- Home
- SIEM use cases
- BloodHound and AD Enumeration
How to detect BloodHound and Active Directory enumeration
In this page
Threat snapshot
Active Directory enumeration is the reconnaissance phase that every sophisticated attack against an AD environment goes through. Before an attacker can escalate privileges, move laterally, or deploy ransomware, they need to understand the environment: which accounts exist, which groups have administrative rights, which machines are domain-joined, which service accounts have delegated permissions, and which attack paths exist from their current position to Domain Admin.
BloodHound changed the economics of this reconnaissance permanently. Before BloodHound, mapping AD attack paths required hours of manual LDAP queries and careful analysis. BloodHound automated that analysis entirely, ingesting bulk AD data collected by its companion tool SharpHound and producing a graph-based visualization of every privilege escalation path in the domain within minutes. An attacker who runs SharpHound from a single compromised workstation with a standard domain user account now has a complete map of the shortest path to Domain Admin before the SOC has even noticed the initial compromise.
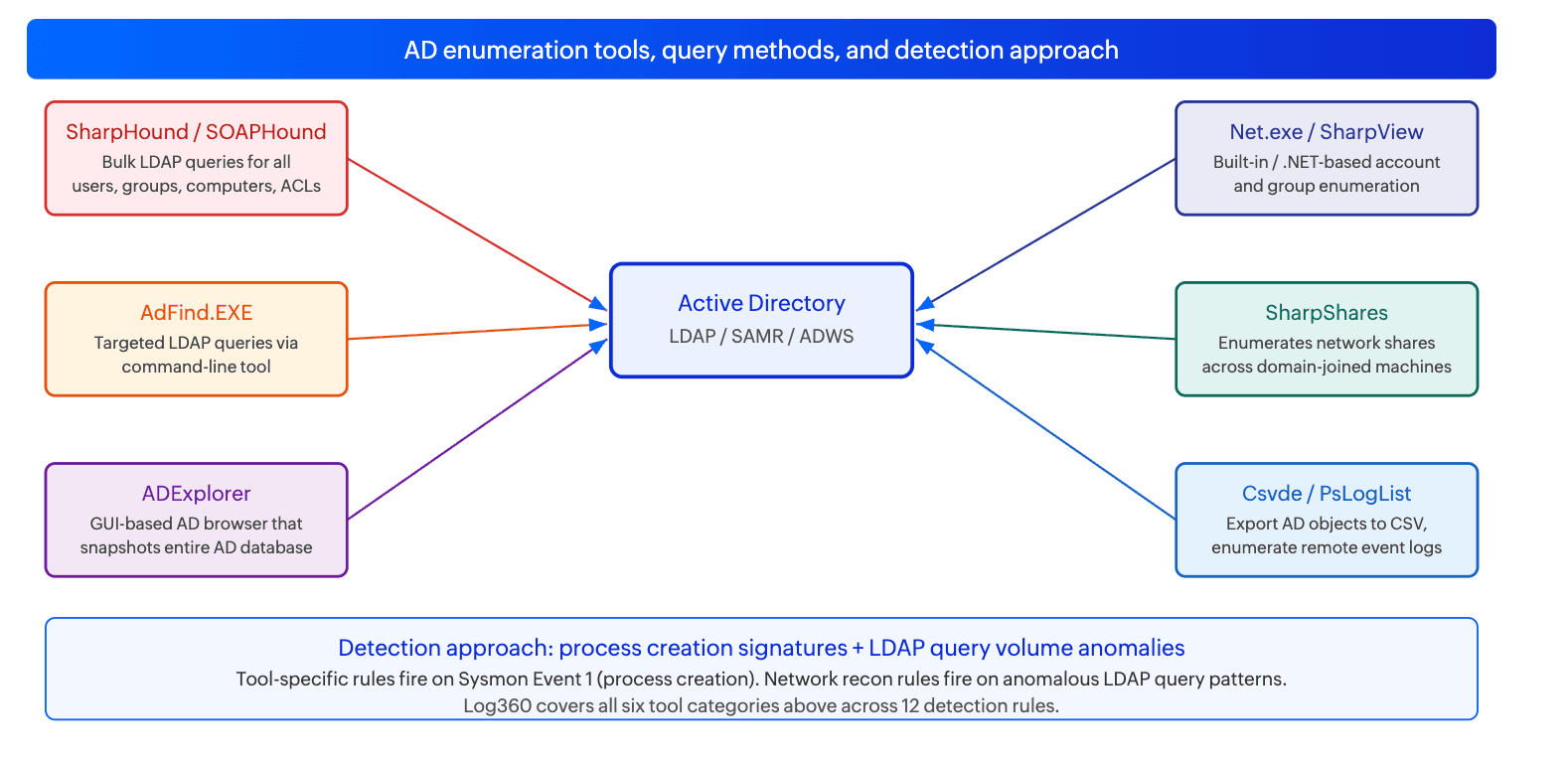
What is less well understood is that BloodHound and SharpHound are not the only tools in this category. AdFind, SOAPHound, SharpView, net.exe, and ADExplorer all perform AD enumeration using different methods and leave different log signatures. A detection strategy that only looks for SharpHound process creation will miss the majority of AD enumeration activity in practice. This page covers the full spectrum of enumeration tooling and the detection rules Log360 uses to catch each variant.
