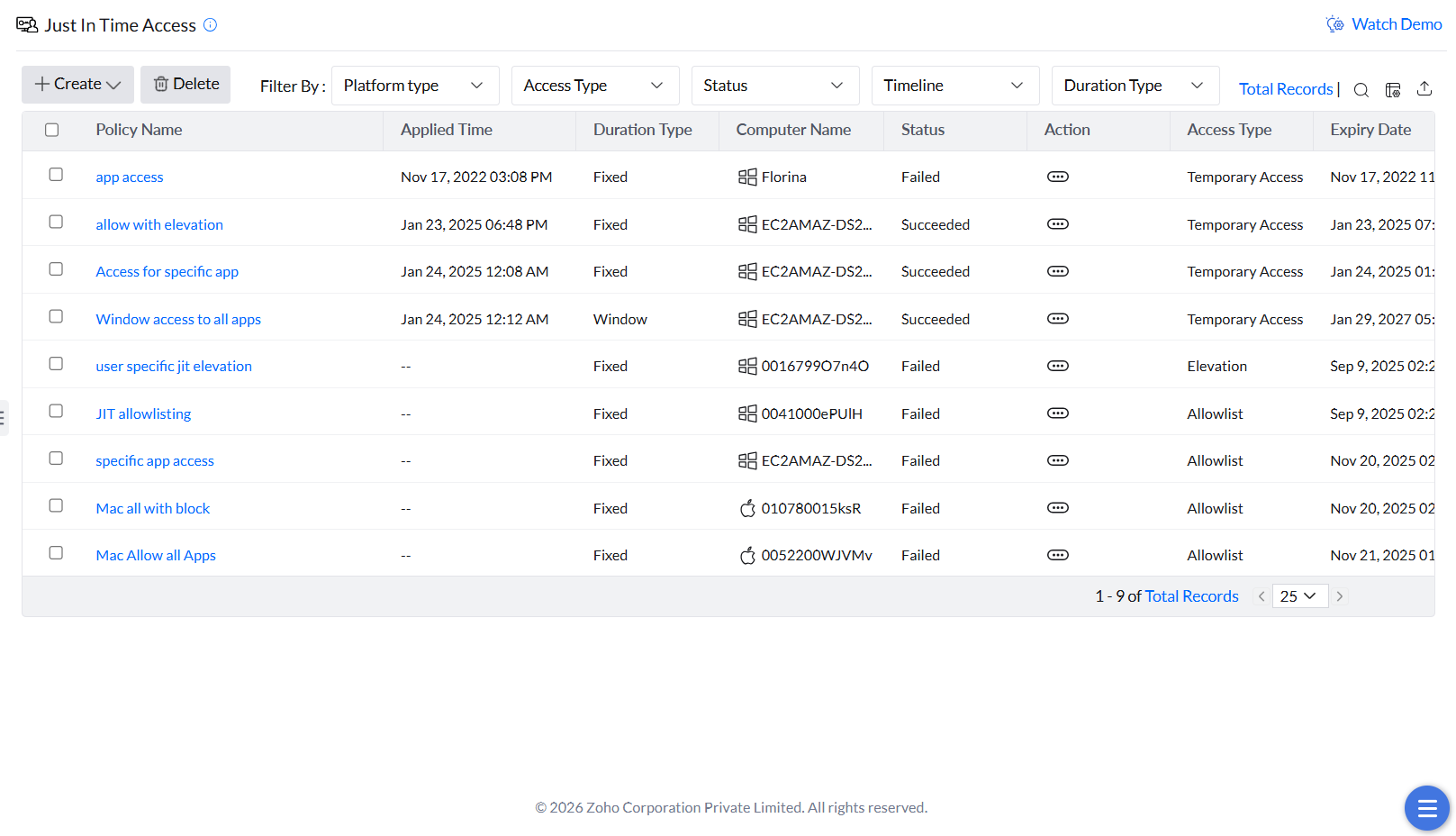
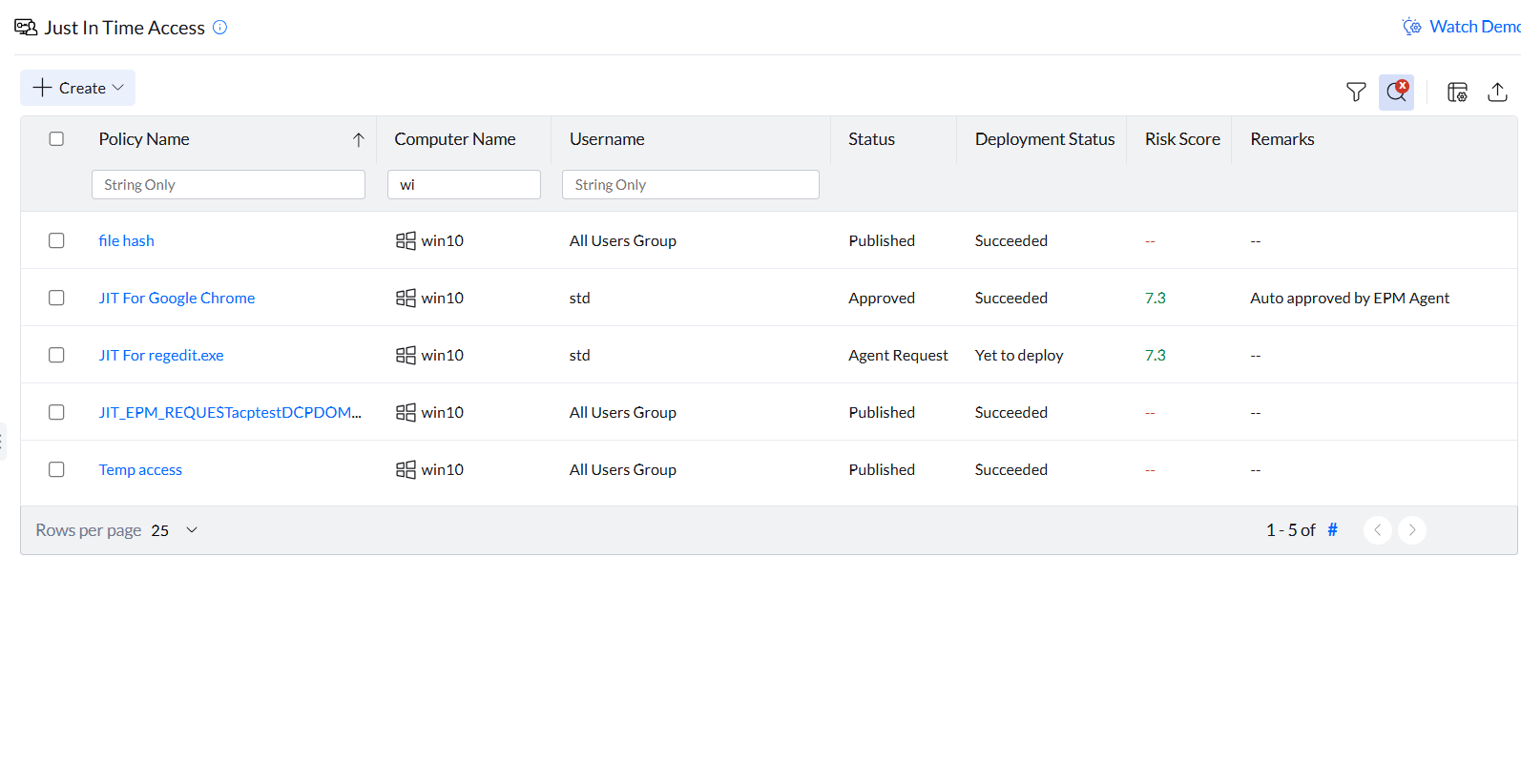
Reviewing and Managing Requests
All pending elevation requests are displayed in the Just-In-Time Access tab, where administrators can review the user's justification and either approve or decline the request based on organizational requirements.
- Approved access is automatically revoked once the requested time duration expires.
- Administrators can also manually revoke active access at any time directly from the console.
