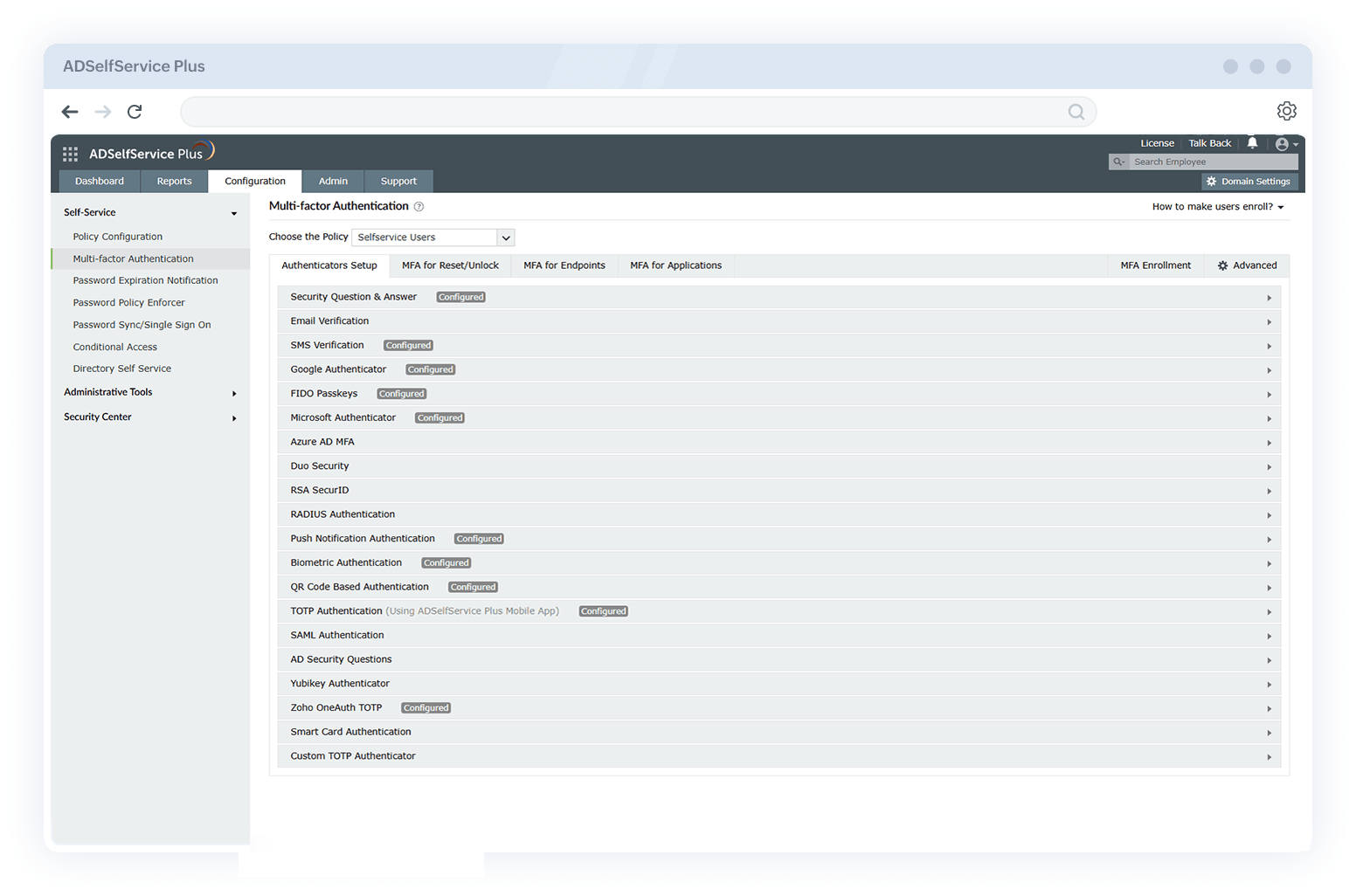
Active Directory MFA that powers up your cyber protection
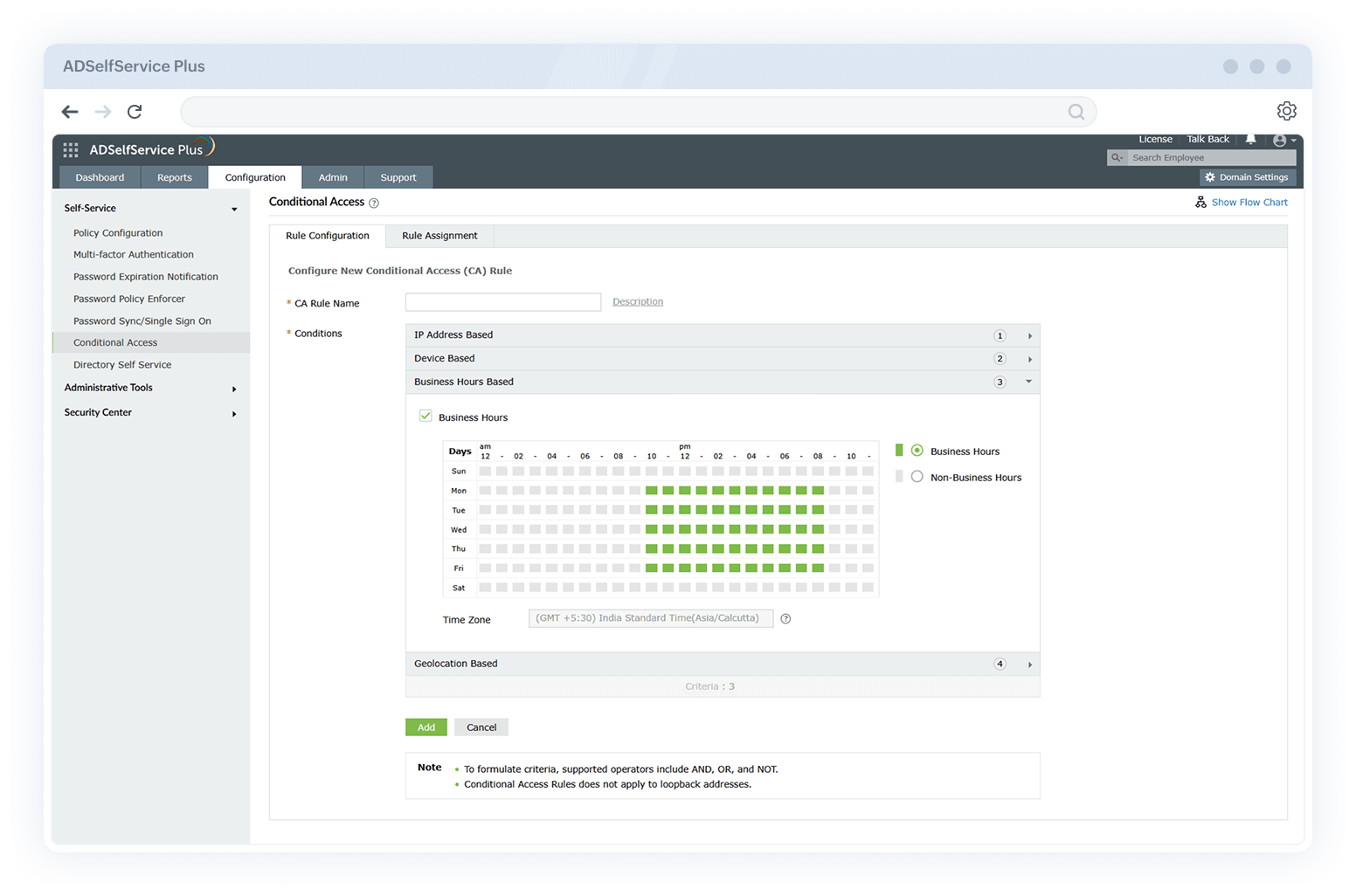
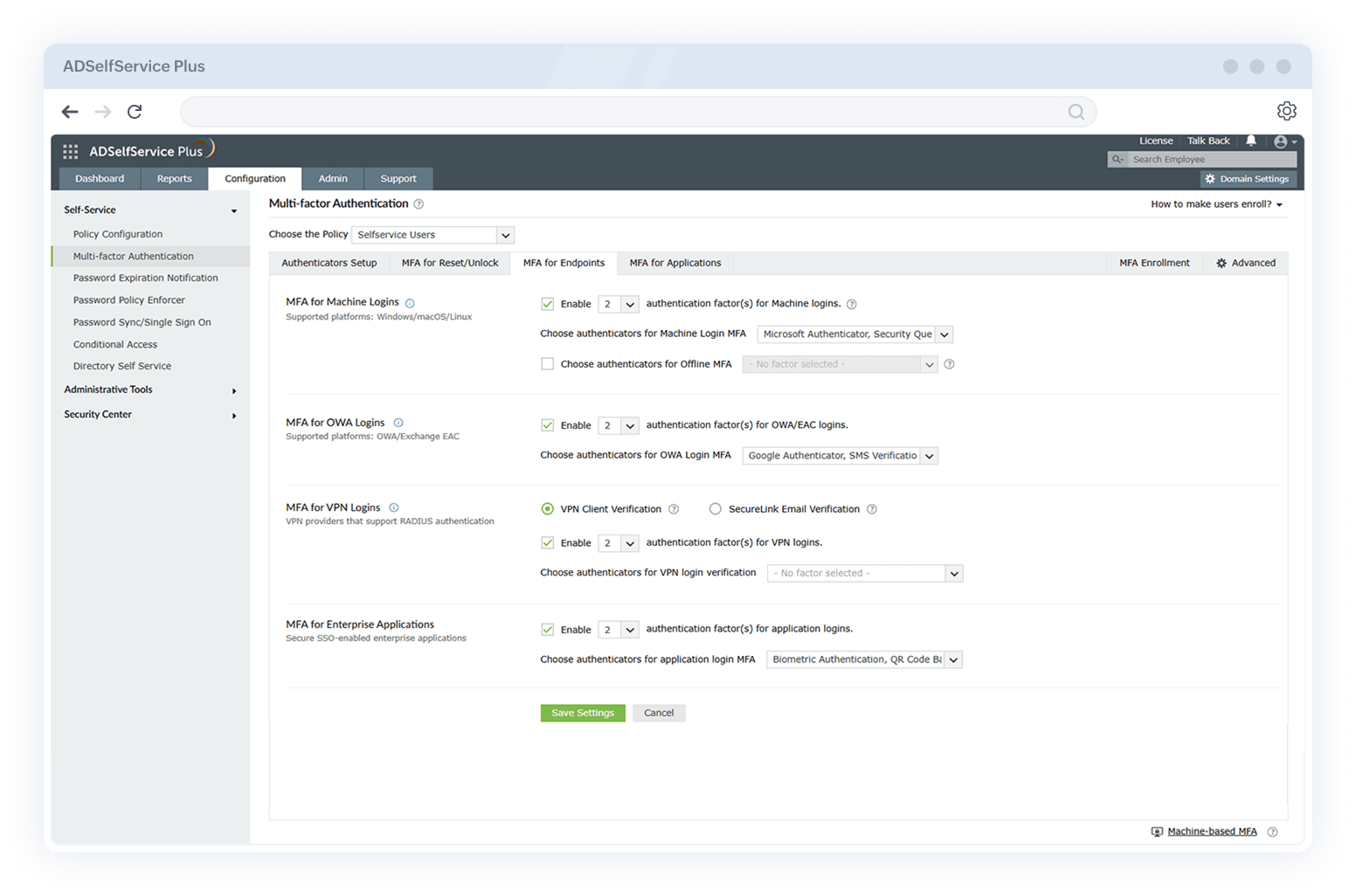
Implementing multi-factor authentication (MFA) for Active Directory user identities reduces the attack surface across your network and protects your business by requiring a higher level of identity assurance. With ManageEngine ADSelfService Plus, you can effortlessly deploy MFA for Active Directory, securing all users and systems across both cloud and on-premises applications and endpoints while strengthening your overall security posture.