Decline Patch
Note: This feature is currently available for Windows and macOS. If you would like to decline patches on Linux systems as well, kindly let us know
Overview
Declining Patch is an important part of patch deployment. When you automate patch management, all the missing patches are downloaded and deployed to the target computers. This results in deploying patches even though they might not be business critical. So, you will have to choose to ignore patches which are not critical. Ignoring to install some of missing patches will reflect on the system's health status. Computers in your network might be rated as Highly Vulnerable, or Vulnerable.
Not all patches necessitate deployment. There are cases where certain patches have to be excluded from your deployment list. Declining a patch results in the following:
- When a patch is declined, it will not be considered as a missing patch.
- It will not be calculated for the system's health status.
- Patches that are declined will not be deployed via automated patch deployment.
You can choose to decline specific patches or all patches pertaining to a specific application. Patches can be declined to all computers or specific group of computers. A default group named, "All Computers Group" is created by Endpoint Central. If you wanted to decline a specific patch to all computers, then you can choose this group and decline the required patches. If you want some of the patches to be declined to a specific group of computers, then you can create separate custom groups like, groups based on OS, or Remote Office, etc. and decline the patches.
Here are a few examples of how decline patch works:
- Assume a specific patch "Adobe Acrobat Reader DC 2022.003" has been declined for a "All computers Group", then that patch will not be considered as missing patch and will not be downloaded in the network. Computers will not be considered as vulnerable, even if this patch is not installed.
- If a critical Patch "Chrome 23.1" is declined for specific custom groups, like custom group "Remote_Office1" and "Remote_Office2", then the patch will be downloaded and deployed to all the missing computers except for those computers in the mentioned custom groups. If this patch Chrome 23.1 is missing in any computer other than the specified custom groups, then those computers might be rated as vulnerable, since a critical patch is missing.
- When a computer is added to a custom group "Remote_Office1", all the patches that are declined to the custom group will be considered as declined to the newly added computer.
Note: Declining a patch will only prevent it from being deployed in future. It will not uninstall or remove the patch from endpoints where it has already been installed.
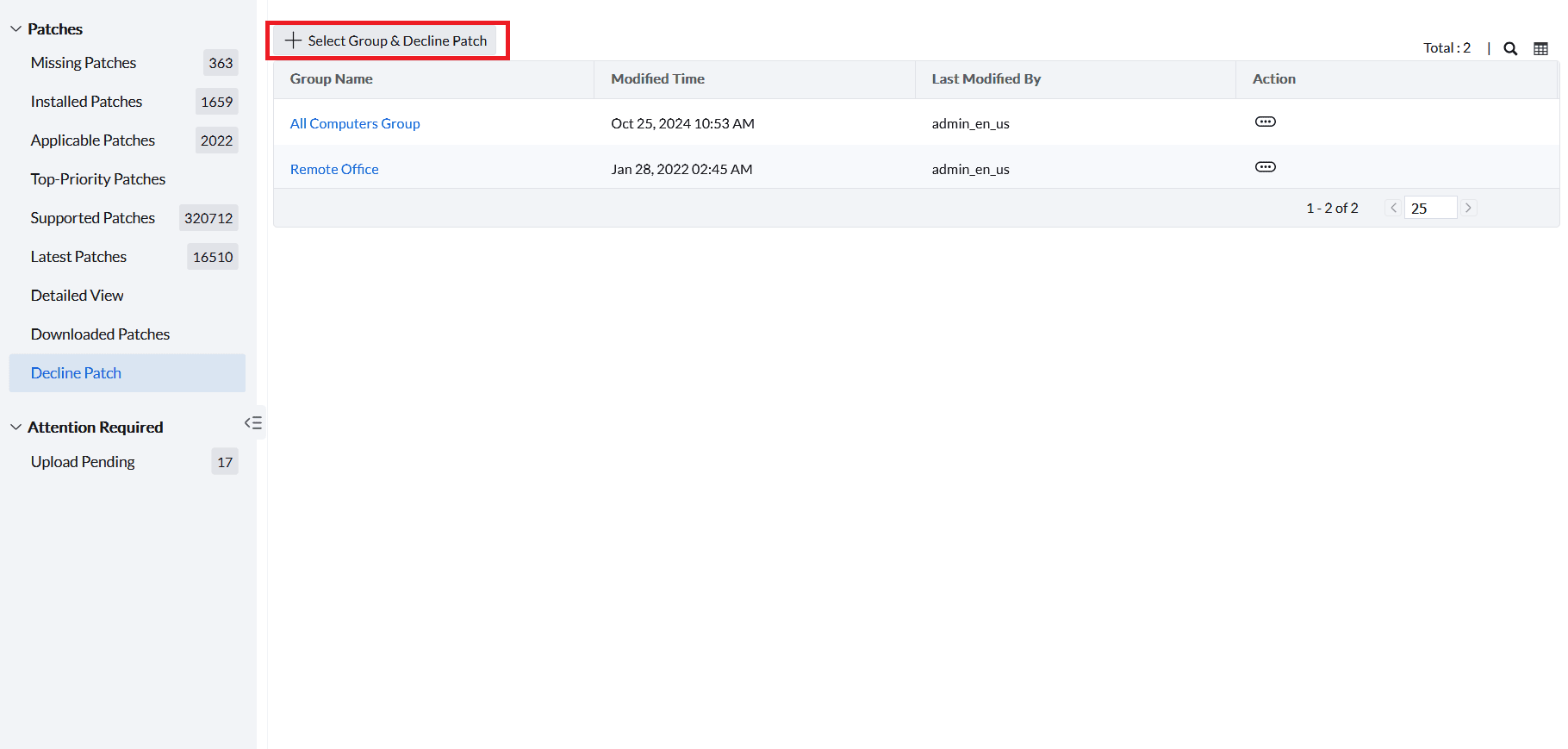
To decline patches, click on Patch Mgmt -> Decline Patch (or) Threats & Patches -> Patches -> Decline Patch and then click on Select Group & Decline Patch.
