- Home
- SIEM use cases
- Short-lived admin accounts
How to detect short-lived admin accounts
In this page
Understanding the threat
Threat actors often create short-lived administrator accounts to gain elevated privileges without drawing attention. These temporary accounts are used to execute high-impact actions such as modifying configurations, exfiltrating data, or deploying malware. Attackers then delete these accounts to erase traces of compromise.
Because these accounts often mimic legitimate privilege requests or change activities, detecting them requires correlating multiple events—account creation, privilege assignment, and account deletion—within short time windows. Early detection of such behavior is critical to preventing privilege escalation and insider-driven compromise.
Category:
- Insider threat
Relevant MITRE ATT&CK tactics and techniques:
Tactics:
TA0003 – Persistence, TA0004 – Privilege Escalation, TA0005 – Defense Evasion
Techniques:
T1078 – Valid Accounts, T1098 – Account Manipulation, T1136 – Create Account
Compliance mapping:
- CMMC AC.L2-3.1.5: Supports continuous monitoring and review of account activity to detect unauthorized administrative privilege assignments and timely corrective action.
- NIST AC-2 (Account Management): Enables detection and management of account lifecycle events (creation, modification, removal) to ensure only authorized accounts retain privileged access.
- CIS 6.8 (IG2): Helps maintain an authoritative account inventory and detect anomalous account creation/deletion events that could indicate privilege abuse.
Scenario
In a hybrid enterprise, a user requests temporary administrative access to complete a software update. Shortly after, multiple admin accounts appear and disappear within a few minutes.
Upon investigation, it’s found that an attacker exploited the privilege request workflow to:
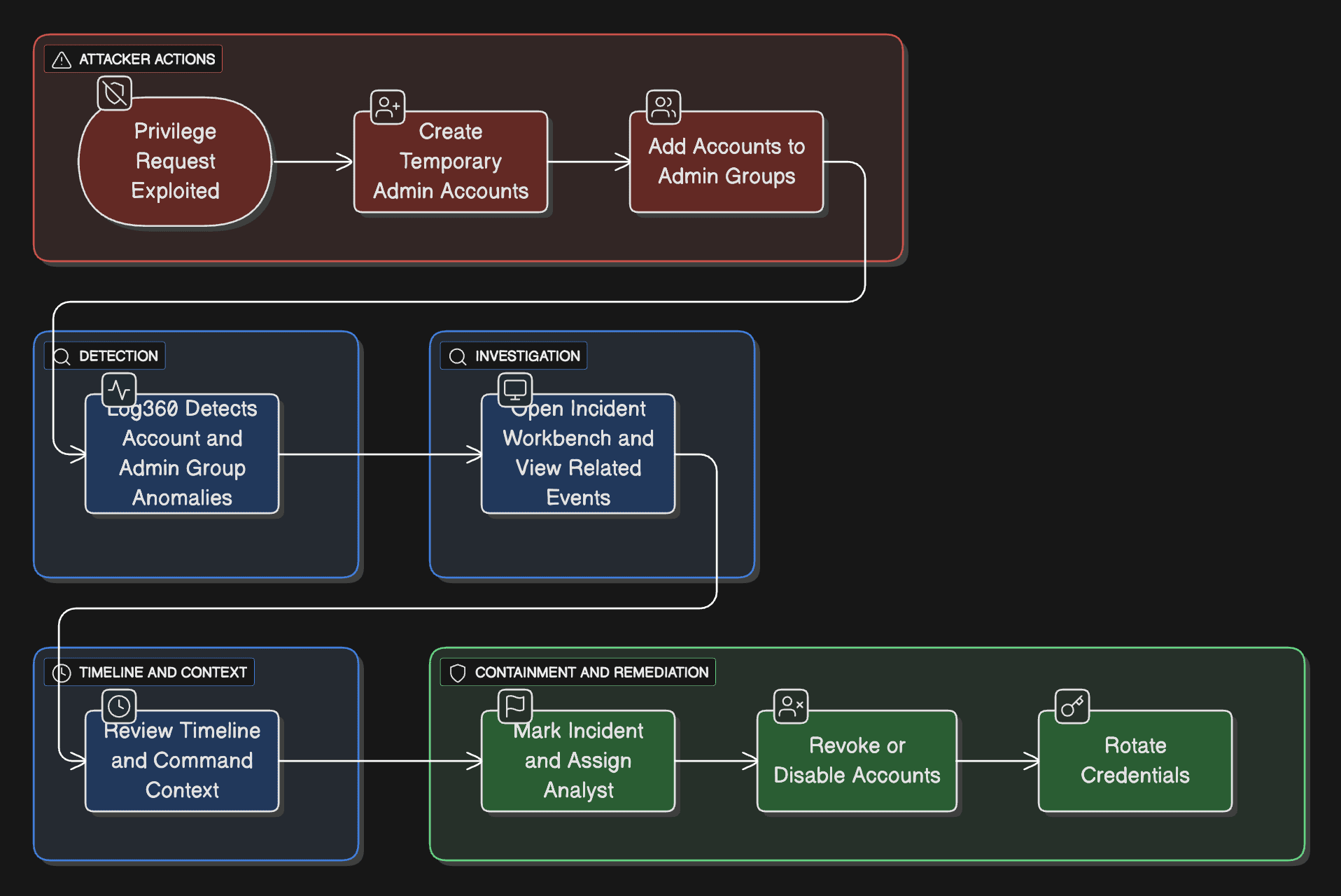
- Create multiple temporary admin accounts.
