- Related Products
- Log360
- AD360
- ADManager Plus
- ADAudit Plus
- ADSelfService Plus
- Exchange Reporter Plus
 Click here to expand
Click here to expand
Users can access VirusTotal API in two ways:
Recommendation: For business workflows it is recommended to use Premium API for integration.
To learn more about VirusTotal, their terms of service, privacy policy, and API usage, please visit their website.
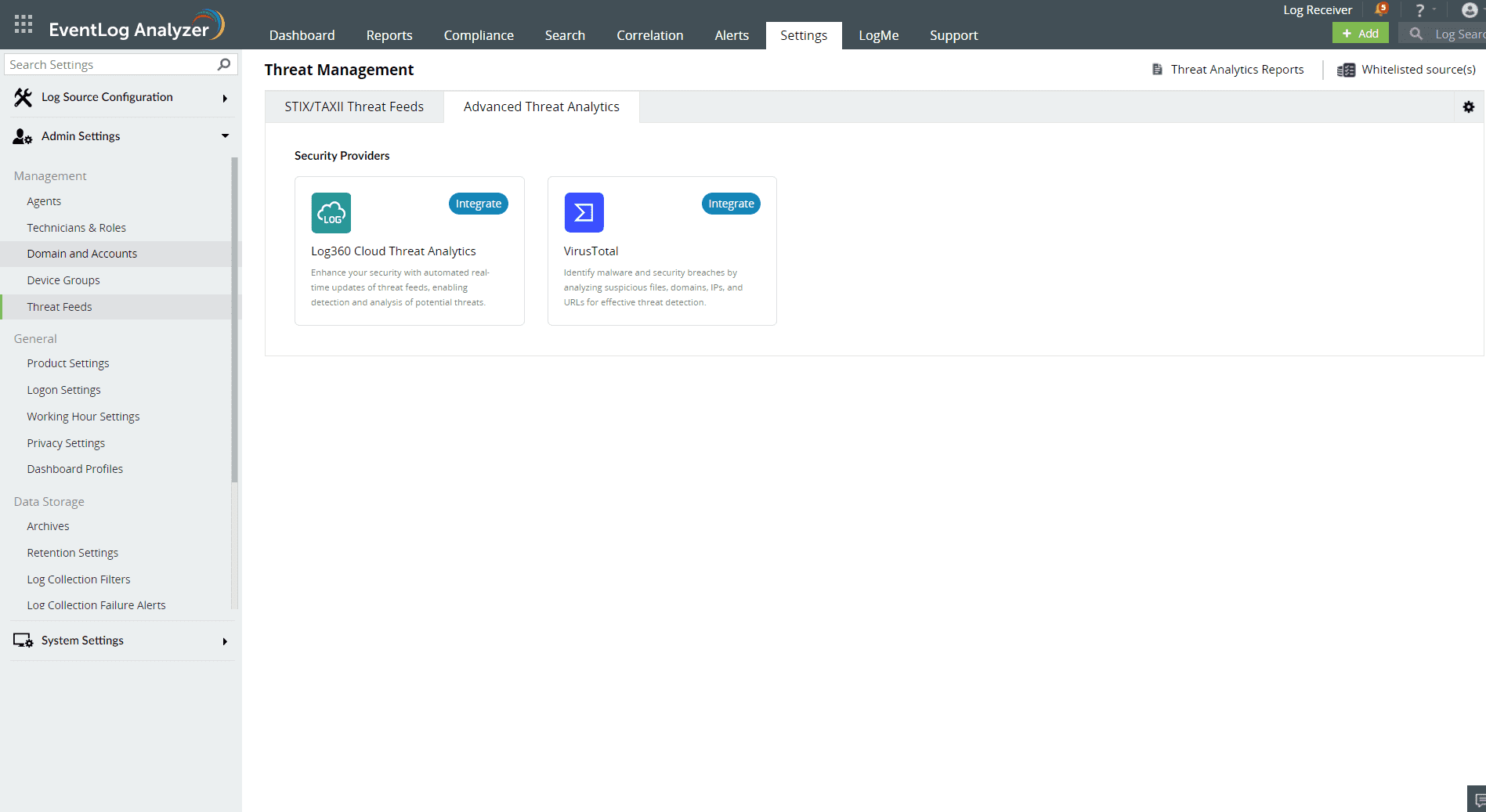
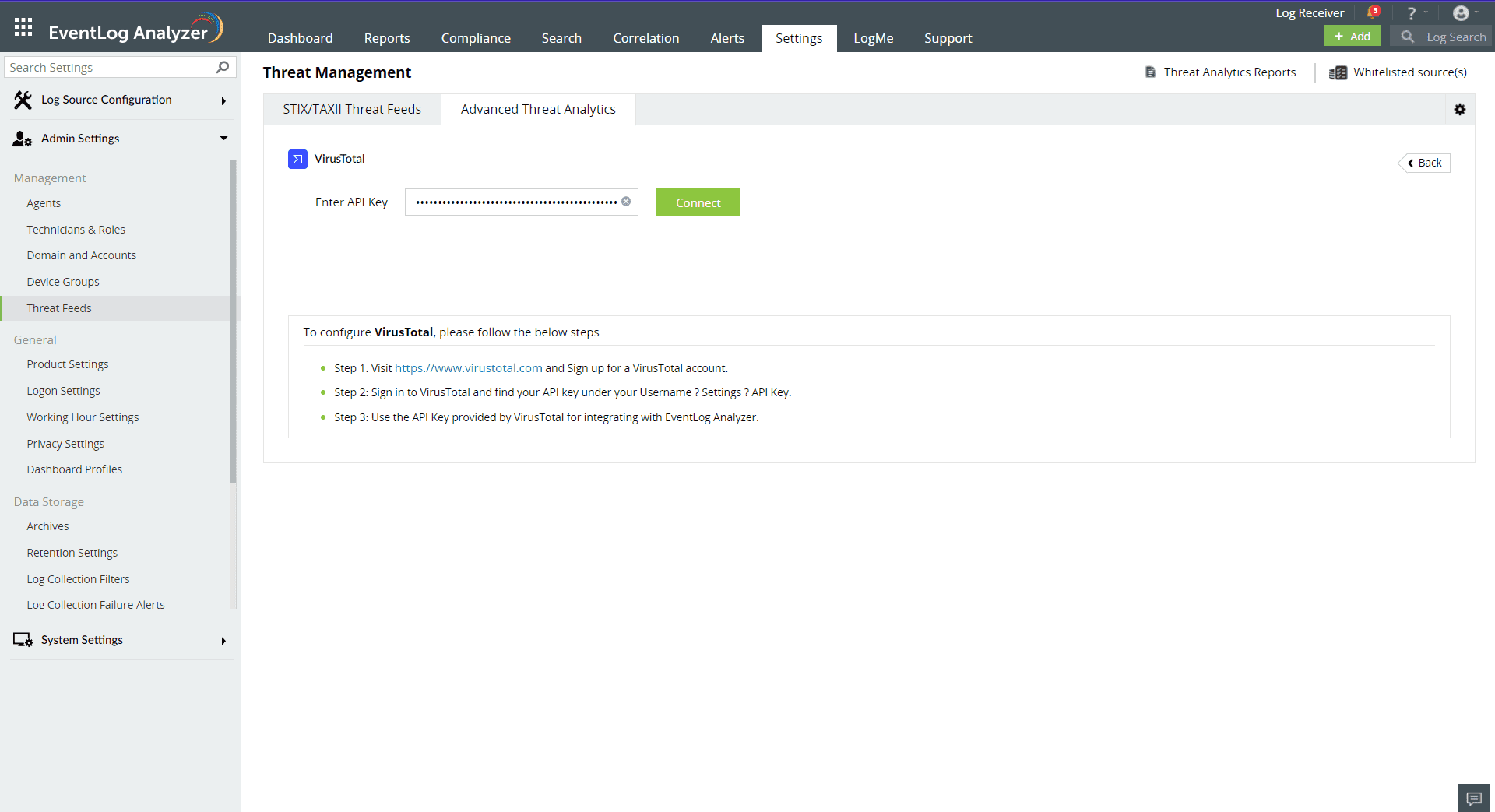
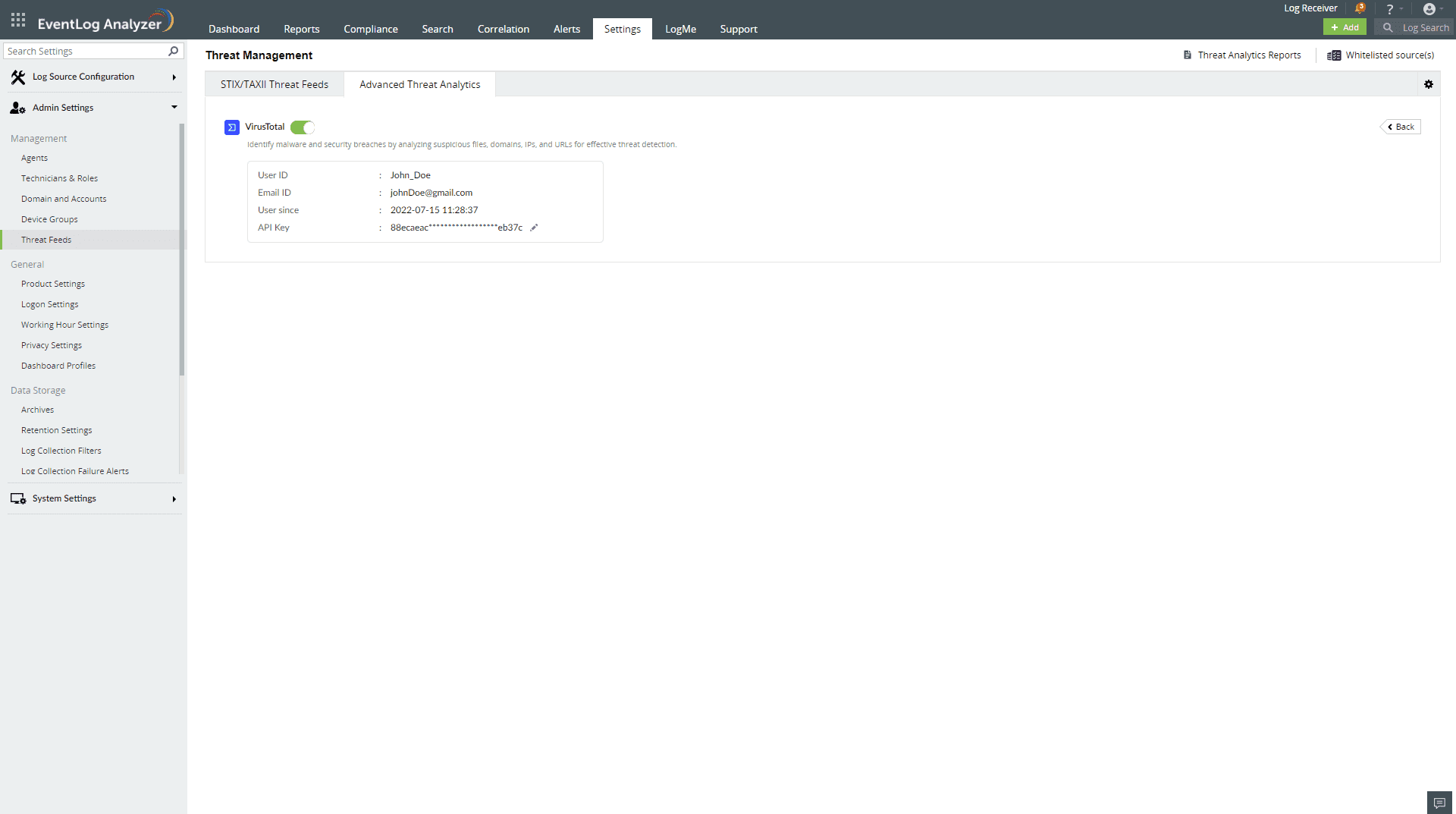
Once you have purchased the Advanced Threat Analytics add-on and applied the license, head to the Advanced Threat Analytics page.