You will be redirected to the Select Group & Decline Patch window.
Choosing the Group
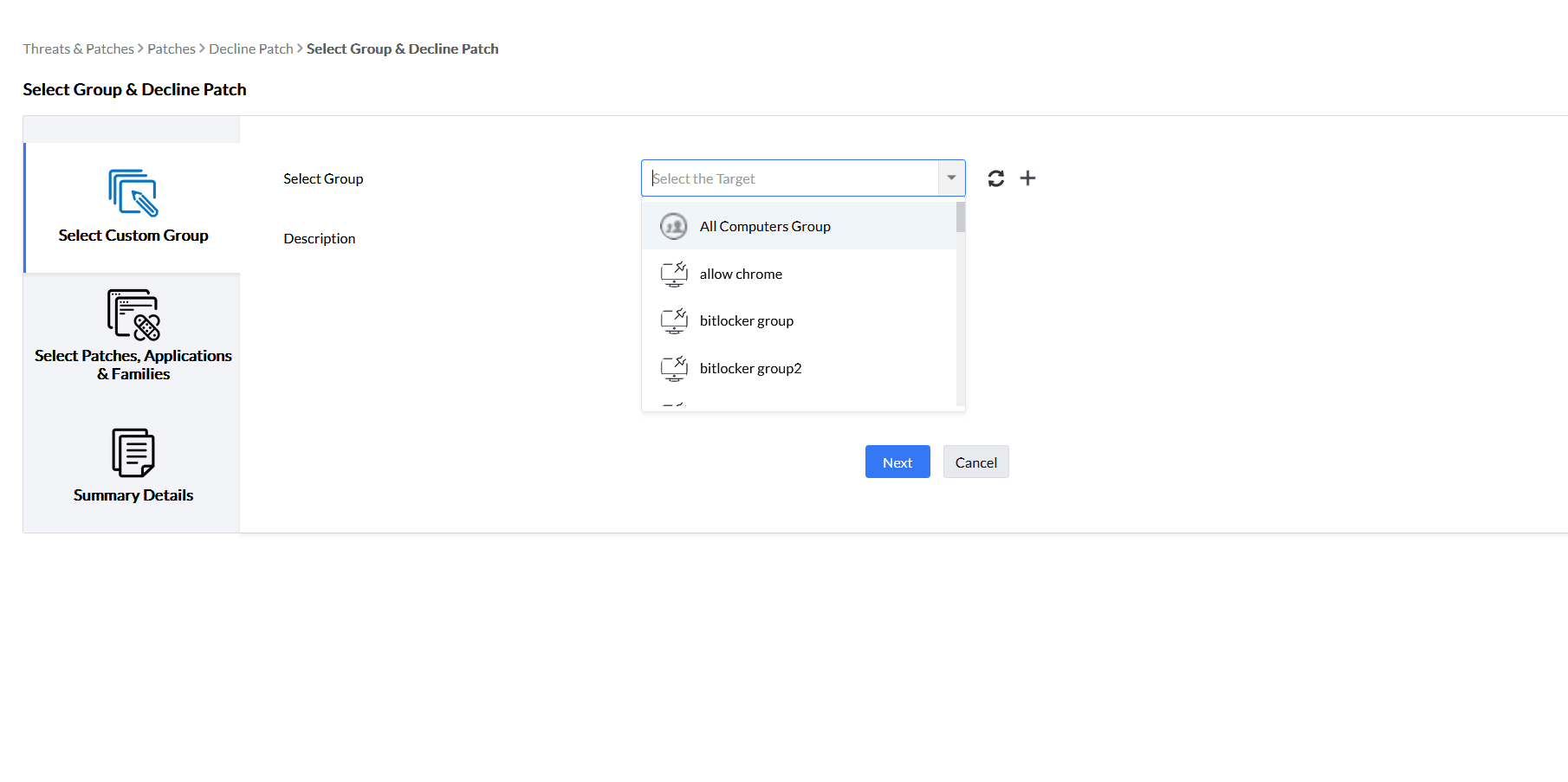
Under Select Custom Group section, choose All Computers Group if you wanted the patch to be declined for all the managed computers, else choose a specific group which contains the required target. Add Description if you want. And then click on Next.
