It's time to go beyond a defensive stance and adopt a proactive outlook.
Security breaches are no longer a question of if, but when. To have any chance of minimizing their impact, organizations must be prepared to detect and respond to them at the earliest. With its extensive threat hunting capabilities, ManageEngine Log360 hands you the power to strike first.
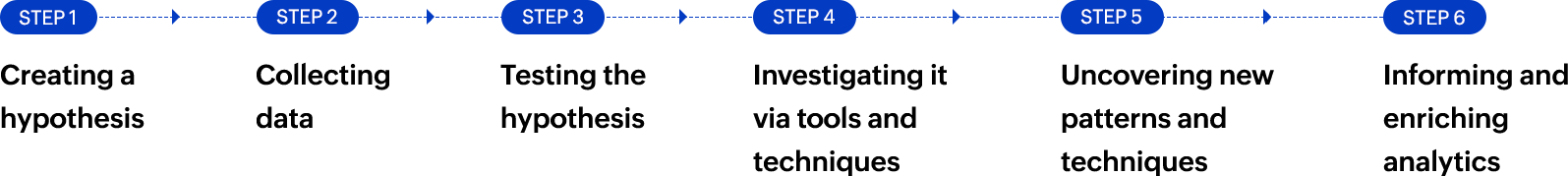
High-speed search analytics
Search through the length and breadth of your logs
A high-speed, flexible, and easy-to-use search tool that lets you build queries in SQL to search through your entire log bucket in a matter of seconds.
- Get quick results: Quickly sift through your log data with a processing speed of 25,000 logs per second.
- Build queries flexibly: Go with basic or advanced options to build SQL queries. Perform wildcard, phrase, Boolean, or grouped searches and find answers quickly.
- Search for anything: Search for any field and any value. Extract new fields and find them in log data through RegEx matching.
- Save your progress: Save your search parameters so you don't have to repeat the process all over.
- Set up real-time alerts: Ensure you get notified when threat patterns repeat in your network.
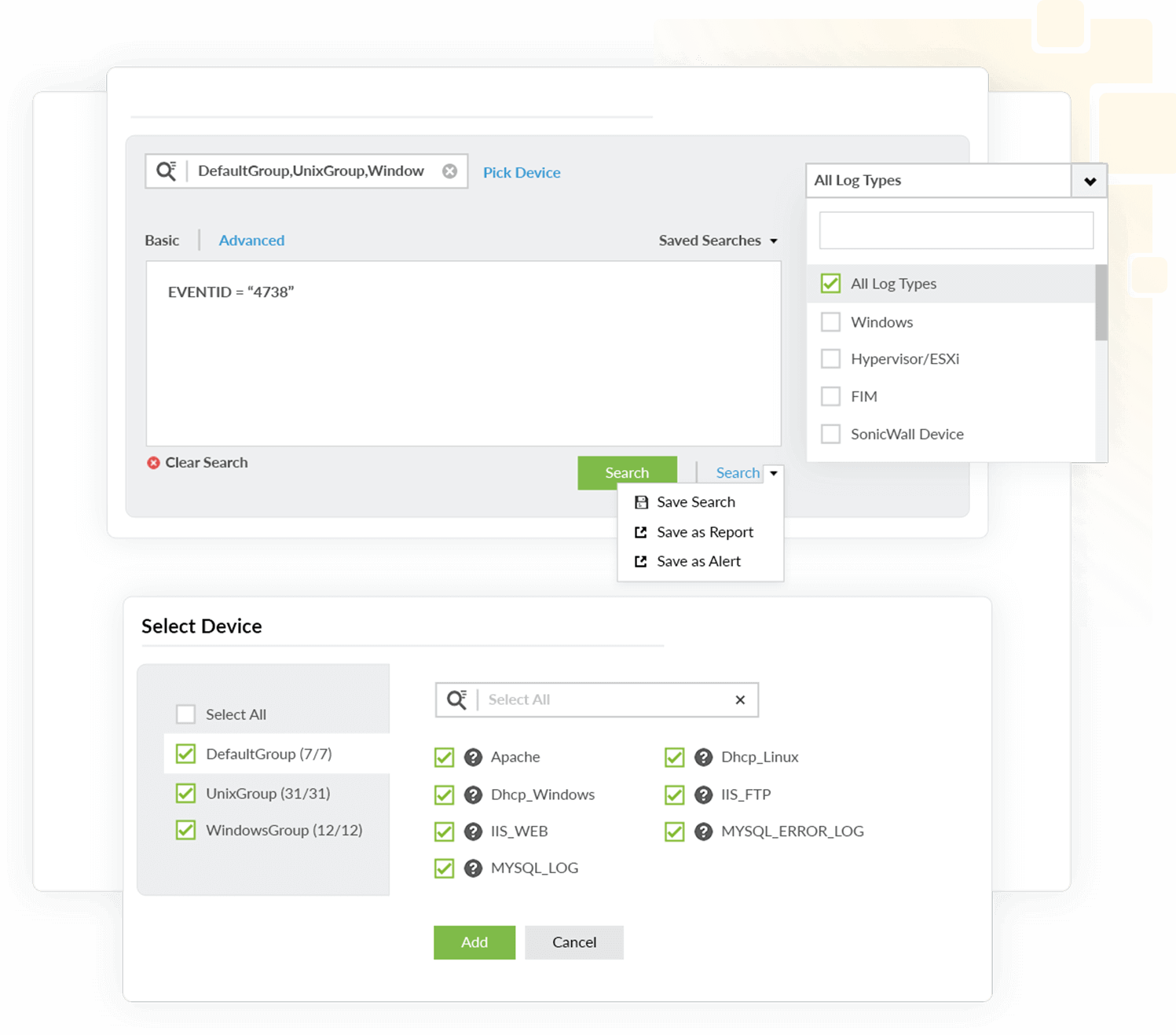
User and entity behavior analytics (UEBA)
Anticipate malicious activity in advance with watch lists An ML-based module, UEBA constantly learns users' behavior patterns and flags down unusual activities and suspicious behaviors as anomalies. Based on the anomalies, it assigns risk scores to users and entities in your network. UEBA leverages this information in these ways.
