- Home
- SIEM use cases
- Vulnerable machines
Vulnerable machines
In this page
Understanding the threat
Vulnerable machines are endpoints that contain unpatched software flaws, misconfigurations, or outdated components and are actively being exploited or probed by threat actors. Attackers frequently rely on built-in system tools, Java-based processes, PowerShell misuse, and service hijacking to exploit known vulnerabilities. These behaviors can reveal that a machine is susceptible to exploitation even before a full compromise occurs. Identifying early indicators of exploitation allows security teams to intervene before attackers escalate privileges, deploy malware, or laterally move.
Category
- Endpoint threat
Relevant MITRE ATT&CK mapping
TA0001 Initial Access: T1190 Exploit Public-Facing Application
TA0005 Defense Evasion: T1059 Command and Scripting Interpreter
Relevant compliance mapping
CMMC SI.L1-3.14.4
NIST SI-2 (Vulnerability Mgt)
CIS 7.3 (IG1)
Scenario
At a company, SOC analysts noticed unusual activity on several endpoints, including unexpected PowerShell mailbox exports, suspicious Java.exe-spawned processes, and unusual child processes tied to dns.exe. One system attempted to run msdt.exe using command parameters associated with a recently disclosed remote code execution exploit. These behaviors indicated that the machines were likely vulnerable to known exploits or already being probed by attackers.
Since the environment lacked real-time monitoring for exploit-linked process behavior, these early signs of compromise went unnoticed. Attackers used these weaknesses to test exploit chains, gather configuration data, and identify paths for deeper persistence.
i) What went wrong