- Add these accounts to critical administrative groups.
- Execute commands for data extraction and configuration changes.
- Delete the accounts to cover their tracks.
Why this happens
- Temporary access requests provide an opportunity for misuse.
- There's a lack of correlation between account creation and deletion events.
- Legitimate-looking privilege changes often bypass detection filters.
What can go wrong
- Unauthorized privilege escalation
- Data theft or ransomware deployment under admin privileges
- Gaps in audit trails due to quick account removal
Prerequisites:
- Forward audit logs from Active Directory, Azure AD (Entra ID), and Microsoft 365 to Log360.
- User and group modification events should be available for analysis.
How to detect short-lived admin accounts using Log360
1. Monitor admin privilege changes
Log360 continuously tracks user and group modifications, highlighting new admin memberships or elevated privileges across AD, Entra ID, and Microsoft 365.
2. Detect short-lived account activity
Use predefined detection rules such as M365 Short Lived Accounts to detect accounts created and deleted within short intervals.
3. Investigate through the Incident Workbench
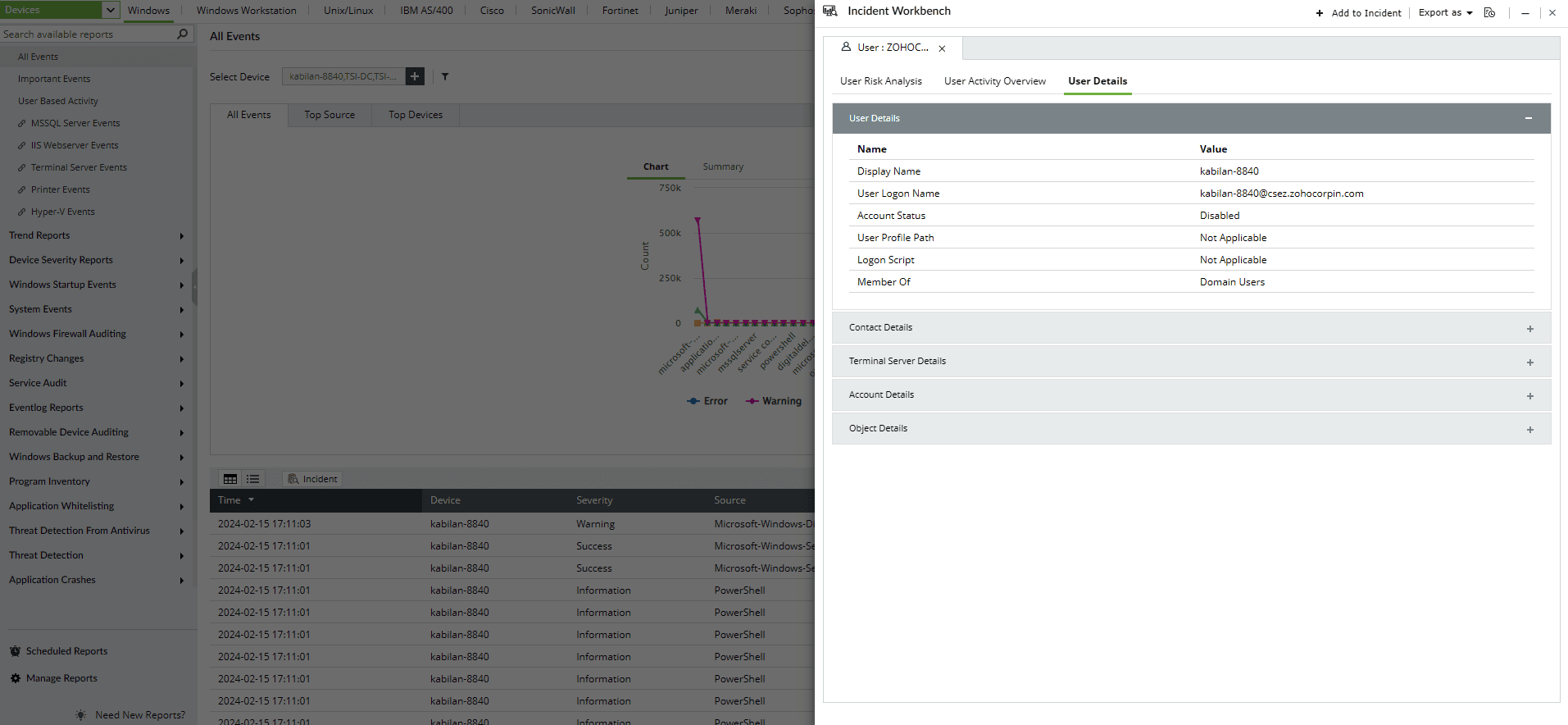
Use the Incident Workbench to investigate suspicious account activities. You can start from an alert or report and expand the investigation window to visualize correlated events—account creation, group membership changes, and account deletion—for deeper context.
