Agenda
Log correlation can help you detect ransomware, brute force attacks, backdoor account creation, worm activity, and much more by sifting through massive volumes of log data. Learn more about the power of correlation and how it can help you proactively mitigate security threats.
Agenda:
- Basics of log correlation
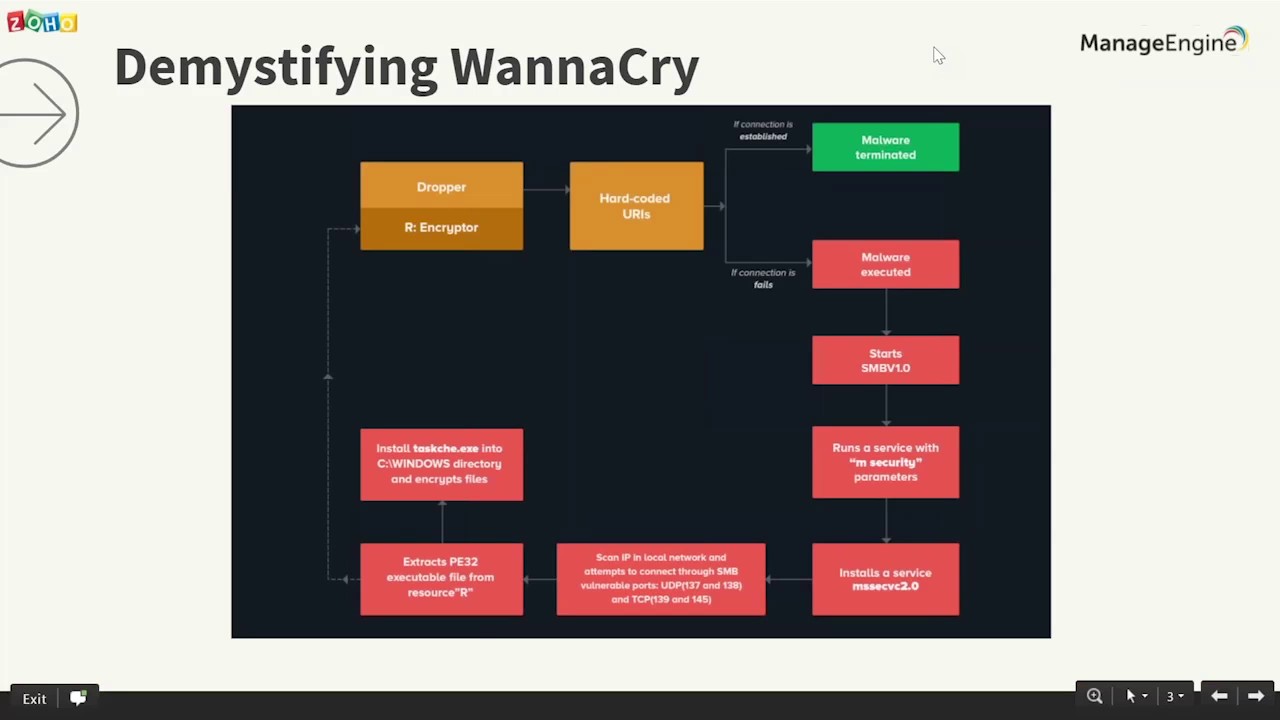
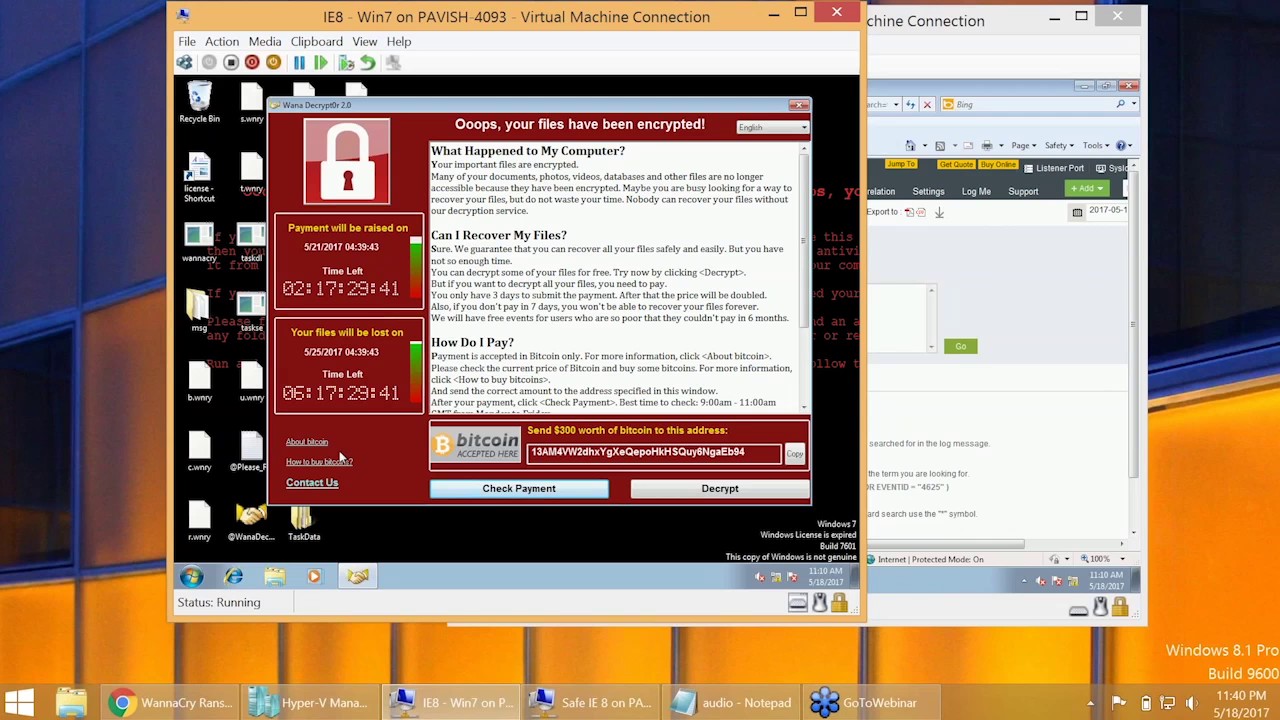
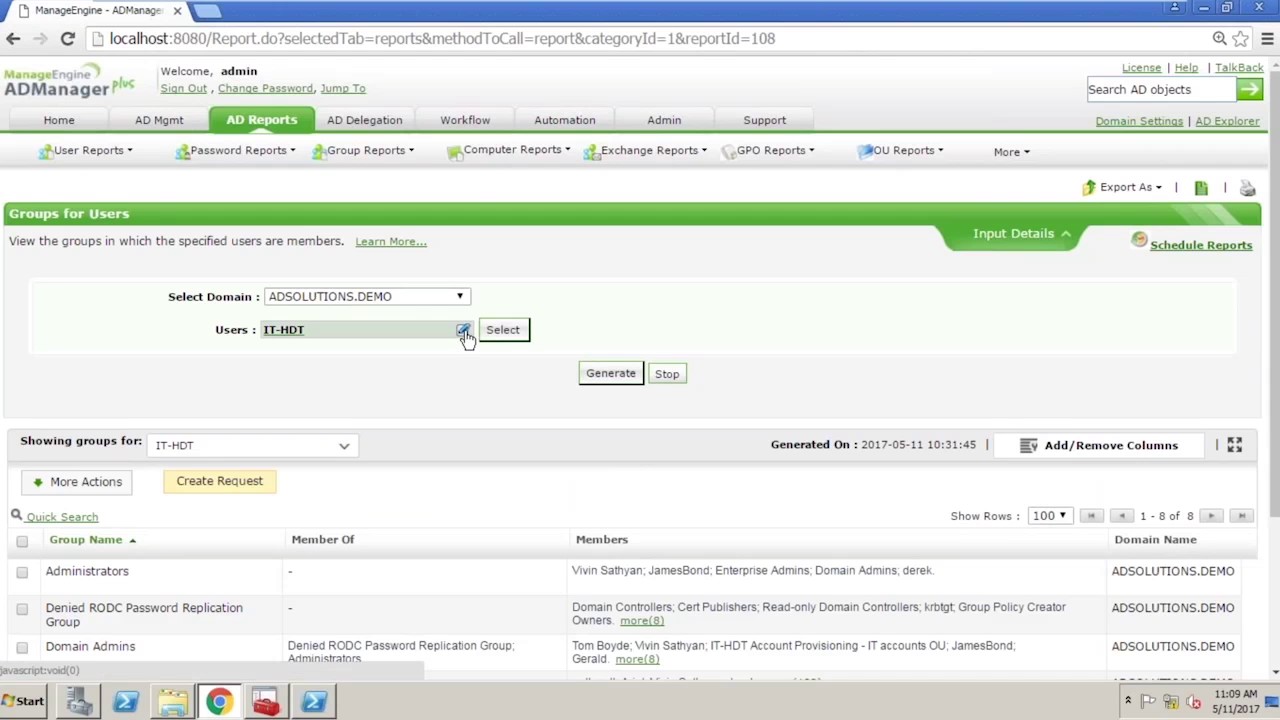
- Use cases: Stop ransomware, brute force attacks, and more
- In-depth incident reports and alerts with EventLog Analyzer
- Customizing attack patterns to reduce false positives