For organizations that depend on the on-premises IT infrastructure and traditional security models, it is easier to verify and authorize everything inside the corporate network, including devices, users, applications, and servers. Users trying to gain access from outside the corporate network are authenticated using virtual private networks (VPNs) and network access control (NAC). With the increasing adoption of the cloud and remote work, the new enterprise architecture is redefining the perimeter. Data is also stored outside of corporate walls, and users access enterprise applications that are located on the cloud, as well as inside their corporate network through various types of devices from locations outside the corporate network.
As the traditional perimeter of the network, with its known points of entries and exits, shifts into something with softer boundary lines, identity is considered the new network perimeter. Identity management will become even more crucial with the adoption of the hybrid cloud and the means of access increasing day by day.
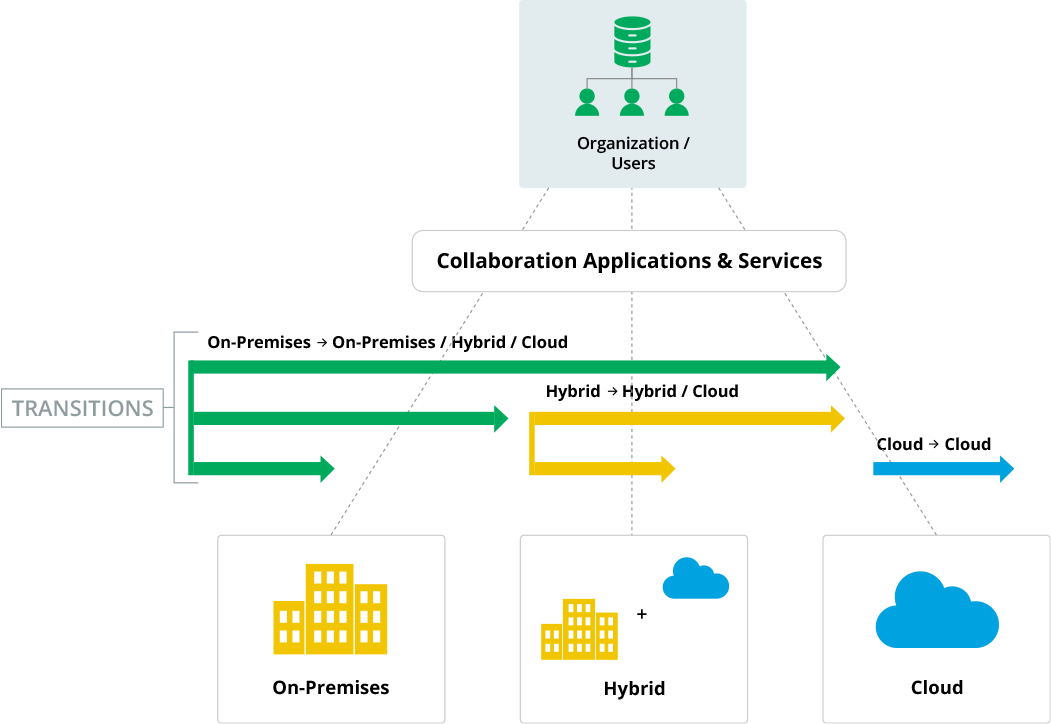
The United States National Institute of Standards and Technology (NIST) defines the hybrid cloud as "a mixed computing, storage, and services environment made up of on-premises infrastructure, private cloud services, and a public cloud, with orchestration among the various platforms." Its primary benefit is agility. Cloud infrastructure is owned, managed, and monitored by the cloud service provider (CSP), which possess a considerable amount of control over data security functions and services within their cloud-hosted infrastructure. Some service providers are not always transparent about their business decisions, which might adversely impact operations for their clients. For example, a service provider might choose to move their data centers locations but not announce this, potentially causing compliance issues. Even differences between vendors platforms create issues for customers wanting to efficiently switch between services, and limits their ability to transition from on-premises data centers to a public cloud, or to a private cloud, and vice versa. A hybrid cloud enables organizations to optimize their cloud connectivity, and maintain flexibility in terms of migrating data and workloads between cloud infrastructures.
