How to secure communication of roaming users using Secure Gateway Server?
Description
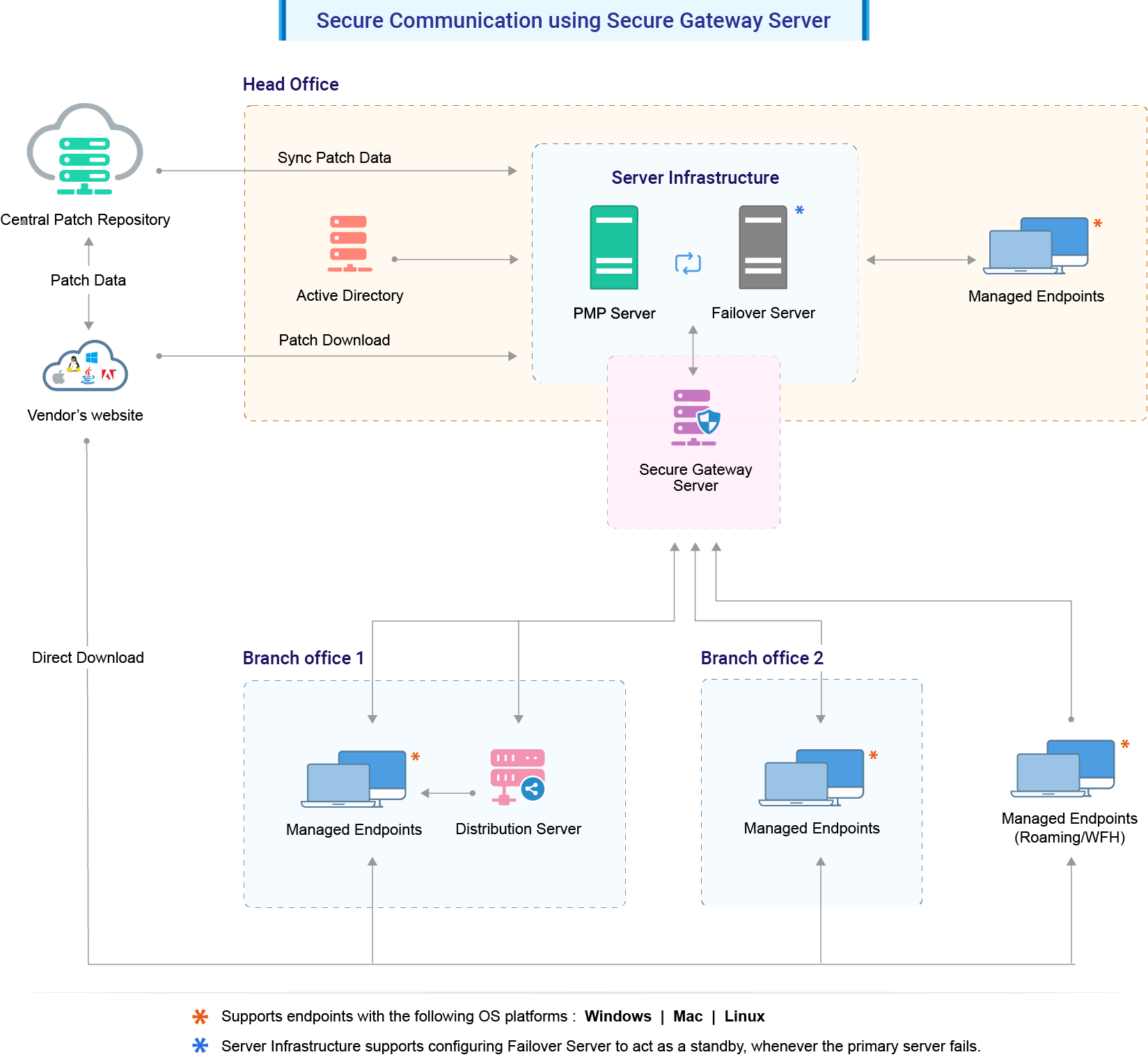
This document will explain you the steps involved in securing the communication of roaming users using Secure Gateway Server component. Secure Gateway server can be used when roaming agents (on the roaming users' devices and desktops) access the server through internet. It prevents the exposure of Central Server directly to the internet by serving as an intermediate between the Central server and roaming agents. This ensures that the Central Server is secure from risks and threats of vulnerable attacks.
How Secure Gateway Server works?
The Secure Gateway server is a component that will be exposed to the internet. This Secure Gateway server acts as an intermediate between the managed roaming agents and the Central server. All communications from the roaming agents will be navigated through the Secure Gateway server. When the agent tries to contact the Central server, Secure Gateway server receives all the communications and redirects to the Central Server.
