USB Device Security Management
The usage of portable storage devices is a growing reality and it poses two main concerns for an organization: data theft and malware injection. In the absence of a comprehensive USB device management software, It is extremely easy for a disgruntled employee to inject malware or steal business-critical information using a USB device. To prevent such things from happening, IT teams need to enforce strong device restrictions with an apt USB security management in place to enforce USB device control.
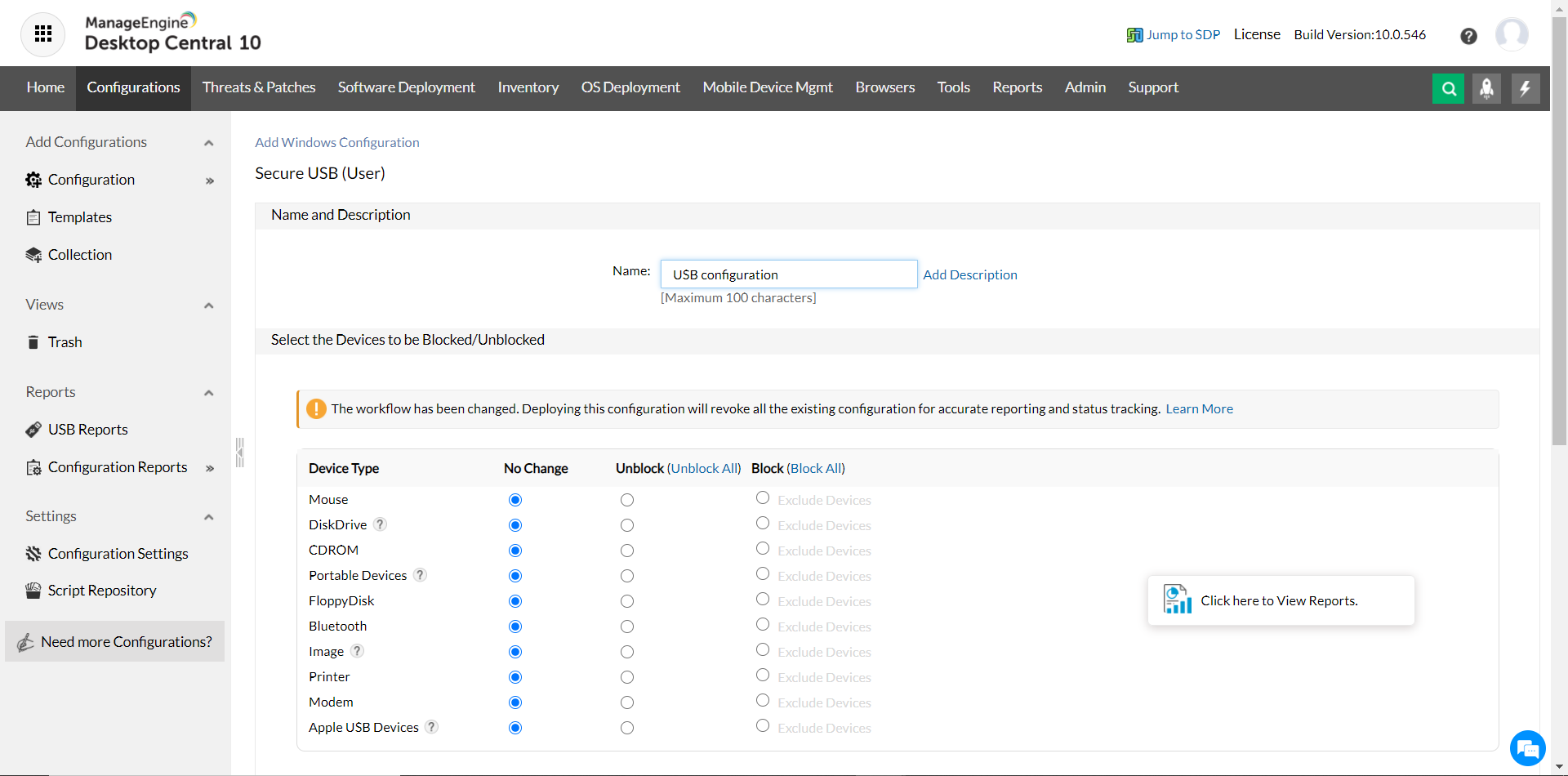
Implementing USB Device Management within your network
Endpoint Central's secure USB management features help administrators limit the scope of USB device usage, selectively based on the various roles and departments. This aspect of USB device control enables administrators to centrally control the usage of various USB devices in the network by blocking or disabling them. It prevents unauthorized download and upload activities as well as the possibility to inject harmful malware into the network. Using the USB security management software the restriction can be set not just on the computer and user level but also on the manufacturer type, providing more accessibility. Our USB managment feature is a simple and easy-to-use feature that allows users to enable USB security with just a few clicks.
Supported USB devices
Endpoint Central's USB security management features currently support enabling or disabling the following USB devices for users and computers:
- Mouse
- Disk drive
- CD-ROM
- Portable storage devices
- Floppy disk
- Bluetooth
- Image
- Printer
- Modem
- Apple USB Devices
USB Device Audit
IT teams face the cumbersome task of analyzing the usage of pen drives, CDs, or any other portable storage devices that might jeopardize your company’s data or security. It is always better to record these activities for future auditing using a USB device manager. Endpoint Central's USB security management software helps track the usage of said USB devices and provides you all the necessary information such as:
- Device name
- User name
- Device type
- Time duration
- Manufacturer and more.
You can choose either a summary or a detailed view of the data. The reports can be exported as a CSV or PDF for further analysis.
USB Alert
Once a USB device has been restricted, USB alert settings can be configured to notify users whenever they plug in a restricted device. This way, IT teams can leverage Endpoint Central's USB device control features can ensure that the end user complies with the USB restriction policy set up by the organization.
USB Encryption
Encryption policies can be configured to control how USB devices interact with managed endpoints. Admins can either restrict access to only encrypted USB devices or prompt users to encrypt their device upon write, thereby ensuring no unencrypted device carries sensitive data out of the organization.
What is USB device management and control?
USB device management & control is the process of monitoring and restricting the usage of USB devices within a network, to protect from insider threats. USB device management is imperative to endpoint and data security and a proper USB security management software keeps threats at bay.
Advantages of USB device management
Securing and managing your USB devices in your corporate network using an enterprise USB device management software can yield many benefits. Some of them are--
- Prevent data theft and data loss that can result due to employees using their personal USB sticks.
- Stop booby-trapped USB devices (devices laced with a worm or virus) from inflicting damage to corporate devices.
- Minimize threats arising from malicious program or code and strenghthen corporate security.
- Enterprise USB management software filters out unidentified and unauthorized devices from connecting to your enterprise.
Looking for an MSP offering? Choose Endpoint Central MSP

Manage and secure client endpoints effortlessly. Discover the benefits of choosing us.