The SOC depended on periodic vulnerability scans and did not have behavioral monitoring in place to detect live exploitation attempts. No alerting existed for suspicious msdt.exe execution, Java subprocess abuse, or DNS service anomalies. As a result, vulnerable endpoints showed signs of compromise long before they were flagged in the vulnerability management workflow.
ii) How vulnerable machine monitoring helps
Monitoring exploit-related behaviors allows security teams to detect vulnerable systems based on real-time attack activity rather than periodic scans. This provides immediate visibility into machines being targeted and reduces the time attackers have to escalate privileges or deploy malware.
iii) Real-world trends
Exploitation frameworks increasingly chain multiple vulnerabilities and rely on native Windows utilities to stay stealthy. Attackers frequently identify vulnerable machines by probing them with low-noise commands before launching full-scale attacks.
Detecting vulnerable machines
Prerequisites
- Enable process creation logging on all monitored endpoints.
- Ensure PowerShell logging and command-line auditing are enabled.
- Forward endpoint logs, including service-level activity, to Log360.
- Document approved application behaviors to identify abnormal process relationships.
- Enable all relevant alert profiles for exploit behavior detection.
How to detect vulnerable machines using Log360
Log360 provides visibility into exploit-linked activity, helping analysts quickly identify endpoints that are vulnerable or under active attack. Here’s how:
a. Identify suspicious exploit-related behavior
Log360 highlights unusual msdt.exe invocation patterns, anomalous Java subprocess behavior, unexpected DNS service child processes, and abnormal PowerShell activity. These behaviors can signal exploitation attempts or unpatched endpoint vulnerabilities.