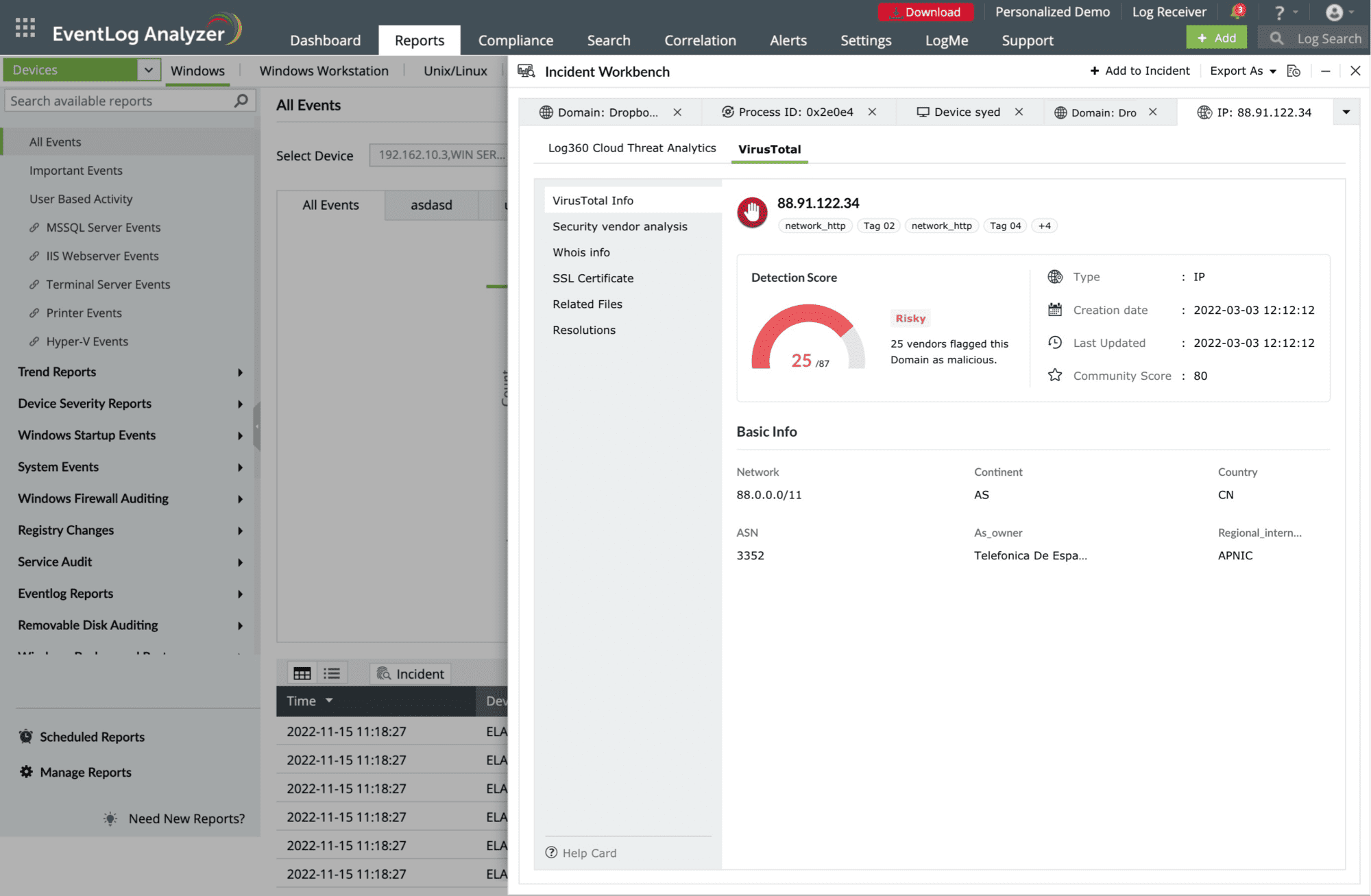
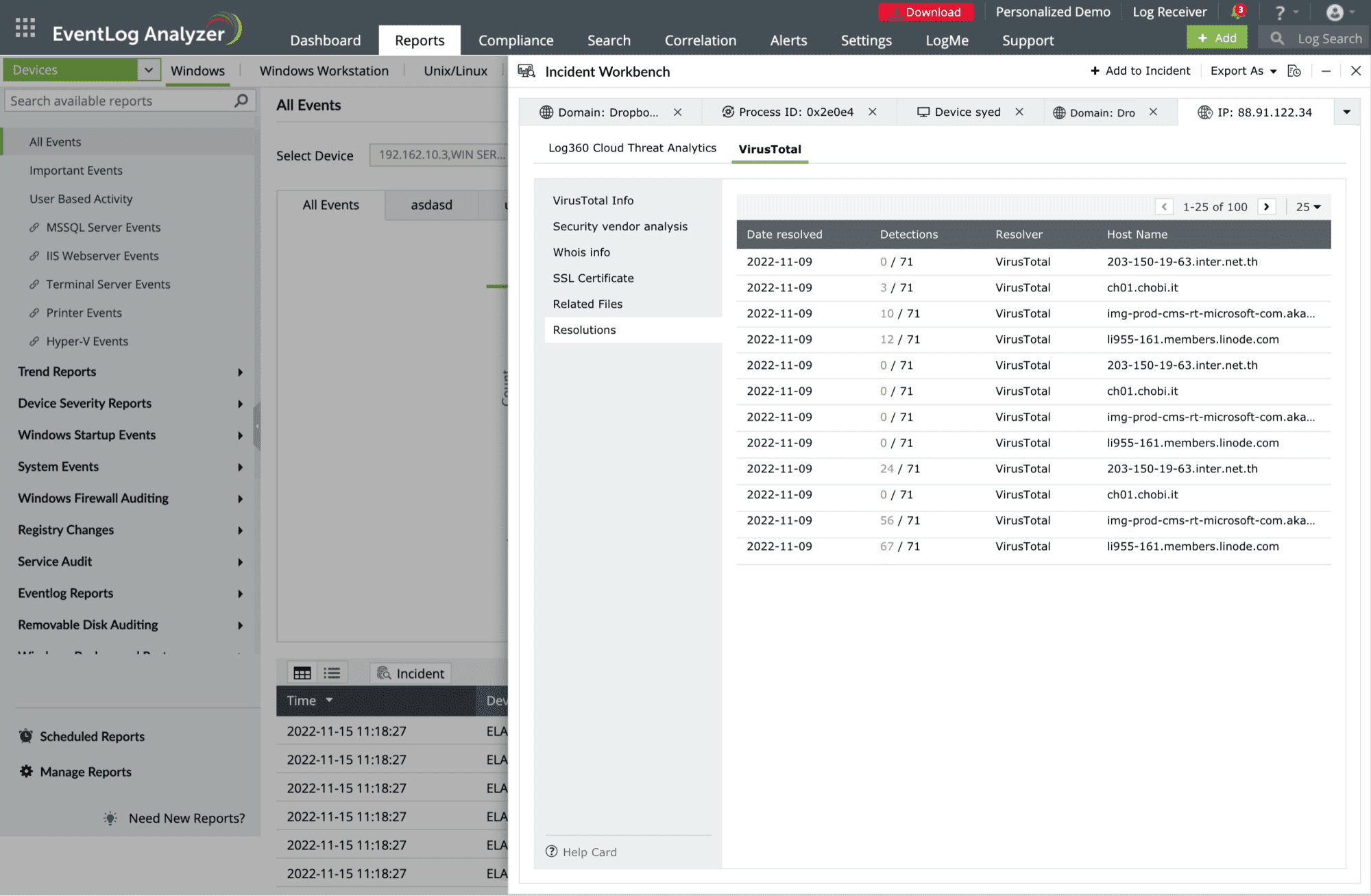
In EventLog Analyzer, users can access the data from VirusTotal through the Incident Workbench. Learn how to invoke the Incident Workbench from different dashboards of EventLog Analyzer.
