Auto Logon Helper
(Feature available only in the Premium and Enterprise Editions)
Password Manager Pro stores the passwords of remote systems and applications. Normally, organizations use tools such as remote desktop applications, Putty or SecureCRT to connect to remote target systems. Password Manager Pro's Auto Logon Gateway feature provides an option to automatically connect to the remote target systems and applications without the need for handling passwords in plain text. In this document you will learn about the following topics:
- How the Auto Logon Gateway Feature Works
- How to Set Up Auto Logon Gateway
- How to Invoke Auto Logon through Gateway
1. How the Auto Logon Gateway Feature Works
Password Manager Pro comes bundled with RDP, SSH, and SQL gateway engines. This feature allows the users to launch remote terminal sessions from within their browser. All the sessions invoked from the Connections tab are initiated and tunneled through the Password Manager Pro server. This allows the administrators to disable RDP, SSH, and SQL permissions in the end user systems such as laptops and desktops but still allow users to access the target systems through tunneled remote sessions. The remote terminal sessions are emulated inside the browser tab and hence there is no need for installing any plug-in or agent in the end points. The only requirement is that the browser should be HTML 5 compatible (For example, IE 9 or above, Firefox 3.5 or above, Safari 4 or above, and Chrome).
As soon as an administrator adds a resource that supports one of these remote terminal session types, the feature becomes available to all users in the system who have access to that resource, with no further configuration anywhere. In addition, the Connections tab will allow users to easily locate remote accounts and launch a session with a single click. The entries in the Connections page with the names RDP and VNC Connections, SSH Connections, and SQL Connections belong to this type and come bundled with the product.
2. How to Set Up Auto Logon Gateway
You can set up Auto Logon Gateway in three ways:
- RDP and VNC Connections
- SSH Connections
- SQL Connections
2.1 RDP and VNC Connections
Notes:
- From build 12100, VNC passwords have to be added as an account under the respective resources.
- The users will be able to initiate VNC connections through their respective VNC accounts from the Resources tab only.
- Adding a VNC password as an account will facilitate validations, such as Access Control and Helpdesk for VNC passwords.
- All Windows systems can be automatically connected to an RDP session. To log into a Windows resource, you need to configure either a domain account or a local account that can be used by users to authenticate and launch a Windows RDP session with the remote host. Alternatively, an administrator can also allow users to launch RDP sessions using their AD account with which they have logged into the Password Manager Pro vault.
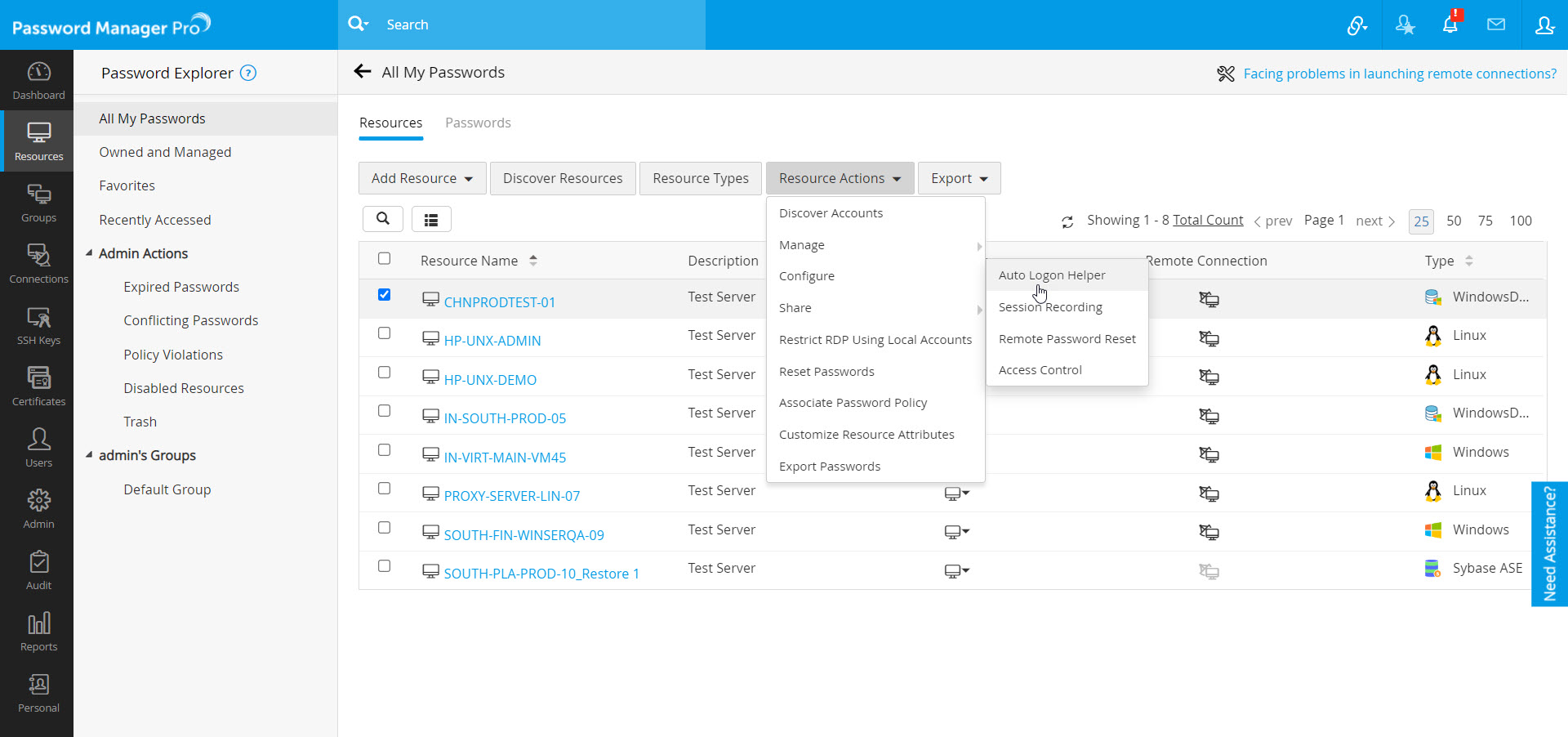
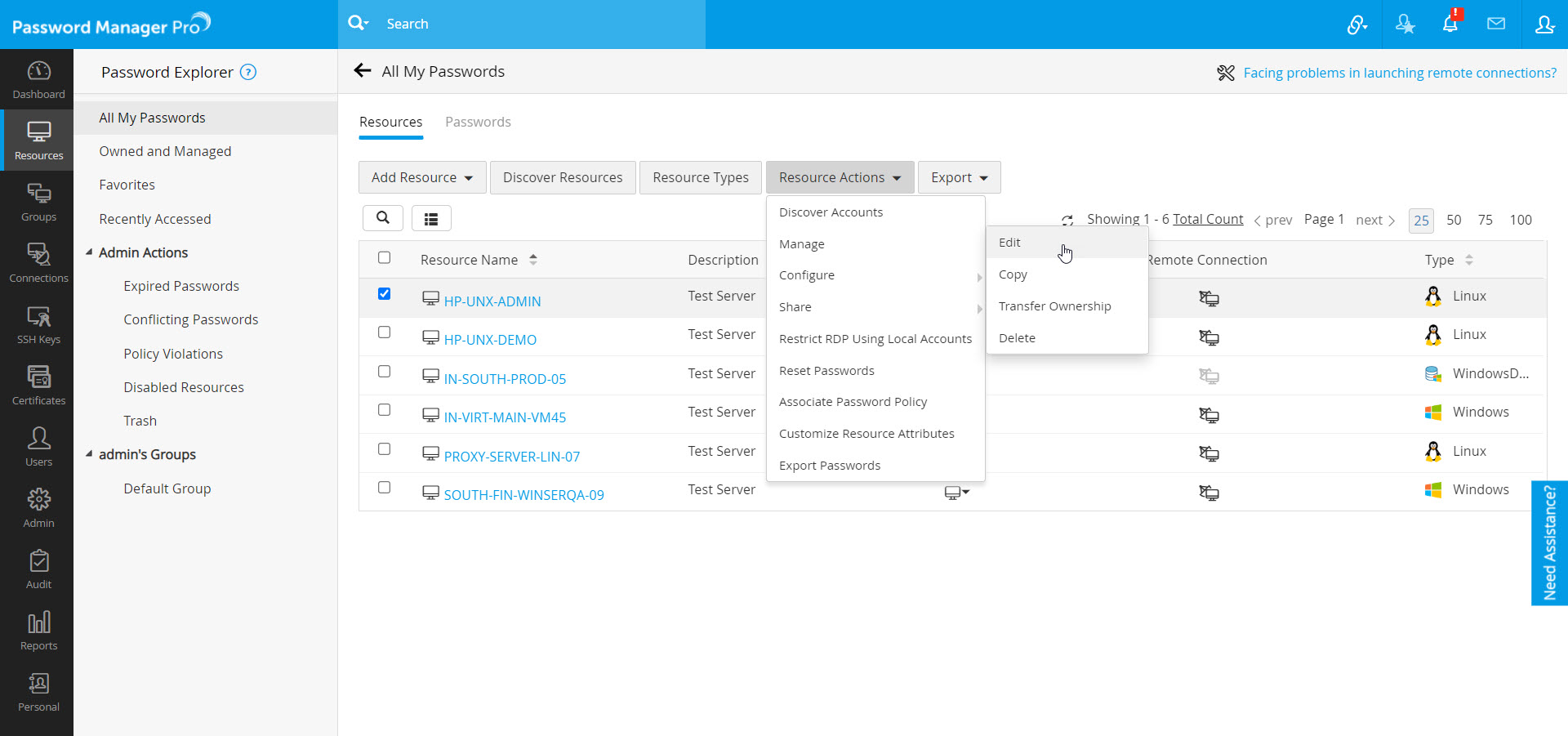
- To configure a domain account, go to the Resources tab and select the desired resource(s).
