# Solutions for meeting cybersecurity performance goals and HHS initiatives
The Department of Health and Human Services (HHS) has introduced the cybersecurity performance goals (CPGs)—a set of controls prioritized from widely adopted NIST CSF and HICP to focus on resilience against the top priority threats to healthcare (as revealed in the Hospital Cyber Resiliency Initiative Landscape Analysis by HHS).
## Why CPGs?
A brief history of HHS Cybersecurity Performance Goals — from the CSA act in 2015 to the HISAA act in 2024.
### 2015 — Congress passes the Cybersecurity Act (CSA)
Acknowledging the rising threat to critical sectors, the U.S. Congress passes the CSA. Section 405(d) aims to establish voluntary best practices to shield healthcare organizations (HCOs) from cyber risks.

### 2015 — HHS sets up a Task Group under section 405(d)
HHS shoulders this responsibility and convenes the 405(d) Task Group, comprising over 150 members from cybersecurity, privacy, healthcare practitioners, IT, and other SMEs.
### 2018 — The Health Industry Cybersecurity Practices (HICP) is created
The task force creates the HICP, a best practice guide focused on the top threats to the healthcare industry along with specific practices that HCOs can follow to combat them. Additionally, the HICP supports compliance with HIPAA’s Security Rule.
### 2018—2022 — Healthcare becomes the #1 ransomware target
**93%** increase in large breaches reported to the HHS Office for Civil Rights (OCR).
**278%** increase in large breaches involving ransomware.
#### Ransomware attacks affect cancer care during COVID-19 pandemic:
- **41%** decrease in total outpatient volume.
#### Major ransomware attack in San Diego-based healthcare NPO:
- Causes **$112M** in lost revenue, remediation, and fines.
In spite of the HICP being enforced, ransomware incidents continue to rise, revealing that many HCOs struggle to adopt and implement these standards effectively due to:
- IT teams at HCOs being understaffed, with technicians juggling multiple roles.
- IT budgets prioritizing large projects like EHR implementation, leaving limited funds for cybersecurity.
### April 2023 — Hospital Cyber Resiliency Initiative Landscape Analysis
Despite multiple frameworks, attacks remain prevalent. HHS conducts research to understand top threats and controls to prevent them, releasing findings in the *Hospital Cyber Resiliency Initiative Landscape Analysis*.
Key findings:
#### Ransomware: The top threat
- **60%** of HCOs affected in 2023.
#### Poor vulnerability assessment
- **53%** of hospitals have a documented response plan for vulnerabilities.
- **20%** of hospitals conduct advanced vulnerability tests.
#### Third-party gateways
- **47%** of ransomware incidents involve third-party sources.
- **3rd** most common risk vector according to CISOs.
#### Antiquated assets
- **96%** of hospitals operate legacy systems with known vulnerabilities.
#### Rising cyber insurance premiums
- **46%** increase in 2021, leading some hospitals to self-insure.
[See the detailed report from HHS](https://405d.hhs.gov/Documents/405d-hospital-resiliency-analysis.pdf)
### Jan. 2024 — HHS releases voluntary CPGs
Based on the analysis findings, HHS releases prioritized cybersecurity practices dubbed the CPGs.
- Focused on top threats plaguing healthcare.
- References key controls from NIST CSF and HICP.
- Split into two categories: essential and enhanced.
- HHS works with Congress on funding programs for implementation.
### Jan. 2024—Sept. 2024 — Largest-ever cyberattack shifts priorities
Despite initiatives, healthcare witnesses increased cyberattacks.
> "Mega corporations like UnitedHealth are flunking Cybersecurity 101, and American families are suffering as a result...these are common-sense reforms, which include jail time for CEOs that lie to the government about their cybersecurity."
> **Ron Wyden**
> U.S. Senate Finance Committee Chair
#### Change Healthcare cyberattack:
- **100 million** individuals affected in the largest-known breach of PHIs.
