Certificates
The macOS AD certificate policy allows admins to distribute certificates to devices in bulk, while leveraging the Active Directory credentials of Users. This simplifies certificate association, while ensuring the devices are secured.
The following details need to be provided, to configure an AD certificate policy:
Note:
Information about the Certificate Authority, certificate renewal, and similar details concerning the certificate need to be obtained from the Vendor itself. MDM will then use these details to simplify certificate management using the policy.
Profile Description
Policy Name
Specify a display name.
Server URL
Specify the URL of the Certificate Authority from where the certificate is purchased or obtained. It can be in this format: https://<ndes_fqdn>/certsrv
CA Name
Specify the name of the Certificate Authority. To check the name of the Certificate Authority, follow these steps:
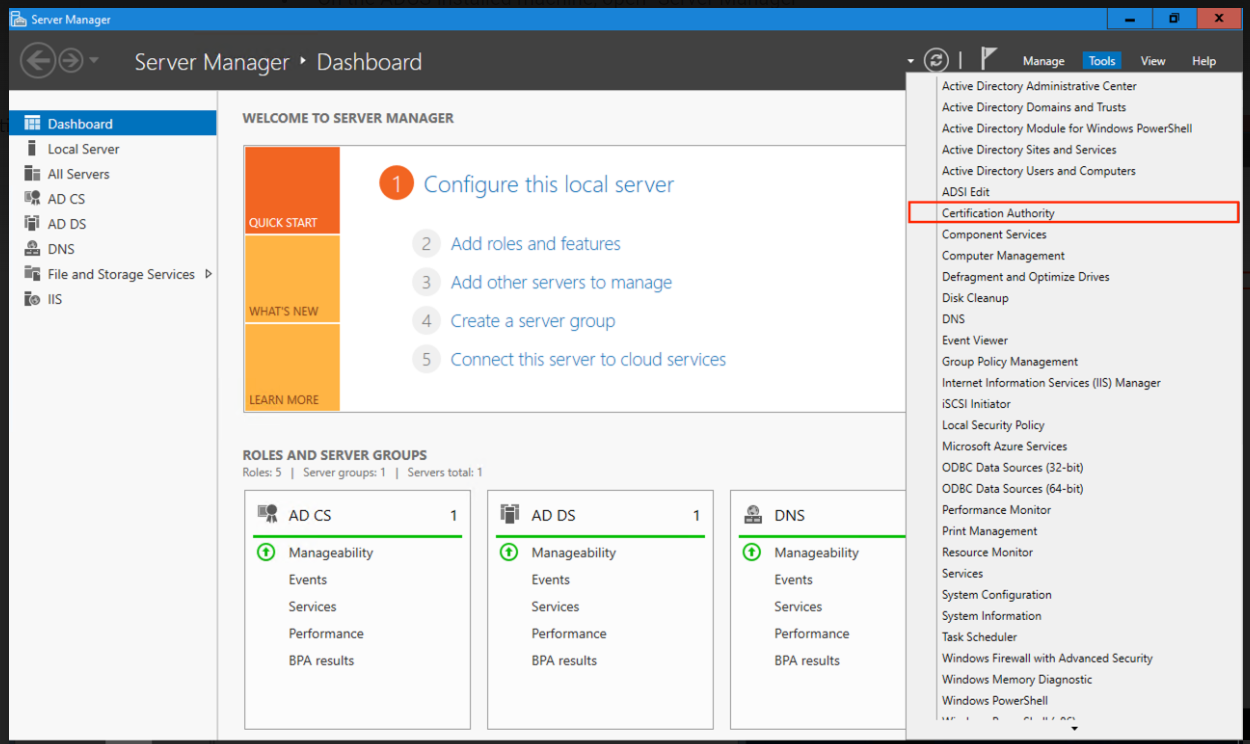
- On the ADCS-installed machine, open "Server Manager".
- On the top right, click "Tools" and from the drop-down, select "Certification Authority".