- Click Resource Actions >> Configure >> Auto Logon Helper from the drop-down.
- In the Configure Auto Logon Helper window that opens, configure the domain account by choosing the required domain from the Domain Name drop-down, specify the Username and the RDP Port for Auto Logon.
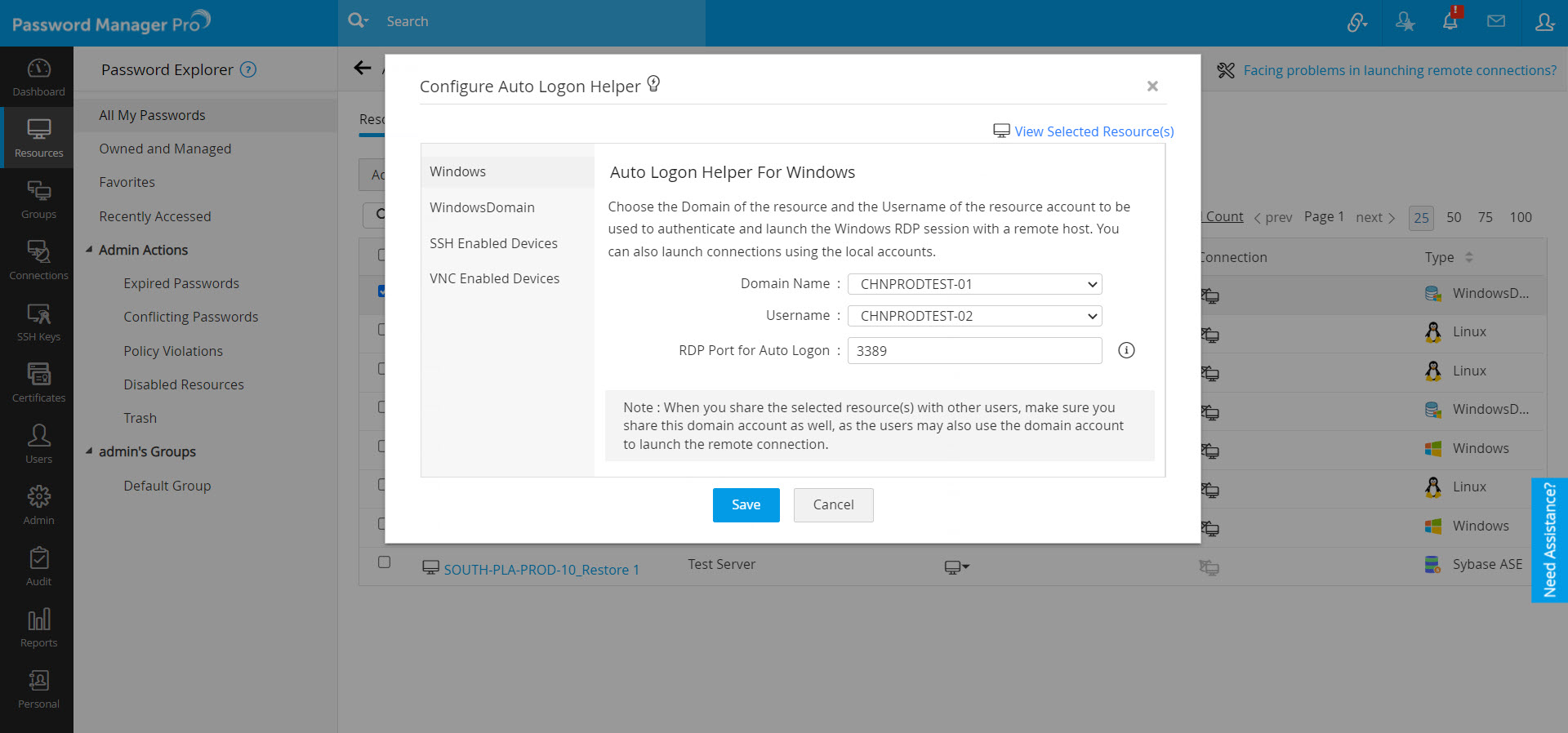
- Click Save.