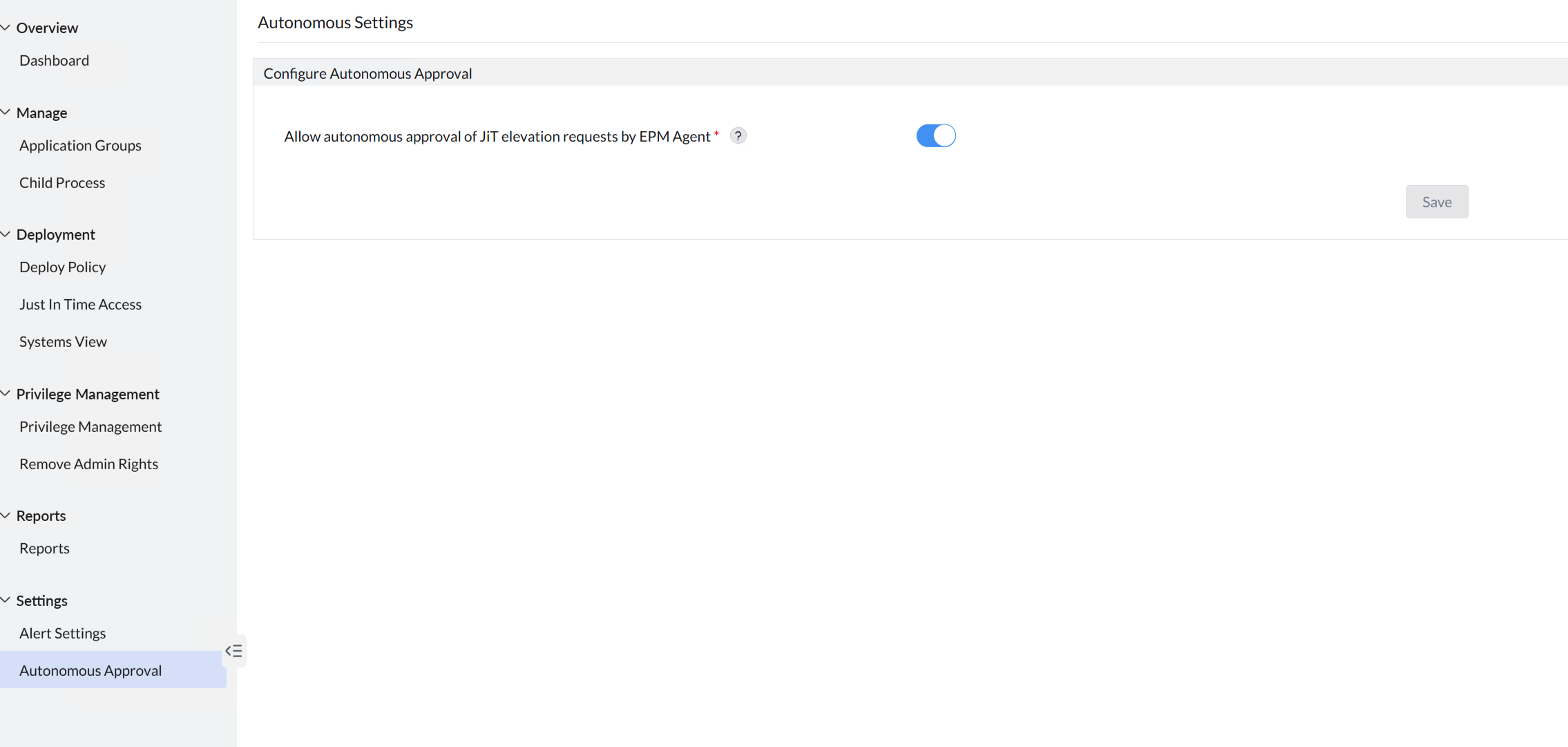
Autonomous Approval
To streamline the approval process for trusted users or low-risk applications, administrators can enable Autonomous Approval. When configured, eligible elevation requests are automatically approved without requiring manual admin intervention. This option can be enabled under Settings → Autonomous Approval.