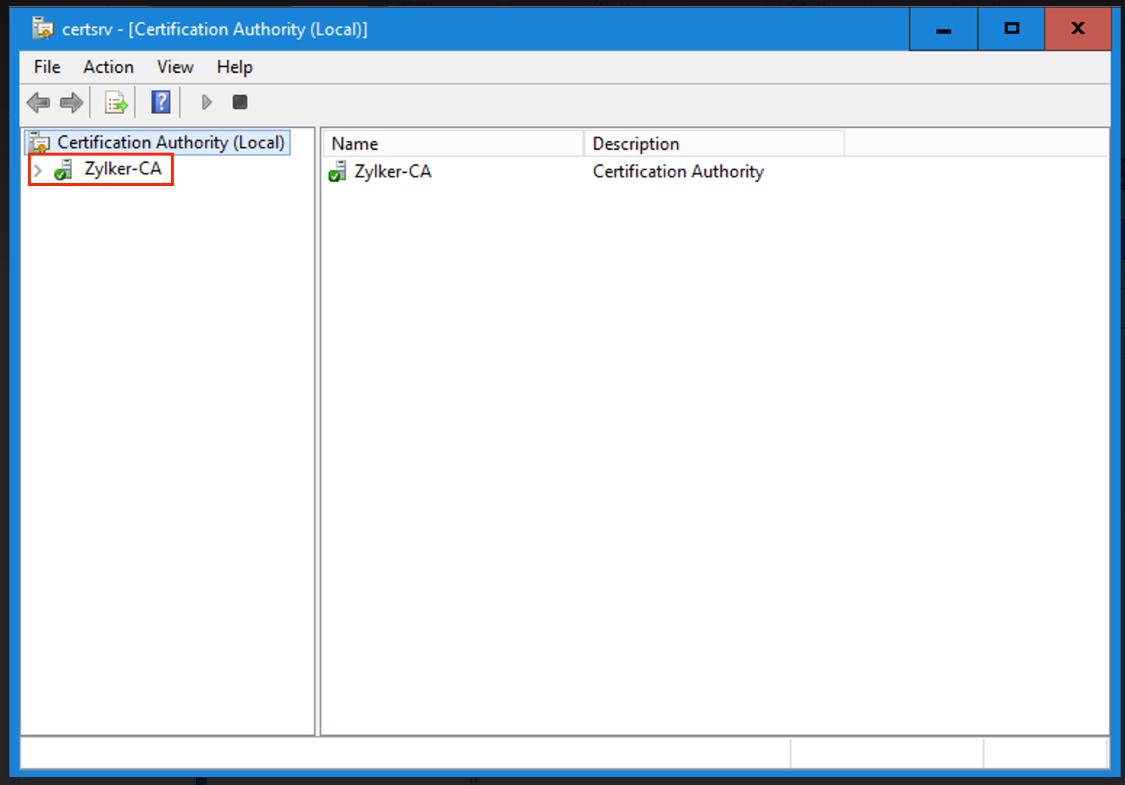
- Next, on the "Certification Authority" window, we could see the CA name.
Certificate Template Name
Provide any name for the template that MDM will assign this policy to. To check the name of the Certificate Template Name, follow these steps:
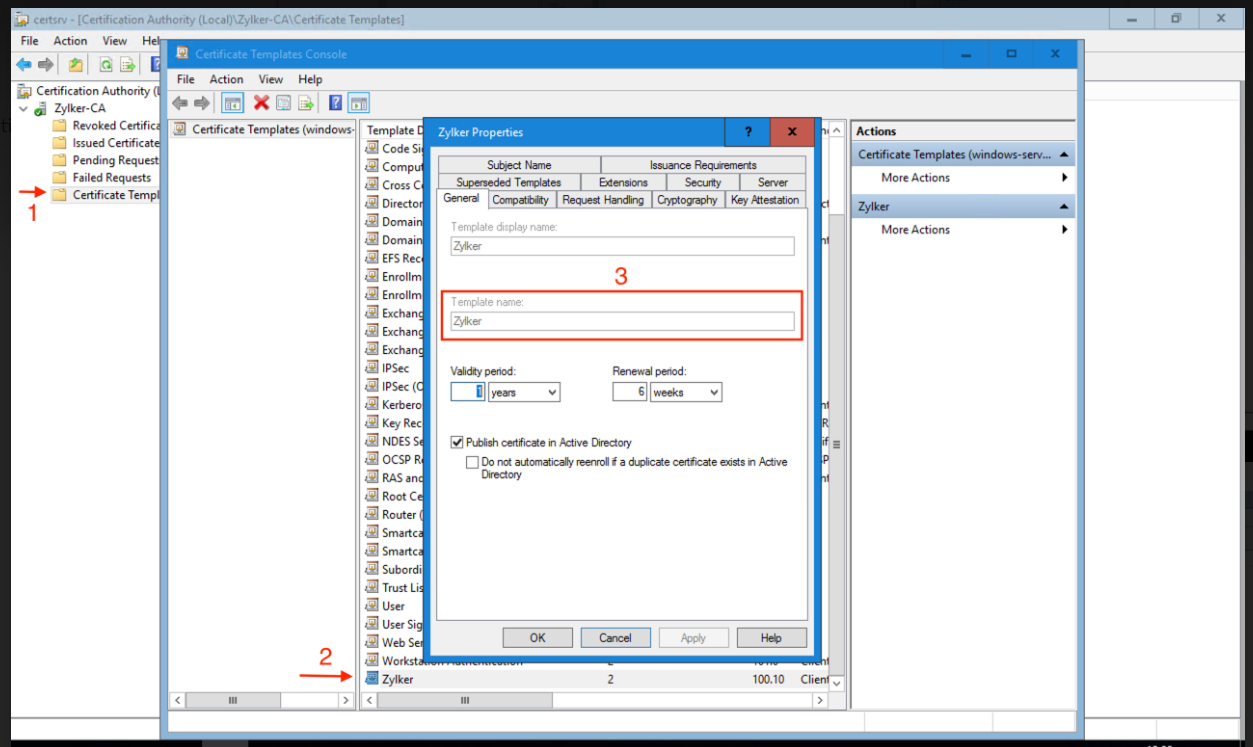
- On the ADCS-installed machine, open "Server Manager".
