How to configure SSO for Microsoft 365 (previously Office 365)
ADSelfService Plus supports AD-based SSO for Microsoft 365 and any other SAML-enabled application. Upon enabling Microsoft 365 SSO in ADSelfService Plus, all users have to do is simply log in to ADSelfService Plus' end-user portal. Once logged in, users can securely access Microsoft 365 and all supported SAML applications in one click, without having to reenter their username and password each time.
Benefits of implementing AD-based SSO for Microsoft 365 with ADSelfService Plus
Reduce password fatigue
Relieve users from having to remember different usernames and passwords for each enterprise application.
Streamline application access
Enable one-click access to all applications from a single portal.
Increase user adoption rate of applications
Increase usage of applications by making them readily available in a unified location.
ADSelfService Plus supports both identity-provider (IdP)-initiated and service-provider (SP)-initiated SAML SSO for Microsoft 365.
IdP-initiated SSO for Microsoft 365
- Users log in to the ADSelfService Plus end-user portal.
- From the ADSelfService Plus self-service portal, they can click the Office 365 icon in the Applications dashboard.
SP-initiated SSO for Microsoft 365
- Users can access their Microsoft 365 domain via a URL or bookmark.
- They will automatically be redirected to ADSelfService Plus' portal for login.
- Once they've signed in, they'll be automatically redirected and logged in to the Microsoft 365 portal.
SAML SSO configuration for Microsoft 365
Before you begin
Note:
- SSO can be enabled only for domains that are verified in Azure AD.
- SSO cannot be enabled for onmicrosoft.com domains that are created by Microsoft.
- SSO cannot be enabled for the default domain (the primary domain in which users are created). It can only be configured for custom domains. Microsoft 365 prohibits SSO configuration for default domains to ensure that administrators can log in to Microsoft 365 regardless of issues with the IdP. If your organization does not have a custom Microsoft 365 domain, you need to purchase one in order to configure SSO.
- Federated domains, i.e., domains in which SSO has been enabled, cannot be configured for password synchronization.
- Download and install ADSelfService Plus if you have not already.
- Link Microsoft 365 and on-premises AD user accounts:
- Using Azure AD Connect
- GUID as sourceAnchor: If you have Azure AD Connect, then use it to update the sourceAnchor attribute in Microsoft 365 with the GUID attribute value in AD.
- Another unique AD attribute as sourceAnchor: If you have already assigned a different attribute value other than GUID for the sourceAnchor attribute, then use the Account Linking option in ADSelfService Plus to map it with the corresponding attribute in AD.
- Using a third-party tool to convert GUID to ImmutableID
- Convert GUID to ImmutableID: If you don’t have Azure AD Connect, then you can download a third-party tool to convert GUID to ImmutableID. Use the tool to convert the GUID value of each user to ImmutableID values and update them in Microsoft 365.
- Update the ImmutableID value in Microsoft 365: Once you have converted the GUID to ImmutableID, you need to update the value in Office 365 for each user using the PowerShell commands given below.
- Command to update ImmutableID attribute while creating new users
$cred = Get-Credential
Connect-MsolService -Credential $cred
New-MsolUser -UserPrincipalName "user01@mycompany.com" -ImmutableId
"<immutable_id>" -DisplayName "user 01" -FirstName "user" -LastName "01"
-LicenseAssignment "<service_pack>" -UsageLocation "<location>" Note: You can check whether the update was successful using this command: Get-MsolUser -All | select userprincipalname,ImmutableId
- Command to update ImmutableID attribute for existing users
Set-Msoluser -UserPrincipalName "<user_mailID>" -ImmutableID “ <immutable_id> ”
- Reconfigure or update SSO settings
- If you are already using SSO for Microsoft 365 from another IdP or want to update ADSelfService Plus SSO settings, then you must first disable SSO in Microsoft 365. Once that has been done, disable SSO in Microsoft 365 by executing the command given below using PowerShell, and replacing the items with information specific to your setup:
$dom = "mycompany.com"
Set-MsolDomainAuthentication -DomainName $dom -FederationBrandName
$dom
-Authentication Managed
Configuring your AD domain in ADSelfService Plus
With ADSelfService Plus, you can use the existing AD credentials of users as well as other advanced authentication techniques for SSO authentication like biometrics, YubiKey, Google Authenticator, and more. To use the existing AD credentials for SSO authentication, you first need to configure an AD domain in ADSelfService Plus to enable SAML SSO for Microsoft 365.
ADSelfService Plus will automatically add all the domains that it can discover in your network. If your domains are automatically added, skip to step 9; otherwise, follow the steps 1-8 to add them manually.