As companies embark on application and data modernization, they should consider using a hybrid cloud, as it balances the application and data workload across both platforms.
Hybrid deployments include the benefits of both the cloud and on-premises. They bring innovation, speed, storage, and scalability of the cloud, and regulatory compliance, performance, and data gravity of on-premises in a single platter. Organizations that operate with workloads distributed among multiple data centers and the cloud need to keep pace with emerging trends in digital transformation and IT security. A hybrid cloud deployment can be beneficial as it can effectively enhance performance, flexibility, and security.
With the increased adoption of remote working, organizations are struggling manage IT services efficiently. Enterprises must strategically utilize their resources so that all infrastructures, applications, data, cloud and on-premise deployments are secure and optimized for business continuity. In these situations, global enterprises often prefer a hybrid application for optimizing data placement. The key factors to remember while deploying the hybrid cloud model are:
In the on-premises model, everything within the network perimeter is verified and trusted. Now, as we move towards remote working and modernization programs for cloud-ready infrastructure and the Internet of Things (IoT), the network perimeter is disappearing. With the increasing number of data breaches, enterprises are realizing that the traditional "moat and castle" approach will not work for hybrid models.
The misuse of employee credentials and improper access controls accounts for 42 percent of unauthorized network access, according to research conducted by Cybersecurity Insiders. Unauthorized access is perceived as the single biggest vulnerability to cloud security, and that’s why it’s critical to deploy a comprehensive security management tool designed exclusively for hybrid cloud security. With the right tool, all cloud applications and gateways can be managed and monitored from a single console.
Managing identities, authentication, and access in on-premises infrastructures can be accomplished simply with Microsoft’s Lightweight Directory Access Protocol (LDAP) and Active Directory (AD). However, in the cloud, it’s much more difficult for IT departments to monitor which users are accessing which applications and services. Therefore, most organizations take a practical approach and adopt more Software as a Service (SaaS) applications. Many organizations upgrade their existing applications to a cloud version, and retire obsolete on-premise and legacy versions when possible.
With a portion of the workload placed outside the on-premises data centers, hybrid enterprises should focus on ensuring secure access to every user, application, and device, irrespective of their location. This access should be contextual, which allows IT admins to create access policies for users based on location, IP address, device, etc. In other words, the only way you can succeed on your cloud journey is by deploying the right identity and access management (IAM) solution.
IAM providers can be classified into three categories:
With varied cloud deployment models, organizations need to enforce proper access policies to ensure data security. Traditional IAM strategies are not enough in an ever-evolving hybrid environment. To address this challenge, organizations must build a unified security strategy with hybrid identity management at the center. Hybrid IAM should focus on three main objectives:
As organizations move to the cloud, a significant amount of an organization's data migrates outside the corporate perimeter. To build a security framework that can withstand the dynamic challenges of cloud infrastructure, it’s important to adopt a Zero Trust security model.
Based on the notion "never trust, always verify", the Zero Trust principle addresses security concerns pertaining to remote work, cloud adoption, and bring your own devices (BYOD). Organizations need to monitor the network and verify every user trying to access the corporate resources. Zero Trust adds additional security with real-time contextual authentication where the user or entity is continuously monitored to assess risk against a benchmark (risk score). In case of an anomaly or malicious behavior, it can trigger re-authentication as necessary.
When sensitive applications and critical data are placed across systems, both on-premises and in the cloud, it is highly crucial to fragment data into micro-perimeters or micro-segments. This reduces the attack surface and protects organizational data from the risk of exposure to malware and vulnerabilities.
Cloud adoption boosts digital transformation for organizations embarking on a modernization program. It is crucial to decide which workloads move to the cloud and which stay on-premises. To ensure secure data access management, organizations must perform proper data valuation by assessing the criticality of the workload they are looking to migrate to the cloud. Exploiting workloads that contain sensitive data could wreak havoc if the organization fails to protect them during data breaches.
There are various stages of implementing the Zero Trust security model. A good place to start is enabling MFA along with strong password policies to all applications and devices. SSO ensures a seamless authentication experience by asking users to log-in with a single ID and password for multiple applications, thereby reducing the attack surface. As a best practice, a MFA-enabled VPN should be implemented to access the corporate network.