AD enumeration, at a glance
| Severity | High |
| Category | Identity & Access |
| Tools covered | BloodHound / SharpHound, SOAPHound, AdFind, ADExplorer, SharpView, SharpShares, net.exe, csvde.exe, PsLogList, AD Web Services connections |
| MITRE ATT&CK tactic | TA0007 (Discovery) |
| MITRE techniques | T1087 (Account Discovery), T1087.002 (Domain Account Discovery), T1087.001 (Local Account Discovery) |
| Platforms covered | Windows, Active Directory |
| Log360 detection rules |
|
| SOC maturity level | Level 2 (investigation) |
| Compliance mapping | NIST CSF DE.AE-1, PCI-DSS 11.5, HIPAA Section 164.312(b), ISO 27001 A.12.4 |
How AD enumeration attacks work
AD enumeration is not a single technique but a collection of methods for querying the directory to understand its structure. Different tools use different query mechanisms, leave different log signatures, and provide different types of information to the attacker. Understanding the method determines the detection approach.
SharpHound and SOAPHound: bulk LDAP collection for BloodHound
SharpHound is the data collection component of the BloodHound toolkit. When executed, it performs a series of bulk LDAP queries against the domain controller to retrieve all users, computers, groups, group memberships, organizational units, GPOs, and access control entries. It also queries each domain-joined machine via SMB and RPC to map local administrators and session information. The collected data is written to a set of JSON files that are ingested by the BloodHound analysis application to produce an attack path graph.
SOAPHound is a newer alternative to SharpHound that performs the same enumeration but uses the Active Directory Web Services (ADWS) interface instead of LDAP. ADWS operates on TCP port 9389 and uses a SOAP-based protocol, which means it bypasses LDAP-based detection and monitoring tools. For environments that are not monitoring ADWS connections, SOAPHound enumeration is largely invisible. The Uncommon Connection to Active Directory Web Services and HackTool - SOAPHound Execution rules address this gap directly.
Log signals: Sysmon Event 1 with SharpHound or SOAPHound binary signatures. High-volume LDAP queries from a single non-DC source within a short time window (SharpHound's bulk collection is characteristically loud in LDAP logs). Network connections to TCP 9389 from non-standard hosts (SOAPHound via ADWS).
AdFind: targeted LDAP queries via command-line
AdFind.exe is a standalone command-line LDAP query tool that has been used in AD enumeration for over a decade. Unlike SharpHound, which performs a comprehensive collection run, AdFind is used for targeted queries: finding specific user attributes, listing group memberships, querying for accounts with specific properties such as unconstrained delegation, or enumerating organizational unit structures. AdFind does not require installation and runs from any accessible path, making it a living-off-the-land-adjacent tool that has historically been underdetected.
AdFind is explicitly named in multiple ransomware operator playbooks (including leaked Conti documentation) as a standard pre-ransomware enumeration tool. Its presence on a machine that is not a known IT administration workstation is a high-confidence indicator of active attack reconnaissance.
Log signals: Sysmon Event 1 with AdFind.exe process creation. Common AdFind command-line patterns include -b dc=domain,dc=com -f objectcategory=computer for computer enumeration and -b cn=users -f objectcategory=person for user enumeration.
