Child Process Control
Programs that are being executed are referred to as processes. Processes that create another process are referred to as parent processes, and their newly created processes are considered child processes.
Traditional application control generally extends to only parent processes, which in this case is the execution of applications. The permission criteria for the child processes invoked by these applications remain a gray area. Given that creating malicious child processes is a common malware strategy used to exploit the parent application as a vector, the fate of child processes should be held under scrutiny.
However, you can’t just go ahead and block all child processes on a whim. Exclusions based on trust and need must be made to enable the uninterrupted functioning of line-of-business applications. But again, selecting all the extensions that need to be allowed can be cumbersome.
For instance, a software developer using an IDE such as Visual Studio might require many extensions or child processes to run. Sysadmins, who deploy child process control policies, may not be fully aware of every employee's prerequisites, and even if they were, it would be impossible for them to select every single extension manually. Instead, the approach can be reversed to enable selection of a set of parent applications and automatically allowing all their invoked child processes.
How does Application Control Plus' Child Process Control work?
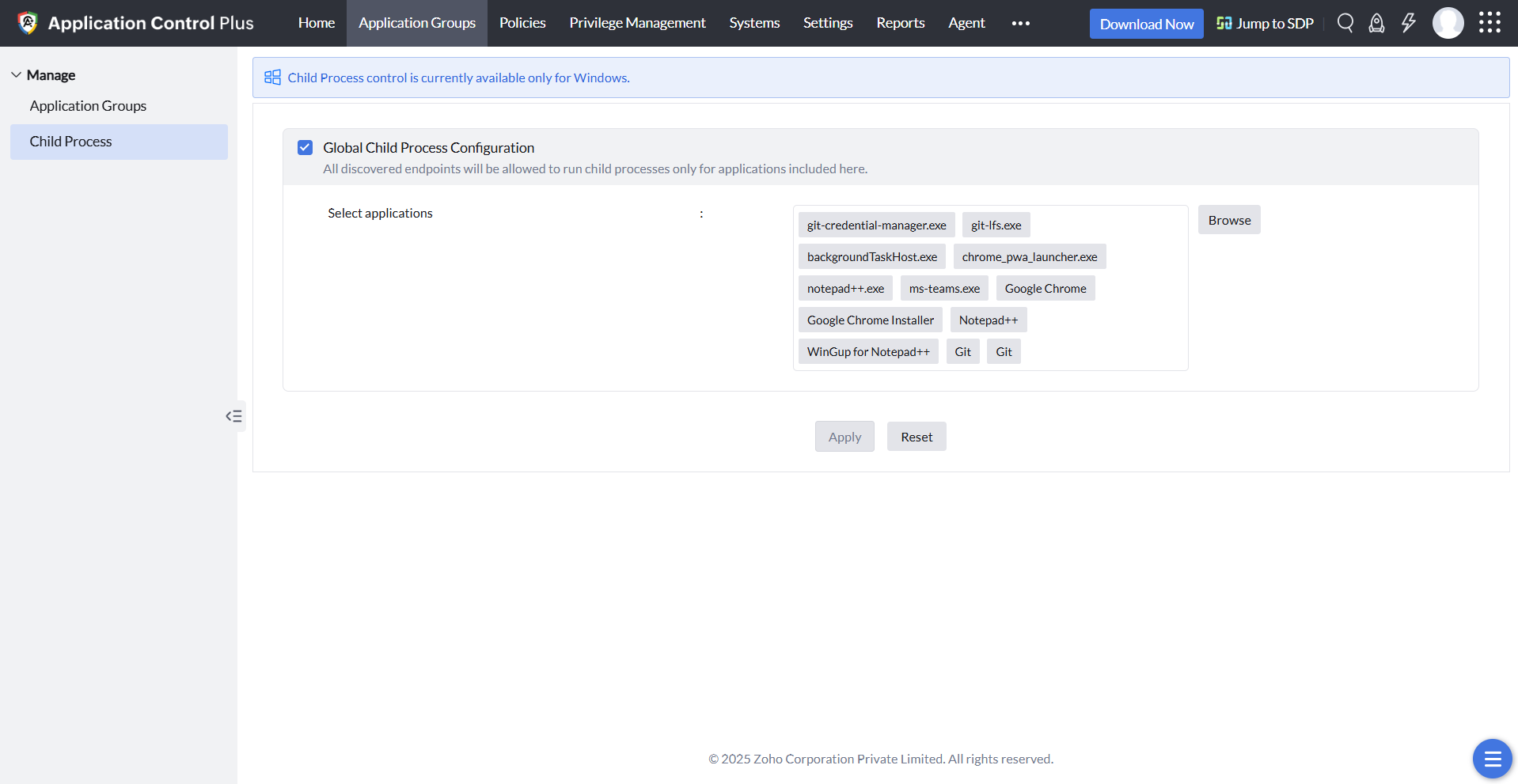
ManageEngine Application Control Plus enables its users to control the child processes of the applications that they allow. Users can globally configure the child process control policy, where they can select all the applications they trust and deem necessary. Only child processes that are invoked by these selected applications and the allowlisted applications will be allowed to run in all the discovered user devices, while the rest will remain blocked.
If the chosen applications are configured to run with elevated privileges using the Endpoint Privilege Management feature, then their child processes can also be executed with the same privileges.
The "Restrict Child Process Elevation" feature lets you run applications with elevated privileges, but it prevents any child processes from inheriting those elevated privileges.
Note: In Audit Mode, all applications and their child processes will be allowed to run unless specifically blocklisted.