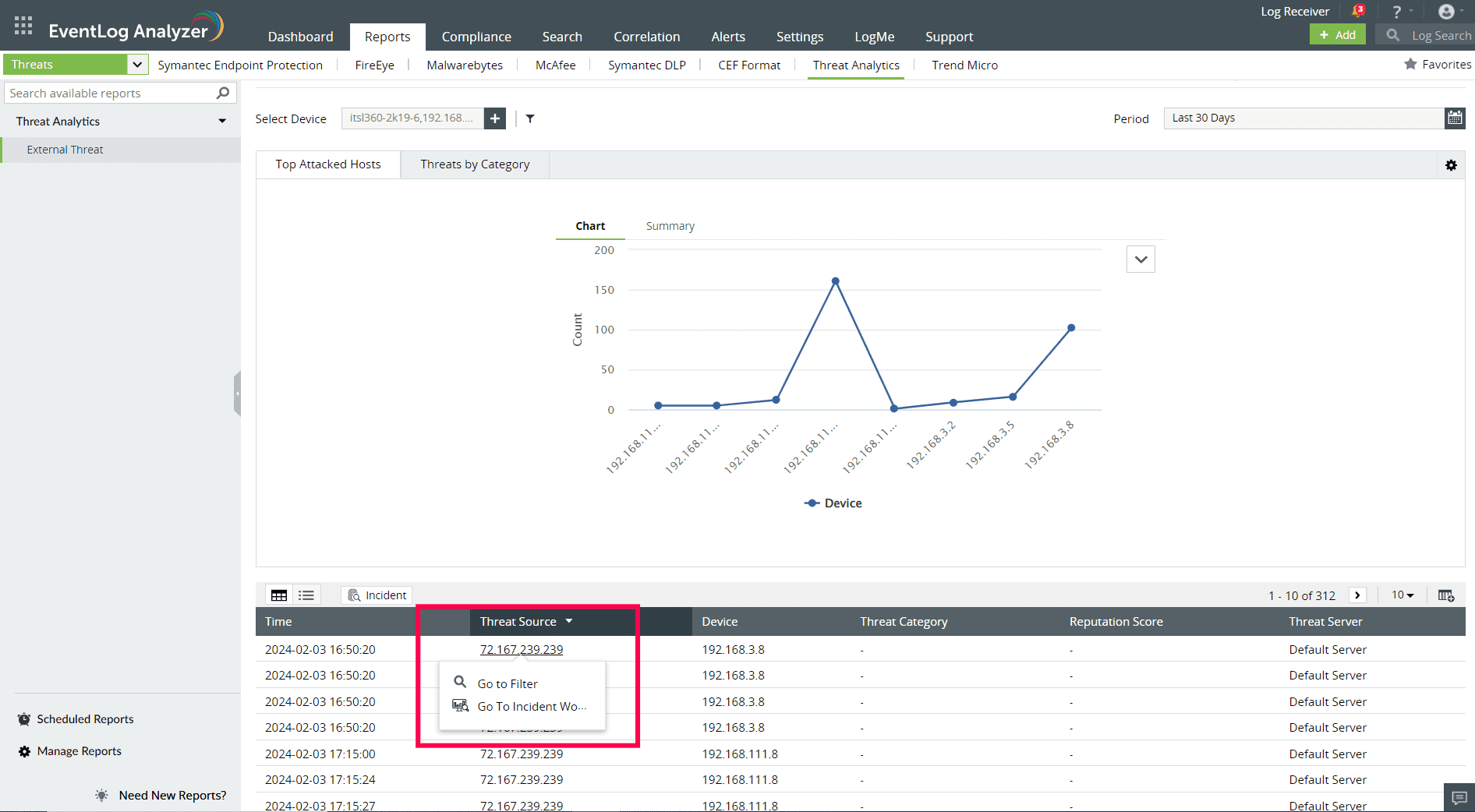

Select any IP, URL, or Domain to analyze in the Workbench. You can access the following data:
This section contains the Detection Score of the Threat Source, which is the number of security vendors who have flagged the source as risky out of all the security vendors. Along with this, the basic details and the geo info of the Threat Source are also available.