Note: Map your Secure Gateway server and Central server IP address to common FQDN in your DNS to minimize bandwidth consumption. For example, if your FQDN is "product.server.com", map this to both your Secure Gateway server and Central server IP address.
Hardware requirements for Secure Gateway Server
The hardware requirements for Secure Gateway Server include the following :
Processor : Intel Core i5(4 core/8 thread) 2.3 GHz. 6 MB cache
RAM size : 4 GB
Hard disk space: 5 GB
Steps
To introduce Secure Gateway server based communication to the central server, follow the steps given below:
- Modify Settings in Central Server
- Install and configure Secure Gateway server
- Infrastructure recommendations
Modify Settings
- Enter the Secure Gateway server's IP address instead of Central server IP address under Central server details while adding remote office. This is to ensure the WAN agents and DS communication to Secure Gateway server.
- Enable secured communication(HTTPS) under DS/WAN agent to Central server communication.
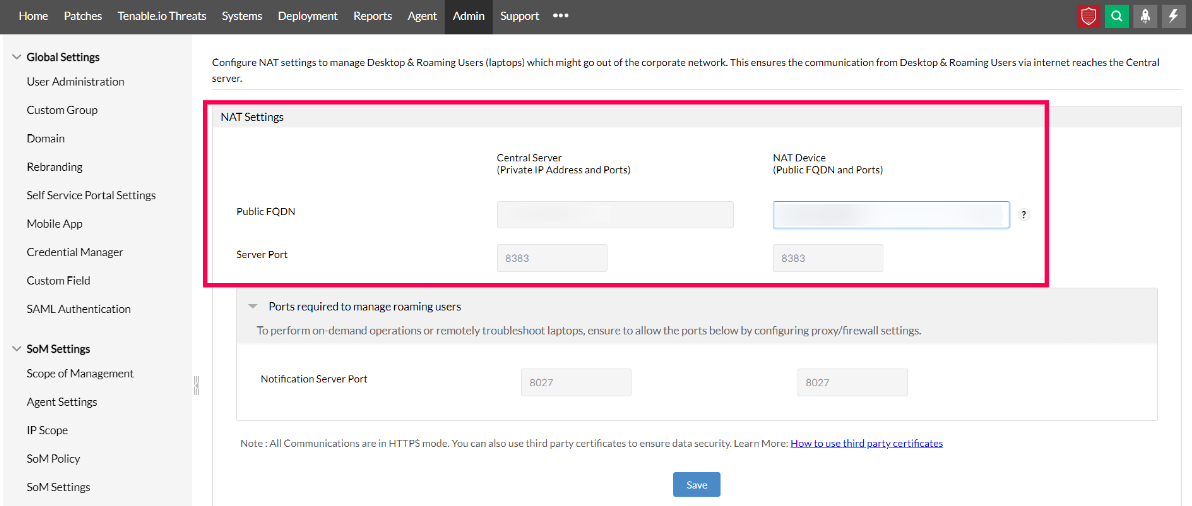
- Configure the NAT Settings using the Secure Gateway's public FQDN/IP address.
- On the Central Server Console, click on the Admin tab -> Server Settings -> NAT Settings.
- Add the FQDN of the Secure Gateway server against the Public FQDN under NAT Device as shown below.
Install and configure the Secure Gateway server
- Download and install the Secure Gateway server.
- Enter the following details under Setting up the Secure Gateway server window, which will open after the installation process
- Central Server Name: Specify the FQDN/DNS/IP address of the Central server
- Http Port: Specify the port number that the Secure Gateway server uses to contact the Central server (eg: 8020)
- Https Port: Specify the port number that the roaming users use to contact the Central server (eg: 8383 - it is recommended to use the same port 8383(HTTPS) for Central Server in secured mode)
- Notification Server port: 8027 (to perform on-demand operations), this will be pre-filled automatically
Infrastructure recommendations
Ensure that you follow the steps given below
- Configure the Secure Gateway server in such a way, that it should be reachable via public IP/FQDN address configured in NAT settings. You can also configure the Edge Device/Router in such a way that all the request that are sent to the Public IP/FQDN address gets redirected to the Secure Gateway Server.
- It is mandatory to use HTTPS communication
- You will have to ensure that the following port is open on the firewall for the WAN agents to communicate the Secure Gateway Server.
Port Type Purpose Connection 8383 HTTPS For communication between the WAN agent/Distribution Server and the server using Secure Gateway Server. Inbound to Server 8027 TCP To perform on-demand operations Inbound to Server
You have now secured communication between Central server, WAN agents and roaming users.