- Launch the ADSelfService Plus web console and log in using admin credentials.
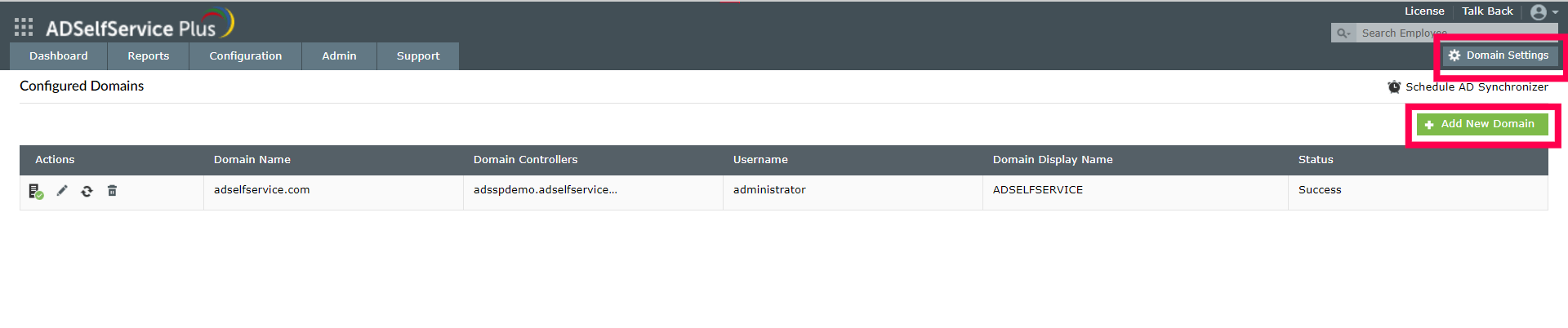
- Click the Domain Settings link available on the top-right corner of the application and select Add New Domain.
- An Add New Domain window will appear.
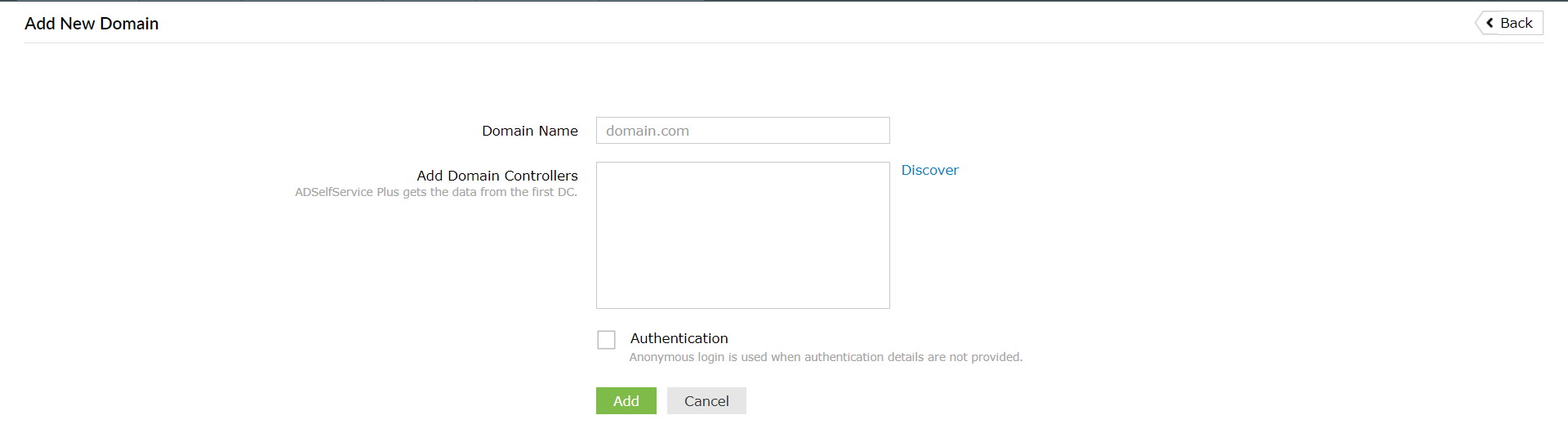
- In the Domain Name field, enter the name of the domain you want to add.
- In the Add Domain Controllers field, click Discover. ADSelfService Plus will try to automatically discover the domain controllers associated with the domain.