4. Review detailed timelines
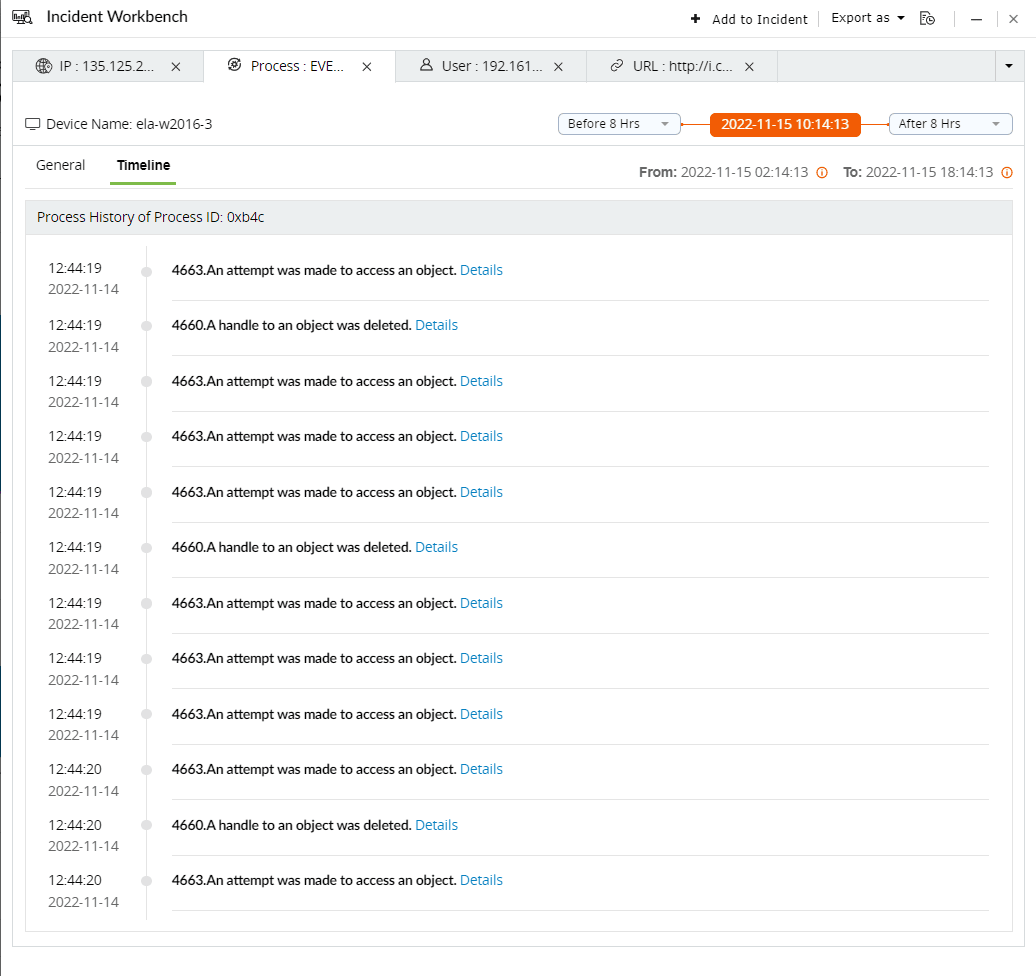
The timeline view helps you trace when an account was created, elevated, and removed, revealing how quickly privilege changes occurred.