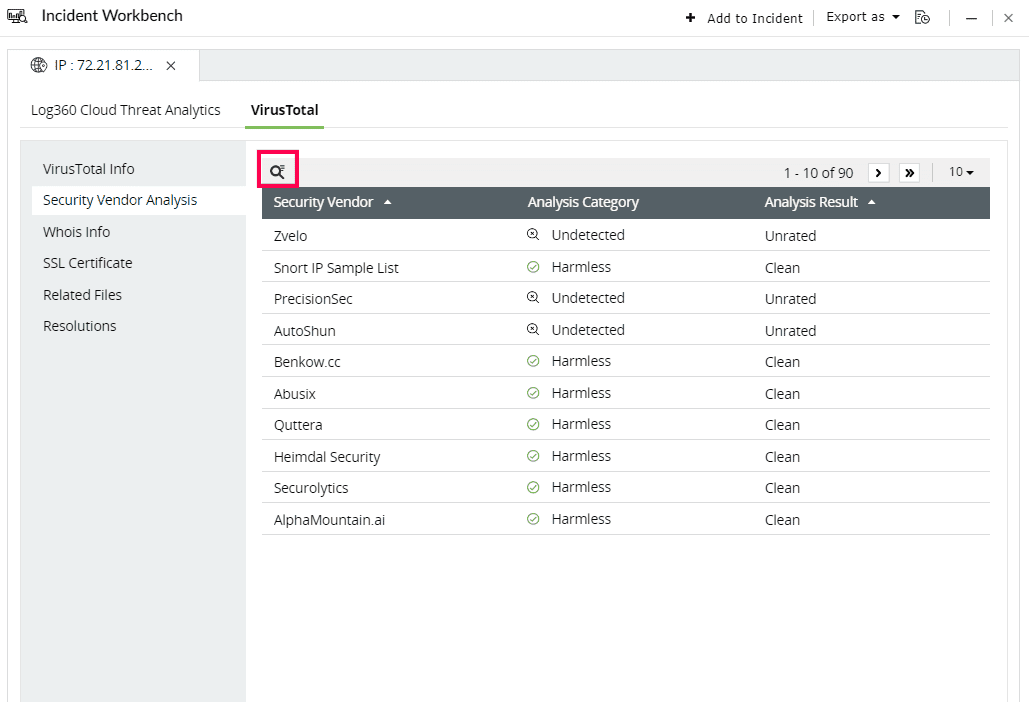
This section contains the individual analysis of 85+ security vendors such as SOCRadar, Fortinet, Forcepoint ThreatSeeker, and ArcSight Threat Intelligence.
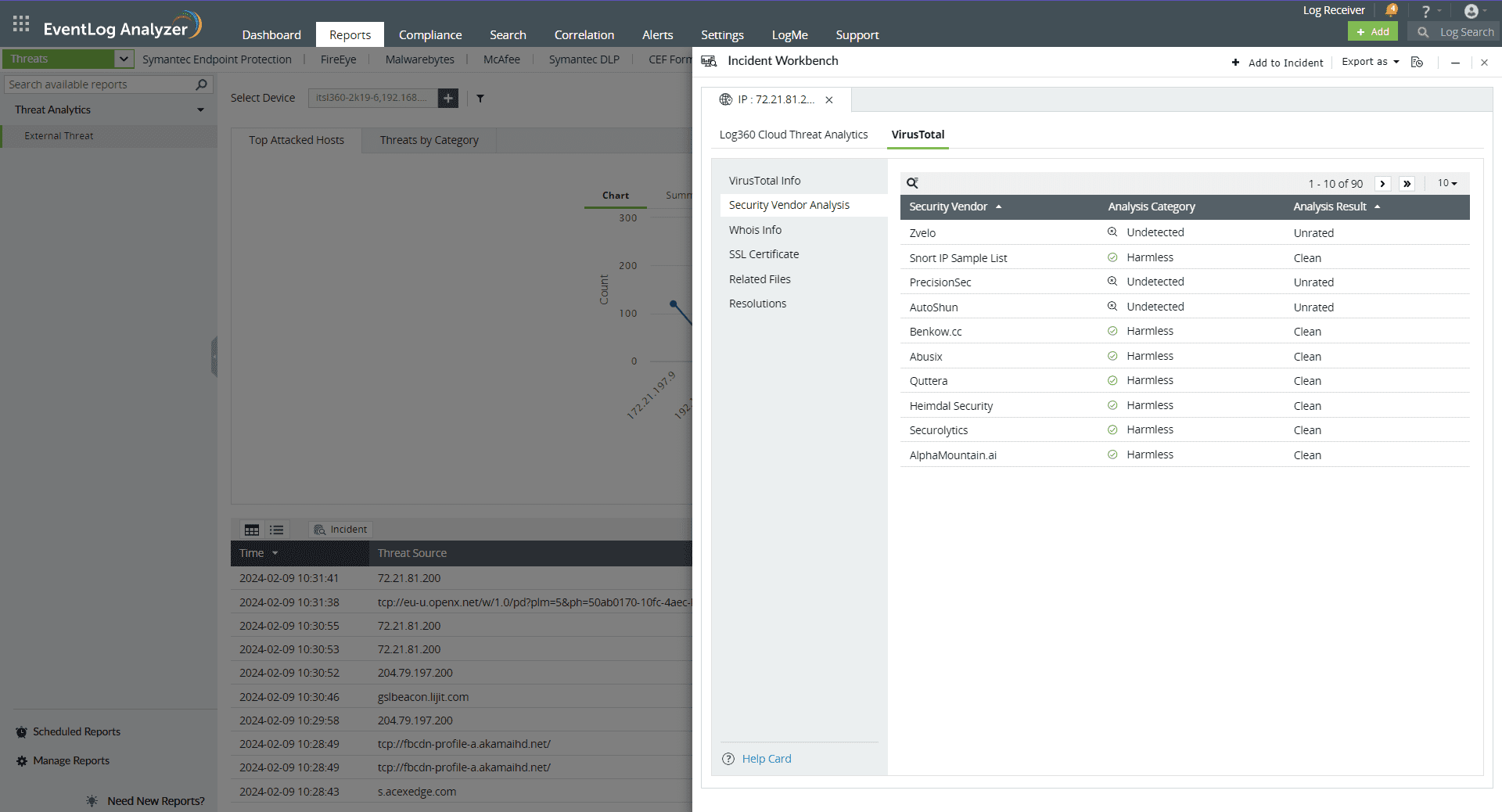
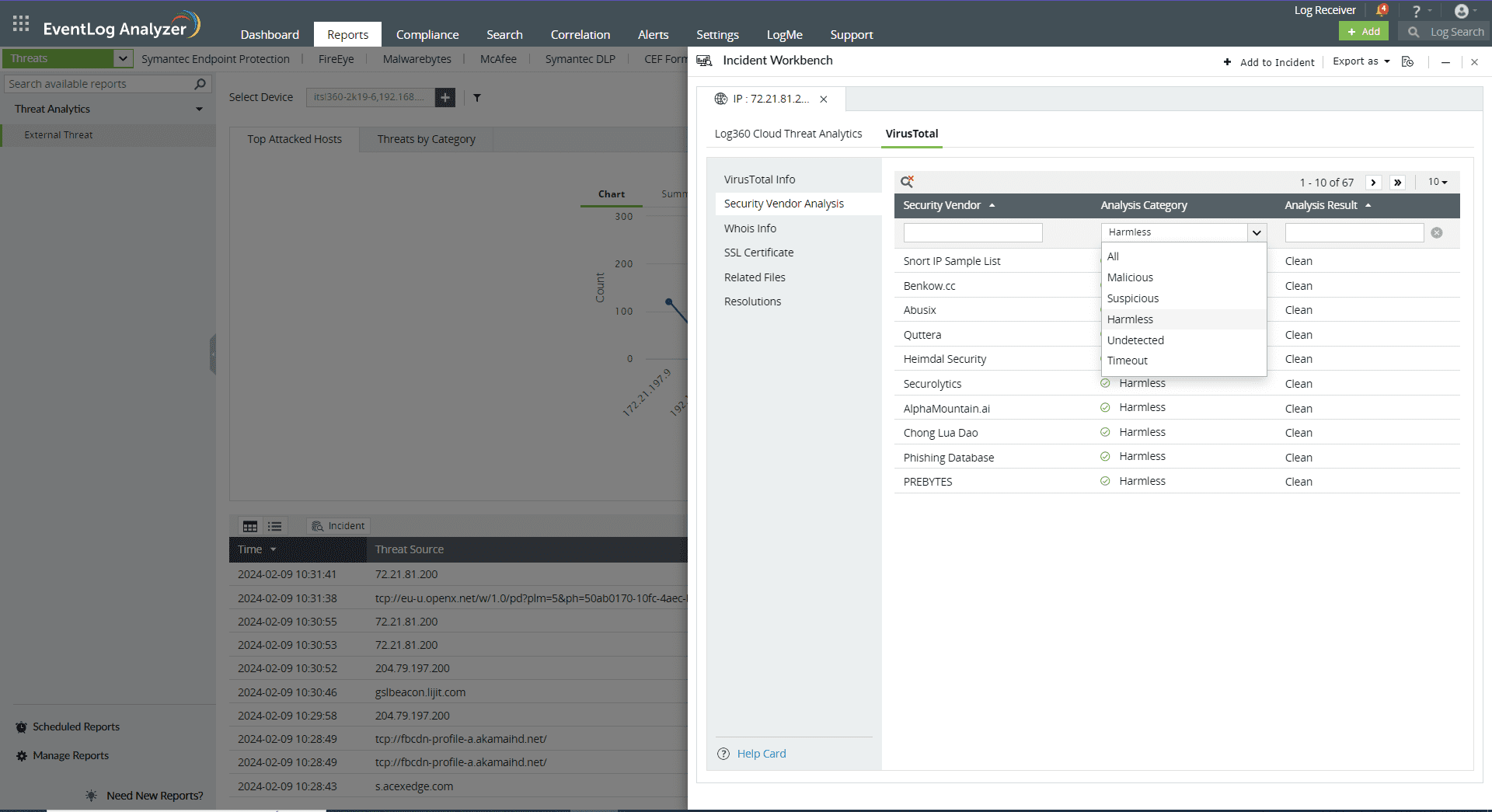