- Detect and watchlist high-risk entities: Log360 watchlists high-risk entities based on their risk scores, which are in turn based on real-time actions.
- Send real-time alerts: Log360 notifies security admins through email or SMS when the risk score of an individual entity crosses a set threshold.
- Construct detailed timelines: Log360 extracts information from logs to construct detailed timelines that give visibility into who did what, when, and where.
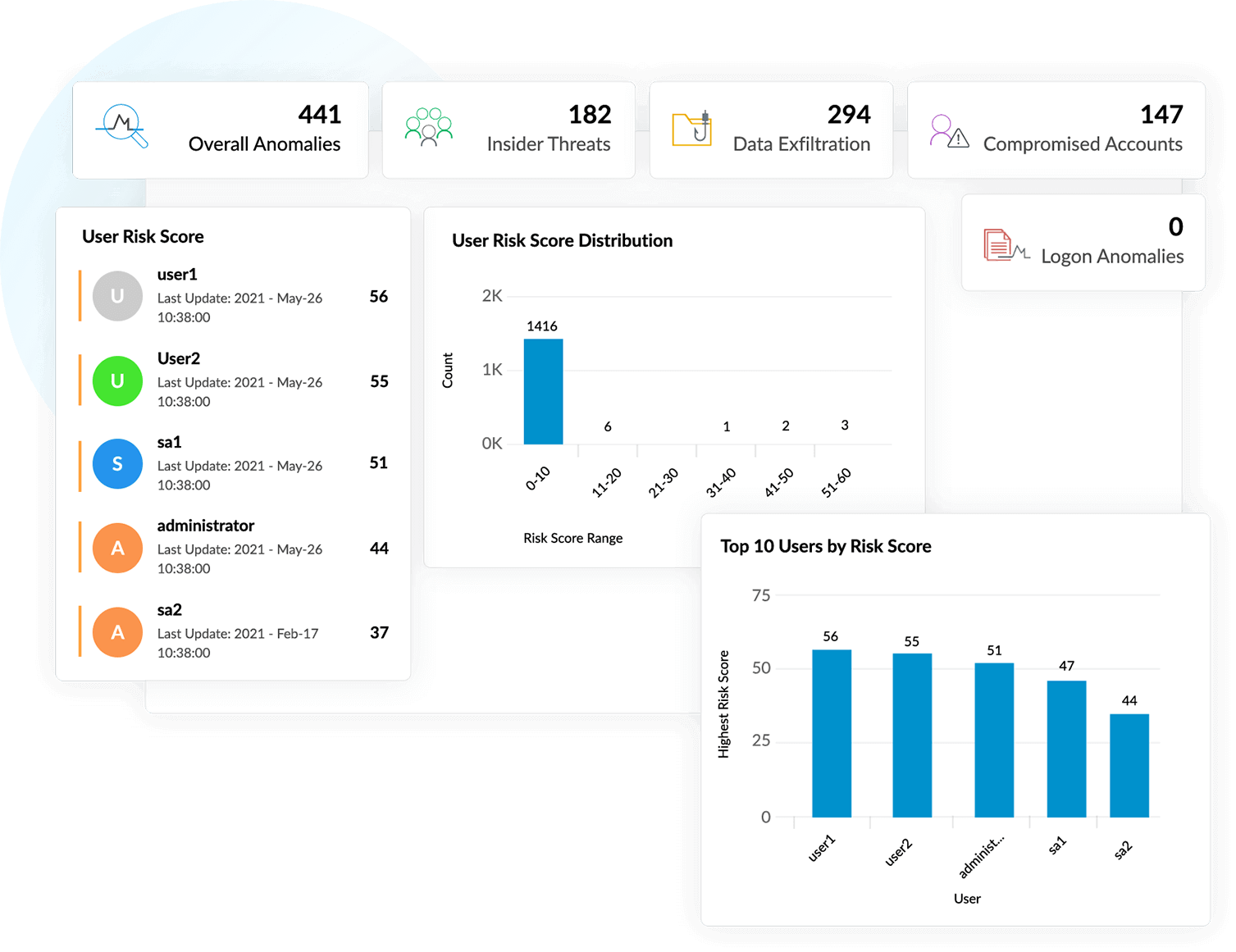
Why choose Log360 for threat hunting?
Equip your threat hunting team with everything they need.
Sign up for a demo nowCollect Collect logs from your entire network.
Analyze Search for anything in your logs and discover threat patterns.
Record Save discovered threats in searches as reports for future reference..
Respond Use automated workflows to respond immediately.
Detect Set up alerts to ensure you don't miss out on discovered threats in the future.
Investigate Use detailed timelines to know what happened when and where.
Resolve Resolve the incident with the help of the built-in console.