| Requirement |
How EventLog Analyzer helps with compliance |
EventLog Analyzer reports |
PMC 1
Accurate time stamp |
Prevents anyone from tampering with log timestamps. |
ELA ensures secure log storage to prevent any tampering. |
PMC 2
Recording of business traffic crossing a boundary |
Records traffic that passes through IIS and Apache web servers in the PMC 2 reports. |
- Apache client errors
- Apache server errors
- Apache HTTP internal server error
- Apache HTTP forbidden
- Apache HTTP server not found
- IIS client errors
- IIS server errors
- IIS password change
- IIS failed user authentication
- IIS HTTP bad request
- IIS site access denied
|
PMC 3
Recording of suspicious activity at the boundary |
Displays all connections that have been denied and possible attacks on network perimeter devices in the PMC 3 reports. |
- Website traffic
- Denied connections
- AWS failed access requests
- All AWS access requests
|
PMC 4
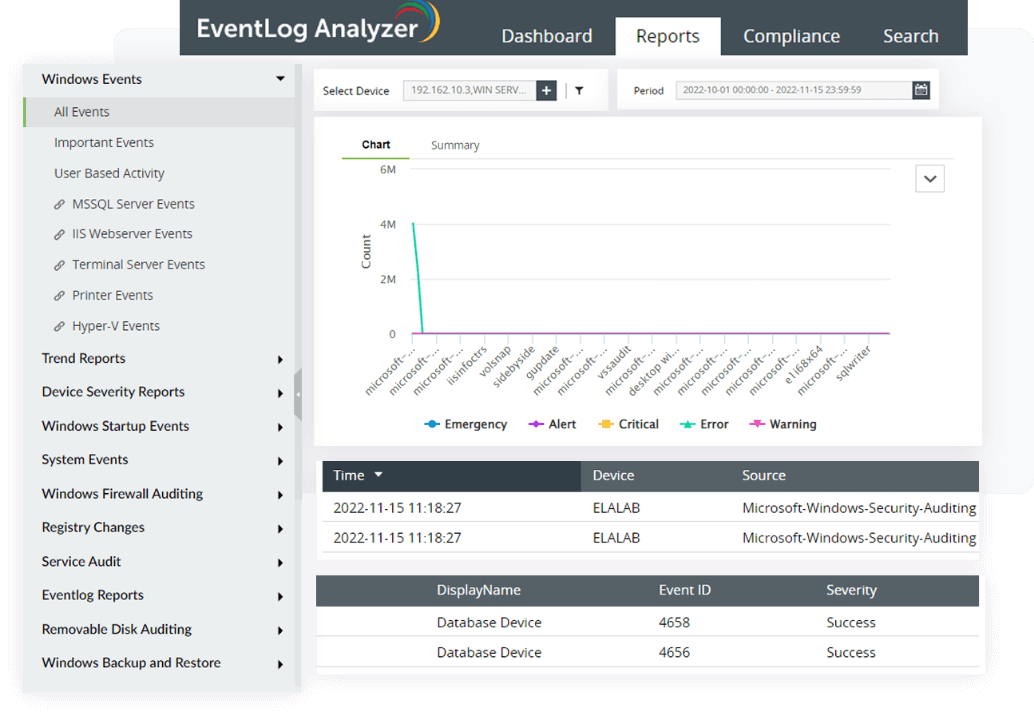
Recording of internal workstation, server, or device status |
Detects and records any suspicious activity, including configuration changes, privileged access, unexpected system and application restarts, software installation, removable media insertion and removal, and sensitive file access. |
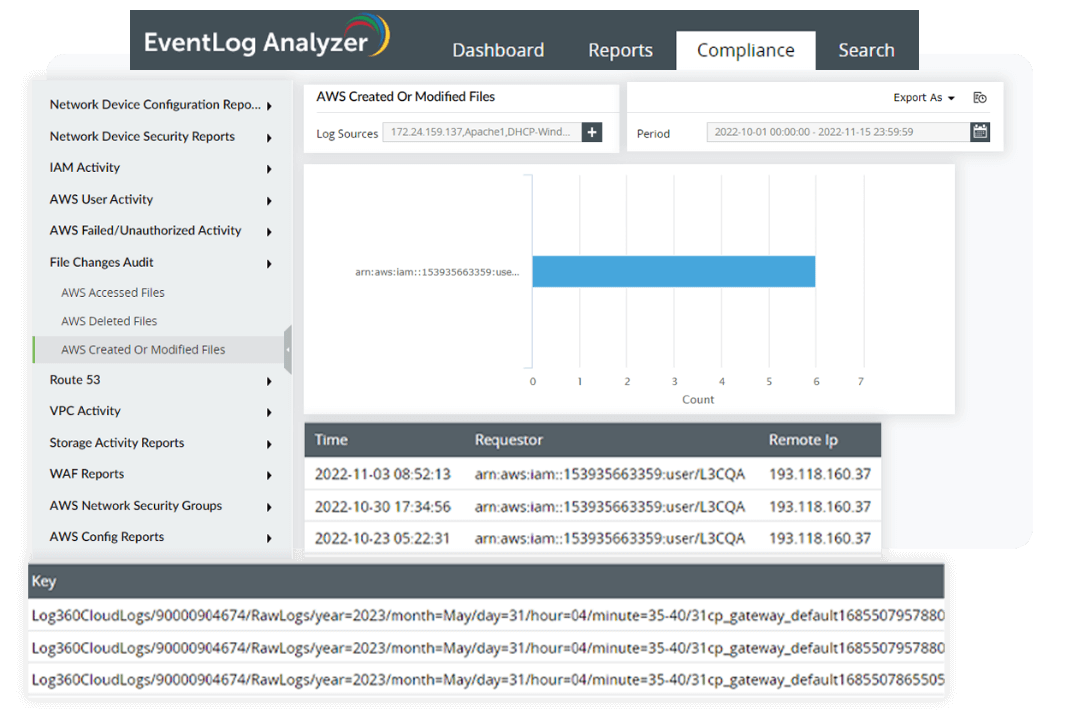