ADExplorer: GUI-based AD snapshot
ADExplorer is a Sysinternals tool from Microsoft that provides a graphical interface for browsing Active Directory. While legitimate in IT administration contexts, attackers use its snapshot feature to capture the entire AD database to a local file in a single operation. An ADExplorer snapshot contains all AD objects, attributes, and relationships in a format that can be analyzed offline without any further network connectivity. This makes it particularly useful for exfiltration: the attacker takes the snapshot, exfiltrates the file, and analyzes the AD structure at leisure without generating any further LDAP traffic. Two rules cover this: one for standard ADExplorer database snapshot usage and one for the pattern identified as suspicious based on context.
Log signals: Sysmon Event 1 with ADExplorer process creation and the -snapshot argument. File creation events for .dat files in user-writable paths following ADExplorer execution.
Net.exe, SharpView, SharpShares, Csvde, and PsLogList
Net.exe is a Windows built-in utility that can enumerate local and domain groups, users, and sessions. While entirely legitimate in isolation, a pattern of net.exe commands targeting domain group membership (net group "Domain Admins" /domain, net user /domain) executed from a non-administrative context within a short window is characteristic of manual or scripted AD reconnaissance. SharpView is a .NET reimplementation of PowerView that performs the same queries but through a compiled binary rather than a PowerShell script, making it harder to detect via PowerShell script block logging.
SharpShares enumerates network file shares across all domain-joined machines, providing the attacker with a map of accessible data repositories. Csvde.exe is a Windows built-in that exports AD objects to CSV files, and PsLogList is a Sysinternals tool for remotely reading event logs from other machines, both of which are abused for AD data collection in the reconnaissance phase.
Log signals: Sysmon Event 1 for SharpView, SharpShares, and PsLogList process creation. Windows process creation audit (Event 4688) for net.exe with domain enumeration arguments. Sysmon Event 1 for csvde.exe with arguments indicating bulk AD object export.
Real-world campaigns
Conti ransomware: AdFind as standard pre-encryption reconnaissance
The 2021 Conti ransomware playbook leak provided a rare inside view of how a major ransomware operation structures its AD enumeration phase. The leaked documentation explicitly references AdFind.exe as the standard tool for domain reconnaissance, with specific command-line examples for enumerating domain controllers, all computers, all users, organizational unit structures, and trust relationships. The enumeration typically occurs within the first two hours of domain access, before any lateral movement begins, and the output is used to identify the shortest path to domain-wide ransomware deployment. The Conti playbook's reliance on AdFind is why the PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE rule is particularly valuable: it directly catches a technique confirmed in documented ransomware operator tradecraft.
APT campaigns: SharpHound and SOAPHound for pre-APT attack path mapping
Multiple APT groups have been documented using BloodHound and SharpHound as standard tools in their post-compromise AD reconnaissance phase. The appeal is the same as for ransomware operators: SharpHound automates what would otherwise require extensive manual LDAP work and delivers a complete privilege escalation map within minutes. More recently, sophisticated threat actors have shifted to SOAPHound specifically to avoid LDAP-based detection deployed in response to SharpHound detections, underlining why ADWS-based detection (Uncommon Connection to Active Directory Web Services and HackTool - SOAPHound Execution) is a necessary complement to process-level detection.
Tool reference table
| Tool | Query method | What it collects | Log360 detection rule |
|---|---|---|---|
| SharpHound | Bulk LDAP, SMB, RPC | All users, computers, groups, ACLs, sessions, local admins | Network Reconnaissance Activity (LDAP volume), AD Privileged Users or Groups Reconnaissance |
| SOAPHound | ADWS (TCP 9389, SOAP) | Same as SharpHound but via ADWS to bypass LDAP monitoring | HackTool - SOAPHound Execution, Uncommon Connection to Active Directory Web Services |
| AdFind.exe | LDAP command-line | Targeted queries: delegated accounts, group memberships, OUs, trusts | PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE |
| ADExplorer | LDAP (full snapshot) | Entire AD database snapshot to local file for offline analysis | Active Directory Database Snapshot Via ADExplorer, Suspicious Active Directory Database Snapshot Via ADExplorer |
| SharpView | .NET LDAP (PowerView equivalent) | Users, groups, computers, ACLs, shares, sessions | SharpView Detection |
| SharpShares | SMB share enumeration | All accessible network shares across domain machines | SharpShares Detection |
| Net.exe | SAMR / LDAP (built-in) | Domain groups, users, computers via built-in Windows tool | Suspicious Group And Account Reconnaissance Activity Using Net.EXE |
| Csvde.exe | LDAP export (built-in) | Bulk AD object export to CSV for offline analysis | Active Directory Structure Export Via Csvde.EXE |
| PsLogList | Remote Event Log API | Event logs from remote machines for session and logon history | Suspicious Use of PsLogList |
Business impact
- Enumeration is the prerequisite for everything that follows. An attacker who has not enumerated the AD environment is operating blind. An attacker who has run SharpHound has a complete map of every privilege escalation path, every misconfiguration, and every high-value target in the domain. Detecting and stopping enumeration before it completes denies the attacker the intelligence they need to execute targeted follow-on attacks.