5. Automate alerts and responses
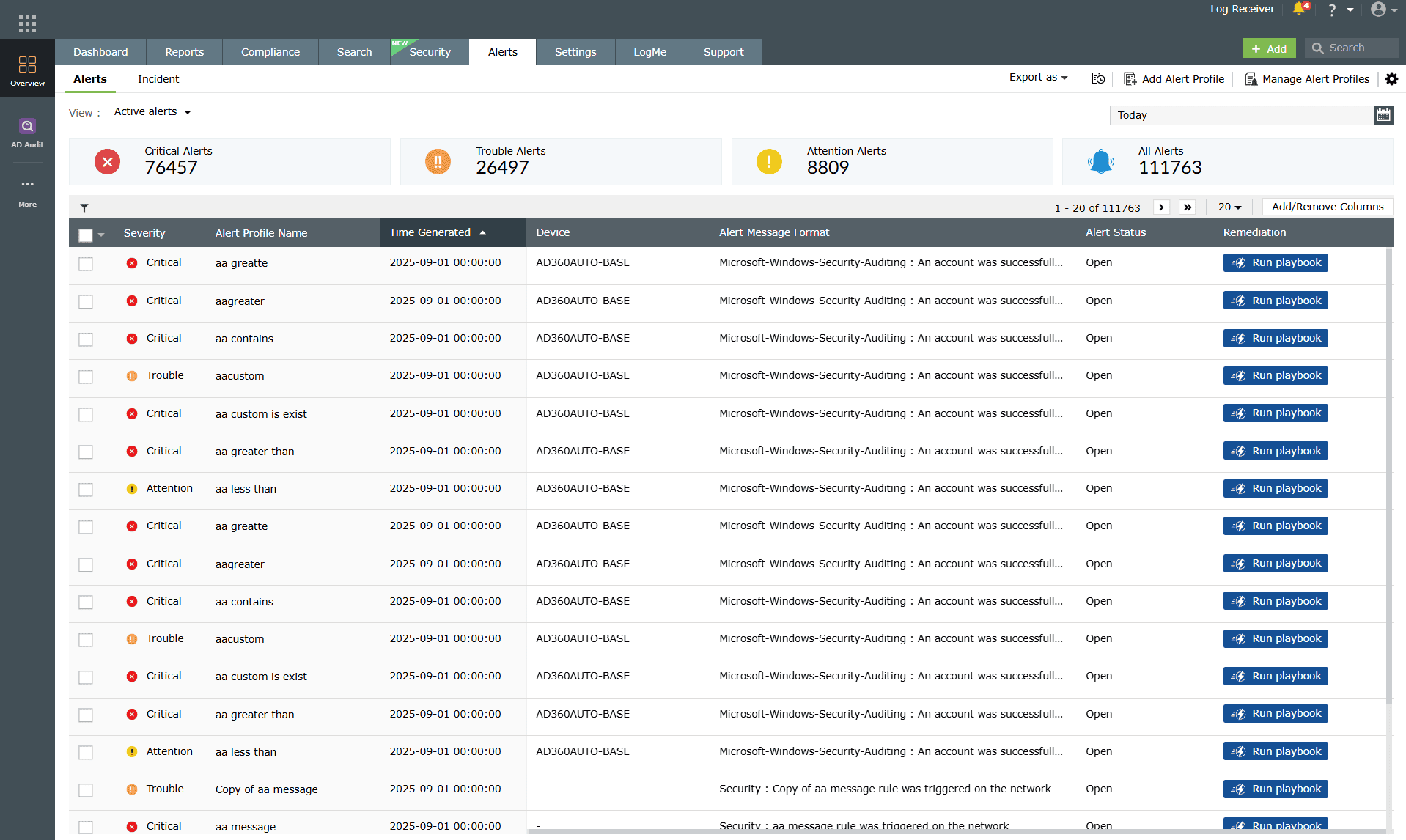
Configure real-time alerts to notify security teams whenever multiple admin accounts are created or removed within a short period, enabling the immediate revocation of unauthorized rights.
Next steps:
- Establish thresholds: Define time-based rules for identifying short-lived admin accounts.
- Correlate activities: Link privilege changes with creation and deletion events to detect misuse.
- Implement automated responses: Integrate alert actions with workflows to disable suspicious accounts automatically.
- Review activity regularly: Periodically analyze admin activity reports to uncover privilege abuse trends.