- AWS accessed files
- AWS deleted files
- AWS created or modified files
- Command executed
- Command failed
- Modified buckets
- Deleted buckets
- AWS failed events
|
PMC 5
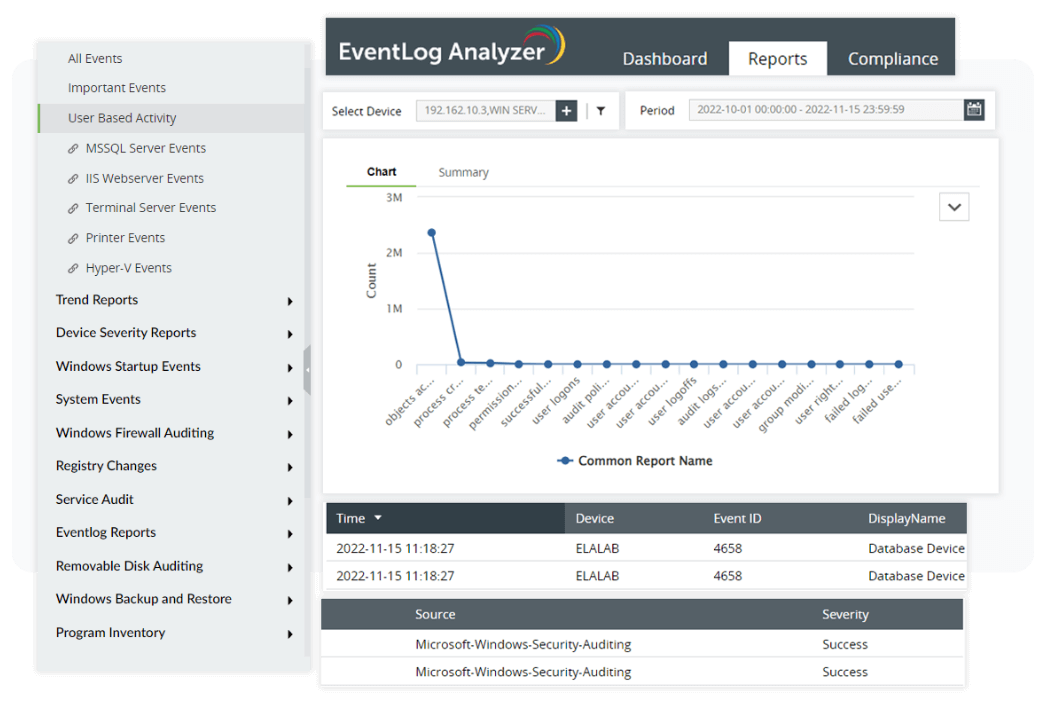
Recording of suspicious internal network activity |
Records policy changes and helps identify if an inside user is carrying out malicious activity. |
- Successful logons
- Failed logons
- Logoff events
- Successful VPN logons
- Failed VPN logons
- Audit policy changes
- User rights assigned
- User rights removed
- Trusted domain created
- Trusted domain modified
|
PMC 6
Recording of network connections |
Records all Windows, Unix, and network perimeter device logons. |
- Windows successful user logons
- Network logon
- Windows successful user logoffs
- Network logoff
- Windows unsuccessful User logons
- User logons
- User logoffs
- Unix unsuccessful user logons
|
PMC 7
Recording of session activity of users and workstations |
Tracks entire user sessions from logon to logoff, including details of their activity during the session. |
- Failed events by user
- Update events by user
- Delete events by user
- Create events by user
|
PMC 8
Recording of data backup status |
Records failed backups and restoration events. |
- Successful Windows backup
- Failed Windows backup