- Low bar to execute, high value of output. Every tool in this category requires only a standard domain user account to run. No elevated privileges, no special access, no vulnerability exploitation. A single compromised employee workstation is sufficient to run SharpHound and collect a complete AD map. This makes enumeration one of the earliest and most reliable signals of an active intrusion beyond the initial foothold phase.
- Offline analysis eliminates time pressure. Tools like ADExplorer's snapshot feature and Csvde export allow the attacker to collect the entire AD dataset and exfiltrate it for offline analysis, meaning subsequent attack planning generates no further AD query traffic. Detection after the snapshot is taken but before exfiltration is the last reliable opportunity to prevent the attacker from having a complete AD map.
- Enumeration feeds downstream attacks at scale. SharpHound output directly feeds BloodHound's attack path analysis, which identifies Kerberoastable accounts, accounts with unconstrained delegation, users with DCSync rights, and ACL abuse paths. Each of these findings becomes a discrete exploitation opportunity. A single SharpHound run can identify dozens of attack paths that an attacker can pursue independently over days or weeks.
Detecting BloodHound and AD enumeration with Log360
Log360's 12 detection rules cover all major AD enumeration tools across two detection approaches: process creation signatures (catching the tool at the moment of execution via Sysmon Event 1) and behavioral anomaly rules (catching unusual LDAP query patterns, ADWS connections, and reconnaissance activity that may not match a specific tool signature). For process-creation-based rules, Sysmon must be deployed on domain-joined endpoints with process creation logging (Event 1) forwarding to Log360. For LDAP and ADWS-based rules, Active Directory audit logs and network connection logs must be forwarding from domain controllers.
BloodHound and SOAPHound detection
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| HackTool - SOAPHound Execution | Trouble | Active Directory | T1087 | SOAPHound binary execution detected via Sysmon process creation. SOAPHound is specifically designed to bypass LDAP-based BloodHound detection by using the ADWS interface instead. Its process creation signature is highly distinctive and has no legitimate use in production environments outside of authorized assessments. |
| Uncommon Connection to Active Directory Web Services | Trouble | Active Directory | T1087 | A network connection to TCP port 9389 (ADWS) on a domain controller from a host that does not normally use ADWS. ADWS is used by tools like PowerShell Active Directory module, RSAT, and SOAPHound. Connections from non-admin workstations or from machines that have never previously connected to ADWS are a strong indicator of SOAPHound or similar ADWS-based enumeration. |
| Network Reconnaissance Activity | Trouble | Active Directory | T1087 | Anomalous LDAP query volume or pattern from a single non-DC source, consistent with SharpHound or similar bulk LDAP collection tools. This rule provides coverage for SharpHound and other LDAP-based enumeration tools that may not match a specific process creation signature but produce a characteristic high-volume LDAP query pattern against the domain controller. |
| AD Privileged Users or Groups Reconnaissance | Trouble | Active Directory | T1087.002 | LDAP queries specifically targeting privileged user accounts and administrative groups such as Domain Admins, Enterprise Admins, Schema Admins, and Protected Users. This targeted query pattern is characteristic of an attacker who has already completed broad enumeration and is now focusing on identifying the highest-value accounts for subsequent attack steps. |
AdFind and ADExplorer detection
