Empower employees to enroll devices by themselves.
Remotely manage only work-related aspects and respect user privacy.
Apply proactive and reactive policies to secure work data.
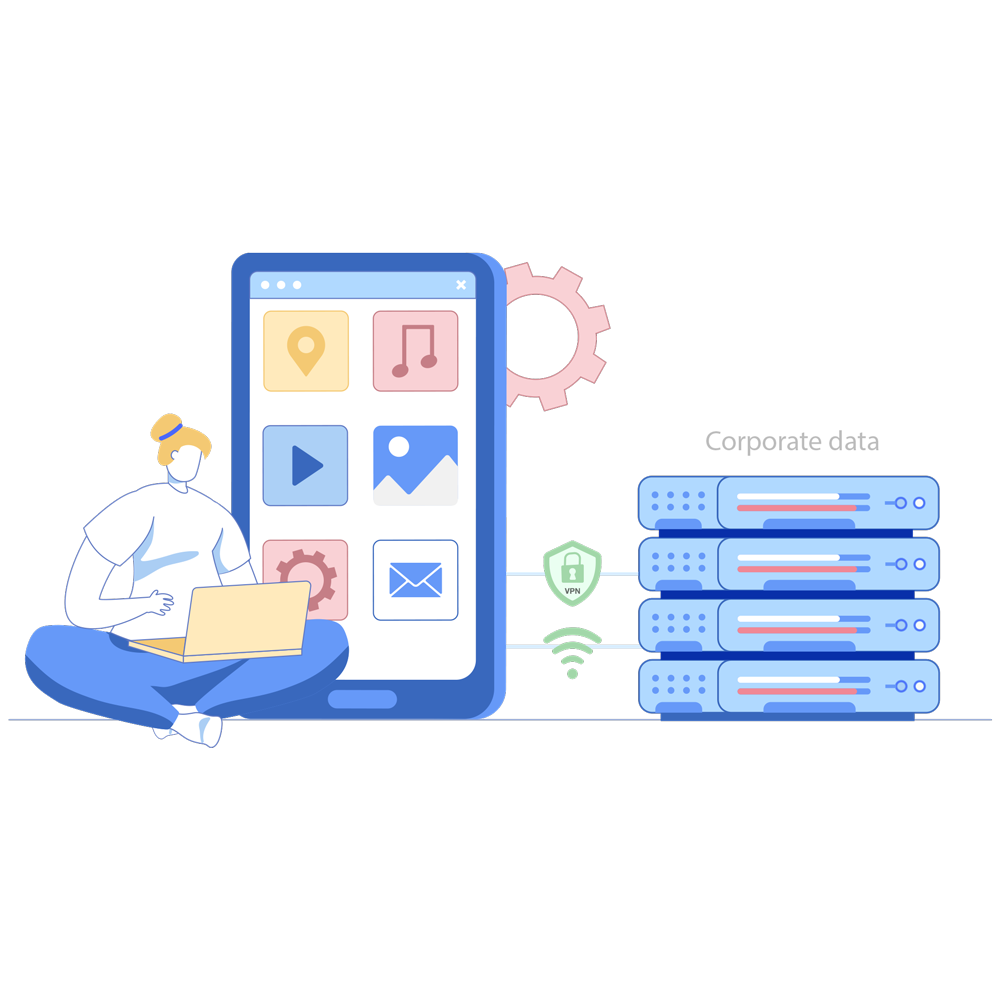
Restrict corporate data access on unauthorized devices.
Let employees identify themselves through two factor authentication when enrolling their devices.
Provision BYODs with profiles that manage and protect work apps and data just like on corporate devices.
Silently deploy work apps for your users and provide secure access to corporate resources through a unified catalog.
Separate and encrypt work data to manage only the work profile for enhanced security and privacy.
Set password policies and restrict sharing via clipboards, screenshots, cloud backups, unmanaged apps, USBs, and wireless network protocols.
Audit and revoke access to business apps and emails on unmanaged devices and encourage enrollment for secure access.
Implement a policy on the collection of data from users and inform them for adherence to compliance policies and regulations.
Set up a VPN just for work apps to secure work data in transit without intruding on user privacy.
Remotely wipe all corporate data from devices when they are lost and when employees leave the organization.
Allow employees to enroll devices by themselves after both OTP- and directory-credential-based authentication or by using Managed Apple ID establish identity. Group personal devices based on the device type, user grouping, and enrollment method to provision devices with settings, apps, content, and network configurations accordingly. Additionally, enroll and manage Android enterprise devices without the need to install a client app on devices.
Secure corporate data without affecting user privacy by containerizing it. Ensure that admins only have management rights over the work container so that the user's personal preferences can remain unmodified. Restrict unauthorized sharing of corporate data between the managed corporate space and the unmanaged personal space through any means, including copy and paste via clipboards. Ensure that malware in the personal space does not affect work data through this separation.
Set up a stringent end-user privacy policy that adheres to both organizational policies and regulationsory by customizing data collection options for phone numbers, locations, and more. Communicate the created privacy policy to end users during device enrollment. Also, hide work notifications on devices after work hours.
Let your users securely tap into corporate resources as needed by configuring a VPN. Configure a per-app VPN and allow users to connect to the VPN service only when accessing corporate apps and websites. Increase productivity by seamlessly configuring corporate connectivity profiles, such as for Wi-Fi and proxy. Automatically authenticate users for all apps at once with mobile single sign-on and certificate-based authentication.
Configure scheduled device scans to detect policy violations and set up remediation steps, such as deactivating the workspace on noncompliant devices. Run Google Play Protect scans to ensure apps are free from malware. Protect the integrity of your corporate data by denying data access to blocklisted apps and websites.

Remotely erase corporate data from devices while keeping personal data intact when employees leave the organization. Limit the impact of compromised devices by automatically detecting and removing jailbroken or rooted devices from management. In case of device theft or loss, instantly lock the device and wipe the corporate data to prevent misuse.








We have been using Mobile Device Manager Plus for over a year now, and it has assisted us in staying compliant with our organization's security and compliance policies. We are able to safeguard our customer data, track our devices, and implement policies over the air.
Syed Ahmad RasoolSr. manager of technology security, Vodafone
Mobile Device Manager Plus is a powerful safeguard against the threat of corporate content coming into the wrong hands. This robust solution enables us to centralize all mobile devices on the same console as a web-portal which is segmented by countries. The access for local IT teams in each country is restricted to the mobile devices in their respective country, ensuring better security.
Abdoul Karim BarrySystems engineer, Microcred Group