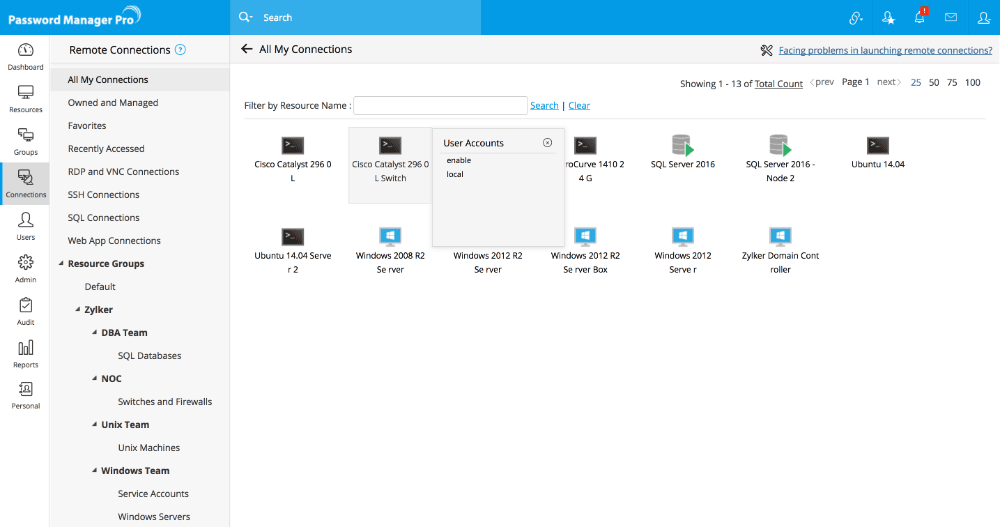
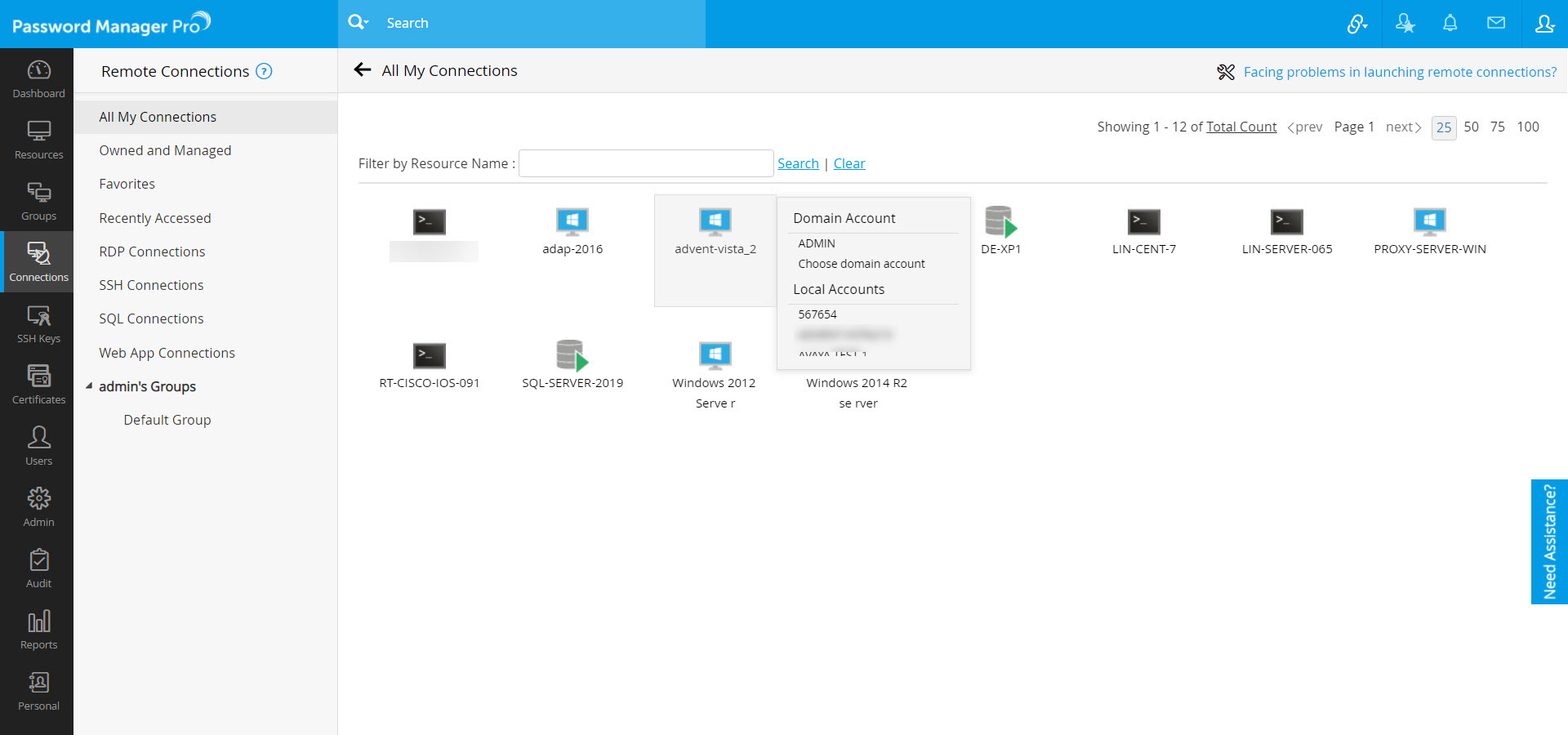
- Once you have configured your domain account, it will appear under the Connections tab as shown below:
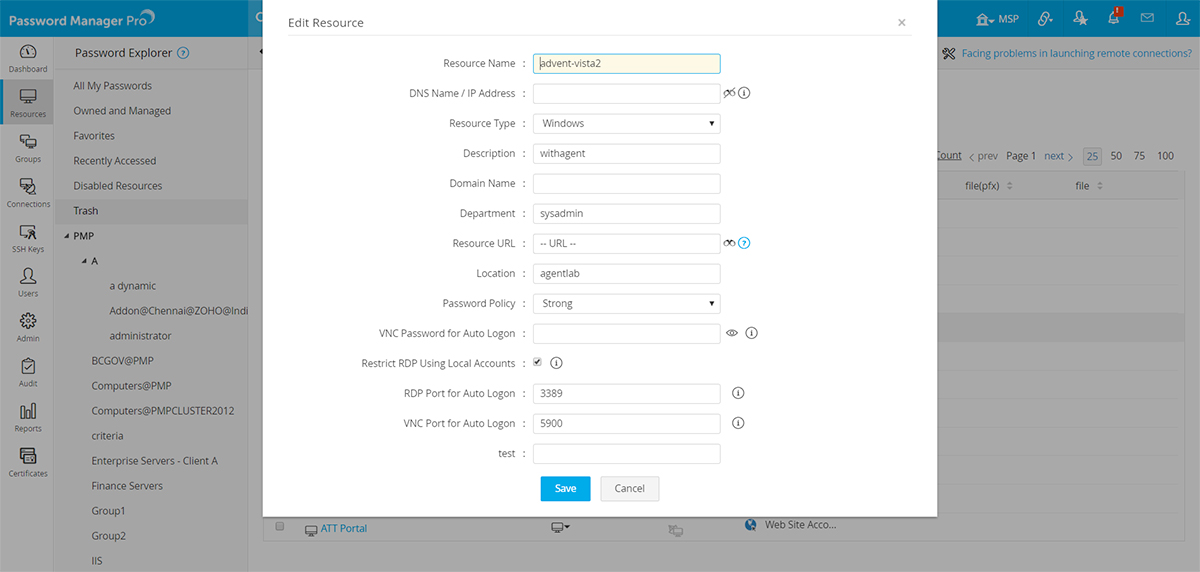
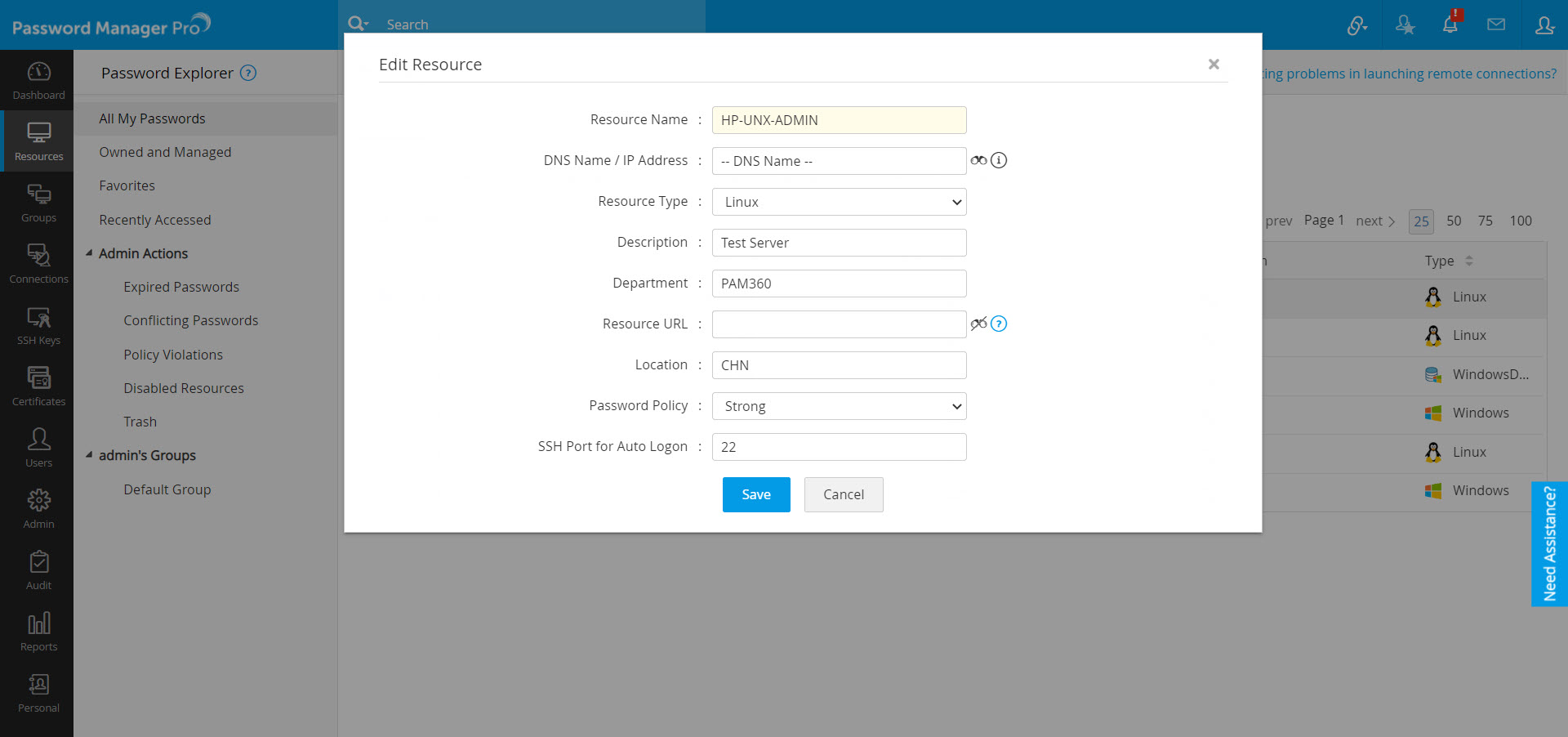
- To customize the port for RDP and VNC for each resource, go to the Resources tab, select the desired resource(s), and click Resource Actions >> Manage >> Edit from the drop-down at the top.
- In the Edit Resource window that opens, enter the RDP and VNC ports in the respective fields, and click Save.
2.2 SSH Connections
- Any SSH based device such as Linux servers or network devices can be added into Password Manager Pro as a resource. This allows administrators and other users to connect to the target system via a remote SSH session.