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE | Trouble | Active Directory | T1087.002 | AdFind.exe execution with command-line arguments consistent with AD enumeration: querying for users, computers, groups, OUs, trust relationships, or accounts with special properties such as unconstrained delegation. AdFind is explicitly referenced in documented ransomware operator playbooks (Conti, Ryuk predecessors) as a standard pre-encryption enumeration tool. |
| Active Directory Database Snapshot Via ADExplorer | Trouble | Active Directory | T1087.002 | ADExplorer executed with the -snapshot argument, creating a local copy of the entire AD database. An ADExplorer snapshot contains all AD objects and attributes and can be analyzed offline with BloodHound or similar tools without generating any further LDAP traffic. The snapshot creation event is the last reliable detection point before the data is exfiltrated. |
| Suspicious Active Directory Database Snapshot Via ADExplorer | Trouble | Active Directory | T1087.002 | ADExplorer snapshot creation in a context identified as suspicious based on the executing account, source machine, or timing characteristics. Complements the standard ADExplorer snapshot rule with additional behavioral context to reduce false positives while maintaining coverage of anomalous snapshot creation patterns. |
Built-in and Sysinternals tool abuse
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| Active Directory Structure Export Via Csvde.EXE | Trouble | Windows | T1087.002 | Csvde.exe executed with export arguments, producing a CSV file containing bulk AD object data. Csvde is a Windows built-in that requires no installation and is frequently overlooked by detection strategies focused on third-party tools. AD export via Csvde from a non-admin account or non-standard location is a reliable indicator of reconnaissance activity. |
| Suspicious Group And Account Reconnaissance Activity Using Net.EXE | Trouble | Active Directory | T1087.001 | Net.exe executed with domain enumeration arguments in a pattern consistent with automated or manual reconnaissance: net group /domain, net user /domain, net group "Domain Admins" /domain, or rapid succession of multiple net commands targeting different domain groups. Single net commands are common; a burst targeting multiple domain groups in rapid succession indicates deliberate reconnaissance. |
| Suspicious Use of PsLogList | Trouble | Windows | T1087 | PsLogList executed to remotely read event logs from one or more domain-joined machines. Attackers use PsLogList to gather logon session information, identifying which accounts have recently authenticated to which machines. This supplements the user and group data collected via LDAP by adding session context that reveals where privileged accounts are currently active. |
| SharpView Detection | Critical | Windows | T1087 | SharpView binary execution detected via Sysmon process creation. SharpView is a compiled .NET equivalent of PowerView, providing the same AD enumeration capabilities but in binary form to avoid PowerShell-based detection controls. It has no legitimate administrative use and its presence indicates active post-compromise reconnaissance. Critical severity due to the breadth of AD data it can collect. |
| SharpShares Detection | Critical | Windows | T1087 | SharpShares binary execution detected via Sysmon process creation. SharpShares enumerates all accessible SMB shares across every domain-joined machine, providing the attacker with a comprehensive map of file storage locations for data staging, lateral movement planning, and identifying sensitive data repositories. Critical severity due to the breadth of network access it involves. |
Attack chain visibility
AD enumeration is not a standalone attack; it is the reconnaissance phase of a broader intrusion. The sequences below show what the enumeration phase looks like in the logs and how it connects to the lateral movement and privilege escalation phases that follow.