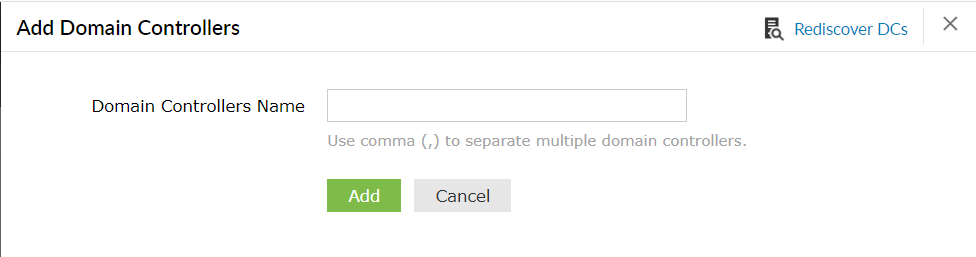
- If the domains are not auto-discovered, then in the pop-up screen, enter the domain controller name in the field provided, and click Add.
- You can leave the authentication fields empty if you are not going to use the end user self-service features of ADSelfService Plus.
- Back in the Add New Domain window, click Add to finish adding the domain in ADSelfService Plus.
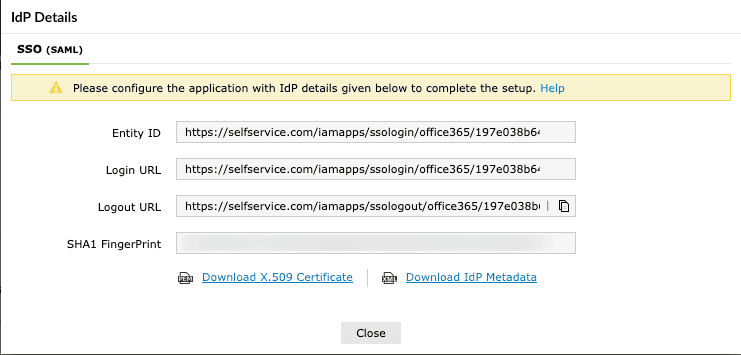
Getting the SAML details from ADSelfService Plus
- Navigate to the Configuration > Password Sync/Single Sign On > Add Application.
- Select Office 365/Azure in the list of applications provided.
- Click IdP Details in the top-right corner of the screen.
- In the pop-up that appears, copy the Login URL and download the SSO certificate by clicking Download Certificate.
Configuring SSO settings in Microsoft 365
- Open PowerShell with admin rights.
- Enter the following command:
$cred = Get-Credential
- In the pop-up that appears, enter the username and password of your Microsoft 365 administrator account.
- Connect with MsolService using the following command:
Connect-MsolService -Credential $cred
- Now, get a list of your Microsoft 365 domains by entering the following command:
Get-MsolDomain
- Enter the domain for which you would like to enable SSO:
$dom = "mycompany.com"
- Enter the login URL value from Step 13 for the $url and $uri commands and the logout URL value for the $logouturl command.
$url = "<login URL value>"
For example, $url =
"https://selfservice.com:9251/iamapps/ssologin/office365/
1352163ea82348a5152487b2eb05c5adeb4aaf73"
$uri = "<login URL value>"
For example, $uri =
"https://selfservice.com:9251/iamapps/ssologin/office365/
1352163ea82348a5152487b2eb05c5adeb4aaf73"
$logouturl = "<logout URL value>"
For example, $logouturl =
"https://selfservice.com:9251/iamapps/ssologout/office365/
1352163ea82348a5152487b2eb05c5adeb4aaf73"
- Now copy the SSO certificate file content from Step 13 and pass it as the value for the following command:
Important: Please edit the file so that there aren’t any new lines before pasting the content into the file.