- On the top right, click "Tools" and from the drop-down, select "Certification Authority".
- On the "Certification Authority" window, right-click on the "Certificate Templates" and select "Manage".
- On the "Certificate Templates Console" window, we could find a list of available certificate templates.
- Right-click on the correct certificate template and select "Properties".
- Go to the "General" tab, and copy the "Template" name (not the Template display name).
- And provide this Template name in MDM.
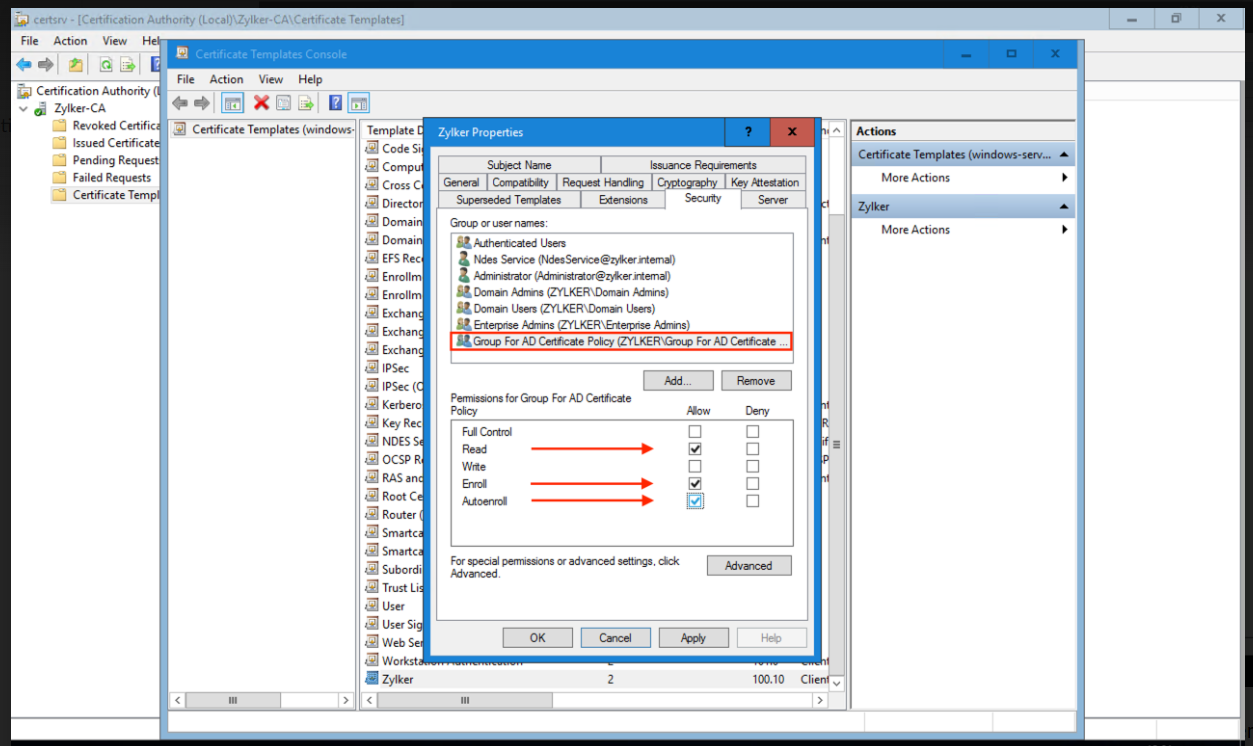
Note: On the "Certificate template properties pop-up", go to "Security" and ensure that the necessary computer groups are added and "Read, Enroll, Auto-Enroll" permissions are provided.
Interval to Renew Certificates
Enter the number of days in advance of certificate expiration that the notification center notifies the user. Negative values are not accepted.
Certificate Key Size
Enter the RSA key size for the certificate signing request. To verify details about the certificate's key size, check the details provided on the certificate. For more information about the certificate, contact the Vendor/CA.
Private Key Export from Keychain
Allows/Restricts exporting the Private Key from the Keychain.
Third Party Apps Accessing the Associated Private Key
Allows/Restricts Third Party Apps to access the Private Key.