- **$2.5B** total impacts recorded by UnitedHealth.
[67%](https://news.sophos.com/en-us/2024/07/30/the-state-of-ransomware-in-healthcare-2024/index.html) of HCOs are hit by ransomware in 2024.
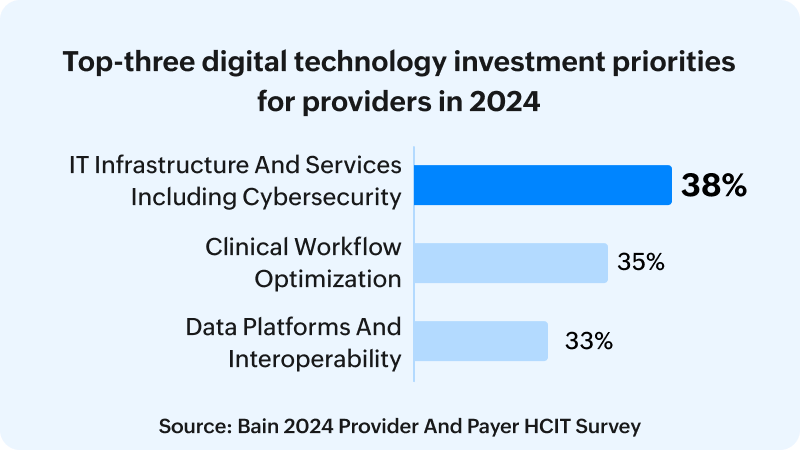
In response, cybersecurity becomes a board-level priority for HCOs, as indicated by the [KLAS report](https://www.bain.com/insights/healthcare-it-spending-innovation-integration-ai/index.html).
### Sept. 2024 — Health Infrastructure Security and Accountability Act (HISAA)
With cybersecurity becoming a national priority, the U.S. Senate introduces HISAA, dictating stringent regulations and fines for cybersecurity violations.
Key highlights:
- Removal of HHS and HIPAA statutory caps on fines to ensure larger HCOs face substantial penalties.
- Allocation of **$1.3 billion** to support implementation, especially for smaller HCOs.
- Mandatory public disclosure of compliance status, with annual executive certification.
- False information may result in fines up to **$1M** and prison time up to **10 years**.
- Annual HHS audits with biennial summaries to Congress.
- Creation of minimum and enhanced security requirements built upon CPGs within two years.
- Until new standards are established, HCOs should assess adherence to CPGs.
## CPGs are the stepping stone to HISAA—here's how you can align with them and be prepared
Before HISAA-specific minimum security requirements become effective, HCOs should assess compliance with the CPGs. While currently voluntary, HISAA will mandate these goals in the future. Since CPGs prioritize controls from NIST CSF and HICP against top healthcare threats, early adoption helps mitigate critical risks and prepares organizations for future mandates.
## Tactical advice on implementing relevant portions of CPG with ManageEngine Endpoint Central
ManageEngine Endpoint Central helps achieve endpoint management and security portions of the essential and enhanced CPG goals.