$cert = "MIICqjCCAhOgAwIBAgIJAN..........dTOjFfqqA="
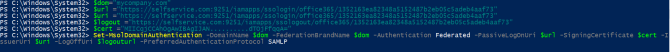
- Next, run the following command to enable SSO in Microsoft 365:
Set-MsolDomainAuthentication -DomainName $dom -FederationBrandName $dom -Authentication Federated -PassiveLogOnUri $url -SigningCertificate $cert -IssuerUri $uri -LogOffUri $logouturl -PreferredAuthenticationProtocol SAMLP
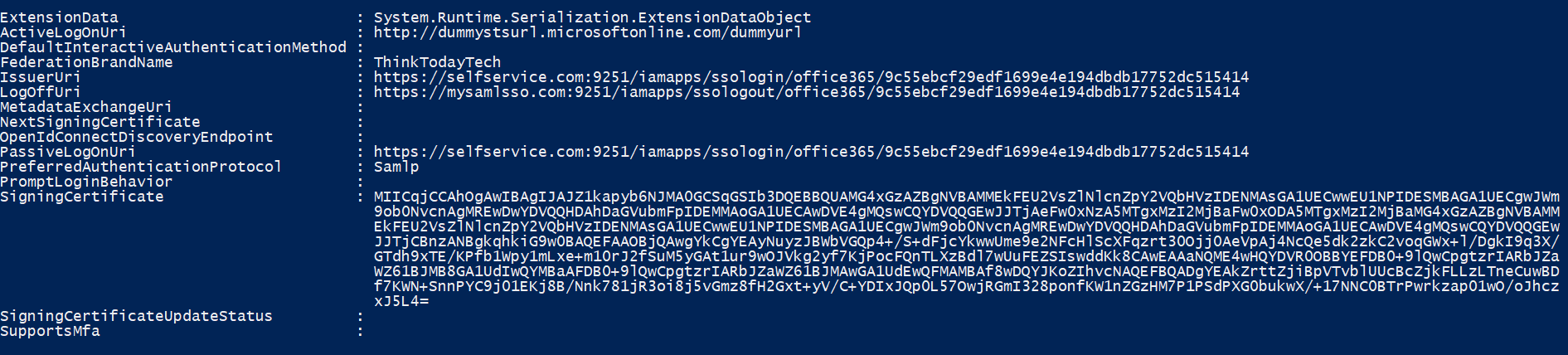
- Test the configuration by using the following command:
Get-MSolDomainFederationSettings -DomainName "mycompany.com" | Format-List *
Adding your Microsoft 365 SSO setup in ADSelfService Plus
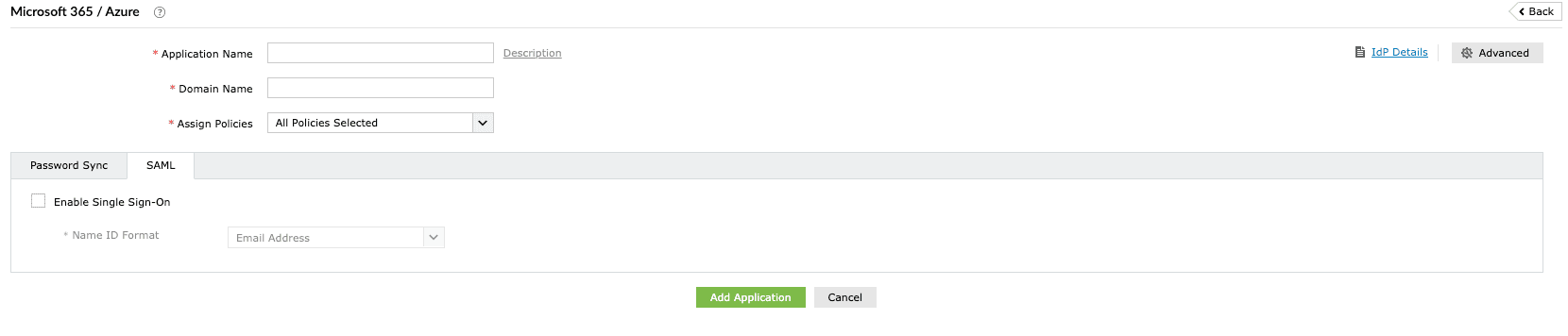
- Now, switch to ADSelfService Plus’ Microsoft 365 SSO configuration page.
- Check the box next to Enable Single Sign-On.
- In the Domain Name field, enter the domain name you used in Step 18.
- Provide an appropriate description in the Description field.
- In the Assign Policies field, click the drop-down box and select the policies for which you wish to enable SSO. The policy you select will determine which users have the SSO feature enabled.
Note: ADSelfService Plus allows you to create OU- and group-based policies for your AD domains. To create a policy, go to Configuration > Self-Service > Policy Configuration > Add New Policy. Click Select OUs/Groups, and make the selection based on your requirements. You need to select at least one self-service feature. Finally, click Save Policy.