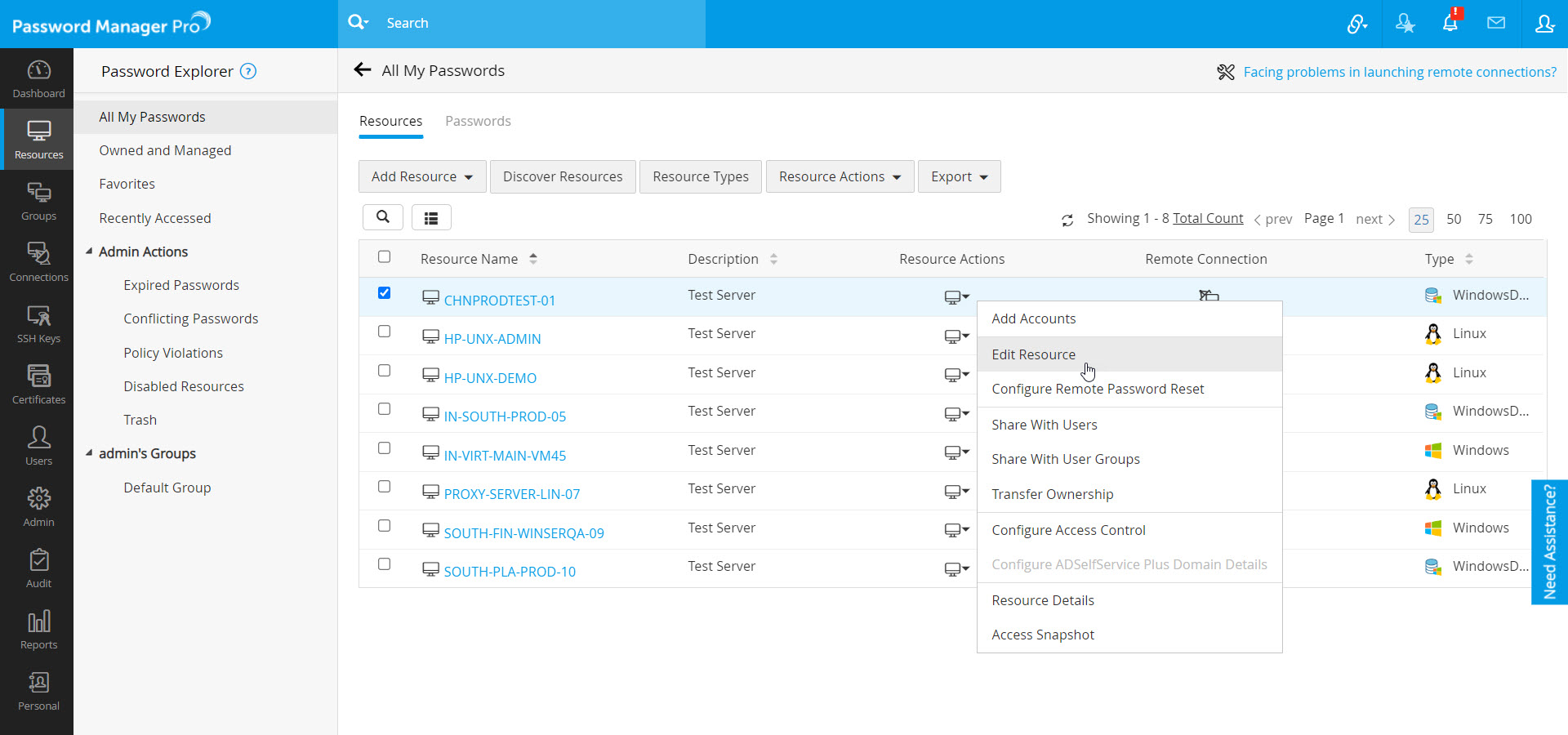
- You can configure the SSH port in which the SSH service is listening on the remote host. Password Manager Pro will use this port for launching the session. To do this, navigate to the Resources tab, select the desired resource(s), and choose Resource Actions >> Edit Resource from the drop-down beside the resource(s).
- In the Edit Resource window that opens, enter the SSH port through which you want to connect to the remote system, and click Save.
- The end users will be able to launch SSH sessions using the local SSH accounts that are shared with them by the administrators.
2.3 SQL Connections
You can add a database instance as a resource in Password Manager Pro to enable remote connections. This feature is supported