b. Enable prebuilt detection rules and alert profiles
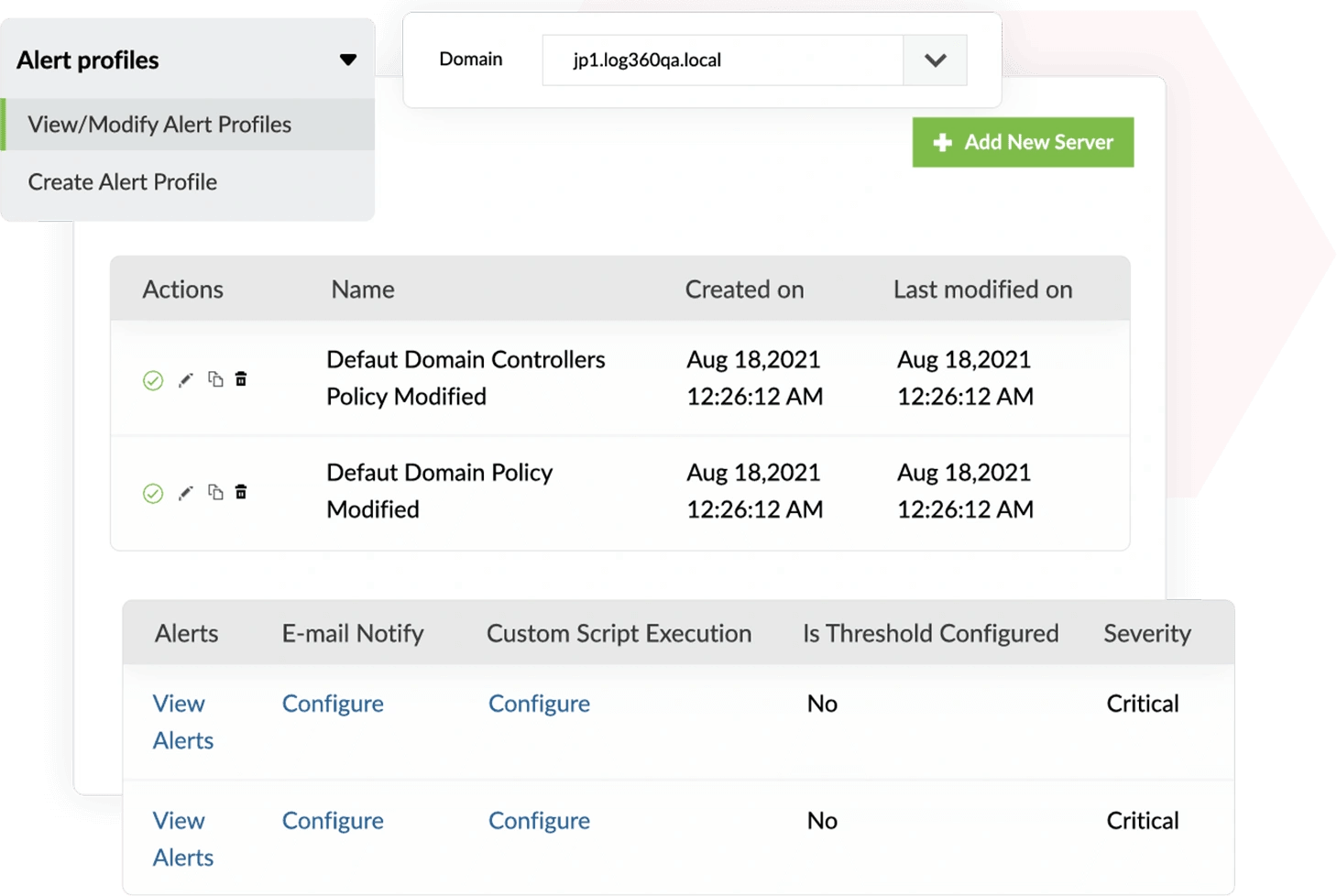
Enable alert profiles for the following detection rules to detect registry-based evasion techniques:
- Potential Arbitrary Command Execution Using Msdt.EXE
- Unusual Child Process of dns.exe
- Suspicious Processes Spawned by Java.EXE
- Suspicious PowerShell Mailbox Export to Share - PS
- Disable-WindowsOptionalFeature Command PowerShell
These detection rules surface behaviors associated with exploit delivery, unsafe subprocess activity, and flaws in unpatched software components.
c. Access the Incident Workbench to analyze timeline and process lineage
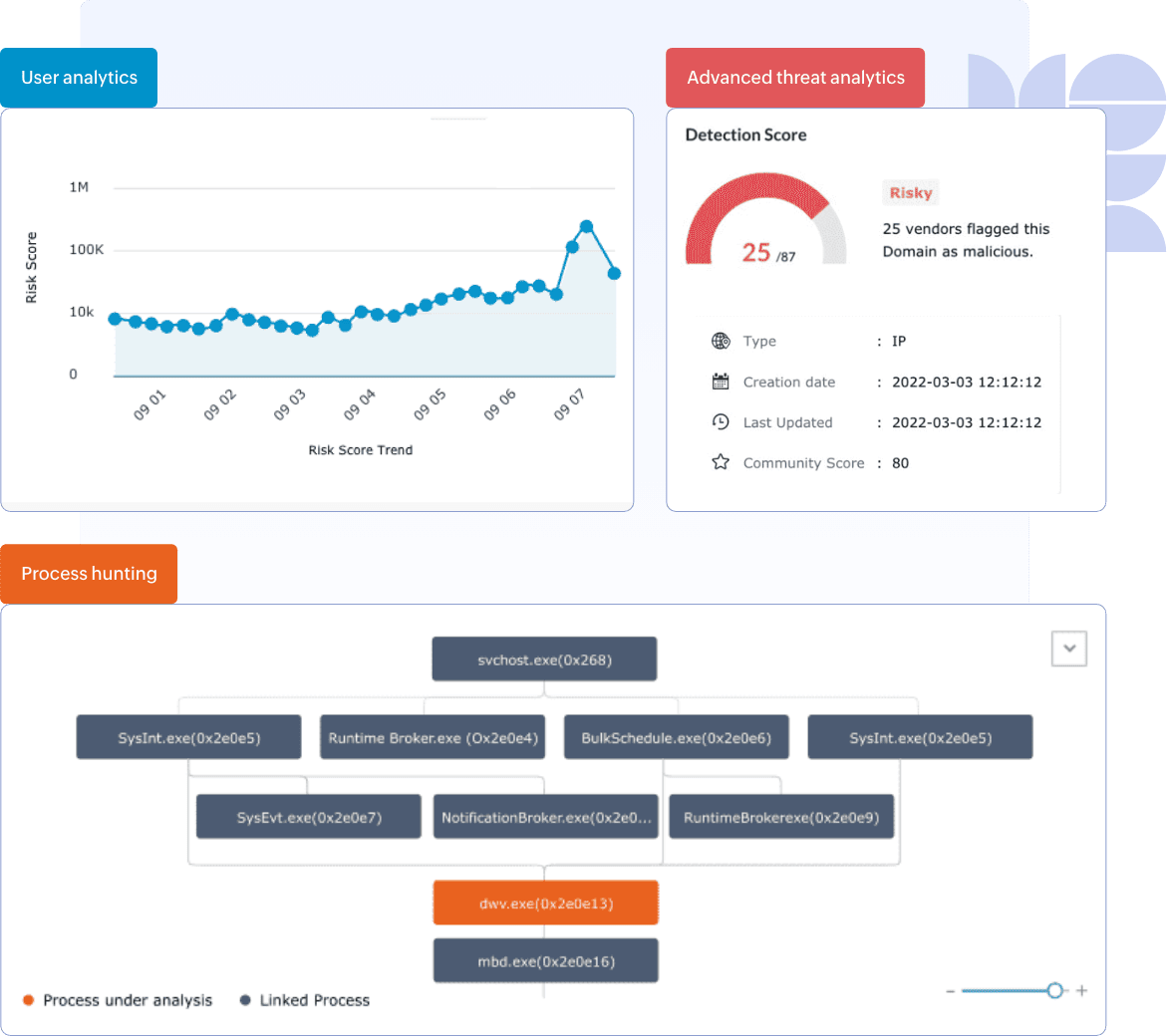
Open the Incident Workbench from any alert to investigate the flagged activity. Use the timeline to review when the suspicious execution occurred and what processes were involved. The Process Hunting Tree helps identify whether the behavior originated from unpatched components or unauthorized exploitation attempts.
d. Raise incidents and assign analysts
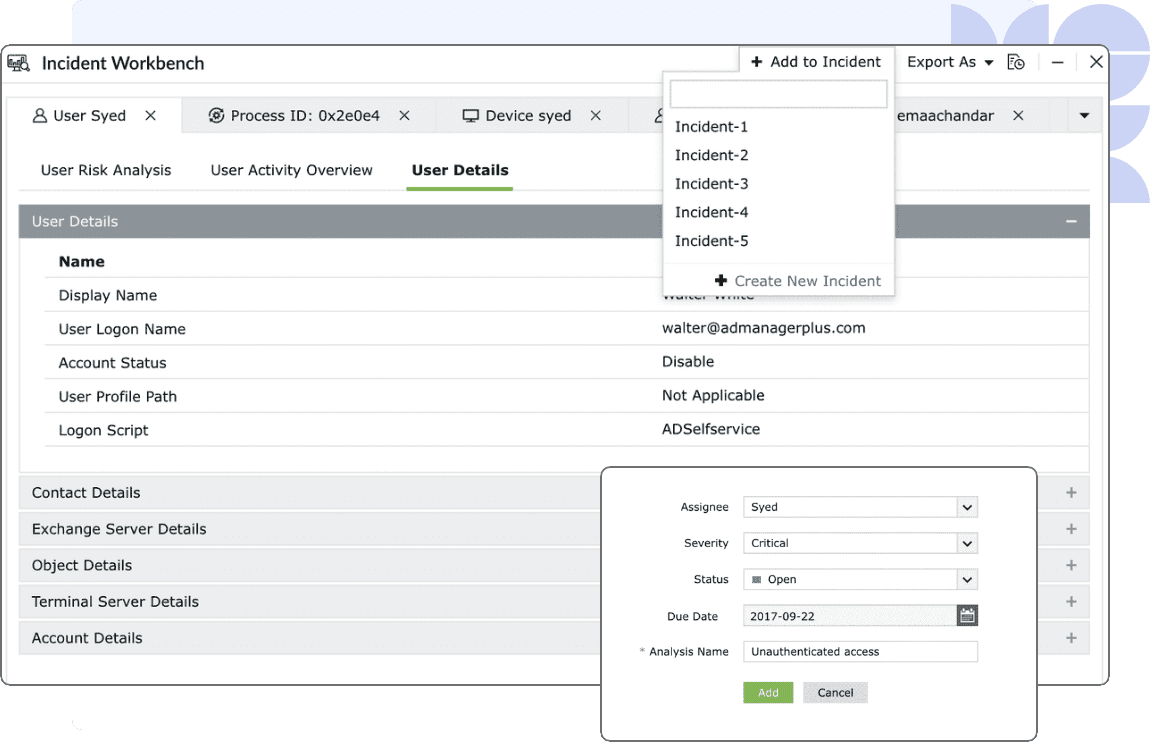
Convert suspicious events into incidents within the Workbench. Assign the case to analysts for deeper review and to determine whether the endpoint requires patching, isolation, or further remediation.
Next steps
- Define high-risk behaviors associated with known exploits in your environment to strengthen detection logic.
- Enable and tune alert profiles for exploit-linked process patterns across endpoints.
- Conduct regular reviews of process lineage and vulnerability activity reports to spot emerging attack behavior.
- Incorporate exploit-behavior detection into the vulnerability management workflow to prioritize patching of actively targeted systems.