Sequence A: SharpHound collection followed by Kerberoasting
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | Sysmon Event 1 (Process Creation) | SharpHound.exe executes on the compromised workstation. The binary may be renamed (a common evasion) but process creation signatures and command-line patterns match. Network Reconnaissance Activity rule fires on the subsequent burst of LDAP queries to the DC. | T+0 |
| 2 | AD audit logs (LDAP query volume) | A burst of LDAP queries originates from the workstation's IP targeting the DC: queries for all computer objects, all user objects, all group memberships, and all ACL entries. The query volume and pattern is inconsistent with normal workstation behavior and consistent with bulk collection. | T+0 to T+5 min |
| 3 | Sysmon Event 1 (Process Creation) | Rubeus.exe or Invoke-Kerberoast executes on the same host. The attacker has used the SharpHound output to identify Kerberoastable service accounts and is now requesting their TGS tickets for offline cracking. The enumeration phase directly feeds the credential access phase. | T+15 to T+60 min |
| 4 | Windows Security Event 4769 (Kerberos TGS) | TGS requests for service accounts with SPNs set, using RC4 encryption (encryption type 0x17), which is the Kerberoasting signature. Multiple TGS requests for different service accounts in rapid succession from the same source confirms active Kerberoasting following the enumeration phase. | T+15 to T+60 min |
Sequence B: AdFind reconnaissance in ransomware pre-positioning
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | Sysmon Event 1 (Process Creation) | AdFind.exe executes with domain computer enumeration arguments. PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE rule fires. This is the standard Conti/Ryuk playbook reconnaissance step: the attacker is mapping domain-joined machines before beginning lateral spread. | T+0 |
| 2 | Sysmon Event 1 (Process Creation) | AdFind re-executes with group membership arguments targeting Domain Admins and Enterprise Admins. AD Privileged Users or Groups Reconnaissance rule fires. The attacker now has a list of privileged accounts to target for credential theft or to avoid when deploying ransomware to prevent immediate remediation. | T+5 min |
| 3 | Windows Security Event 4624 (Type 3 logon) | Network logons begin from the source host to multiple domain-joined machines. The attacker is using the AdFind output to navigate the domain, connecting to machines identified as high-value targets (file servers, backup servers, domain controllers). | T+1h to T+4h |
Investigation playbook
When an AD enumeration detection rule fires, the most important question is not just "which tool ran" but "what did the attacker learn and what are they likely to do next." Enumeration is a means to an end; the investigation goal is to understand the scope of information collected and anticipate the next attack phase before it starts.
Step 1: Triage - identify the tool and scope of collection
| Rule that fired | Tool and collection method | What the attacker now knows | First action |
|---|---|---|---|
| Network Reconnaissance Activity or AD Privileged Users or Groups Reconnaissance | SharpHound or similar LDAP-based bulk collection | Complete AD structure: all users, groups, computers, ACLs, attack paths to Domain Admin | Check source IP for SharpHound process creation via Sysmon. Determine if collection completed. Identify the compromised account and workstation. |
| HackTool - SOAPHound Execution or Uncommon Connection to AD Web Services | SOAPHound via ADWS (bypass LDAP monitoring) | Same as SharpHound. Attacker chose SOAPHound specifically to avoid LDAP detection. | Isolate the host. The attacker is aware of LDAP monitoring and has adapted. Treat as a more sophisticated threat actor. Check for prior SharpHound attempts on the same host that may have triggered detection. |
| PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE | Targeted LDAP queries via AdFind | Targeted AD information based on the specific AdFind arguments used. Check command-line for what was queried. | Review the full AdFind command line from Sysmon Event 1. Identify what the attacker queried. If querying for domain controllers or delegated accounts, treat as pre-lateral-movement intelligence gathering. |
| Active Directory Database Snapshot Via ADExplorer (either variant) | Full AD database snapshot to local file | Entire AD database, available for offline analysis. May already be staged for exfiltration. | Determine if the snapshot file has been exfiltrated. Check network logs for outbound transfers following the snapshot creation. Identify the file path from the Sysmon process creation log. |
| SharpView Detection or SharpShares Detection | Compiled .NET enumeration tool | SharpView: same as SharpHound. SharpShares: all accessible network shares across domain. | Treat as active post-compromise reconnaissance. Identify the compromised account and check UEBA scores. Determine if other enumeration tools ran on the same host. |
| Suspicious Group And Account Reconnaissance Activity Using Net.EXE | Built-in net.exe with domain arguments | Domain group memberships, specifically which accounts are in privileged groups. | Check the specific net commands run. Focus on whether Domain Admins or other privileged groups were targeted. A single net command is low signal; multiple commands in rapid succession from the same session is high signal. |
Step 2: Determine the scope of what was collected
- For process-based detections, retrieve the full command-line arguments from the Sysmon Event 1 record. The command line tells you exactly what the tool was configured to collect: all objects (broad collection indicating pre-BloodHound ingestion) or specific attributes (targeted reconnaissance indicating a more specific objective).
- For SharpHound or SOAPHound, check whether JSON output files were created on the host (file creation events in Sysmon). The presence of the output files confirms collection completed. The absence may indicate the collection was interrupted by the detection and response, which is a meaningful win.