for MySQL, PostgreSQL and MS-SQL databases. Note that the SQL connections are CLI based, meaning they allow users to execute queries to perform operations.
- To configure an SQL connection for remote sessions, navigate to the Resources tab, click Resource Action present next to the SQL resource and select the Configure Remote Password Reset.
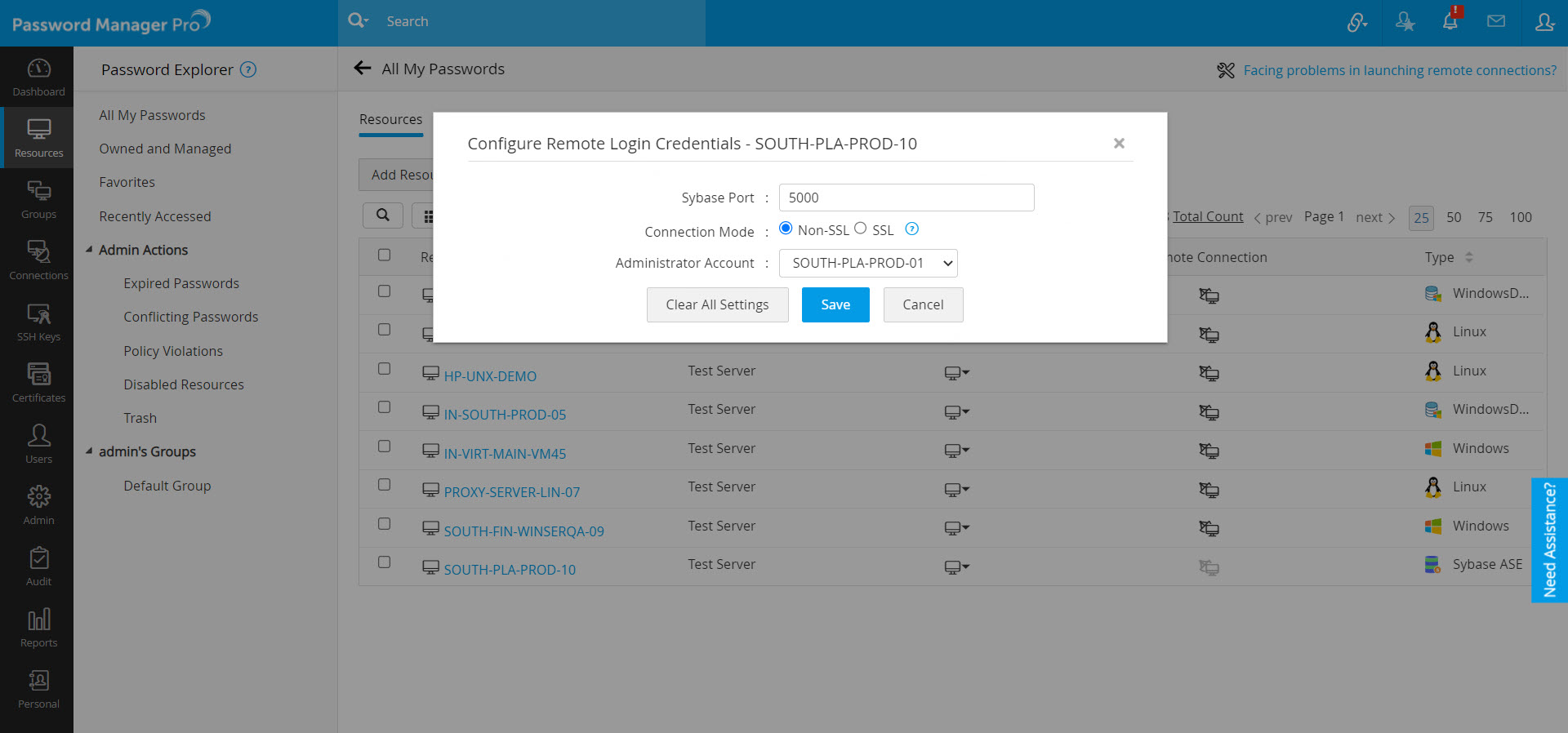
- Specify the port number that needs to be used for SQL connection. The SQL session will be initiated in this port with the account that is shared with the users.
2.4 Port Requirements for Client Access
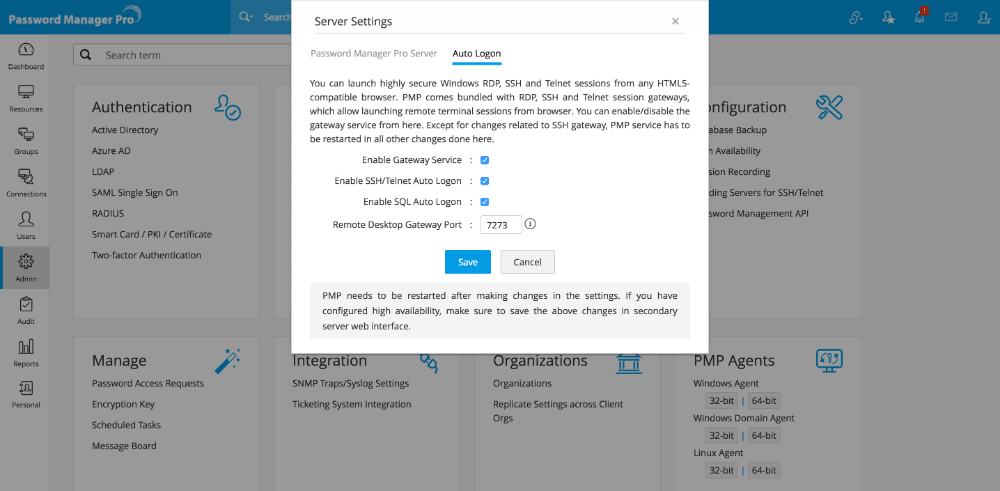
- The Windows RDP Auto Logon Gateway listens at port 7273 in Password Manager Pro server by default. This is a secure web socket port (wss://) and you should allow traffic to this port from the end user machines for this feature to work.
- You can change this port by navigating to Admin >> Configuration >> Password Manager Pro Server.
- In the new window that opens, switch to Auto Logon tab and then enter the port in the Remote Desktop Gateway Port field.
- Password Manager Pro web server (7272 in Password Manager Pro server) and this gateway should open and listen at different ports. The SSH and Telnet Gateways have no such requirement as they use the same Password Manager Pro web server port for all communication.
Note: When Password Manager Pro is installed, it generates a self-signed SSL certificate for the instance which is also used by the Auto Logon Gateway to encrypt the traffic. It is recommended that you apply a CA signed certificate to the Password Manager Pro instance before opening it out for end users. In case of a self-signed certificate, connecting to the gateway is not possible unless users explicitly mention the gateway port in the URL, accept the warning and install the self-signed certificate. (For steps to generate unique SSL certificate, refer to this section of our site).
3. How to Invoke Auto Logon through Gateway
As soon as an administrator adds a resource that supports one of the three remote terminal session types (Windows RDP, SSH and SQL sessions), the feature becomes available to all users in the system who have access to that resource, with no further configuration anywhere. The Connections tab will allow users to easily locate remote accounts and launch a session with a single click.