Choosing the Patches, Applications or Families
Under Select Patches,Applications & Families section, you can choose the patches to be declined or the applications or the family of applications for which the patches need to be declined.
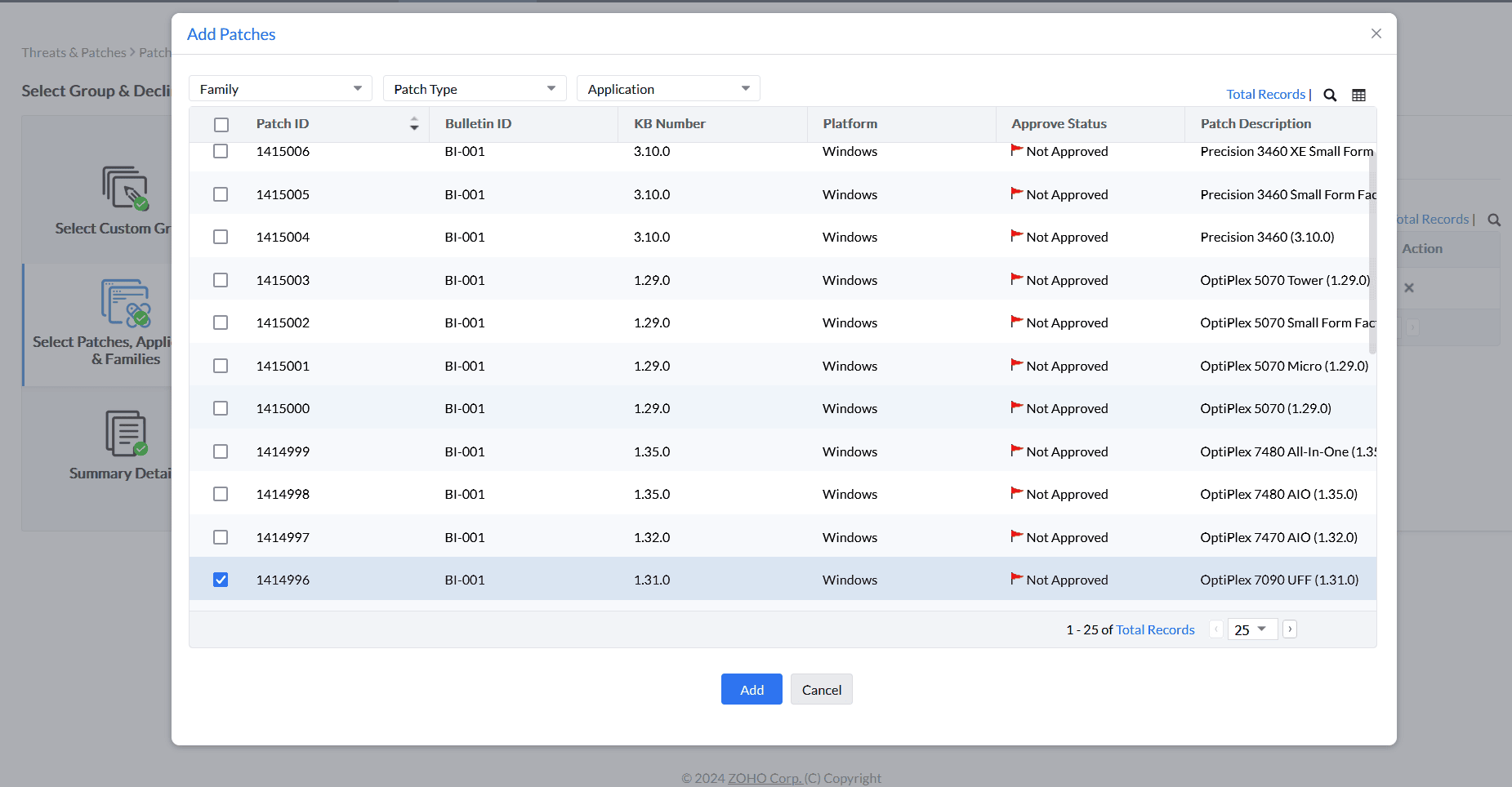
To choose patches for declining, under Patches section click on Add Patches.
A new window will be opened, where you can choose patches based on Family, Patch Type and Application.
After choosing the patches, click on Add.
Similarly, you can choose to decline patches for the applications or the family of applications under Applications tab and Family tab, respectively.
A new window will be opened, where you can choose patches based on Family, Patch Type and Application, along with the option to provide a reason and remarks for declining — ensuring a clear audit trail for future reference. (Replace the point in "Choosing the Patches, Applications or Families")
Note:Adding reason and remarks feature is available on Endpoint Central versions 11.5.26.20.01 and above. (At the end of the page)
Under Summary Details section, you can see the details of the settings, review it and click on Save.
You have successfully declined patches for the group. You can now see that Patches that are declined will not be reflecting the system health status or not been calculated as missing patches.