- For ADExplorer snapshots, check the file path and size of the created snapshot file. A multi-gigabyte .dat file confirms a complete AD snapshot was taken. Check immediately for outbound network transfers of that file size or the specific file path.
- Check whether multiple enumeration tools ran on the same host in the same session. A host that ran AdFind followed by SharpHound followed by Rubeus within an hour is further along in the attack chain than one that only ran a single tool.
Step 3: Investigate using the Incident Workbench
- Click on the source hostname or compromised account username in the alert to open the Incident Workbench. Use the Process analytics tab to view the full process tree on the source host. This shows what spawned the enumeration tool, what ran before it (indicating how the attacker got to that host), and what ran after it (indicating what they did with the collected data).
- Use the User analytics tab to check the UEBA risk score and activity baseline for the account that ran the enumeration tool. A standard domain user account suddenly running SharpHound or AdFind is a maximum-anomaly behavioral event. The User analytics tab also shows recent logon history, helping identify whether the account was used from unusual locations or at unusual times.
- Use Advanced Threat Analytics on any external IPs involved (for example, if the host made connections to external IPs following the enumeration run, which may indicate C2 communication or data exfiltration).
- Save the Incident Workbench session to an incident. The process tree and user activity timeline from this session are the primary evidence record for determining the full scope of the compromise.
Step 4: Anticipate the next attack phase
- If SharpHound or SOAPHound completed collection, the attacker now has a complete attack path map. Expect Kerberoasting (TGS requests for service accounts with SPNs), AS-REP roasting (TGT requests for accounts without pre-auth), DCSync attempts, or targeted lateral movement to machines identified as stepping stones to Domain Admin. Monitor for these patterns immediately.
- If AdFind queried for computers or domain controllers, expect lateral movement attempts from the source host to those machines within hours. Monitor for Event 4624 (Type 3 logons) from the source host IP to other machines.
- If SharpShares ran, the attacker knows where data is stored. Monitor for unusual file access from the source account to file servers identified during the share enumeration, particularly large-volume reads or access to directories the account has never previously accessed.
- Check whether any accounts identified by the enumeration (domain admins, service accounts with SPNs, accounts with DCSync rights) show anomalous activity in the hours following the enumeration event. UEBA score spikes on these accounts are the earliest indicator that the attacker is moving from reconnaissance to exploitation.
Step 5: Collect evidence and build the timeline
- Export Sysmon Event 1 logs from the source host covering the attack window. Preserve the full command-line field for each enumeration tool invocation.
- Export AD LDAP query logs from domain controllers for the relevant time period, showing the query volume and patterns from the source host. This documents what was queried even if the process-creation log has gaps.
- If an ADExplorer snapshot was created, preserve the file creation event including file path, size, and timestamp. Check whether the file was subsequently accessed or transferred.
- Export the Incident Workbench session timeline from Log360 as the compliance artifact for NIST CSF DE.AE-5 and HIPAA Section 164.308(a)(6) incident procedures documentation.
Response and remediation
Immediate containment
- Isolate the source host. The machine that ran the enumeration tool is the attacker's operational workstation for this phase of the attack. Isolation prevents the attacker from using the collected AD data for immediate follow-on attacks from that machine and from running additional enumeration tools.
- Disable the account used to run the enumeration. Whether the account belongs to a compromised employee or is a service account, disable it immediately. A standard domain user account running SharpHound or AdFind indicates credential compromise; the account should be treated as attacker-controlled until investigation confirms otherwise.
- Locate and delete any collected output files. For SharpHound JSON files, ADExplorer snapshots, and Csvde CSV exports, identify the file paths from the Sysmon logs and delete them before they can be exfiltrated. Check staging directories (user temp, downloads, and any custom output paths specified in the tool command line).
- Alert on accounts identified as high-value targets by the enumeration. If the tool queried for Domain Admins, Kerberoastable accounts, or accounts with DCSync rights, place those accounts under enhanced monitoring immediately. Any anomalous activity from those accounts in the hours following the enumeration event should be treated as active exploitation.