Click on the search icon in the top left corner to filter based on Security Vendor, Analysis Category, and Analysis Result.
Here are the Analysis Categories:
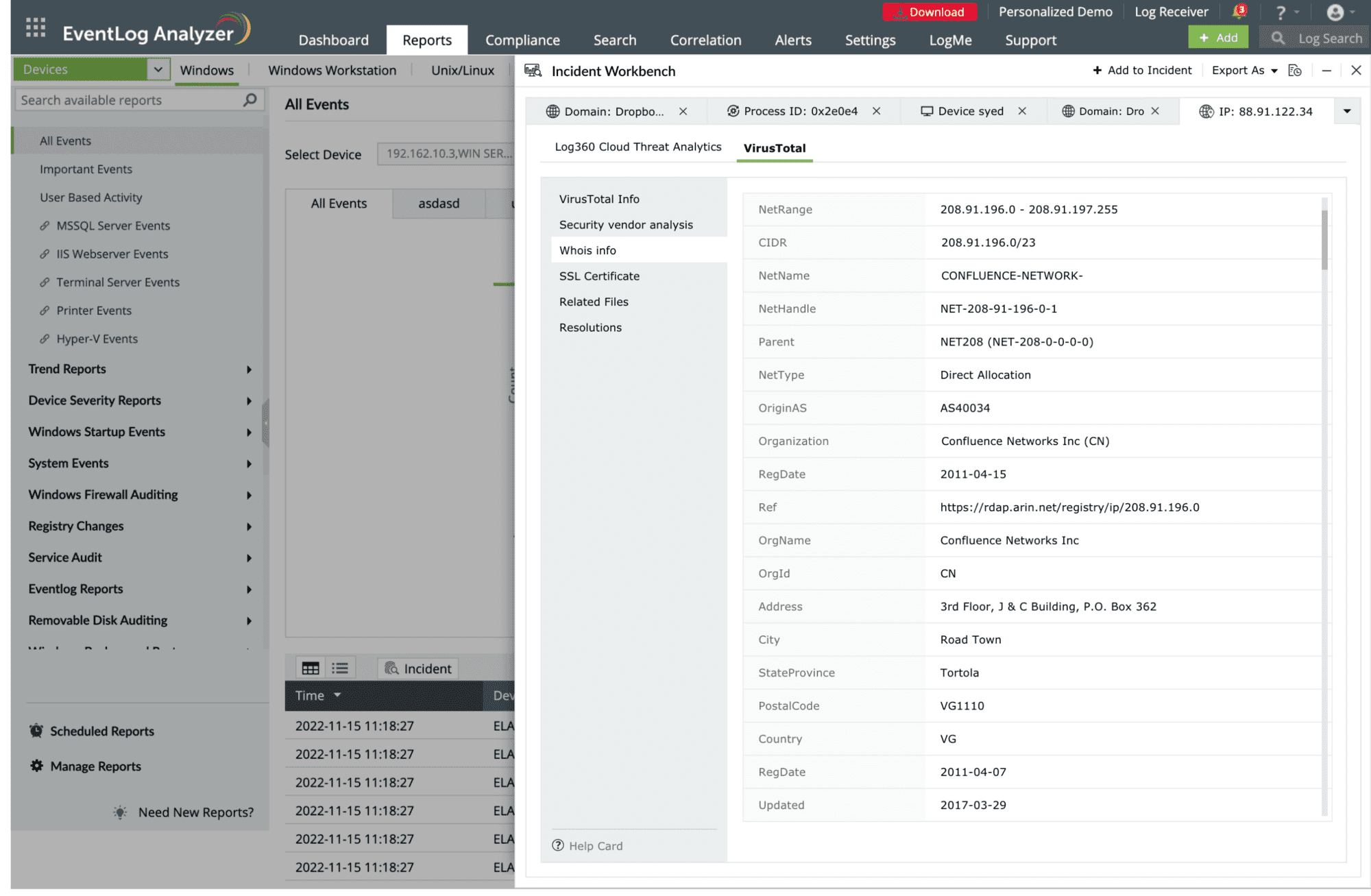
This section contains the Whois information of the threat source domain.