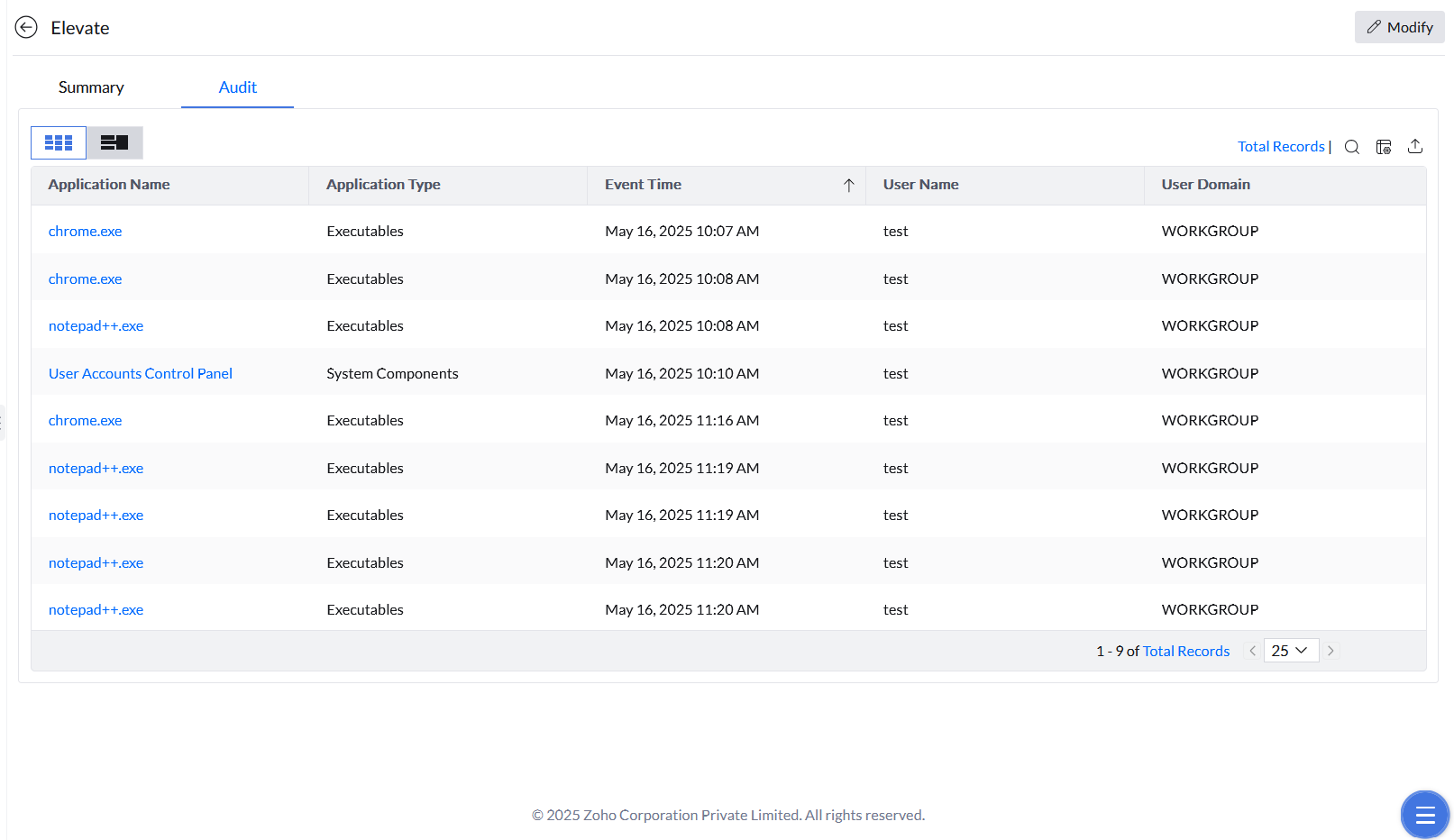
Just-In-Time Events Report
The events occurring under each JIT policy are accessible by clicking the desired policy and selecting the Audit tab.