Response actions by trigger
| Trigger | Immediate action | Owner |
|---|---|---|
| SharpView Detection or SharpShares Detection (Critical) | Isolate host immediately. Disable executing account. Check process tree for preceding compromise indicators. Treat as active intrusion. | SOC L2 + Incident Response |
| HackTool - SOAPHound Execution | Isolate host. Attacker is evading LDAP monitoring. Escalate urgency. Check for prior failed SharpHound runs on same host indicating adaptive adversary. | SOC L2 + Incident Response |
| PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE | Isolate host. Review AdFind command line for scope of collection. Check for lateral movement indicators on other machines from the same source IP. | SOC L2 |
| Active Directory Database Snapshot Via ADExplorer | Isolate host. Locate and delete snapshot file immediately. Check outbound traffic for exfiltration of the snapshot file. If exfiltrated, treat as full AD compromise. | SOC L2 + Incident Response |
| Network Reconnaissance Activity or AD Privileged Users or Groups Reconnaissance | Identify source IP. Check for process creation of known enumeration tools on that host. Assess whether collection completed based on LDAP query logs. | SOC L2 |
Hardening
- Deploy Sysmon on all domain-joined endpoints with a configuration that captures process creation (Event 1) including full command-line logging. Most of the detection rules in this use case depend on Sysmon Event 1. Without Sysmon, process-creation-based detection of enumeration tools is not possible.
- Enable LDAP query logging on domain controllers to capture the query volume and patterns that SharpHound and similar tools generate. LDAP diagnostic logging can be enabled via the Windows registry: set HKLM\SYSTEM\CurrentControlSet\Services\NTDS\Diagnostics\16 Field Engineering to 5.
- Restrict access to ADWS (TCP 9389) via host firewall rules on domain controllers to only allow connections from known IT administration workstations and servers. This prevents SOAPHound from reaching the ADWS interface from arbitrary workstations.
- Block known enumeration tool binaries via AppLocker or WDAC for standard user accounts. SharpHound, SOAPHound, AdFind, SharpView, and SharpShares have no legitimate use by standard domain users. Blocking execution of these binaries from user-writable paths eliminates a large class of enumeration attempts.
- Audit and restrict LDAP query permissions. Standard users should not be able to query all user objects, all computer objects, and all group memberships in a single session. Implementing LDAP query result size limits and requiring authenticated binding for privileged attribute queries reduces the effectiveness of bulk collection tools.
False positive tuning
| False positive source | Rules affected | Tuning strategy |
|---|---|---|
| IT administrators using AdFind or ADExplorer for legitimate AD management | PUA - Suspicious ActiveDirectory Enumeration Via AdFind.EXE, ADExplorer snapshot rules | Create an allowlist scoped to specific IT administrator accounts and their designated management workstations. Do not create a blanket exception by account alone; require the account AND the source machine to match. Any execution from a non-admin account or non-management workstation should still alert regardless of the exception. |
| RSAT and PowerShell AD module used by helpdesk and IT staff | Uncommon Connection to Active Directory Web Services, Network Reconnaissance Activity | RSAT tools and the PowerShell AD module use ADWS and generate LDAP queries that can trigger these rules. Allowlist known IT workstations and service accounts that regularly use RSAT. The Uncommon Connection to ADWS rule is specifically tuned for non-standard connections; known RSAT hosts should be excluded from the "uncommon" baseline. |
| Net.exe used by IT staff for account management | Suspicious Group And Account Reconnaissance Activity Using Net.EXE | Single net commands are common and expected. The rule is designed to fire on patterns of multiple domain enumeration commands in rapid succession. Tune the threshold to require a minimum of three distinct domain-targeting net commands within a short window before alerting. Allowlist specific admin accounts that frequently use net.exe for domain management tasks. |
| Authorized penetration testing and red team exercises | All 12 detection rules | Create time-bounded exceptions scoped to the authorized assessment source IP range and tied to the approved change ticket. Remove exceptions immediately when the assessment window closes. SharpView and SharpShares are Critical severity rules; never create permanent exclusions for these. |
| Vulnerability scanners performing AD queries | Network Reconnaissance Activity, AD Privileged Users or Groups Reconnaissance | Some vulnerability scanners query AD as part of authenticated scan workflows. Identify the scanner service account and source IP. Create a scoped exception for that specific account and IP combination. Monitor whether the query patterns match normal scanner behavior (consistent, scheduled, same query set each time) versus adaptive enumeration (varying queries, off-schedule, increasing scope). |