- Successful Windows restore
- Failed Windows restores
|
PMC 9
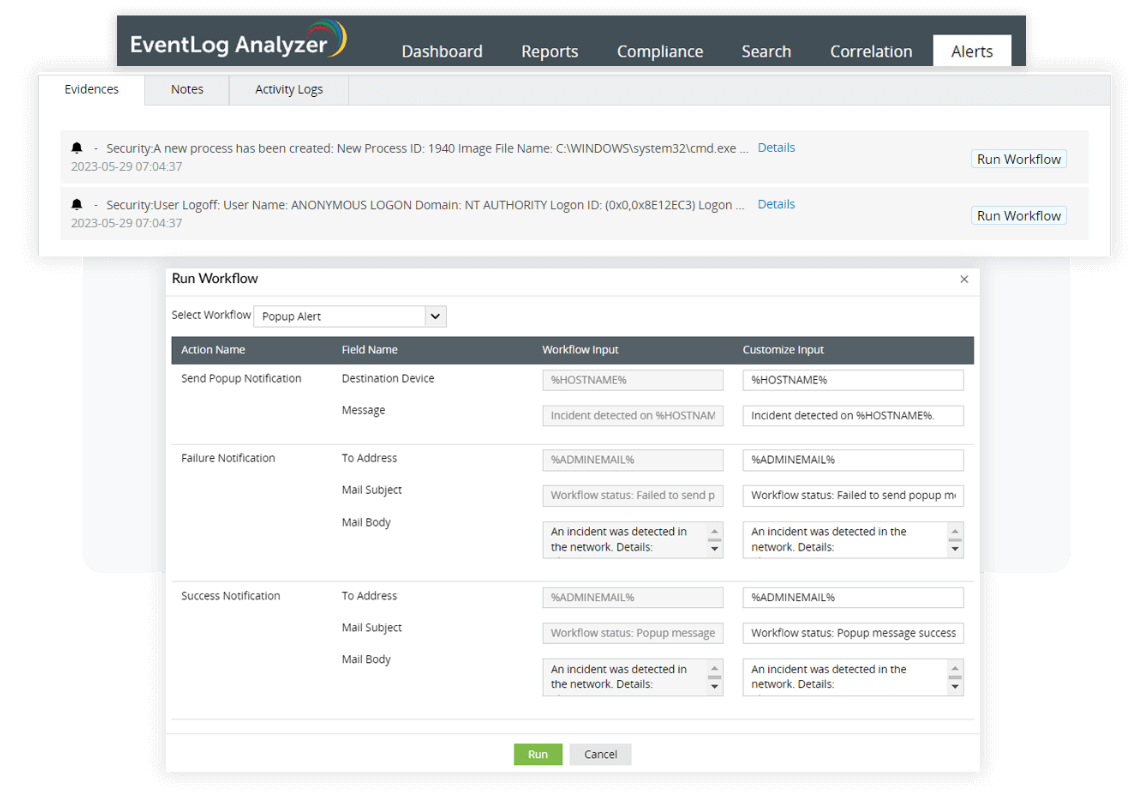
Alerting when critical events occur |
Sends real-time alerts via email and SMS when any anomalous activity happens in the network. A program can be assigned to run when an alert is generated. |
ELA's incident response and management console alerts the users when critical events occur. |
PMC 10
Reporting on the status of the audit system |
Tracks the clearing of all security logs and event logs. |
- Event logs cleared
- Security logs cleared
|
PMC 11
Production of sanitized and statistical management reports |
Offers a highly customizable reporting function. Admins can configure existing reports to suit their specific requirements, or they can create new ones. |
ELA allows you to customize and schedule the existing predefined report in order to meet the unique security policy requirements that are concerned with your enterprise/industry. |
PMC 12
Providing a legal framework for protective monitoring activities |
Ensures that all data is collected and analyzed for forensic validity. |
ELA allows you to centrally collect, archive, search, analyze and correlate machine generated logs obtained from heterogeneous systems, network devices and applications, and generates forensic reports. |