### Meeting the essential goals
| CPG Goal | Description | How Endpoint Central helps you |
|---|---|---|
| Mitigate Known Vulnerabilities | Reduce the likelihood of threat actors exploiting known vulnerabilities to breach organizational networks directly accessible from the internet. | Scan for known vulnerabilities and deploy patches immediately wherever applicable. [Learn more about vulnerability management](https://www.manageengine.com/products/desktop-central/vulnerability-management.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals) |
| Email Security | Reduce risk from email-based threats such as spoofing, phishing, and fraud. | Circulate educational content to mobile devices to raise phishing awareness. [Learn more about content management](https://www.manageengine.com/mobile-device-management/help/content_management/mdm_document_distribution.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals) |
| Basic Cybersecurity Training | Ensure users learn and perform more secure behaviors. | Distribute cybersecurity education content to mobile devices. [Learn more about content distribution](https://www.manageengine.com/mobile-device-management/help/content_management/mdm_document_distribution.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals) |
| Strong Encryption | Maintain confidentiality of sensitive data and integrity of IT and OT traffic in motion. | Enforce encryption on devices to protect sensitive data. [Learn more about encryption](https://www.manageengine.com/products/desktop-central/endpoint-data-security.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals#data-encryption) |
| Revoke Credentials for Departing Members | Prevent unauthorized access by former workforce members. | Remove local user profiles from all associated shared devices. [Learn how to remove local user profiles across all devices](https://www.manageengine.com/products/desktop-central/help/computer_configuration/managing_windows_local_users.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals#Remove-User) |
| Basic Incident Planning and Preparedness | Ensure safe and effective responses and recovery from cybersecurity incidents. | - Perform vulnerability scans across the device fleet.
- Automatically detect and mitigate ransomware, restoring stable backups.
- Monitor devices for IoCs.
- Remotely wipe and reset compromised devices. |
| Unique Credentials | Use unique credentials to detect anomalous activity and prevent lateral movement. | Enforce organizational password policies for all users. [Learn more about password policies](https://www.manageengine.com/products/desktop-central/password_policy.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals) |
| Separate User and Privileged Accounts | Prevent compromised user accounts from accessing privileged accounts. | Use a dedicated dashboard to manage administrative accounts, control UAC, revoke unnecessary privileges, and restrict elevated access. |
| Vendor/Supplier Cybersecurity Requirements | Identify, assess, and mitigate third-party risks. | Patch third-party products with support for 850+ applications. [Learn more about patch and vulnerability management](https://www.manageengine.com/products/desktop-central/features.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=essential-goals) |
### Meeting the enhanced goals
| CPG Goal | Description | How Endpoint Central helps you |
|---|---|---|
| Asset Inventory | Identify known, unknown (shadow), and unmanaged assets. | Maintain a comprehensive inventory of managed devices integrated with leading ITSM products. [Learn more about asset management](https://www.manageengine.com/products/desktop-central/it-asset-management.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=enhanced-goals) |
| Third Party Vulnerability Disclosure | Discover and respond to known threats in vendor-provided assets. | Continuously monitor assets for third-party vulnerabilities. [Learn more about vulnerability management](https://www.manageengine.com/products/desktop-central/vulnerability-management.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=enhanced-goals#vulnearbility-as) |
| Third Party Incident Reporting | Respond to known security incidents across vendors. | - Scan devices and applications to identify vulnerabilities.
- Patch and fix misconfigurations with support for 1,500+ third-party vulnerabilities.
[Learn more about patch and vulnerability management](https://www.manageengine.com/products/desktop-central/features.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=enhanced-goals) |
| Cybersecurity Mitigation | Act quickly on prioritized vulnerabilities from testing and simulations. | Apply patches and correct insecure configurations for relevant vulnerabilities. |
| Detect & Respond to Relevant Threats & TTPs | Detect relevant endpoint threats and secure network entry and exit points. | Conduct real-time monitoring to detect malware and secure endpoints. [Learn more about our next-gen antivirus capabilities](https://www.manageengine.com/products/desktop-central/nextgen-antivirus.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=enhanced-goals) |
| Centralized Incident Planning & Preparedness | Maintain and drill cybersecurity incident response plans. | - Perform vulnerability scans across the device fleet.
- Automatically detect and mitigate ransomware.
- Monitor for IoCs.
- Remotely wipe and reset compromised devices. |
| Configuration Management | Define and maintain secure system settings based on established baselines. | Configure and align devices with organizational baseline policies. [Learn more about configuration management](https://www.manageengine.com/products/desktop-central/configuration-management.html?utm_source=enterprise-cpg-hhs&utm_medium=website&utm_content=enhanced-goals) |
**Source:** hhscyber.hhs.gov/performance-goals.html