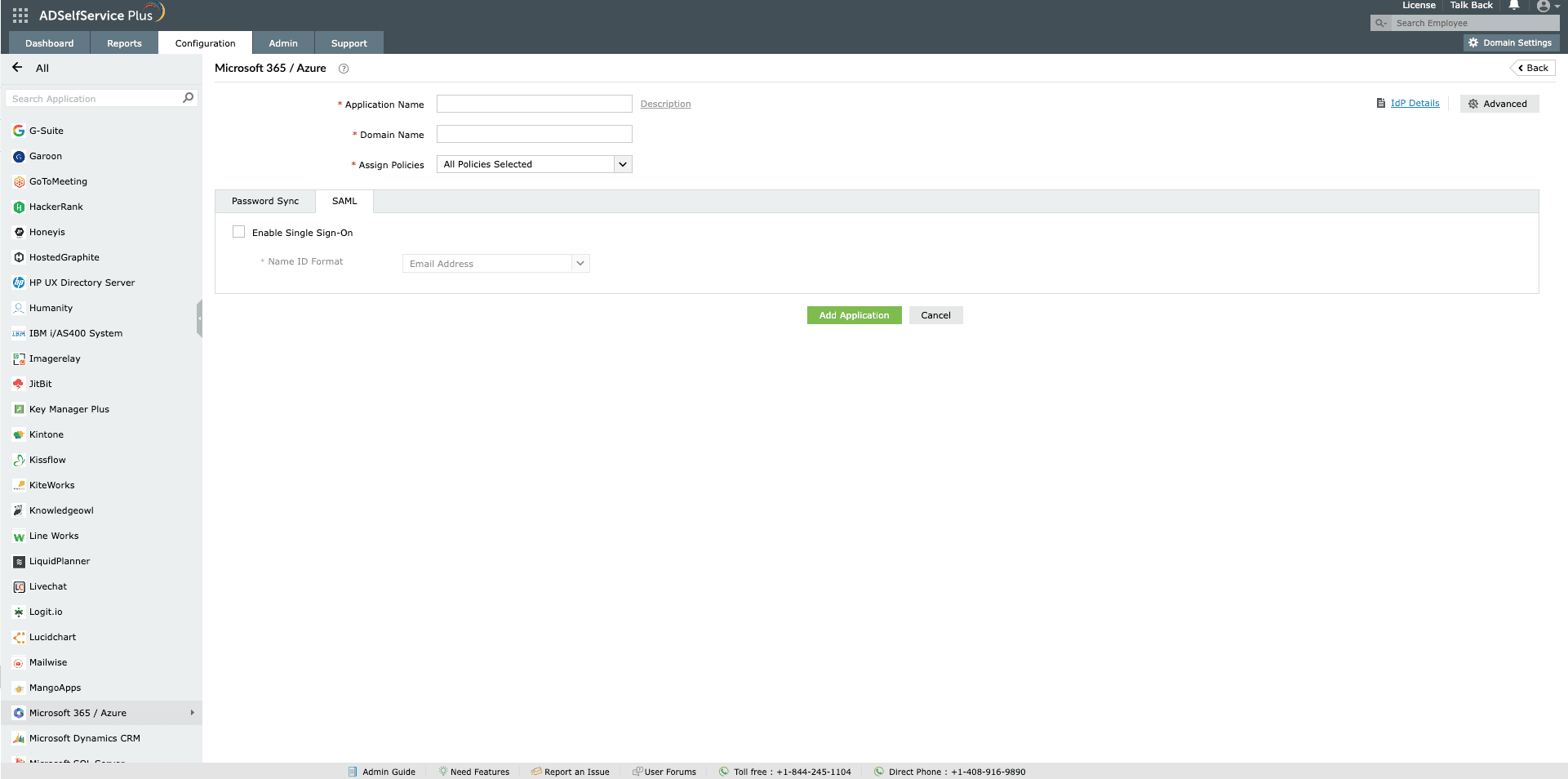
- Click Add Application.
Now users can log in to their Microsoft 365 accounts automatically without having to enter their username and password again.
Once SSO is set up, users only need to authenticate once, then they can log into their Microsoft 365 accounts automatically without having to enter their username and password each time.
Unify access to cloud and on-premises applications with SAML SSO
Highlights
Free Active Directory users from attending lengthy help desk calls by allowing them to self-service their password resets/ account unlock tasks. Hassle-free password change for Active Directory users with ADSelfService Plus ‘Change Password’ console.
Get seamless one-click access to 100+ cloud applications. With enterprise single sign-on, users can access all their cloud applications with their Active Directory credentials. Thanks to ADSelfService Plus!
Intimate Active Directory users of their impending password/account expiry by mailing them these password/account expiry notifications.
Synchronize Windows Active Directory user password/account changes across multiple systems, automatically, including Office 365, G Suite, IBM iSeries and more.
Ensure strong user passwords that resist various hacking threats with ADSelfService Plus by enforcing Active Directory users to adhere to compliant passwords via displaying password complexity requirements.
Portal that lets Active Directory users update their latest information and a quick search facility to scout for information about peers by using search keys, like contact number, of the personality being searched.