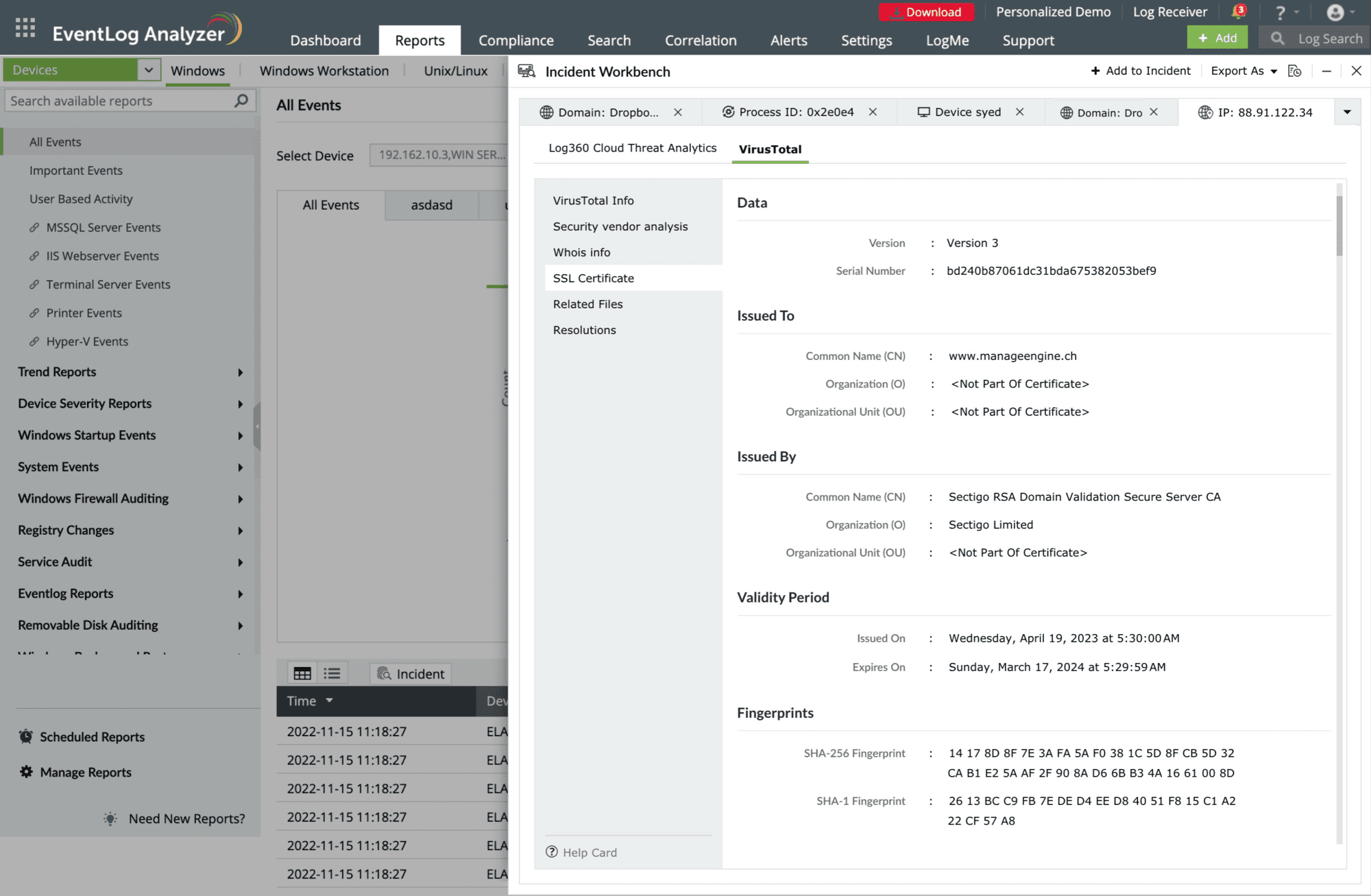
This section contains details of the SSL certificate issued to the Threat Source and who issued it.
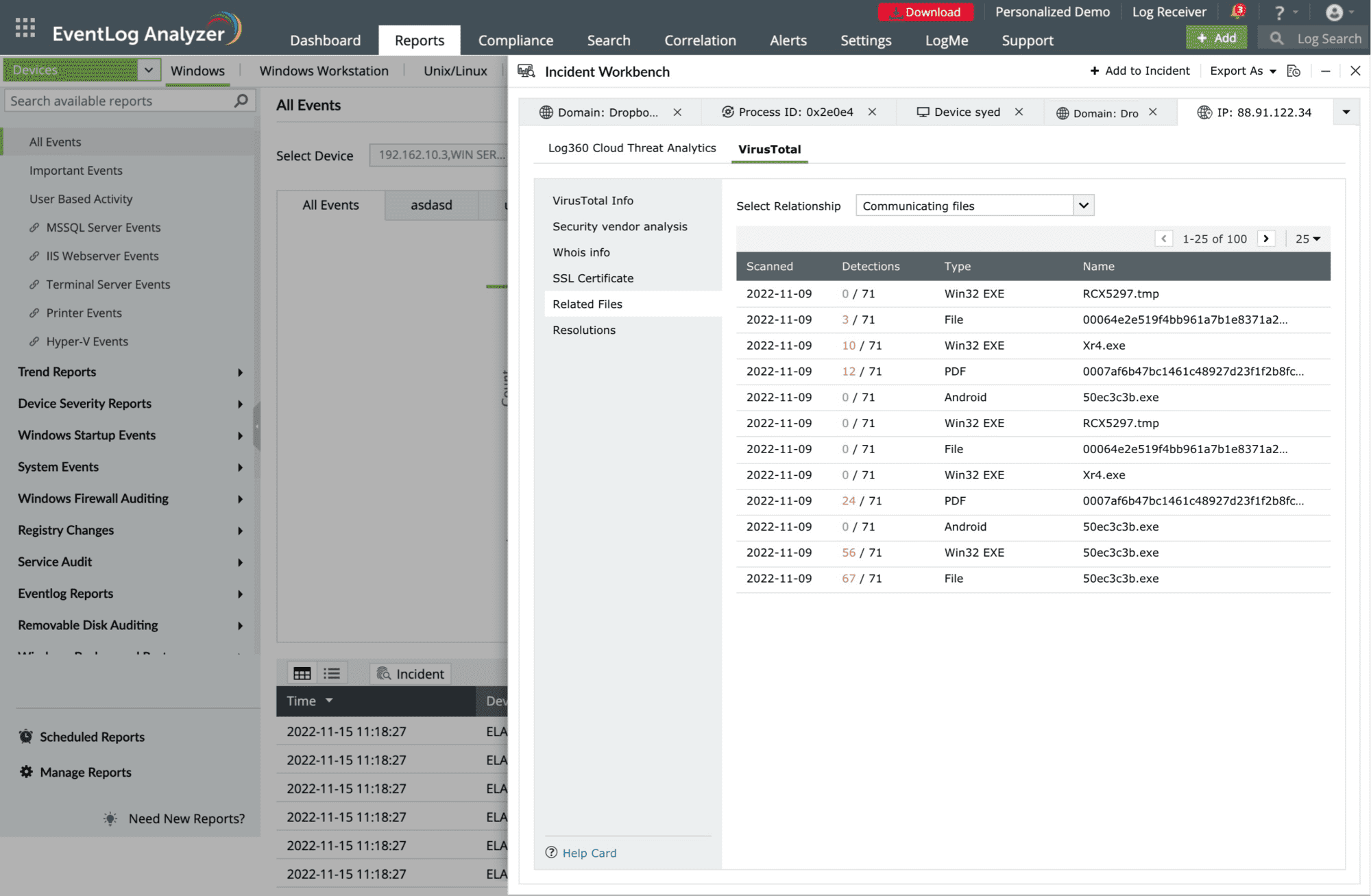
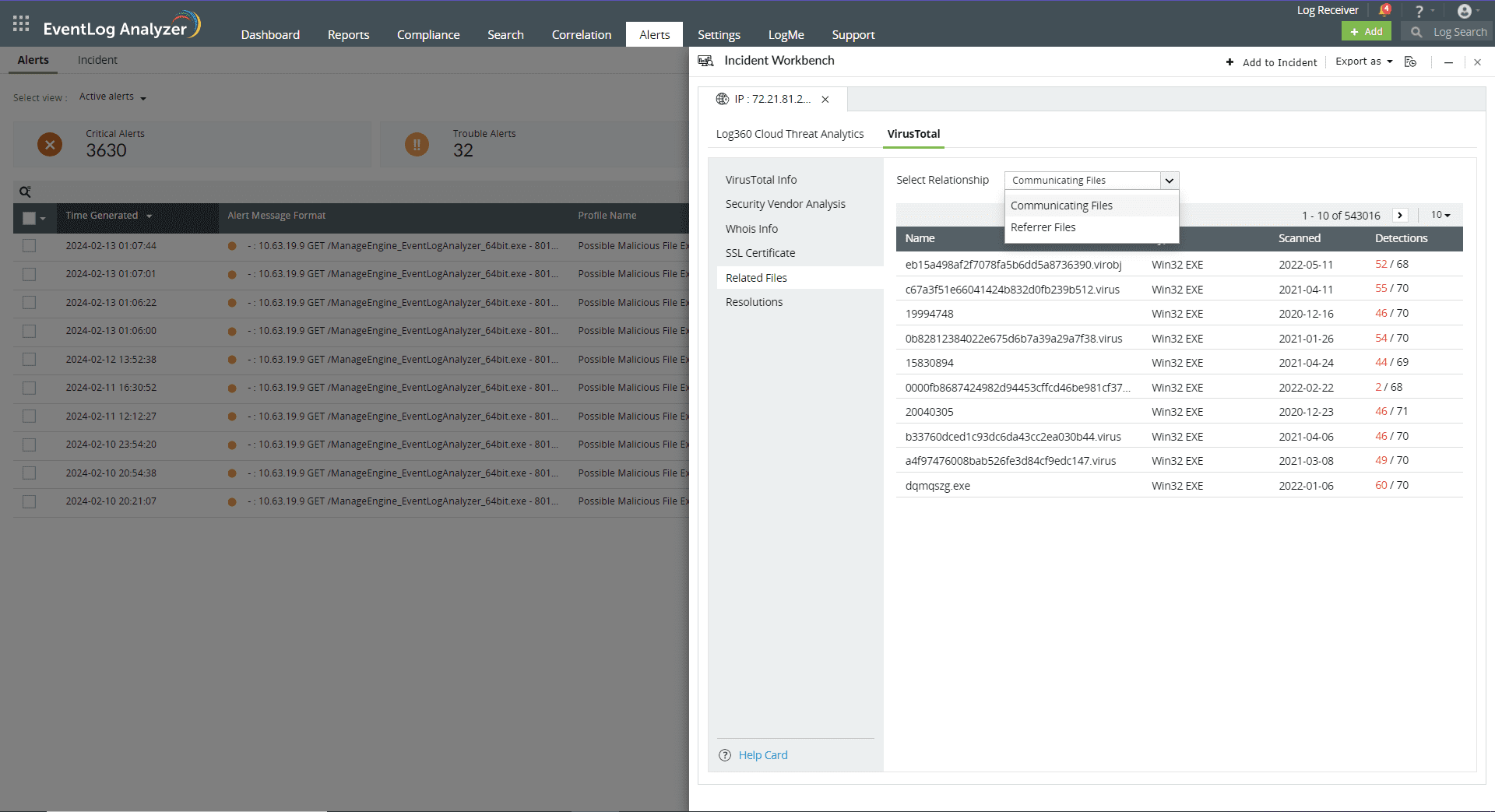
This section maps the relationship of the files to the IP address in following ways:
This section contains the past and current IP resolutions for a particular domain.
Copyright © 2020, ZOHO Corp. All Rights Reserved.